Building an effective privacy program is a long-term objective. With fast-changing regulations, the path to compliance is often a long-term project.
That said, there are two areas of your privacy program that require immediate action based on today’s regulations. First, privacy rights requests (DSARs) that enable consumers to exercise a privacy request in regard to their personal data, such as access, deletion, or rectification. Second, incident management processes to assess and mitigate data incidents that involve personal data as a result of unauthorized access or activity.
In several privacy regulations, regulators require a timely response from data holders in both instances. Due to media coverage, advocacy groups, the increasing scope of individuals covered under privacy regulations, and increased information sharing, consumers are becoming more aware of privacy rights and the ability to request the personal information an organization holds about them. As a result, the rate of DSAR inquiries will continue to grow, and privacy teams need to be prepared to act.
And with nearly 281.5 million people impacted by a data breach this year — a 17% increase over last year — the threat of global hacker activity is a tangible reality for all organizations that store and transact data.
Under either of these conditions, organizations need to be prepared to respond to DSARs and incidents quickly and effectively. Manual and semi-automated processes can no longer keep up with the complexity that’s required.
As a result, maturing privacy teams are turning to automation to scale DSAR and incident management efforts. They know the right tools will help them not only shorten their response timelines but also reduce the manual efforts and risk of human error when it’s most critical.
Step 1: Establish Effective Intake Methods for DSARs & Incidents
Preparation enables immediate action for both DSAR requests and incident reports. An effective intake method equips teams from day one with the necessary information to perform their compliance obligations at speed.
DSAR intake methods
Regardless of their current volume of requests, all privacy teams should create a system that centralizes DSAR intake management. This could look like a web form, self-service portal, or survey. In any case, all intake requests must flow into one location for efficient processing.
Any request that falls through the cracks presents a risk of non-compliance, so it’s important to build a system that helps mitigate this risk.
DSAR intake forms are typically public-facing and accessible online. But teams also have to be prepared to process privacy rights requests when they’re submitted elsewhere within the organization.
For example, consumers can send requests to an employee’s email or via posts on company social media. Organizations are required to review and process these. It may be useful to create an internal DSAR intake form to track and manage these types of requests alongside standard submissions.
Incident intake methods
When a data incident occurs — whether via hacker activity, through human error, or others — organizations need an intake strategy that enables privacy teams to assess the resulting compliance factors at stake.
To protect the process, organizations must provide a secure intranet that collects the necessary information to take action. The intake forms should be configurable to the incident type and align with requirements set by governing bodies.
It’s also essential that the incident intake approach centralizes the effort into one platform so teams can make comprehensive assessments under pressure.
Step 2: Create a Structure for Responses
Creating a structure for responses will also shorten the timeline for DSAR and incident management. While most organizations already have workflows in place, these often rely on manual tasks that increase the overall timeline and leave room for error.
If teams evaluate the steps within their response workflows, they’ll discover there are several opportunities to optimize them with automation.
Managing DSAR responses
Once a privacy rights request comes in, organizations typically have a required response time of between 15 to 45 days depending on the jurisdiction in scope. Automating DSAR response management is critical for privacy teams, as they’re becoming responsible for more DSAR resolutions than ever before. Therefore, it’s important that a robust workflow is in place so that the response to the DSAR request is efficient.
Your workflow will need to include the key steps required for completing requests, such as verifying the identity of the subject, discovering, and potentially redacting or deleting personal data in scope, checking for legal holds, communicating with the Data Subject as well as gaining any necessary internal approval. With different privacy regulations having different requirements, the flexibility of having different workflows depending on the type of request, location of the data subject, as well as other factors is necessary.
Having robust workflows in place certainly helps to make the response efficient. However, a workflow of complete manual steps risks creating time-consuming responses. This is why most organizations are now looking at what can be done to further automate.
Managing incident responses
No matter how small the incident, privacy teams must complete a full risk assessment before generating a response. This involves creating an incident response protocol that incorporates the right team members from the start.
Effective communication, role designation, and coordination are the keys to fast action — in addition to working with tools that generate intelligence about an incident based on applicable regulations.
Automation can power several connective steps to hasten incident response. This includes generating guidance based on each jurisdiction involved and streamlining the process of notifying affected individuals.
Step 3: Enhance DSAR and Incident Workflows With Automation
Workflows are a great first step in managing the response to both DSARs and incidents and provide a great “base”. However, manual or semi-automated workflows are not going to allow the most efficient response which is why the incorporation of automation where appropriate is key.
Automation in your DSAR workflows
Responding to DSAR requests can be a painstaking process, especially when it comes to the retrieval of a Data Subject’s Data. Data storage is often fragmented, and formats are often inconsistent, making it difficult to fulfill DSAR obligations in a timely manner. The look-up of an individual’s data is the area that is ripe for automation.
When an organization is equipped with a data inventory that unifies data sources and types, privacy teams are better equipped to fulfill their compliance obligations for privacy rights requests. Once you know what systems hold relevant data, you can perform targeted searches on those systems, regardless of if the data is structured, unstructured, hosted in the cloud, on-premises, within a SaaS platform, etc. A unified data inventory is an invaluable asset that will help teams continue to scale their DSAR processing volume over time.
OneTrust Data Discovery gives you the most efficient and lightweight method to conduct these targeted scans of systems. The OneTrust solution takes a surgical approach to finding data directly correlated to the requestor so that time and resources are maximized in the search and collection of personal data.
DSAR and incident management are critical activities that will only continue to increase in importance in the short term. The key to managing them effectively under critical timelines is automation.
Further ways to automate DSARs
Finding the individual’s data is not the only way teams can automate. Validating DSAR inquiries requires striking a balance. To manage risk, privacy teams must avoid asking for more personally identifiable information than they already hold. But verifying identity is still essential to the process.
Integrations with customer databases and identity validation technologies help to simplify identity verification. It’s also possible to validate a requestor’s identity through automated data discovery. By scanning enterprise-wide for requestor information such as email, phone, and logins, privacy teams can significantly shorten the ID verification process.
Furthermore, DSARs include many request types, including the right to access and the right to be forgotten. Depending on the nature of the request, teams must retrieve the requested data, then redact it, provide it to the requestor, and/or destroy it.
Targeted Data Discovery automates the effort from discovery through deletion for DSARs and CCPA opt-out requests. The technology takes a surgical approach by retrieving data from relevant systems and fulfilling requirements by jurisdiction and request type. This helps teams respond effectively — and fast — as request volume grows.
Automation in your incident management workflow
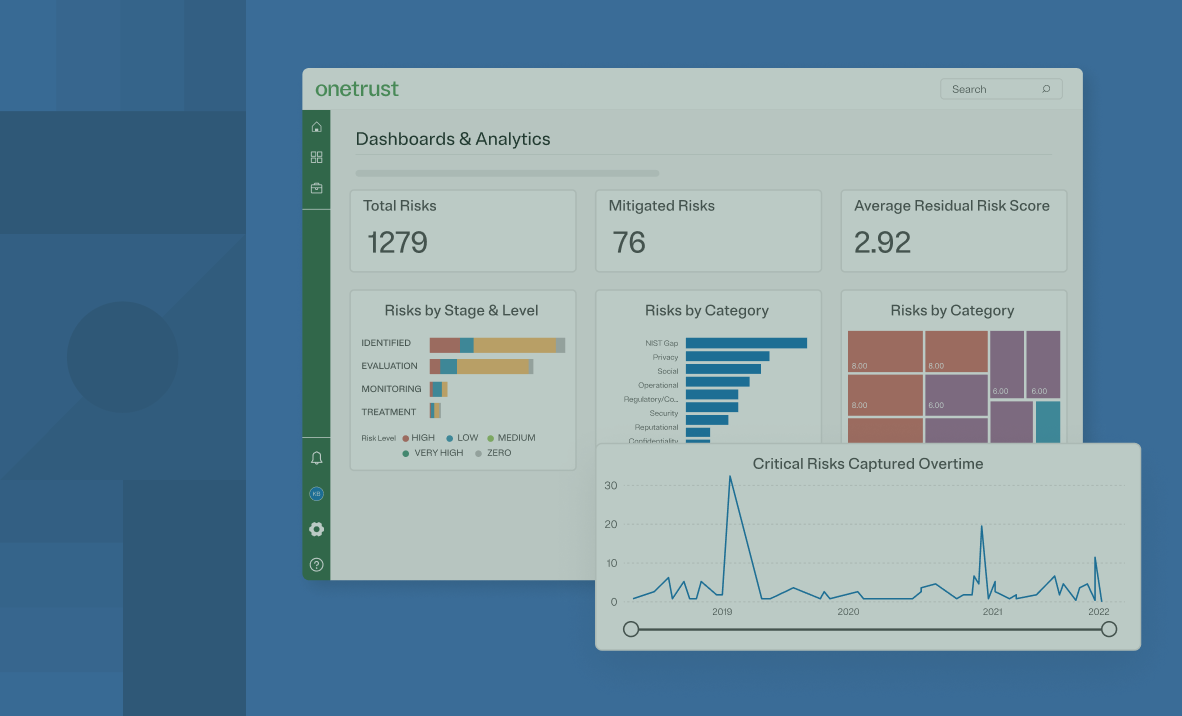
When an incident occurs, compliance isn’t the only issue at stake. 50% of consumers are more likely to trust companies that respond quickly to data incidents. To maintain or regain ground, it’s incumbent on privacy teams to create a clear picture of the type of incident and how many people were affected in a short amount of time.
An effective Data Map helps with the categorization of what data you hold in your systems and of whom is going to allow you to immediately understand the scope of the incident. Building up a map of this data that has the level of detail required to make this analysis can only truly be achieved through automated data discovery. OneTrust Data Discovery allows organizations to understand the types and classifications of data they hold on data systems right down to the individual column or file level. This builds up an accurate map of your data, its exact locations, as well as other required details.
Once you build up this Data Map, in the case of a breach or incident you are able to immediately understand the impact in terms of what data and end-users have been affected. From here, the next stages of the incident resolution, as well as analysis of the root cause and what happened, can be achieved more effectively.
Completing this work through automation frees up the capacity for the incident management team to take action to avoid future incidents of a similar nature. This is particularly helpful in the case of a major incident or if the team has to notify impacted customers, vendors, and other stakeholders of the incident details.
How OneTrust Can Help
OneTrust Privacy Rights Management automates privacy requests from intake to fulfillment. Our solution enables privacy teams to scale their DSAR processing efforts with time-saving automation workflows that:
- Streamline the intake process with templates based on CCPA, GDPR, LGPD, and others
- Simplify identity verification with various validation approaches and customer database integrations
- Fully automate requests with Data Discovery to verify and fulfill requests across the IT ecosystem
- Automate sensitive data redaction using AI and manage in a single dashboard
OneTrust Incident Management provides automated workflows to manage the complete incident lifecycle. Our solution cuts down on manual processes and speeds up the completion timeline. Features include:
- Improved visibility into incidents with configurable intake forms and dashboards
- Simplified investigations with rule-based workflows that scan for severity
- Guidance analysis based on multi-jurisdictional factors
- Streamlined notification management for impacted parties
Find out how your privacy team can benefit from our easy-to-use tools. Request a demo today!