Blog
What Can and Can’t Be Automated for SOC 2
Not all SOC 2 components can be automated, but those that can will save your business time and money.
October 5, 2022

Everyone is searching for a simplified SOC 2 experience but there’s some confusion about what can and can’t be automated for SOC 2. It’s not something that can be 100% hands-free.
Reducing your number of daily decisions is a form of automation. It’s how you streamline processes, limit distractions and save time and manpower. By default, manual implies the opposite—especially with SOC 2. As a result, you can’t help but feel a bit panicky as you prepare for what you assume will be a labor-intensive experience that will suck the joy out of your day-to-day tasks. But not all manual tasks are complex.
For example, take a smart coffee machines that consistently deliver a decadent caffeine experience. As a home barista, you can choose between a cappuccino or a basic cup of black, set a program to run or even ask Alexa to do it for you. However, you’re still responsible for installing a coffee pod and filling the water reservoir manually for the machine to complete the task. The hands-on, manual expectations are quick, clear and straightforward, though.
Manual work for SOC 2 is similar. With the right automation, the manual evidence collection tasks are a lot like adding water. You save time and end up with a successful audit to pair with your delicious cup of coffee. Let’s take a look at some examples of what can and can’t be automated for SOC 2.
What Can Be Automated for SOC 2
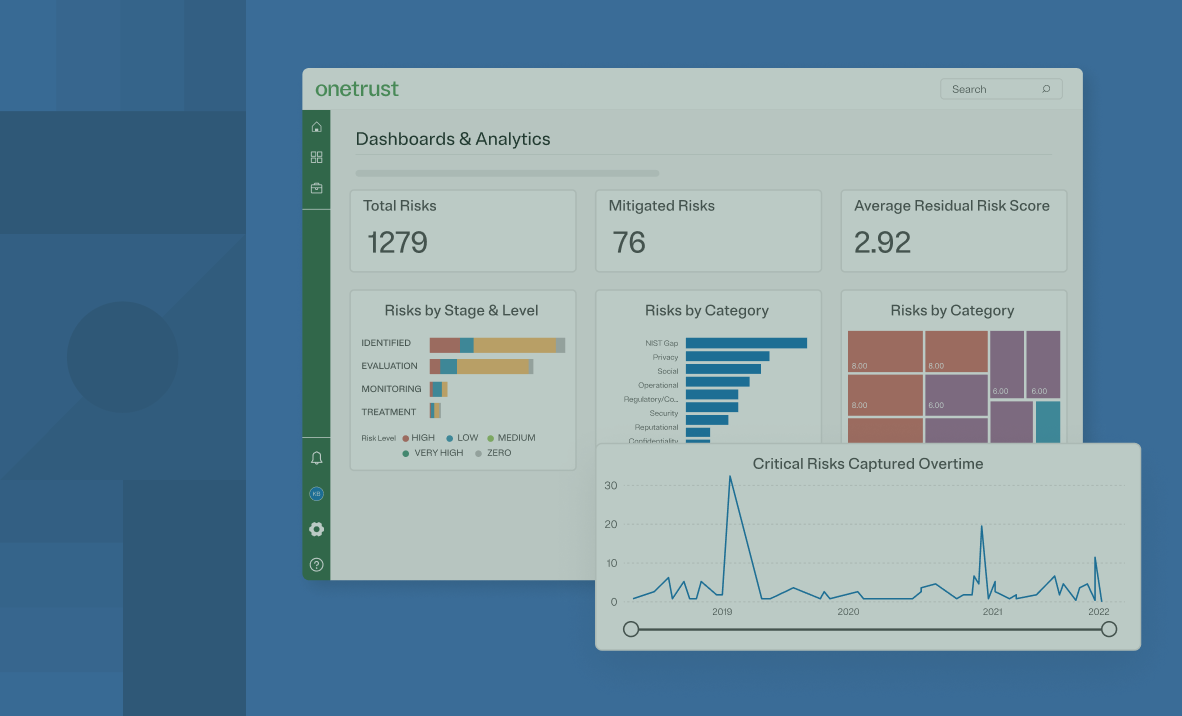
Most organizations face the same SOC 2 challenge—ensuring their team implements the necessary controls and properly document evidence. Automating evidence tasks saves time, money, and stress.
When searching for SOC 2 software, automated evidence collection and integrations are a high priority.
What Can’t Be Automated for SOC 2
If a software provider claims to automate the entire SOC 2 process, they may not be sharing all the details. In fact, it’s just not possible. Instead ask questions specifically about the following manual tasks.
HR-related tasks like background checks
Most organizations use a third party for background checks. All the information they’re supplied is pulled into whatever HR system they use. Depending on the position in question, background checks may include:
- Criminal records
- Employment history
- Reference checks
- Citizenship status or a work visa
- Credit history
- Education
- Social media profiles
- Driving record
- Medical records
Does a SOC 2 auditor require an employee’s traffic ticket from 2012? Of course not. In fact, that’s private information they definitely don’t want in their possession. Auditors want to see evidence that the background check was completed, but not the contents of the check.
Collecting this information manually just makes sense. That way, data requiring redaction or removal is confidently completed. Will you fail your SOC 2 for sharing Bob’s traffic ticket with an auditor? No, but it does increase back and forth communication with your auditor, potentially delaying completion.
Executive management review meetings
Companies typically have executive management meetings or board meetings on a set frequency. These quarterly or semi-annual meetings generally are not run through software. But, they usually have presentations. The decks include company performance, strategy points, and overviews resulting in discussions. Those are documented in meeting minutes. The minutes and the visuals may be stored in the cloud, but an integration won’t pull the evidence a SOC 2 auditor requires.
There’s information in these presentations and confidential notes similar to the background check. A screenshot with redacted information is plenty for evidence regarding executive management review meetings. And if your auditor is looking for something specific, they’ll guide you.
Business continuity and disaster recovery plans or tests
Business continuity and disaster recovery plans or tests can be managed with sophisticated software. However, it’s still common in businesses of all sizes to maintain these on good old-fashioned printouts. After all, if a disaster occurs and the connection to your network is lost, how will you know what to do? That’s why Word or PDF docs are still routine.
These plans also require annual testing. Multiple departments review them and provide feedback for revisions. Then there’s real-life scenario testing. What was the scenario? When did you execute the plan? What was the outcome and which departments were involved? Organizations maintain all of this manually within their documents, making it easy for auditors to collect the information relative to the SOC 2 audit via screenshot.
Learn more about gaining compliance by downloading this eBook about the ISO 27001 journey. To learm more about OneTrust Compliance Automation tool, go here.
You May Also Like

Upcoming webinars
Third-Party Risk
AI Risk Management: Preparing for EU AI Act Compliance While Driving Innovation
Learn how to turn AI governance principles into action with this live webinar. We will discuss how organizations can operationalize AI governance, manage AI risk, and oversee third‑party AI to meet evolving regulations.
July 08, 2026

Upcoming webinars
Technology Risk & Compliance
The New Risk Model: Converging Privacy, GRC and AI Governance
Join risk leaders from OneTrust and PwC as they explore how forward-looking organizations are converging privacy, GRC, and AI governance into a unified, intelligence-driven model.
June 10, 2026

On-demand webinars
Technology Risk & Compliance
How OneTrust solves the ‘Why should I care?’ of risk insights
Discover how OneTrust aggregates and contextualizes risk data, models business and technical impact, and delivers board-ready dashboards that translate technical risk into clear, executive-level decisions.
May 19, 2026

On-demand webinars
AI Governance
The AI Risk Maturity Journey: Embedding Continuous Governance Across the Lifecycle
Learn how leading teams move from reactive compliance to lifecycle-embedded governance — enabling better communication of AI risk to executives, stronger oversight, and measurable business value.
May 07, 2026

On-demand webinars
Third-Party Risk
How OneTrust solves inconsistent and subjective risk scoring
Learn how OneTrust enables structured, transparent risk scoring by standardizing questionnaires, distinguishing inherent and residual risk, creating explainable scores, and turning risk data into actionable business insights.
May 05, 2026

eBook
Technology Risk & Compliance
The Modern CISO Risk Surface: AI, Third Parties, Fourth Parties, and Beyond
Today’s enterprise operates across clouds, SaaS ecosystems, partner integrations, AI, and global supply chains. And that has expanded the digital ecosystem beyond anything we’ve ever seen.
April 27, 2026

On-demand webinars
Technology Risk & Compliance
How OneTrust solves manual, ad-hoc IT and asset risk
See how OneTrust helps security and IT teams centralize asset risk visibility, automate and standardize assessments, connect controls and compliance, and reduce manual effort through scalable, ongoing risk management.
April 21, 2026

On-demand webinars
AI Governance
Operationalizing AI Governance: From Complexity to Control
Join our webinar to learn how to architect a scalable AI governance stack, connecting risk, compliance, and development for responsible AI adoption.
April 14, 2026

On-demand webinars
Third-Party Risk
How OneTrust solves visibility gaps and standardizes risk management
Learn how OneTrust helps security and risk teams replace fragmented vendor data with a centralized risk architecture, delivering a single source of truth, mapped vendors, full visibility, and scalable, proactive risk management.
March 31, 2026

On-demand webinars
Technology Risk & Compliance
Smarter TPRM in action: Using AI to drive efficiency and better risk outcomes
See how AI‑enabled TPRM transforms traditional vendor risk programs in this live demo, showcasing faster assessments, reduced manual effort, clearer risk insights, and smarter prioritization across the third‑party lifecycle to build a more scalable, outcome‑driven TPRM program.
March 25, 2026

On-demand webinars
Technology Risk & Compliance
Compliance in the AI Era: What changes in 2026 (and How to Keep Up)
Join OneTrust experts for a practical look at what’s ahead in 2026 and how leading teams are simplifying compliance across frameworks, geographies, and systems.
March 17, 2026

On-demand webinars
Third-Party Risk
Simplifying Risk and Compliance: From Chaos to Clarity Webinar Series
Join our demo webinar series to see how OneTrust simplifies third-party management and technology risk & compliance.
March 02, 2026

On-demand webinars
Technology Risk & Compliance
2025 regulatory round-up: Navigating the evolving compliance landscape
In this webinar, our regulatory intelligence experts break down the most important updates across 60+ global frameworks and help your teams move from research to action with practical, operational guidance.
January 14, 2026

eBook
Technology Risk & Compliance
The strategic guide to third-party risk management
FLLR and OneTrust guide outlines five TPRM principles to manage third-party risk, avoid pitfalls, and build a scalable program.
January 09, 2026
Data Sheet
Technology Risk & Compliance
A programmatic guide to 60+ complex frameworks
Managing compliance is a constant challenge and can present an undue burden on organizations as new regulations, standards, and frameworks are introduced and updated globally and across geographies and industries.
January 05, 2026

Resources
Third-Party Risk
Integrated risk insights power smarter decisions
Modern organizations are swimming in data. Every business function, from sales and marketing to IT and security, generates valuable insights. Yet these datasets are often siloed, duplicated, or disconnected.
December 22, 2025

Infographic
Technology Risk & Compliance
Connecting risk insights enable smarter business decisions
What happens when datasets across every business function in an organization are siloed or disconnected? The risk and compliance teams struggle to see the whole picture.
December 17, 2025

On-demand webinars
Responsible AI
Future of Third-Party Risk Management: AI, Governance, and Strategic Transformation
Discover how AI, governance, and transformation frameworks are reshaping Third-Party Risk Management. Join OneTrust and Deloitte on Dec 9.
December 09, 2025

On-demand webinars
AI Governance
Risk-enabled innovation: Uniting AI governance and risk management to accelerate responsible growth
Join OneTrust’s CISO and Head of AI Governance & Privacy to uncover how risk and governance alignment drives responsible AI innovation.
December 04, 2025

Upcoming webinars
Technology Risk & Compliance
Transforming risk management through integrated enterprise risk: A perspective from OneTrust & PwC
Join PwC and OneTrust for a webinar on how leading organizations are reinventing risk management through a connected, digital-first Integrated Risk Management (IRM) approach.
November 04, 2025

On-demand webinars
Third-Party Risk
Highlights of the Fall OneTrust release for risk solutions
Watch how OneTrust’s latest Risk Solutions release empowers teams with AI-driven vendor onboarding and automated evidence analysis for smarter compliance.
October 28, 2025

On-demand webinars
Technology Risk & Compliance
How OneTrust supports NIS-2 compliance: On-demand demo of our solution
Watch now this on-demand webinar to see how OneTrust helps organizations identify, manage, and mitigate cybersecurity risks in alignment with NIS-2 compliance obligations.
October 22, 2025

On-demand webinars
Technology Risk & Compliance
Evolution for compliance programs: A 5-point blueprint to mature your programs
Join our webinar to learn a practical compliance maturity framework and uncover strategies to evolve and optimize your compliance program.
October 07, 2025

eBook
Technology Risk & Compliance
Reinventing risk management through integrated risk: A joint perspective from PwC and OneTrust
A joint perspective from PwC and OneTrust on reinventing risk management through integrated risk:
September 11, 2025

Upcoming webinars
Technology Risk & Compliance
5 automation trends modernizing InfoSec in 2025
Learn how automation is transforming InfoSec program management to tackle modern risks, boost resilience, and deliver measurable business value.
August 13, 2025

On-demand webinars
Technology Risk & Compliance
Taming compliance complexity: Strategies for scaling across frameworks, systems & geographies
Discover how to scale compliance programs amid rising regulations and complexity. Gain actionable strategies to streamline controls, audits, and global oversight.
July 23, 2025

Report
Technology Risk & Compliance
OneTrust named a leader in the 2025 IDC MarketScape for worldwide GRC software
The OneTrust platform connects data, privacy, and risk teams in one unified system, so you can stay ahead of regulatory change and support responsible growth. Download the excerpt to learn how OneTrust helps you move faster, without sacrificing compliance.
July 17, 2025

On-demand webinars
Responsible AI
Building AI governance with security at the center
Discover how security leaders are securing AI models, data, and infrastructure while driving risk-aware AI governance programs.
July 10, 2025

On-demand webinars
Technology Risk & Compliance
Unifying third-party and tech risk in an AI-driven world
Join our webinar to learn how risk and security leaders are aligning third-party and tech risk for scalable, AI-ready compliance programs.
July 08, 2025

On-demand webinars
Technology Risk & Compliance
The automation advantage: Unlocking ROI from risk and compliance
Learn how automation reduces compliance costs, boosts audit readiness, and delivers 75%+ time savings across the compliance lifecycle in this practical, ROI-focused session.
May 28, 2025

On-demand webinars
Privacy Management
OneTrust Spring Release
We explore the latest release which introduces AI-assisted features that help privacy and third-party risk teams scale by reducing manual effort and friction, so they can focus on the work that matters most.
May 27, 2025

eBook
Technology Risk & Compliance
The risk-resilient enterprise: Automating compliance for security & scale
Risk flows throughout your organization’s systems and data, and without mapping or monitoring, your company’s security posture is constantly under pressure.
April 24, 2025

On-demand webinars
Technology Risk & Compliance
From reactive to resilient: Building and scaling a modern enterprise risk program
Join our masterclass for CISOs & InfoSec leaders to build scalable, modern risk management programs. Gain actionable strategies, frameworks, and real-world insights for success.
April 22, 2025

On-demand webinars
Technology Risk & Compliance
Harmonizing risk and compliance: Unifying InfoSec programs through automation
Join this webinar to discover how to streamline ISO 27001, GDPR, NIST & PCI DSS with automation, reduce manual work and enhance oversight.
April 09, 2025

Infographic
Technology Risk & Compliance
Automating compliance mitigates risk
Download our infographic to learn steps involved in compliance automation and how it mitigates risk in your organization's security program.
March 27, 2025

On-demand webinars
Technology Risk & Compliance
Operational resilience in a changing world: Going beyond compliance
Join this session to unpack key regulations, such as ISO 27001, APRA CPS 230, DORA, & SOC2, to learn how they impact internal & third-party operations.
February 20, 2025

On-demand webinars
Technology Risk & Compliance
Compliance Automation product showcase
Join our live demonstration and see how Compliance Automation can help boost compliance efficiency with automated workflows, shared evidence, and 40+ frameworks.
December 19, 2024

On-demand webinars
Technology Risk & Compliance
The PDPL in Saudi Arabia is now in effect: is your business ready?
Join our Saudi Arabia PDPL webinar for an overview on the data protection law, its requirements, and how to prepare for full enforcement.
December 12, 2024

On-demand webinars
Technology Risk & Compliance
Elevating client compliance with OneTrust Automation: Key strategies for partners
Discover how to use OneTrust Compliance Automation to establish client baselines, improve efficiency, and drive scalability. Learn key strategies to enhance your compliance impact.
December 11, 2024

On-demand webinars
Technology Risk & Compliance
Understanding the NIS 2 Directive: Compliance insights and best practices
This DataGuidance webinar explores the latest and expected developments in the implementation of the NIS 2 Directive, focusing on practical compliance strategies to ensure your organization is prepared.
December 04, 2024

On-demand webinars
Technology Risk & Compliance
Tech risk and compliance masterclass: An evidence-based approach to building by-design risk and compliance practices
Discover strategies to embed compliance and risk management into business processes with minimal disruption, using technology-driven solutions for efficiency, scalability, and improvement.
November 06, 2024

On-demand webinars
Technology Risk & Compliance
Building a strong security posture: Managing compliance, risk, and business engagement in a dynamic landscape
Join our webinar to learn how to optimize security posture, streamline compliance, and leverage automation to manage IT risk in today's complex digital landscape. Register now!
October 29, 2024

On-demand webinars
Privacy Automation
Build resiliency and operationalize compliance with OneTrust: Fall product release recap, 2024
Join our upcoming product release webinar to explore how these new capabilities can help your organization navigate complex frameworks, streamline third-party management, and accelerate AI and data innovation.
October 22, 2024

On-demand webinars
Technology Risk & Compliance
Tech risk & compliance masterclass: The anatomy of a framework
Master the fundamentals of constructing robust compliance frameworks that can seamlessly integrate with organizational operations while aligning with regulatory and strategic mandates to deliver measurable insights on your progress and gaps.
August 14, 2024

Upcoming webinars
Third-Party Risk
Third-Party Risk Management: From compliance to strategy series
Navigate third-party risk challenges and discover strategic steps to scale, automate, and operationalize your program with this webinar series.
August 09, 2024

Upcoming webinars
Technology Risk & Compliance
Tech risk and compliance masterclass series
Unlock tech risk management & compliance excellence. Master risk management, build robust frameworks, and foster cross-functional collaboration for long-term resilience.
August 07, 2024

On-demand webinars
Technology Risk & Compliance
Introducing OneTrust Compliance Automation
Join us as we explore OneTrust Compliance Automation, a holistic and fully integrated solution that streamlines and optimizes workflows, compliance, and attestation.
July 25, 2024

On-demand webinars
Data Discovery & Classification
Catch it live: See the all-new features in OneTrust's Spring Release and Post-TrustWeek recap
Join us as Ryan Karlin, Senior Director of Product Marketing highlights important updates from TrustWeek including an inside look into OneTrust's new platform features that make it easier for customers to activate data responsibly, surface and mitigate risk, and navigate the complex regulatory environment.
June 06, 2024

Report
AI Governance
GRC strategies for effective AI Governance: OCEG research report
Download the full OCEG research report for a snapshot of what organizations are doing to govern their AI efforts, assess and manage risks, and ensure compliance with external and internal requirements.
May 22, 2024

Infographic
Third-Party Risk
Streamline compliance with the Digital Operational Resilience Act (DORA)
Download our infographic to learn about the new DORA regulation, who needs to comply, and how OneTrust can help streamline the process.
April 29, 2024

On-demand webinars
Ethics Program Management
EthicsConnect: Risk - It’s not just for breakfast anymore
Join us for an insightful exploration of navigating a risk-based approach to ethics and compliance in today's corporate landscape. Hosted by three E&C leaders, our virtual discussion will delve into essential considerations for companies striving to align their compliance strategies with their risk profiles.
April 25, 2024

Infographic
Technology Risk & Compliance
Rethinking risk assessments: Bridging the gap between best practices and action
Download our infographic to learn the main challenges faced during risk assessments, proven frameworks for assessing risks, and how to translate guidance into action.
March 07, 2024

On-demand webinars
Technology Risk & Compliance
PCI DSS Compliance: How to scope and streamline monitoring with Certification Automation
Join our PCI DSS webinar where we discuss how Certification Automation can help free up valuable InfoSec resources, streamline audits, and stay continuously compliant.
March 05, 2024

eBook
Ethics Program Management
Business messaging apps: A guide to corporate compliance
How can your business use third-party messaging apps while staying compliant? Dive into key usage considerations based on the DOJ’s 2023 guidance.
February 13, 2024

On-demand webinars
Technology Risk & Compliance
5 automation trends to modernize InfoSec compliance
Join our webinar for insights on transforming InfoSec program management. Navigate the complexities of modern security with a flexible, scalable, and cost-effective approach.
February 07, 2024

Infographic
Third-Party Risk
4 top-of-mind challenges for CISOs
What key challenges do CISOs face going into the new year? Download this infographic to hear what experts from industries across the board have to say.
January 30, 2024

eBook
Technology Risk & Compliance
NIST CSF 2.0: Changes, impacts and opportunities for your Infosec program
Get your free guide to the NIST Cybersecurity Framework 2.0 and learn how its proposed changes will impact your InfoSec programs.
December 18, 2023

Resource Kit
Technology Risk & Compliance
NIST CSF essentials: Empowering cybersecurity excellence
Download our NIST CSF Essentials resource kit and master cybersecurity compliance with expert insights, strategies, and real-world case studies.
December 15, 2023

On-demand webinars
Technology Risk & Compliance
Demonstrating GDPR compliance with Europrivacy criteria: The European Data Protection Seal
Join our webinar to learn more about the European Data Protection Seal and to find out what the key advantages of getting certified.
November 30, 2023

Data Sheet
Technology Risk & Compliance
Integrations to automate your framework compliance: ISO 27001, SOC 2, and NIST CSF
Explore how OneTrust integrations can help you automate compliance with today’s most popular InfoSec frameworks.
November 28, 2023

Checklist
Technology Risk & Compliance
SOC 2 checklist: 8 steps to achieve compliance
This SOC 2 checklist provides clear action steps that enable you to mature your security program and fast-track your way to compliance.
November 28, 2023

eBook
Technology Risk & Compliance
Navigating the ISO 27001 compliance journey eBook
In this guide, you’ll learn what ISO 27001 is, which steps to take at each phase of the process, and how automation can help you get and stay compliant.
October 16, 2023

Infographic
Technology Risk & Compliance
Understanding Europe's Top InfoSec and Cybersec Frameworks
Learn the ins and outs of Europe’s top InfoSec and cybersec frameworks, including ISO 27001, UK Cyber Essentials, the NIS2 Directive, DORA, and more.
October 05, 2023

Infographic
Technology Risk & Compliance
5 key areas for improved automation in InfoSec compliance
Streamline and scale your organization’s InfoSec compliance program by focusing on these five key areas of automation.
October 02, 2023

eBook
Technology Risk & Compliance
Prioritizing the right InfoSec frameworks for your organization
In this free eBook, we explore the basics of three top InfoSec frameworks and how to decide which is the best fit for your organization.
September 27, 2023

eBook
Privacy Management
Responsible data use: Navigating privacy in the information lifecycle eBook
Download this eBook and get the insights you need to safeguard customer privacy and ensure responsible data use in the information lifecycle.
August 22, 2023

Resource Kit
Technology Risk & Compliance
PCI DSS essentials: A resource collection for compliance
Achieve PCI DSS standard compliance with our comprehsive guide to safeguarding your organization's payment card data.
August 08, 2023

Data Sheet
Technology Risk & Compliance
Certification Automation: Managing PCI DSS compliance
See how OneTrust Certification Automation streamlines PCI DSS compliance by identifying controls and requirements with automation.
July 05, 2023

On-demand webinars
Technology Risk & Compliance
How to successfully implement ISO 27001 to demonstrate security and assurance across any jurisdiction
Join our live webinar and hear from security professionals on how to get ISO 27001 certified, streamline audit preparation, and demonstrate security assurance across any regulatory jurisdiction.
June 28, 2023

eBook
Third-Party Risk
InfoSec's guide to third-party risk management: Key considerations and best practices
Download our eBook to learn practical advice on how to approach third-party risk management like an InfoSec expert.
June 05, 2023
Data Sheet
Technology Risk & Compliance
Compliance Automation external audit management
Take a look at how OneTrust Compliance Automation can help streamline your preparation for audits, drive accountability, and track results.
May 16, 2023

On-demand webinars
GRC & Security Assurance
Combating InfoSec compliance fatigue: Insights for navigating growingly complex requirements
In this webinar, you will hear first-hand from information security experts experts what are the key pain-points and their strategies to be audit ready.
February 27, 2023

On-demand webinars
Technology Risk & Compliance
Introducing OneTrust Certification Automation: Build, scale, and automate your InfoSec compliance program webinar
In this webinar, learn how to right-size your compliance scope for different frameworks across various business dimensions and enable an agile audit process.
February 15, 2023

On-demand webinars
GRC & Security Assurance
Introducing OneTrust Certification Automation: Reinforce privacy accountability with automated InfoSec compliance
Learn how to enable an agile audit process by breaking down complex InfoSec requirements into actionable tasks to help automate your compliance program.
February 10, 2023

Infographic
Technology Risk & Compliance
ISO 27001: Global changes and impact to your compliance program
This infographic will explain how the updates to the ISO 27001 framework will have a huge impact on information security programs across all industries.
December 14, 2022

eBook
Technology Risk & Compliance
The future of information security
Learn how to respond to the security landscape and build a proactive InfoSec program to help your customers and business.
October 10, 2022

eBook
Technology Risk & Compliance
The art of the enterprise IT risk assessment
Ensure your enterprise IT risk assessment is a success with a top-down approach that gets executive buy-in from the start
September 16, 2022

eBook
Technology Risk & Compliance
The enterprise DevSecOps playbook
As a unified business function, DevSecOps combines rapid software development with top-notch security at scale.
September 02, 2022

On-demand webinars
GRC & Security Assurance
How to reinforce your InfoSec risk program in a “Not If, But When” incident environment webinar
Learn how scaling your approach to managing IT assets & risk assessments can deliver a complete picture to better measure and inform program investments.
August 16, 2022

On-demand webinars
GRC & Security Assurance
5 critical mistakes to avoid when answering security questionnaires
Avoid these 5 critical mistakes when answering security questionnaires and streamline responses with this webinar.
March 01, 2022

On-demand webinars
GRC & Security Assurance
How successful security teams manage risk to build Trust and drive Growth
Watch this webinar to learn what makes a successful risk management program and how effective security teams build trust.
January 12, 2022
Demo
Technology Risk & Compliance
OneTrust Tech Risk and Compliance demo
Manage tech risks and ensure compliance with our all-in-one solution. Automate workflows, scale resources, and measure program effectiveness to stay ahead of evolving regulations.

Infographic
Technology Risk & Compliance
The future of GRC: 10 drivers and trends
In this infographic, we cover the top 10 GRC drivers and trends that will impact the future of organizations, including fragmented internal data and systems.

Fundamental to Comprehensive: Where Does Your Compliance Program Stand? Infographic | Resources | OneTrust

On-demand webinars
Technology Risk & Compliance
Risk in 30'
Join our risk management webinar series to learn how AI, NIS2, and modern TPRM practices help teams reduce manual work and strengthen resilience.
