“Start small with a minimum viable product, something that can improve the security posture right here, right now.”
—Zuzana Rebrova, Head of Third-Party Cyber Risk Management, Swiss Re
Create a TPRM program that addresses your organization’s highest security risks and aligns with strategic objectives
Katrina Dalao
Sr. Content Marketing Specialist, CIPM
July 11, 2023

Working with third parties is nothing new for most organizations. By the time leadership decides to start a formal third-party risk management (TPRM) program, there’s often multiple third-party relationships already in motion. This makes it challenging to create a TPRM program that addresses all vendors, suppliers, and third parties — each posing its own unique risks to the organization.
To help navigate the winding road of third-party risk management, we spoke with six InfoSec and third-party risk leaders from OneTrust and Fortune Global 500 companie about their approach to building a TPRM program and the lessons they learned along the way.
Whether you’re working with one or 1,000 third parties, establishing a TPRM program follows these general steps:
In this post, we cover the first step of building your TPRM program: Scoping your program and getting leadership buy-in.
Download our InfoSec's guide to third-party risk management, which covers all the steps in setting up a TPRM program, from planning to monitoring and reporting.
While every TPRM manager wants a program that actively mitigates all third-party risks, the reality is that not all relationships need to be evaluated at the same level. It takes significant resources to perform security checks, risk reviews, and other due diligence tasks — which aren’t always available, especially at the start of a TPRM program.
Defining your program scope helps establish clear boundaries, deliverables, and timelines, and keeps the focus on efforts that deliver the highest value.
“There are a lot of considerations, but early on, you're trying to knock out the low-hanging fruit and figure out your risk exposure based on the partners you have,” says Tim Mullen, Chief Information Security Officer, OneTrust. "We’re going to have a lot more rigor when it comes to reviewing a security or financial services vendor versus a vendor that provides us with something like paper towels or toilet paper.”
Use these questions to help set the scope for your TPRM program:
“Start small with a minimum viable product, something that can improve the security posture right here, right now.”
—Zuzana Rebrova, Head of Third-Party Cyber Risk Management, Swiss Re
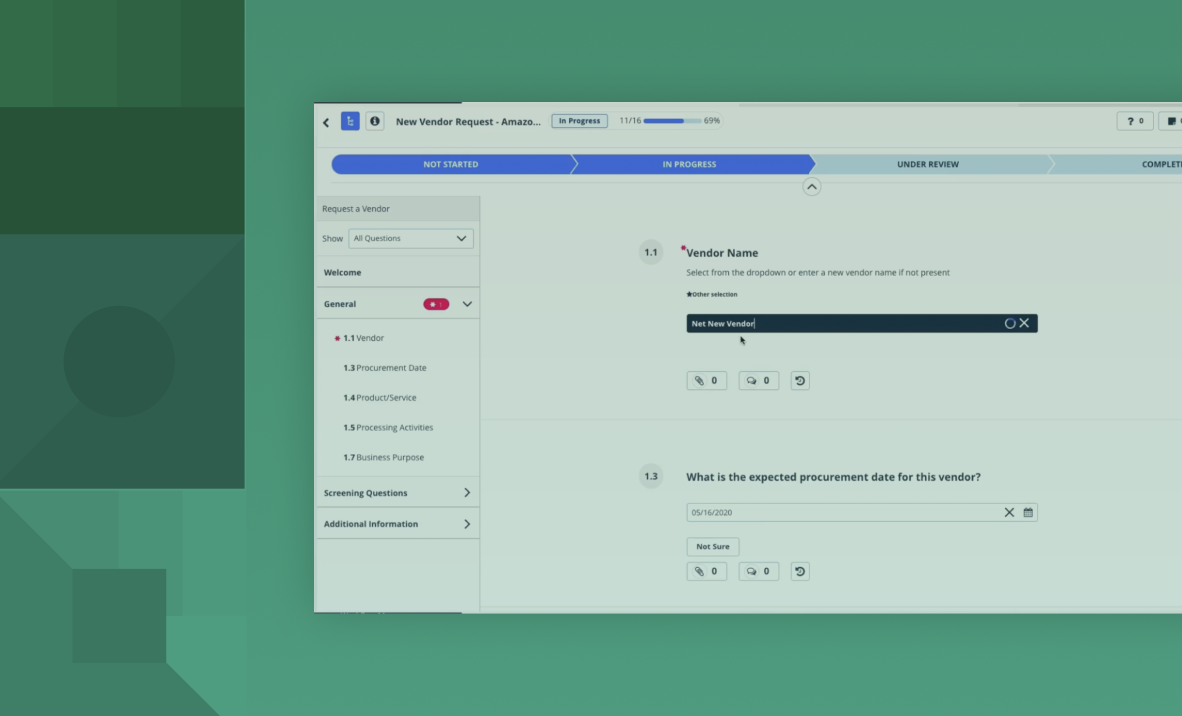
Next, take inventory of your current suppliers, contractors, partners, and other vendors, and determine which of the third parties will be included in the scope of your TPRM program.
The following questions can help determine if a third party is in or out of scope for your TPRM program:
This inventory serves as a single source of information and helps organizations better categorize third parties according to risk. Therefore, it’s important to update third-party inventories with any new, terminated, or revised vendor contracts.
“Third parties are just another asset you're trying to manage. And with any asset, there’s always a level of risk or a threat that comes with it,” says Kevin Liu, Senior Director of Information Security at OneTrust.
“Identify third-party risks and understand their potential exposure and impact to the organization. Then, once you have those things, you can create an assessment process and assign a criticality to the third party.”
Once the scope and other details are defined, it’s time to present the TPRM program to the leadership team.
Learn everything you need to know about third-party risk management in this guide that covers best practices, the TPRM lifecycle, and more.
All the experts we interviewed aligned on one universal tenet: Getting buy-in from leadership is critical to the success of your TPRM program.
“Start from the top. Management needs to understand that third-party risk really matters, what the impact could be, and how it could affect the company,” says Zuzana Rebrova, Head of Third-Party Cyber Risk Management at Swiss Re.
This involves presenting the program objectives and strategies for achieving them, as well as the business case for how a TPRM program effectively protects the organization against risks and potential losses.
Whether it’s the board, C-suite, or other key stakeholders, having top-level support goes a long way in fostering a risk culture. Leadership can not only champion the program, but also help establish governance for how TPRM activities integrate into day-to-day operations.
“The more you coordinate and socialize your intended outcome with the leaders and stakeholders in the organization, the more you’re able to set resource levels, measure whether you're actually achieving the value you want, and structure your program accordingly,” says Matthew Solomon, VP of Technology and Cyber Risk Management at Humana.
Ultimately, TPRM is an organization-wide exercise requiring involvement from multiple teams. While InfoSec or compliance typically oversees TPRM, anyone who deals with third parties — including privacy, procurement, finance, and legal — needs to be aligned and in agreement with the program.
Taking the time to plan your third-party management program sets you up for success in the long run. The best way to start your TPRM program is to get leadership and stakeholder buy-in early on and then define the program scope in a way that mitigates the highest risks and aligns to strategic objectives.
Reduce risk, build trust, and enhance business resilience by unifying third-party management across privacy, security, and compliance. Book a demo today.
Leadership buy-in helps secure the budget, resources, and cross-functional alignment necessary to operationalize third-party risk management across departments. Without executive support, TPRM initiatives often lack the visibility and authority to influence procurement, IT, and compliance decisions.
Organizations can show value by quantifying vendor risk exposure, tracking remediation timelines, and linking TPRM outcomes to reduced incidents and improved compliance posture. Data-driven reporting and benchmarking help communicate progress and reinforce the ROI of continuous vendor monitoring.
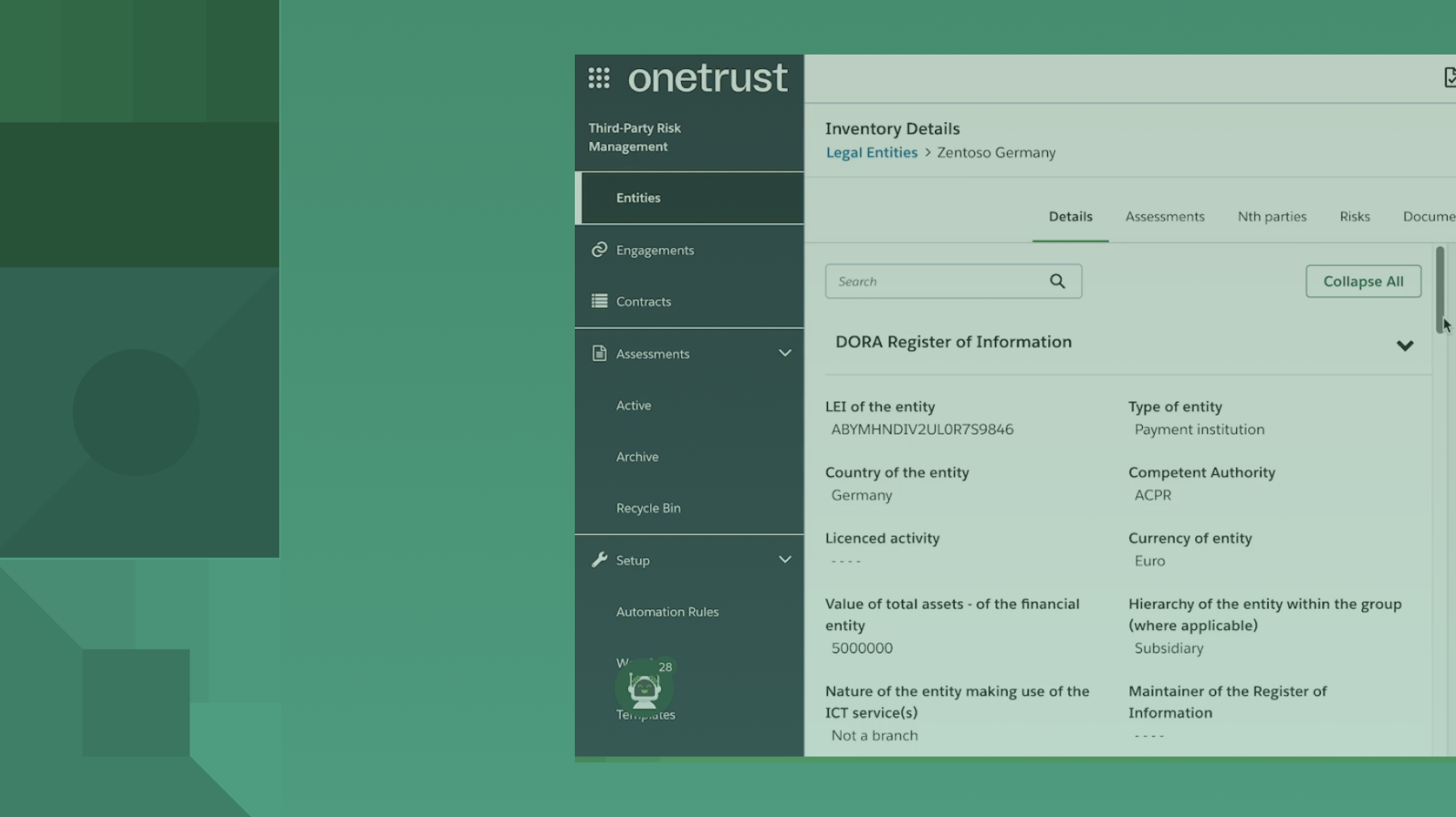
Frameworks like the GDPR, DORA, and ISO 27001 require organizations to assess and monitor third-party risks to safeguard personal and operational data. These regulations emphasize accountability and due diligence in managing vendor relationships, making structured TPRM programs essential for compliance.

Upcoming webinars
Join OneTrust’s fireside chat to learn why ISO 27001 is the baseline for modern governance and how to move beyond certification to scalable risk management, AI governance, and board-ready security programs—register now.

Upcoming webinars
Learn how to turn AI governance principles into action with this live webinar. We will discuss how organizations can operationalize AI governance, manage AI risk, and oversee third‑party AI to meet evolving regulations.

On-demand webinars
Discover how OneTrust aggregates and contextualizes risk data, models business and technical impact, and delivers board-ready dashboards that translate technical risk into clear, executive-level decisions.

On-demand webinars
Learn how leading teams move from reactive compliance to lifecycle-embedded governance — enabling better communication of AI risk to executives, stronger oversight, and measurable business value.

On-demand webinars
Learn how OneTrust enables structured, transparent risk scoring by standardizing questionnaires, distinguishing inherent and residual risk, creating explainable scores, and turning risk data into actionable business insights.

eBook
Today’s enterprise operates across clouds, SaaS ecosystems, partner integrations, AI, and global supply chains. And that has expanded the digital ecosystem beyond anything we’ve ever seen.

On-demand webinars
Join our webinar to learn how to architect a scalable AI governance stack, connecting risk, compliance, and development for responsible AI adoption.

Infographic
Digital supply chains are shifting daily and traditional risk management programs aren’t built to keep up.

On-demand webinars
See how OneTrust automates vendor onboarding, due diligence, and ongoing reviews—standardizing intake, speeding approvals, improving collaboration, and reducing risk so teams move faster without losing control.

On-demand webinars
Learn how OneTrust helps security and risk teams replace fragmented vendor data with a centralized risk architecture, delivering a single source of truth, mapped vendors, full visibility, and scalable, proactive risk management.

On-demand webinars
See how AI‑enabled TPRM transforms traditional vendor risk programs in this live demo, showcasing faster assessments, reduced manual effort, clearer risk insights, and smarter prioritization across the third‑party lifecycle to build a more scalable, outcome‑driven TPRM program.

eBook
Data Protection Leader March 2026 explores EU digital reform, US and California AI regulation, NIS2 enforcement, ISO 42001, and modern AI governance.

Upcoming webinars
Discover how AI is transforming third‑party risk management in this webinar, exploring governance of third‑party AI from intake to monitoring and how TPRM leaders use AI.

On-demand webinars
Join our demo webinar series to see how OneTrust simplifies third-party management and technology risk & compliance.

Infographic
AI risk can’t be managed in silos. Effective AI governance brings security, privacy, risk, and the business together to reduce exposure and accelerate innovation.

On-demand webinars
In this session, we’ll explore how leading enterprises are moving from reactive vendor oversight to a programmatic, data-driven approach that strengthens resilience across the entire supply ecosystem.

On-demand webinars
Join seasoned practitioners from OneTrust as we explore how risk assessment has changed, where it stands today, and what the future will demand of risk professionals.

On-demand webinars
In this webinar, learn how organizations operationalize privacy at scale by embedding privacy across the tech lifecycle.
eBook

On-demand webinars
Discover how AI, governance, and transformation frameworks are reshaping Third-Party Risk Management. Join OneTrust and Deloitte on Dec 9.

On-demand webinars
Join OneTrust’s CISO and Head of AI Governance & Privacy to uncover how risk and governance alignment drives responsible AI innovation.

On-demand webinars
Watch how OneTrust’s latest Risk Solutions release empowers teams with AI-driven vendor onboarding and automated evidence analysis for smarter compliance.

On-demand webinars
Watch now this on-demand webinar to see how OneTrust helps organizations identify, manage, and mitigate cybersecurity risks in alignment with NIS-2 compliance obligations.

On-demand webinars
Join our webinar to explore agentic vs. agentish AI, and learn how risk teams can adopt AI responsibly with transparency and control.

On-demand webinars
Join our webinar to explore TPRM best practices, from NIS2 and DORA to aligning privacy with risk in a shifting regulatory landscape.

Report
The OneTrust platform connects data, privacy, and risk teams in one unified system, so you can stay ahead of regulatory change and support responsible growth. Download the excerpt to learn how OneTrust helps you move faster, without sacrificing compliance.

On-demand webinars
Our Chief Information Security Officer (CISO) department's approach to assessing and mitigating third-party risks using our platform.

On-demand webinars
Join our webinar to learn how risk and security leaders are aligning third-party and tech risk for scalable, AI-ready compliance programs.

Upcoming webinars
Join Protiviti and OneTrust where we’ll explore how to evidence DORA compliance effectively and with minimal effort. You’ll gain practical advice on aligning your third-party risk program to regulatory expectations—without slowing down innovation.

eBook
These days, organizations are required to safeguard their customer data and comply with privacy regulations — a task that becomes even more challenging with the increase in third-party relationships.
Demo
Discover how OneTrust helps financial institutions comply with the DORA regulation by streamlining ICT risk and third-party management at scale.

On-demand webinars
Join this session to explore strategies for breaking down silos, integrating risk insights, and strengthening security and compliance postures with a unified risk management approach.

Infographic
OneTrust’s spring 2025 product release introduces three powerful features designed to accelerate contextual risk visibility by streamlining third-party risk assessment processes.

On-demand webinars
Join this live webinar to explore how automated vendor assessments, real-time monitoring, and compliance workflows can enhance risk insights and operational efficiency.

On-demand webinars
Join this webinar to discover how automation enhances third-party risk management. Learn best practices for vendor risk assessment, due diligence, and compliance.

On-demand webinars
Join OneTrust and Deloitte to explore the U.S. DOJ Cybersecurity Rule, key risks, and best practices for managing cross-border data transfers and ensuring compliance.

On-demand webinars
Join our webinar to explore actionable strategies powered by OneTrust solutions to foster collaboration across privacy and TPRM stakeholders to better support your organizations.

On-demand webinars
Join our expert panel to explore DORA compliance post-deadline. Learn key lessons, risk challenges, and best practices for operational resilience.

eBook
For financial institutions in Australia, the Australian Prudential Regulation Authority’s (APRA) CPS 230 standard is a clarion call to fortify cyber resilience.

On-demand webinars
Register for our live demo webinar to see how OneTrust Third-Party Management can revolutionize your third-party risk management approach.

On-demand webinars
Join us to learn more about the Digital Operational Resilience Act (DORA) and how OneTrust can help organizations research, implement, and monitor compliance at scale with DORA and other related regulations and standards like NIS2 and ISO.

Checklist
The Digital Operational Resilience Act (DORA) is the first regulation to oversee the security functions of financial entities across the European Union.

On-demand webinars
Join us for a virtual Lunch & Learn session and explore how OneTrust’s Third Party Management solution can streamline your risk management processes.

On-demand webinars
Join our Saudi Arabia PDPL webinar for an overview on the data protection law, its requirements, and how to prepare for full enforcement.

On-demand webinars
Register for this OneTrust webinar to learn about the relevant resilience focused requirements of DORA, NIS 2, and other global regulations.

On-demand webinars
This DataGuidance webinar explores the latest and expected developments in the implementation of the NIS 2 Directive, focusing on practical compliance strategies to ensure your organization is prepared.

Infographic
This infographic gives an overview on how third-party management affects technology, growing threats, and how OneTrust Third-Party Management can help combat them.

Report
As AI continues to offer unparalleled opportunities for business innovation, it also presents risks that organizations must tackle head-on through scalable governance programs that span multiple data sources. Six key trends are defining these challenges.

On-demand webinars
In this webinar, our experts will discuss the Canadian regulation and others like it globally, while providing actionable insights into building a robust and mature Third-party program.

On-demand webinars
Join our OneTrust webinar on tackling IT security risks for banks in South Africa. Explore strategies for safeguarding sensitive data, ensuring POPIA compliance, and managing cyber threats. Gain actionable insights to strengthen your security posture and build customer trust.

On-demand webinars
Join our upcoming product release webinar to explore how these new capabilities can help your organization navigate complex frameworks, streamline third-party management, and accelerate AI and data innovation.

On-demand webinars
Join to explore how OneTrust's TPRM solution can revolutionize your third-party risk management approach. We will cover best practices for implementing and leveraging the software to minimize risks.

eBook
Streamline third-party relationships and avoid common mistakes in the process.

Checklist
Third-party management doesn’t have to be a complicated process for your business.

Infographic
Working with third parties introduces privacy and security risks, making compliance and business growth a balancing act.

Infographic
Third-party management keeps manufacturing operations running smoothly by verifying vendor and supplier compliance with regulations.

eBook
It’s imperative for security teams to implement a holistic approach to third-party management.

On-demand webinars
Join our upcoming webinar to learn how to navigate the complexities of managing modern slavery, anti-bribery, and corruption within your third-party ecosystem.

On-demand webinars
Join us in a webinar where we will discuss PDPL, third-party risk, and compliance best practices. Learn how you can automate and simplify your third-party management program with OneTrust.

On-demand webinars
Join this APAC webinar to learn the unique competencies of third-party risk and due diligence programs and examine when and how to align them to maximize the effectiveness of each.

On-demand webinars
Amidst South Africa's dynamic AI terrain and evolving data privacy regulations like POPIA, mastering third-party risk management is paramount. This session explores the balance between AI innovation and data protection.

eBook
Download this eBook to explore third-party management across industries and key considerations before bringing this approach organization-wide.

On-demand webinars
As innovation teams race to integrate AI into their products and services, new challenges arise for development teams leveraging third-party models. Join the webinar to gain insights on how to navigate AI vendors while mitigating third-party risks.

On-demand webinars
The EU has adopted several new Cyber Laws that will impact many businesses and will come into force over the next few months (in October in the case of NISD2) and require actions now. Join the webinar to learn about the latest cyber developments.

On-demand webinars
Join this free demo session to learn the ins an outs of OneTrust’s Third-Party Management solution.

On-demand webinars
This webinar will show you how to develop strategies for assessing reputational risks as it relates to third parties and the impact of third-party relationships.

On-demand webinars
In this webinar, we’ll discuss the unique competencies of third-party risk and due diligence programs and examine when and how to align them.

Infographic
Download our infographic to learn about the new DORA regulation, who needs to comply, and how OneTrust can help streamline the process.

On-demand webinars
Learn how to leverage financial, operations, compliance, ESG, and cyber scores to drive resilience insights and detect possible supply chain disruptions.

Checklist
See the path to managing third-party risk effectively with a checklist that outlines the six steps for a sound TPRM program.

On-demand webinars
How can you build a privacy-focused TPRM program? In this webinar, we discuss best practices for privacy compliance when working with third parties, from onboarding to offboarding.

Video
Watch this video for the five top trends shaping the third-party management industry this year.

Checklist
Managing third-party risk is a critical part of AI governance, but you don’t have to start from scratch. Use these questions to adapt your existing vendor assessments to be used for AI.

Infographic
What key challenges do CISOs face going into the new year? Download this infographic to hear what experts from industries across the board have to say.

On-demand webinars
Join this webinar as we discuss key trends for third-party management and lessons learned over the last year.

On-demand webinars
Insight into your third parties’ inherent risks can change the way you run your TPM program.

On-demand webinars
Join our webinar to learn the primary goals of successful Third-Party Risk and Third-Party Due Diligence programs.

On-demand webinars
Join our webinar and learn how to save time and streamline third-party risk assessment throughout the TPRM lifecycle.

eBook
Understand the importance of data privacy in third-party risk management, and 10 best practices for achieving privacy compliance when working with third parties.

On-demand webinars
Join this webinar to learn how to manage the third-party risk lifecycle across teams while optimizing your processes with automation.

On-demand webinars
In this webinar, we'll share seven practical tips for effective third-party risk monitoring, helping you to identify new risks and take timely action to protect your business.

Infographic
Learn how to actively screen and monitor your third parties in the OneTrust Third-Party Risk Exchange.

On-demand webinars
Join our in-depth webinar and learn how to define third-party due dilligence levels and when to apply them during your vendor management lifecycle.

On-demand webinars
Join us as we explore how automating third-party management workflows streamlines processes, drives alignment across teams, and reduces reduntant work.

On-demand webinars
In this webinar, we examine the scope of third-party due dilligence, best practices, and industry trends driving greater scrutiny on third parties.

On-demand webinars
Join our webinar and learn how to create an effective, privacy-focused third-party risk management (TPRM) program that streamlines recordkeeping and reduces your risk exposure.

Video
The OneTrust Vendor Risk Management provides businesses access to pre-completed vendor risk assessments while supporting industry standards.

On-demand webinars
Join OneTrust and HackNotice as we discuss effective ways to protect your organization from third-party data breaches and build strong incident response workflows.

On-demand webinars
Join our upcoming webinar as we explore the pivotal ways procurement and InfoSec teams can collaborate to reduce third-party risks.

eBook
Download our eBook to learn practical advice on how to approach third-party risk management like an InfoSec expert.

On-demand webinars
In this webinar, you will learn how to reduce the use of spreadsheets for third-party risk management and cut costs when building your TPRM program.

On-demand webinars
Watch this webinar to learn how to align your TPRM and TPDD programs to achieve workflow efficiencies and the distinction between the two discipline areas.

In-Person Event
Join this OneTrust live event series, which will address critical topics such as navigating data management, compliance automation and third-party risk.

Infographic
The number of businesses and third-party suppliers has increased, widening the risk landscape. This infographic shows how businesses are managing that risk.

On-demand webinars
Learn how to balance the intricacies of CPRA, VCDPA, CPA, CTDPA, and UCPA when managing third parties and understanding privacy-related risks.

On-demand webinars
Attend this webinar to learn about Third-Party Risk Management (TPRM) workflow definition and maintenance best practices you can apply to your business.NEED

On-demand webinars
In this webinar, you will learn how to utilize TPRM to help to optimize workflows, leverage data, and increase accountability across sourcing and procurement.

On-demand webinars
Our third-party risk software helps you build a vendor inventory, conduct vendor assessments, mitigate risks, monitor vendors over time, and more.

On-demand webinars
Watch the demo video to learn how OneTrust Third-Party Risk Management can help your TPRM program meet your privacy team's expectations.

On-demand webinars
In this session, we’ll outline how to identify, reduce, and monitor cyber risk as it relates to your third parties including methods for tracking cyber risks over time.

On-demand webinars
Join OneTrust for a demo on how our privacy management platform helps Canadian businesses streamline ISO 27001:2022 compliance.

On-demand webinars
Learn how InfoSec teams can automate scoping mandatory requirements and streamline generating evidence to prove compliance across ISO.

On-demand webinars
In this webinar session, we’ll outline how to take a data-driven approach to understand, reduce, and monitor cyber risks as it relates to your third parties.

On-demand webinars
This webinar focuses on the fundamental considerations when managing third parties and enables your organization to build a solid and scalable foundation.

On-demand webinars
In this webinar, we provide a live product demonstration to show you how your organization can optimize and scale a third-party risk program.

On-demand webinars
Learn the top 7 red flags for risky third parties, mitigation tactics for reducing third-party risk, and key ways to streamline risk identification, and more.

eBook
Ensure your enterprise IT risk assessment is a success with a top-down approach that gets executive buy-in from the start

On-demand webinars
Watch our LkSG webinar to understand the scope of LkSG, how your company will need to adjust, and the repercussions of noncompliance.

On-demand webinars
In this webinar, we discuss best practices for how privacy and security teams can work better to eliminate redundant work, save time, and be more efficient.

On-demand webinars
Watch this webinar to hear how to leverage third-party risk management workflow creation and maintenance best practices.

On-demand webinars
In this panel discussion, we address critical points such as defining the metrics to track in relation to third parties and their cybersecurity risks.

On-demand webinars
In this webinar, we’ll review services providers under the ADPPA and outline how you can ready your third-party risk program to align with privacy regulations.

Checklist
Download our LkSG readiness checklist to understand your readiness for risk management systems and responsibilities, and due diligence obligations.

On-demand webinars
In this webinar, we’ll explore these questions and layout 7 must-know best practices to conduct more meaningful third-party risk assessments.

eBook
Understand what it takes to build a successful third-party risk management program through OneTrust's third-party risk management guide.

On-demand webinars
Join our panel of experts as we discuss the German Supply Chain Due Dilligence Act and the best practices for compliance.

On-demand webinars
This webinar will discuss best practices for how privacy and security teams can work together to eliminate redundant work, save time, and be more efficient.

On-demand webinars
Join this webinar to learn how you can integrate your Third-Party Risk Management program within a broader IT Security platform

On-demand webinars
Watch this webinar and see how the COVID-19 pandemic forced companies to accelerate automation and scale their third-party management.

On-demand webinars
Discover effective strategies for preparing security questionaire responses with our free webinar.

eBook
Download our guide on third-party management and learn what you need to know to shift your buisness to TPM.

eBook
In this eBook, learn the business value of TPRM software and why all leading organizations rely on it when working with third-party vendors.

On-demand webinars
Watch our free webinar to discover how to optimize your third-party risk program and reduce manual data management with automation.

On-demand webinars
Join this webinar to learn best practices on how your organization can step-up business resilience with better third-party risk management.

Upcoming webinars
Prepare for 2022 Trends in Third-Party Risk Management and future-proof your Third-Party Trust program.

On-demand webinars
This webinar will discuss how to create a Third-Party Risk Management (TPRM) program that prioritizes privacy compliance and simplifies record-keeping.

eBook
Download the OneTrust Vendor Risk Management Handbook for an in-depth understanding of updated regulations, requirements and more.

eBook
Download our third-party risk management eBook and get a complete roadmap to your TPRM lifecycle.

Upcoming webinars
Join this webinar series, which will focus on the four foundational pillars of Third-Party Risk Management: Automation, Compliance, Reporting, and Collaboration.

On-demand webinars
Watch our webinar and gain insight on how to navigate InfoSec's evolving compliance landscape.
Demo
Discover how our Third-Party Management solution helps you assess, monitor, and mitigate vendor risks while ensuring compliance.

On-demand webinars
Join our risk management webinar series to learn how AI, NIS2, and modern TPRM practices help teams reduce manual work and strengthen resilience.