Governance, risk, and compliance (GRC) has grown in depth and breadth in recent years, with a variety of specialized activities designed to protect today’s businesses.
Cybersecurity, third-party risk, and other policies fall under the GRC domain, with the total software market worth projected to reach $134.86 billion by 2030.
As the landscape continues to evolve, GRC practices will go beyond simply meeting compliance objectives. Insights from governance and risk management will also play a significant role in the strategic compliance decisions made across industries and businesses.
Taking a holistic, horizontal approach can strengthen your organization’s security posture against potential cyberthreats and data breaches.
What else can you expect from GRC in the coming year? Below, we outline the top 10 emerging drivers and trends that will shape the way security compliance is achieved moving forward.
Drivers
The fast rate of change within GRC shows no signs of slowing down, with businesses dedicating more time and resources to their compliance programs. We break down the five main drivers prompting this shift to greater security compliance:
1. Change is the only constant
As the InfoSec landscape evolves, it’s the responsibility of each organization to maintain regulatory compliance. This requires being aware of all updated regulations and emerging risks.
For example, a new version of the Payment Card Industry Data Security Standard (PCI DSS) was released last March 2022 and takes full effect in March 2025. Impacting all entities that process, transmit, or store cardholder data, the PCI DSS 4.0 introduces 64 new regulations that cover how online payments are processed and secured.
2. Growing extended enterprise
Companies today are increasingly dependent on third parties and fourth parties to provide mission-critical services. Whether it’s payroll processing or managed web hosting, every outsourced service comes with greater regulatory and risk exposure. To mitigate the risks created from an expanding network, organizations need ways to optimize their tech stack and have deeper visibility into their vendors.
3. Fragmented internal data and systems
While most organizations naturally operate within teams and departments, the siloed structure results in disconnected data stored across separate systems. This increases the likelihood of duplicate security controls and policies and makes it unnecessarily complicated to collect the evidence needed for framework compliance. In time, fragmented systems hinder a company’s audit progress and weaken overall security posture.
4. Need for redefined GRC platforms
Every day, we hear about new IT risks and cybersecurity threats. Unfortunately, the GRC platforms of the past can’t keep up with today’s fast-changing environment. Many older solutions still require ad-hoc coordination and manual processes that lead to duplicative evidence collection, employee fatigue, and higher compliance costs.
5. Need for external GRC content
GRC platforms that identify risks without any context can only offer limited advantages. They provide a basic structure to house your data, but not much else beyond that. Organizations have a growing need for additional risk and compliance content that gives a broader view of ongoing compliance efforts and maps control frameworks to overall objectives.
Trends
The journey to security and compliance is never done. The five trends below help future-proof your GRC program and ensure your company stays ahead of upcoming risks and compliance changes:
1. Interconnected GRC architecture
As organizations move more data to the cloud and application infrastructures, GRC architecture is quickly adapting to address the interconnected risks, including dynamic risk and control mapping that emerge from the growing network of systems and operations.
2. Pre-built automated integrations
GRC integrations have historically been a burden to scope, build, and maintain. The most effective platforms will offer pre-built integrations that enable companies to instantly access and share data across systems, automate evidence collection to reduce duplicative work, and send real-time alerts for any security anomalies.
Leverage 100+ integrations to automate evidence collection and flag posture alerts.
3. Better together technologies
The most efficient GRC platforms will provide integrated security expertise and a central roadmap to achieve regulatory compliance. Expert-vetted guidelines help define InfoSec policies, identify control gaps and overlaps, and manage security programs all the way through your internal and external audits.
4. Business engagement
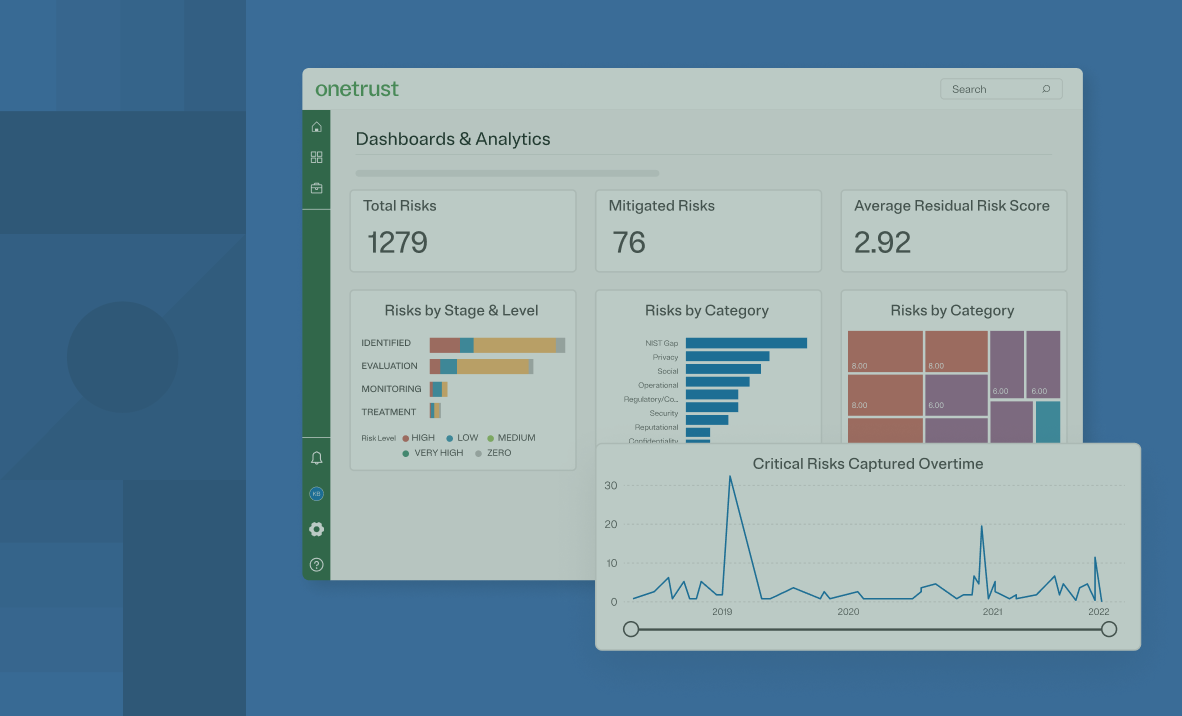
The rise of risk culture within enterprises creates a corresponding demand for greater visibility into existing security postures. Today’s GRC solutions will automatically map risks and controls to regulatory frameworks and help fast-track audit projects with ongoing oversight for internal and external stakeholders.
5. GRC mobility and engagement
With the increased reliance on software applications and changes in regulatory frameworks, organizations need a new approach to GRC compliance. Solutions that combine compliance content, automation capabilities, and expert guidance can bridge the gap between strategy and execution. Bringing all data into a centralized portal or interface that’s supported on mobile devices delivers a more intuitive user experience that’s easily accessible to the business.
About OneTrust Compliance Automation
OneTrust Compliance Automation helps you navigate changes within the information security landscape and stay ahead of compliance requirements.
With simplified security standards, automated scoping wizards, and a proprietary shared evidence framework, our integrated platform can fast-track your audit process enable you to test once, comply many.
Reduce your cost of compliance up to 60% and obtain certifications 50% faster.
Download our 10 GRC drivers and trends infographic, which you can use as a reference to build and scale your own security compliance program.