All businesses have a semi-structured data model, made up of two types of data: unstructured and structured data.
Most business data is unstructured and held in tools often with open access to all employees. If left unchecked, this exposes the business to the risk of data loss and non-compliance.
With structured data, data management is an easier task, as relational databases (such as SQL) and datasets have predefined fields that can be easily accessed and processed.
While having large amounts of unstructured data in your organization is not inherently bad, the issues of access, data sensitivity, and compliance get exponentially more complicated in an unstructured data environment. Examples of unstructured data include text files (documents), spreadsheets, video files, audio files, web pages, and even social media posts.
1. Understanding, Identifying and Governing Your Unstructured Data
The big data and metadata that sits in these sources could be subject to the following:
- Encryption/masking requirements
- Retention Periods
- Privacy Rights Requests
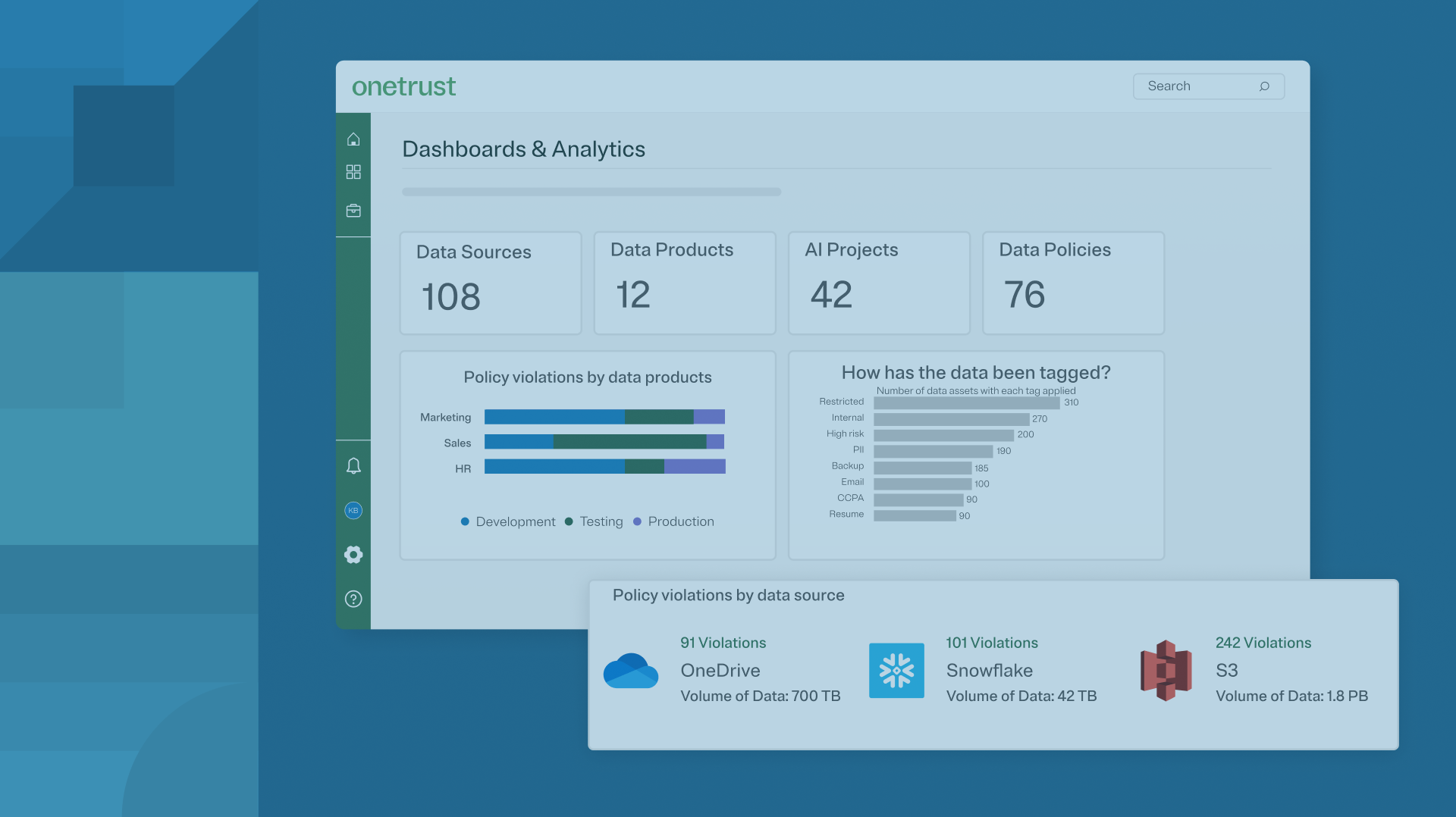
Automating your data discovery and classification process in unstructured environments is the most effective way to help ensure it remains compliant, accessible, and secure.
The words automation, artificial intelligence, natural language processing, and machine learning algorithms are thrown around far too often nowadays, and although they are powerful technologies that can be leveraged effectively, they don’t guarantee efficiency.
You need to provide them with business intelligence – the rules they need to follow for your enterprise data. Have a legal expert walk your team through applicable regulatory bodies and data regulations that apply to your industry and region to fine-tune your unstructured data environment to a well-cataloged file system.
2. Streamlining Employee Privacy Rights Requests
As is the case with consumers, employees are also learning more about their data rights. With the GDPR and CPRA clearly laying out provisions for employees to know and understand the extent of their employer’s data, employee requests to access personal information are on the rise.
What makes these requests more cumbersome than a standard privacy rights request from a customer is the scale of employee information companies have. This information tends to sit in emails, chats, SharePoint files, and other unstructured sources of data.
Handling employee rights requests can be broken down into three steps:
- Streamline the ID verification process by using an internal portal for a single pipeline
- Optimize real-time data discovery with tools to scan sources for employee information
- Automate redaction to ensure no sensitive data leaks
3. Enforcing Document Retention and Deletion Policies
Even employees with the best intentions commonly store files in non-designated data storage areas, generate share links for documents without thinking twice about the associated risk, and use their personal devices to access and share data that may be considered confidential.
Counteracting these practices first requires data analysis to document high-risk processes that lead to the scenarios mentioned above.
The next steps are flagging policy violations and escalating to InfoSec teams for investigation and remediation when the volume of high-risk activity reaches a specified threshold. This schema will allow your organization to enforce data retention and deletion policies effectively.