You can’t launch a third-party risk management (TPRM) program and expect it to protect your organization forever. New cybersecurity risks emerge every day and your third-party ecosystem and relationships will evolve.
Gartner estimates that 45% of organizations around the globe will have experienced an attack on their digital supply chains by 2025. To safeguard against these attacks, organizations need responsive security measures that keep pace with changes in the threat landscape.
When it comes to TPRM programs, maintenance is as important as the development itself. By keeping its third-party processes up-to-date, organizations can stay ahead of potential issues and minimize any negative impact if they do occur.
We asked six InfoSec and third-party risk leaders from OneTrust and Fortune Global 500 companies on ways to best maintain a TPRM program, as well as how they typically report results to leadership. This is the last post in our series on building a TPRM program.
Download our InfoSec's guide to third-party risk management, which covers all the steps in setting up a TPRM program, from planning to monitoring and reporting.
How Do You Monitor Third-party Risks?
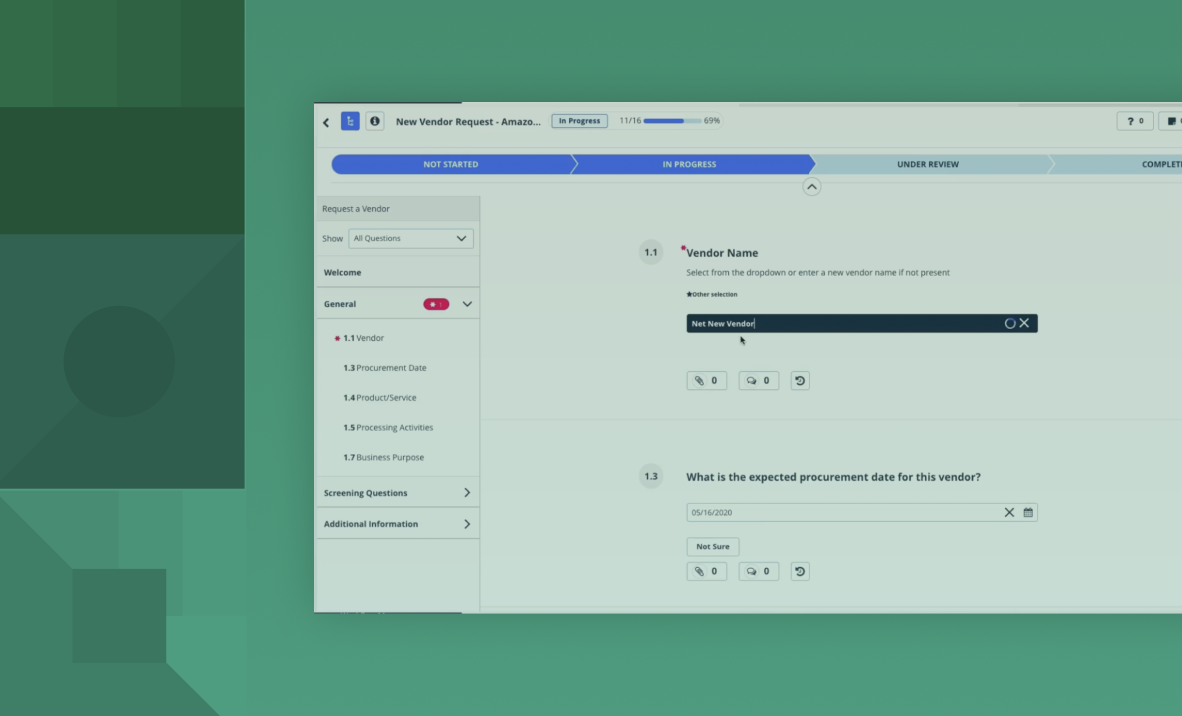
Most third parties are in the ongoing monitoring stage of the TPRM lifecycle. Even if they pass their initial assessment with flying colors, it’s only a snapshot of the third party’s current state — ongoing monitoring is still necessary to mitigate risk throughout the entire relationship.
Third-party monitoring is typically facilitated by an automated risk monitoring tool, and should include a step-by-step plan to address any security alerts and determine the necessary actions for every issue.
“Even after a vendor is onboarded, you need to plan your monitoring process and workflow in case an issue comes up. Say something happens related to environmental, social, and governance (ESG) — who's handling that? It’s not a security issue. If you define roles and responsibilities ahead of time, then you’ll know the next steps,” says Kevin Liu, Sr. Director of Information Security at OneTrust.
“When I see an alert, I make sure to assess and understand it first because not every single alert is equal. Go through the list of what you’re monitoring for — the security posture, the social governance aspect, the financial health in some cases, and so on.”
If an alert needs to be addressed, teams should get in touch with the third party to further investigate and limit any potential threats. This can involve turning off the third party’s access and requiring status updates as they work through their corrective action plan. Only when the third party can provide evidence that the issue has been resolved should an organization grant access back into their internal systems.
Maintain a TPRM Program
The key to maintaining a TPRM program is being responsive to any changes in your third-party environment or risk landscape.
“If you're doing the same business as you were last year and nothing's really changed, you might not need to do any active maintenance,” says Tim Mullen, Chief Information Security Officer at OneTrust. “Of course, if there’s something new in the market — a new vulnerability, new zero day, something that’s piquing our interest — that can prompt a change.”
The following questions can help guide your routine maintenance process:
- Did you engage in a new third-party contract?
- Are you sharing different types of data?
- Are there any potential new risks identified by the organization?
- Have you started a new line of business?
- Did you engage in any mergers and acquisitions or asset sales?
“Another common thing that happens is you sign on a vendor and then the scope changes. For example, you could have implemented a new functionality and then all of a sudden, a vendor that was low risk now has access to highly sensitive data,” says Jose Costa, Sr. Director of GRC Labs & Research at OneTrust. “Even little changes in vendor relationships should go through another assessment process.”
In most cases, you should revisit your TPRM program once a year. The goal of reassessing TPRM processes is to not only maintain security, but also continue maturing your program.
“Don’t just assess TPRM — assess everything that touches it. What's your policy related to vendor management? Are there issues the organization identified related to this vendor or even another vendor in the same category? Bring in any relevant information and assess your TPRM program holistically to see how to move forward,” says Liu.
Report TPRM Program Performance to Management
Reporting on the performance of your TPRM program is different for every organization.
Depending on the maturity of your program and what matters most to management, any number of the following metrics can be included:
- Total number of third parties assessed
- How long it takes to assess third parties
- Distribution of third parties across low, medium, and critical tiers
- Overall level of risk exposure introduced by third parties
- Volume of issues associated with third parties (over a period of time)
- Average remediation period
- Any overdue risk mitigation activities
“If you're just starting to implement a TPRM program, you may report how many vendors have gone through the process, how many are compliant, etc. Or you may report the major risks you’ve assessed, how you mitigated them, and how you plan to evaluate them on a regular basis,” says Costa. “It really depends on what management wants to see, but I would keep it high-level and at least make sure 100% of my vendors, irrespective of the size and complexity, go through the process and that the process is working.”
As the program matures, management will want to see the actual impact of your TPRM efforts and how they lead to lower risk. This requires finding ways to meaningfully quantify the change in third-party risk levels and highlighting that in your reports.
“In information security, there are very rarely precise and actual estimates of real risk. So we have to look for indicators of risk, proxies for risk, or even more lagging indicators of the actual number of incidents,” says Matthew Solomon, VP of Technology and Cyber Risk Management at Humana. “In terms of showing the actual impact of the program, the trick is really to get as close to the quantification of your risk level as you can and how you're driving that down.”
Lower Risk Levels With TPRM
Regardless of where you are along your TPRM journey, the end goal is to see lower risk across your organization. This can be achieved by actively monitoring security alerts, addressing any potential issues, and periodically reviewing your program for any significant changes or updates. Finally, show the result of your team’s efforts by quantifying third-party risk levels and highlighting the actual risk impact of your work.
Reduce risk, build trust, and enhance business resilience by unifying third-party management across privacy, security, ethics, and ESG. Book a demo today.