More and more companies are outsourcing key business activities to third parties. However, these third parties can present a significant risk to your organization if not handled with care. We’ve seen the results of unsecure third parties in recent data breaches, and it’s important to be proactive in mitigating future security risks. To do this, it’s important to assess your third parties against risk in a way that’s cost-effective, time-friendly, and low-effort for your vendors. The Shared Assessments Standard Information Gathering (SIG) assessment does exactly that.
What Are the SIG Core and SIG Lite Assessments?
The Shared Assessments Program, managed by The Santa Fe Group, focuses on third-party risk assurance by helping organizations manage third-party risk, cybersecurity controls, IT, privacy, data, security and business resiliency. The two assessments central to the Shared Assessments Program are the SIG Core, and the SIG Lite.
SIG Core: The Standardized Information Gathering (SIG) Core questionnaire is designed to assess third parties that store or manage highly sensitive or regulated information, such as payment card information or genetic data. This tool is meant to provide a deeper level of understanding about how a third party secures information and services. It is meant to meet the needs of almost all third-party risk assessments, based on industry standards.
SIG Lite: The SIG Lite questionnaire is designed to provide a broad, high-level understanding about a third party’s internal information security controls, along with other risk domains, such as privacy and ESG. This level is for organizations that need a basic level of assessment due diligence. It can also be used as a preliminary assessment before a more detailed review.
What’s New in 2022?
The 2022 SIG contains direct mappings to eighteen of the most critical reference documents across industries in the body of the SIG, along with content from the SIG library and the SCA. The SIG directly maps to:
- Cloud Security Alliance (CSA) Cloud Controls Matric (CCM) v.4.0.1, 2021
- CSA Consensus Assessments Initiative Questionnaire (CAIQ) v.4, 2021
- EU General Data Protection Regulation (GDPR) 2016/679, May 2018
- European Banking Authority Guidelines on Outsourcing Arrangements, Feb 2019
- Federal Financial Institutions Examination Council’s (FFIEC) IT Examination Handbook: Revised Business Continuity Management Booklet, Nov 2019
- FFIEC Cybersecurity Assessment Took (CAT) May 2017
- FFIEC IT Examination Handbook: Management, Nov 2015
- HHS HIPPA Administrative Simplification, March 2013
- International Standards Organization
- (ISO) 27001 and 27002:2013
- ISA 62443-4-1
- ISA 63443-4-2
- ISO PIMS, Aug 2019
- Nat’l Institute of Standards and Technology (NIST) Cybersecurity Framework, April 2018
- New York State Dept of Financial Services (NYDFS) Cybersecurity Requirements for Financial Services Companies 23 NYCRR 500
- NIST Privacy Framework: A Tool for Improving Privacy Through Enterprise Risk Management
- NIST SP 880-53 r5, Security and Privacy Controls for Federal information Systems and Organizations
- PCI DSS 3.2.1, 2018
- Shared Assessments Standardized Control Assessment (SCA) Procedures
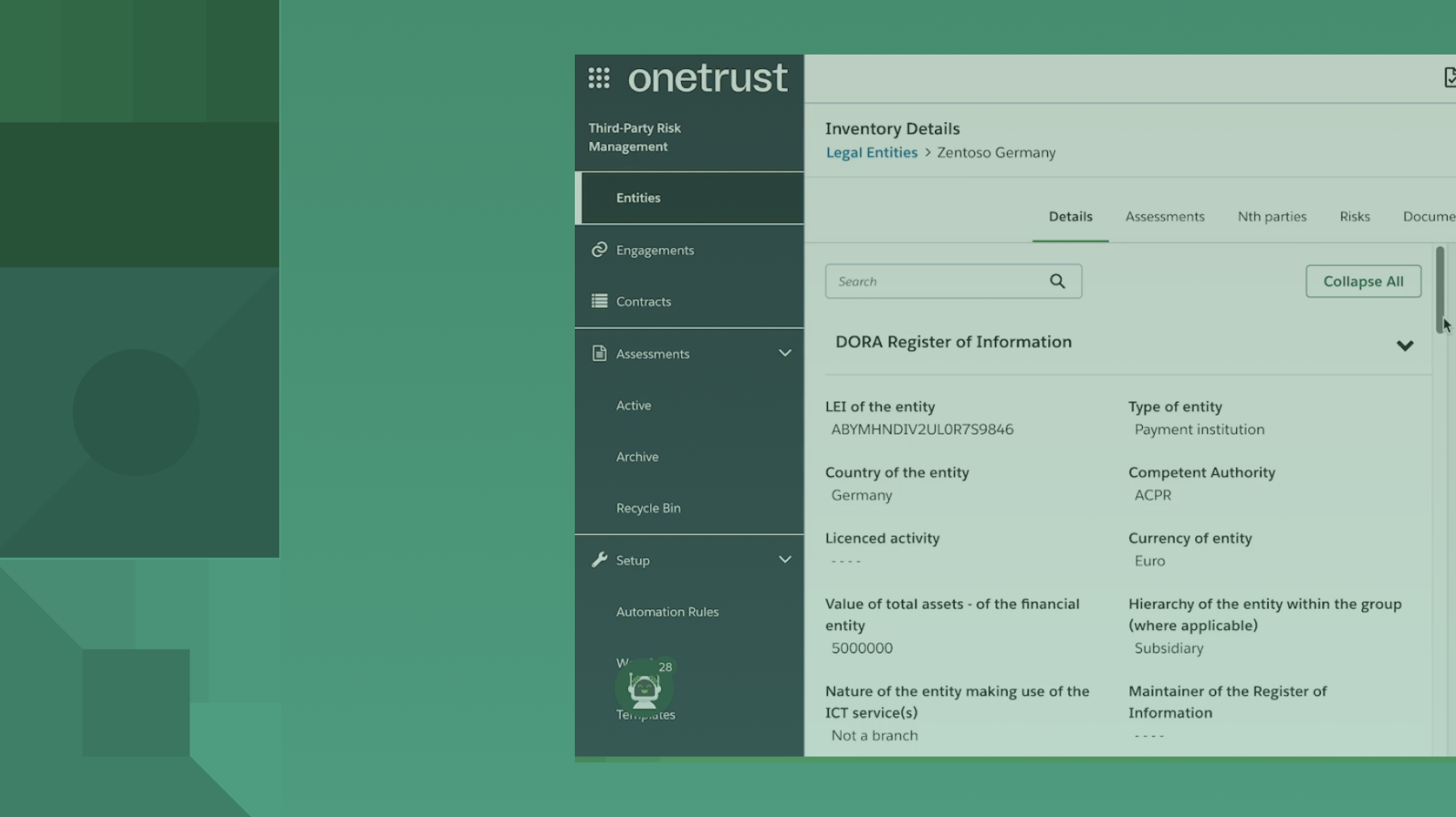
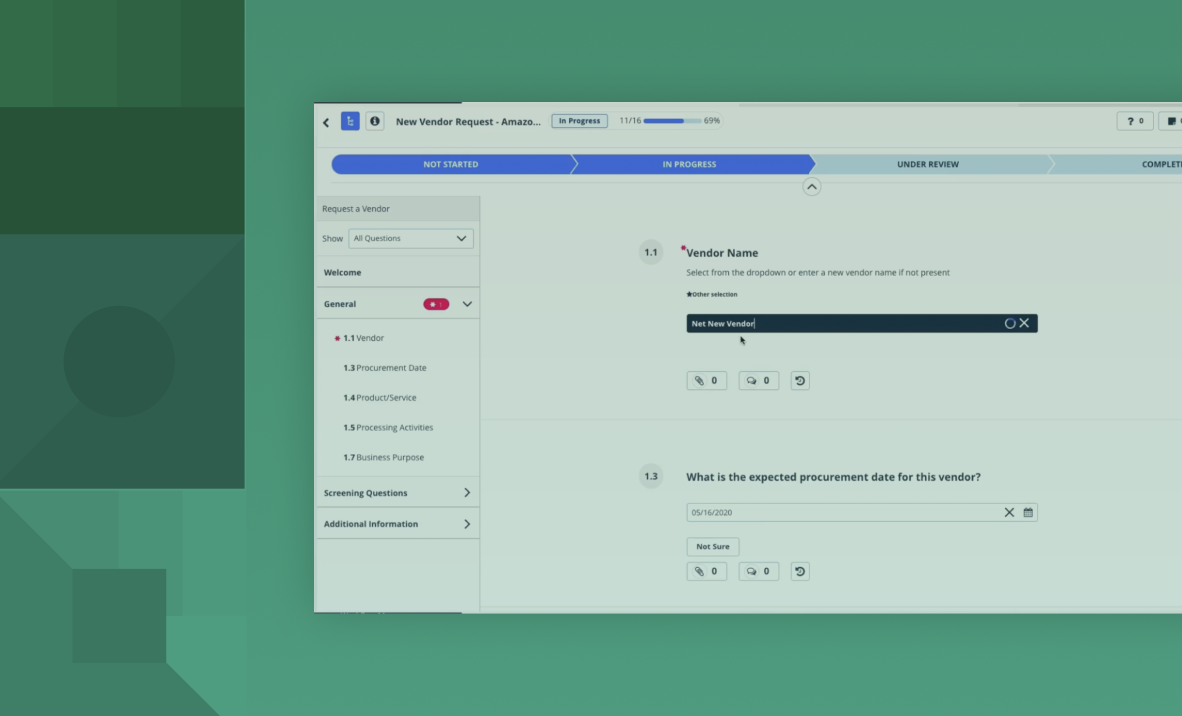
How OneTrust Can Help
OneTrust Vendorpedia offers same-day support for both the 2022 SIG Lite as well as the SIG Core.