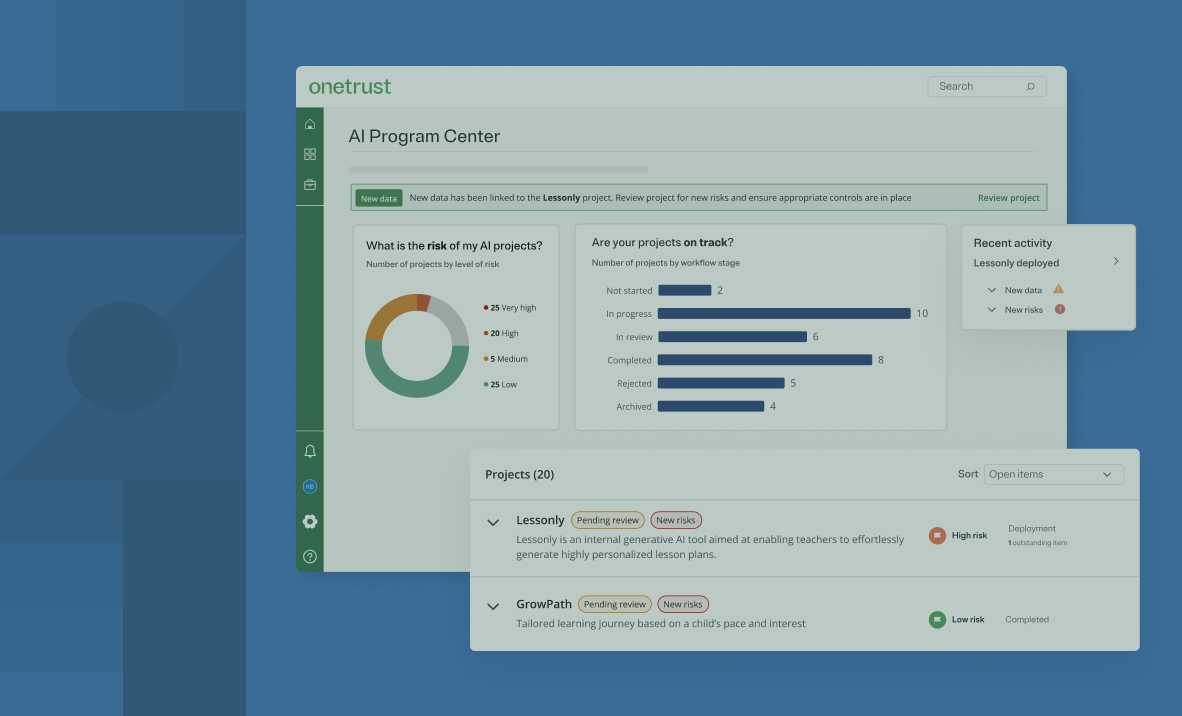
Explore expert insights, best practices, and tools to help you manage risk, ensure compliance, and innovate responsibly.
OneTrust Resources
Explore featured collections
The latest in AI
Data Privacy Day 2026
Latest resource and articles
Help center
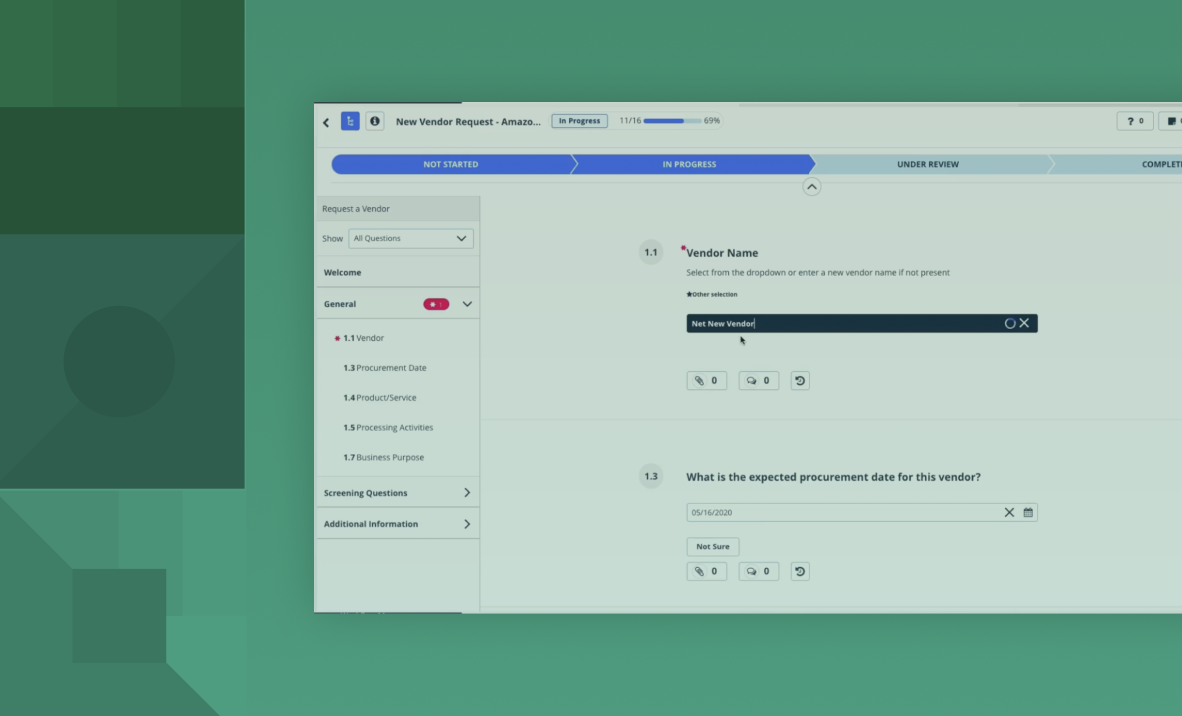
Review product documentation to learn more about features and how to configure your system to best support your needs.
Regulatory research
Navigate complex regulations, understand their practical impact, and make informed decisions with guidance and insights from our community of 1,700 expert contributors.
Training & certifications
We provide comprehensive, free online courses along with in-person paid engagement options tailored to both beginners and advanced professionals.