More Data, More Problems
Acknowledging the problems that massive amount of data poses to your organization is going to be step one in proper classification.
Problem 1: Lack of visibility into a growing dataset
Your organization collects and generates a massive amount of data across different systems in a variety of forms. Before you can establish and enforce policies to promote usability, secure data, and maintain compliance, you must understand what data you have and WHY you have it.
Problem 2: Need to reconcile data risk and reward
Because of this relationship, you’re always on the hunt for technology that helps your business understand the data it has, the risks it poses to the business, external requirements (compliance) related to data, as well as the internal initiatives and expectations related to it.
Problem 3: Time to market
Your business needs to be able to find sensitive data, highlight where it lies, and be able to quickly take remediation efforts in the event of a security incident.
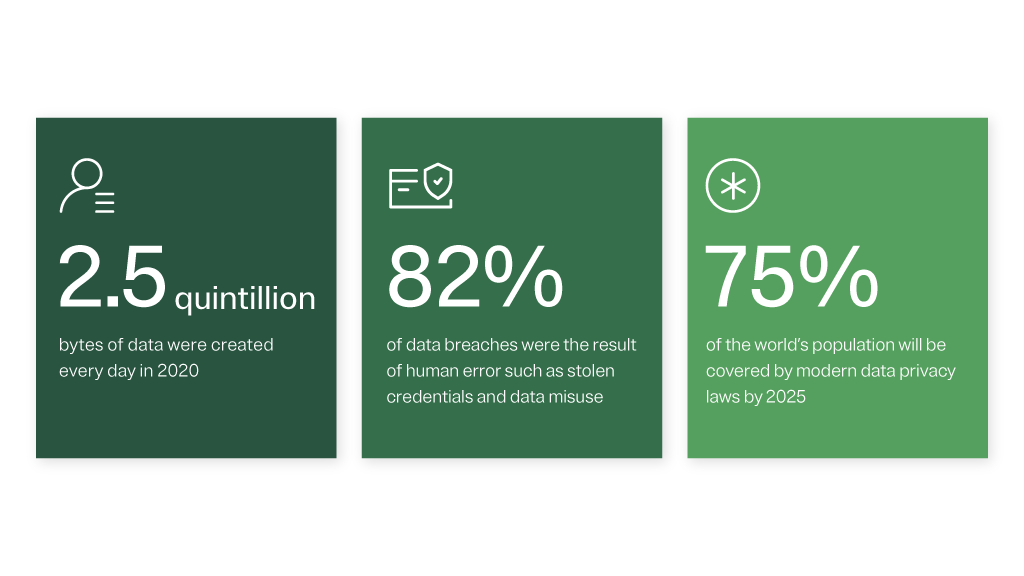
The average volume of data held by an enterprise grew by 42% last year. One of the biggest challenges stemming from this explosion of data is insider access. Does your company know how to monitor and manage this type of data sprawl? Join this webinar to learn more.
What Is Data Access Governance?
The key objective of data access governance is to gain visibility into risk and enforce data access policies. Data access management has evolved into an independent initiative that requires an autonomous strategy, budget, and implementation schedule. Data access governance covers many crucial areas, including data security; protecting PII; providing access to critical data assets; and managing permissions.
What Is Dark Data?
Dark data is the information assets an organization collects, processes, and stores during regular business activities, but generally fails to use for other purposes. For example, dark data could come in the form of analytics, business relationships, and direct monetization.
Who Is a Data Citizen?
A data citizen is an employee who is given access to an organization’s proprietary information. Use of the word “citizen” is meant to emphasize the idea that an employee’s right to access corporate data also comes with responsibilities.
What Is a Data Estate?
A data estate is simply the infrastructure to help companies systemically manage all their owned corporate data.
What Is Data Minimization?
Data minimization is a principle that states data collected and processed should not be held or further used unless this is essential for reasons that were clearly stated in advance to support data privacy.
What Is Data Security Posture Management?
Data Security Posture Management (DSPM) is an emerging market focused on reducing risk and improving the security around an organization’s most valuable asset – its data.
What Is Data Sprawl?
Data sprawl is the proliferation in the number and different kinds of digital information (data) created, collected, stored, shared, and analyzed by businesses, primarily at the enterprise level. On average, organizations have four-to-six platforms to manage data.
What Is ROT Data?
Redundant, obsolete, or trivial (ROT) data is the digital information a business has despite the data having no business or legal value, i.e. a duplicated piece of information or data point that doesn’t help the company in any positive way.
In order to cull and manage ROT data, your business needs a data retention and deletion strategy. Join this webinar for tips and best practices on ensuring ROT data isn’t hindering your business.
Shift Left: A Data Classification Strategy
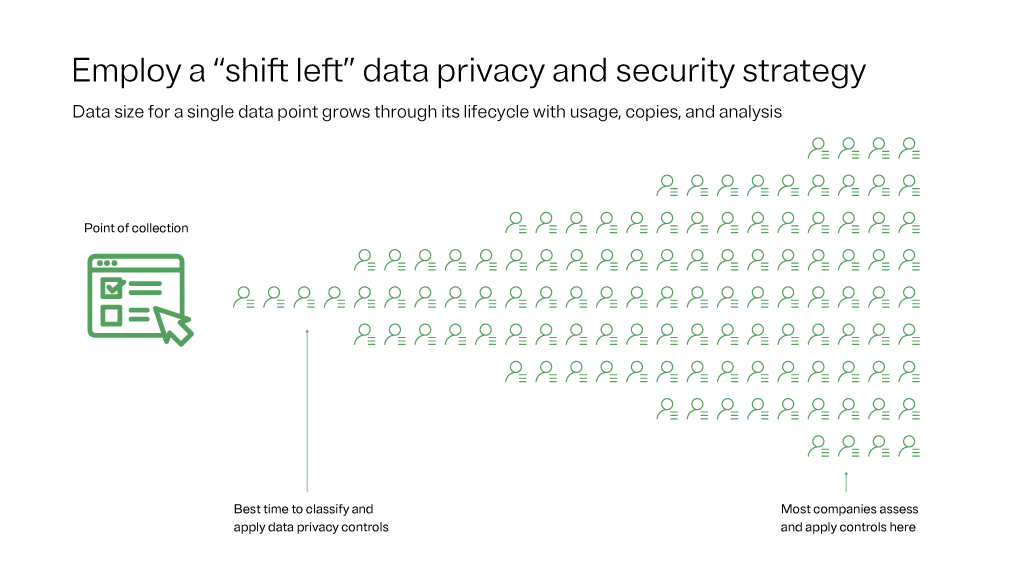
Data discovery has as much to do with classifying its whereabouts and importance as it does what actions should ultimately be taken with that digital information. Forward-looking security should be employing the shift left strategy. But what exactly does that mean?
Shift left is a philosophy that looks at data ingestion at the left side of a horizontal funnel (see image). According to IAPP, that narrow end represents the point when data first enters the company’s tech ecosystem. As you move right in the funnel, the amount of data grows with copies, inferences, and data analysis. The point of collection is best suited to classify and inventory data, creating downstream efficiencies. Most companies classify and inventory data toward the right side of the funnel, which is a recipe for delays, inaccuracies, and potential security incidents.