Despite being a voluntary framework, The National Institute of Standards and Technology Cybersecurity Framework (NIST CSF) has been adopted by organizations around the globe, with an estimated 50% of U.S. organizations using the standard as of 2022.
The popularity of the NIST CSF lies in its flexibility and ease of use. It was designed to help any size organization better understand, manage, reduce, and communicate their cybersecurity risks.
Its latest version, the NIST CSF 2.0, maintains this non-prescriptive and technology-neutral approach, while introducing additional guidance through profile templates, mappings, case studies, and other implementation resources.
This enables the framework’s application across a variety of use cases, from refining and enhancing well-established risk programs to building new cybersecurity initiatives from the ground up.
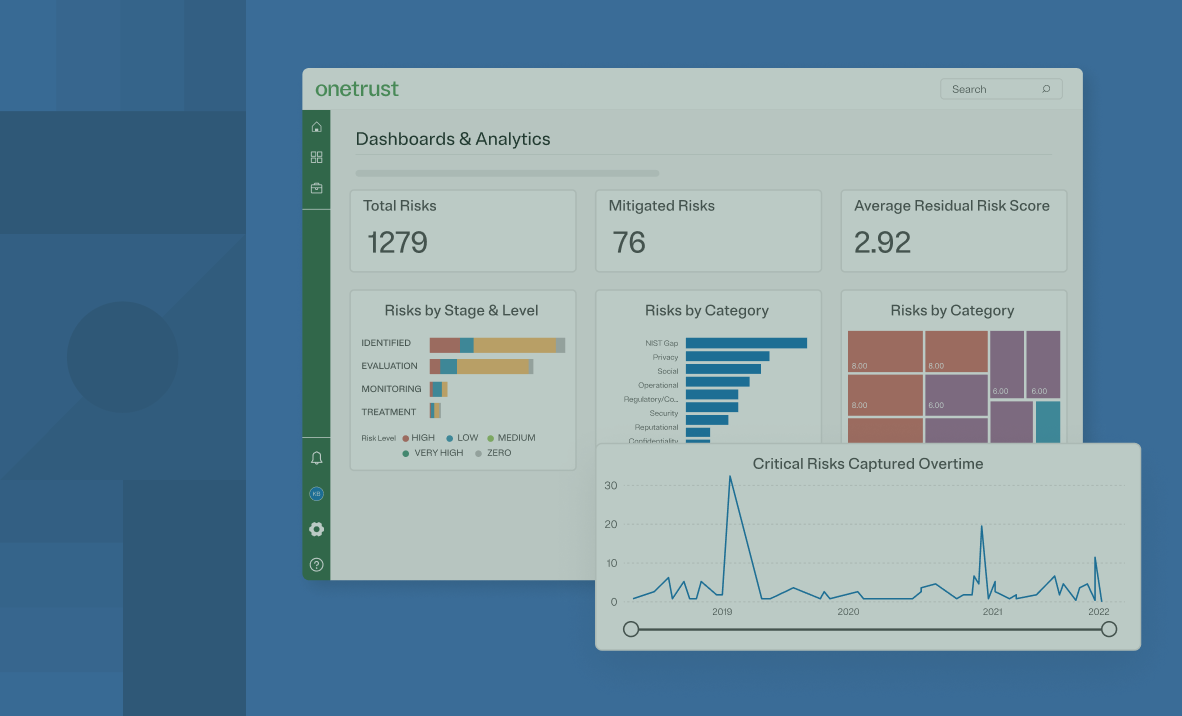
The NIST CSF has two common applications: for cybersecurity risk management and as a cybersecurity maturity assessment. While there’s no right or wrong approach — each one can bring significant benefits — it’s important to distinguish between the two and determine which best fits your organization's broader cybersecurity goals.