Blog
What Is Third-Party Risk Management?

What Is Third-Party Risk Management?
Third-party risk management (TPRM) is a form of risk management that focuses on identifying and reducing risks relating to the use of third parties (sometimes referred to as vendors, suppliers, partners, contractors, or service providers).
The discipline is designed to give organizations an understanding of the third parties they use, how they use them, and what safeguards their third parties have in place. The scope and requirements of a TPRM program are dependent on the organization and can vary widely depending on industry, regulatory guidance, and other factors. Still, many TPRM best practices are universal and applicable to every business or organization.
While exact definitions may vary, the term “third-party risk management” is sometimes used interchangeably with other common industry terms, such as vendor risk management (VRM), vendor management, supplier risk management, or supply chain risk management. However, TPRM is often thought of as the overarching discipline that encompasses all types of third parties and all types of risks.
Why Is Third-Party Risk Management Important?
While third-party risk isn’t a new concept, upticks in breaches across industries and a greater reliance on outsourcing have brought the discipline into the forefront like never before. Disruptive events, have impacted almost every business and their third parties – no matter the size, location, or industry. In addition, data breaches or cyber security incidents are common. In in 2021, the impact that third parties have on business resilience was highlighted through outages and other third-party incidents. Some of the ways you can be impacted are:
- Internal outages and lapses in operational capabilities
- External outages affecting areas across the supply chain
- Vendor outages that open your organization to supply chain vulnerabilities
- Operational shifts that affect data gathering, storage, and security
Most modern organizations rely on third parties to keep operations running smoothly. So, when your third parties, vendors, or suppliers can’t deliver, there can be devastating and long-lasting impacts.
For example, you may rely on a service provider such as Amazon Web Services (AWS) to host a website or cloud application. Should AWS go offline, your website or application also goes offline. An additional example could be the reliance on a third party to ship goods. If the shipping company’s drivers go on strike, that can delay expected delivery times and lead to customer cancellations and distrust, which will negatively impact your organization’s bottom line and reputation.
Outsourcing is a necessary component of running a modern business. It not only saves a business money, but it’s a simple way to take advantage of expertise that an organization might not have in house. The downside is that if a proper TPRM program is not in place, relying on third parties can leave your business vulnerable.
What Are the Top TPRM Best Practices?
There are endless TPRM best practices that can help you build a better program, regardless of whether you’re just beginning to make TPRM a priority, or you want to understand where your existing program could be improved. We’ve outlined what we believe are the 3 most critical best practices that are applicable to nearly every company.
1) Prioritize Your Vendor Inventory
Not all vendors are equally important, which is why it is critical to determine which third parties matter most. To improve efficiency in your TPRM program, segment your vendors into criticality tiers.
Most companies segment vendors into three groups:
- Tier 3: Low risk, low criticality
- Tier 2: Medium risk, medium criticality
- Tier 1: High risk, high criticality
In practice, organizations will focus their time and resources on tier 1 vendors first, as they require more stringent due diligence and evidence collection. Typically, tier 1 vendors are subject to the most in-depth assessments, which often includes on-site assessment validation.
Many times, especially during initial evaluation, these tiers are calculated based on the inherent risk of the third party. Inherent risk scores are generated based on industry benchmarks or basic business context, such as whether or not you will be:
- Sharing proprietary or confidential business information with the vendor
- Sharing personal data with the vendor
- Sharing sensitive personal data with the vendor
- Sharing personal data across borders
- Serving a critical business functions
Additionally, impact of the vendor can be a determining factor. If a third party can’t deliver their service, how would that impact your operations? When there is significant disruption, the risk of the vendor will inevitably be higher. Determine this impact by considering:
- The impact of unauthorized disclosure of information
- The impact of unauthorized modification or destruction of information
- The impact of disruption of access to the vendor/information
Another way to tier vendors is by grouping based on contract value. Big-budget vendors may automatically be segmented as a tier 1 vendor due to the high risk based solely on the value of the contract.
2) Leverage Automation Wherever Possible
Efficiencies emerge when operations are consistent and repeatable. There are a number of areas in the TPRM lifecycle where automation is ideal. These areas include, but are not limited to:
- Intaking and onboarding new vendors. Automatically add vendors to your inventory using an intake form or via integration with contract management or other systems.
- Calculating inherent risk and tiering vendors. During intake, collect basic business context to determine a vendor’s inherent risk, and then automatically prioritize vendors posing the highest risk.
- Assigning risk owners and mitigation tasks. When a vendor risk is flagged, route the risk to the correct individual and include a checklist of mitigation action items.
- Triggering vendor performance reviews. Set up automation triggers to conduct a review of the vendor each year, and if the vendor fails the review, trigger off-boarding actions.
- Triggering vendor reassessment. Send a reassessment based on contract expiration dates and save the previous year’s assessment answers so the vendor doesn’t have to start from scratch.
- Sending notifications and other alerts. When a new risk is flagged or a new vendor is onboarded, send an email or alert the relevant stakeholder through an integration with an existing system.
- Scheduling and running reports. Set up automated reports that run on a daily, weekly, or monthly basis and automatically share them with the right person.
Every TPRM program is different, so start by looking internally at the repeatable processes that are ripe for automation. From there, start small and take practical steps to automate key tasks. Over time, these small automations will compound, saving your team valuable time, money, and resources.
3) Think Beyond Cybersecurity Risks
When considering a third-party risk or vendor risk management program, many organizations immediately think about cybersecurity risks. But TPRM entails so much more. While starting small and focusing only on cybersecurity risks is a good first step, there are other types of risks that need to be prioritized. These risks include:
- Reputational risks
- Geographical risks
- Geopolitical risks
- Strategic risks
- Financial risks
- Operational risks
- Privacy risks
- Compliance risks
- Ethical risks
- Business continuity risks
- Performance risks
- 4th party risks
- Credit risks
- Environmental risks
The key takeaway here is that understanding all relevant types of risk (and not just cybersecurity) is imperative to building a world-class TPRM program.
What Is the Third-Party Risk Management Lifecycle?
The third-party risk management lifecycle is a series of steps that outlines a typical relationship with a third party. TPRM is sometimes referred to as “third-party relationship management.” This term better articulates the ongoing nature of vendor engagements. Typically, the TPRM lifecycle, is broken down into several stages. These stages include:
- Vendor identification
- Evaluation & selection
- Risk assessment
- Risk mitigation
- Contracting and procurement
- Reporting and Record-keeping
- Ongoing monitoring
- Vendor off-boarding
Phase 1: Third-Party Identification
There are many ways to identify the third parties your organization is currently working with, as well as ways to identify new third parties your organization wants to use.
To identify vendors already in use and build a vendor inventory, organizations take multiple approaches, which include:
- Using existing information. Organizations often consolidate vendor information from spreadsheets and other sources when rolling out third-party risk software.
- Integrating with existing technologies. Technologies that are in use often contain detailed vendor information, such as CMDBs, SSO providers, contracts, procurement, and other systems. Organizations will often plug into these sources to centralize their inventory in a single software solution.
- Conducting assessments or interviews. A short assessment to business owners across the company, such as marketing, HR, finance, sales, research and development, and other departments can help you uncover the tools in use at your organization.
To identify new third parties, organizations will often leverage a self-service portal as part of their third-party risk management program. With a self-service portal, business owners can build their inventory. Share the portal with your business by linking to it from your intranet or SharePoint. Self-service portals also help gather preliminary information about the third party, such as:
- Personal information involved
- Hosting information
- Privacy Shield and
- other certification
- Business context
- Scope of engagement
- Vendor Name
- Expected procurement date
- Business purpose
- Primary vendor contact (email, phone, address)
- Data type involved
- Prior security reviews or
- Certifications, if applicable
Using this information, you can classify third parties based on the inherent risk that they pose to your organization.
Phase 2: Evaluation and Selection
During the evaluation and selection phase, organizations consider RFPs and choose the vendor they want to use. This decision is made using a number of factors that are unique to the business and its specific needs.
Phase 3: Risk Assessment
Vendor risk assessments take time and are resource-intensive, which is why many organizations are using a third-party risk exchange to access pre-completed assessments. Other common methods include using spreadsheets or assessment automation software. Either way, the primary goal of understanding the risks associated with the vendor is the same.
Common standards used for assessing vendors include:
- ISO 27001 & ISO 27701
- SIG Lite & SIG Core
- NIST SP 800-53
- CSA CAIQ
As well as industry-specific standards, such as:
Phase 4: Risk Mitigation
After conducting an assessment, risks can be calculated, and mitigation can begin. Common risk mitigation workflows include the following stages:
- At this stage, risks are flagged and given a risk level or score.
- During the evaluation phase, organizations will determine if the risk is acceptable within their defined risk appetite.
- When treatment occurs, a risk owner must validate that the required controls are in place to reduce the risk to the desired residual risk level.
- At this phase, organizations monitor risks for any events that may increase the risk level, such as a data breach
Phase 5: Contracting and Procurement
Sometimes done in parallel with risk mitigation, the contracting and procurement stage is critical from a third-party risk perspective. Contracts often contain details that fall outside the realm of TPRM. Still, there are key provisions, clauses, and terms that TPRM teams should look out for when reviewing vendor contracts.
Some of these include:
- Defined Scope of Services or Products
- Price and Payment Terms
- Term and Termination Clauses
- Intellectual Property Ownership Clause
- Deliverables or Services Clause
- Representation and Warranties
- Confidentiality Clause
- Disclaimers or Indemnification
- Limitation of Liability
- Insurance
- Relationship Clause
- Data Processing Agreement
- 4th Party or Subprocessor Change Clauses
- Compliance Clause
- Data Protection Agreement
- Service Level Agreements (SLAs), Product Performance, Response Time
Home in on these key terms to report on requirements in a structured format. Simply determine if key clauses are adequate, inadequate, or missing.
Phase 6: Reporting and Recordkeeping
Building a strong TPRM program requires organizations to maintain compliance. This step is often overlooked. Maintaining detailed records in spreadsheets is nearly impossible at scale, which is why many organizations implement TPRM software. With auditable recordkeeping in place, it becomes much easier to report on critical aspects of your program to identify areas for improvement.
In practice, a sample reporting dashboard may include:
- Total supplier count
- Suppliers sorted by risk level
- Status on all supplier risk assessments
- Number of suppliers with expiring or expired contracts
- Risks grouped by level (high, medium, low)
- Risks by stage within the risk mitigation workflow
- Risks to your parent organization and risks to your subsidiaries
- Risk history over time
Phase 7: Ongoing Monitoring
An assessment is a “moment-in-time” look into a vendor’s risks; however, engagements with third parties do not end there – or even after risk mitigation. Ongoing vendor monitoring throughout the life of a third-party relationship is critical, as is adapting when new issues arise.
For example, new regulations, negative news stories, high-profile data breaches, and evolving usage of a vendor, may all impact the risks associated with your third parties. Some key risk-changing events to monitor include:
- Mergers, acquisitions, or divestitures
- Internal process changes
- Negative news or unethical behavior
- Natural disasters and other business continuity triggering events
- Product releases
- Contract changes
- Industry or regulatory developments
- Financial viability or cash flow
- Employee reduction
Phase 8: Vendor Offboarding
A thorough offboarding procedure is critical, both for security purposes and recordkeeping requirements. Many organizations have developed an offboarding checklist for vendors, which can consist of both an assessment sent internally and externally to confirm that all appropriate measures were taken. Critical too is the ability to maintain detailed evidence trail of these activities to demonstrate compliance in the event of regulatory inquiry or audit.
Which Department Owns TPRM?
There is no one-size-fits-all approach to third-party risk management. All companies are different, and as a result, there is no set-in-stone department that owns vendor risk responsibilities. Some mature organizations may have a third-party risk or vendor management team, but many organizations do not. As a result, common job titles and departments that “own” third-party risk include:
- Chief Information Security Officer (CISO)
- Chief Procurement Officer (CPO)
- Chief Information Officer (CIO)
- Chief Privacy Officer (CPO)
- Information Technology (IT)
- Sourcing and Procurement
- Information Security
- Risk and Compliance
- Supply Chain Manager
- Third-Party Risk Manager
- Vendor Risk Manager
- Vendor Management
- Contract Manager
The list above is by no means comprehensive; however, the diverse variety of titles and departments can shed some light on the diverse approaches taken to third-party risk management.
Ultimately, these stakeholders and departments must work together to manage vendors throughout the third-party lifecycle. As such, TPRM often extends into many departments and across many different roles.
What Are the Benefits of Third-party Management Software?
With third-party management software, your organization can develop and scale a successful TPRM management program that adds value to your bottom line. The return on investment (ROI) is significant when leveraging the automation opportunities that purpose-built software provides. The biggest benefits include:
- Improved security
- Improved customer trust
- Increased time savings
- Increased cost savings
- Less redundant work
- Better data visibility
- Faster vendor onboarding
- Simpler assessments
- Better reporting capabilities
- Easier audits
- Less risks
- Better vendor performance
- Less spreadsheets
How Can OneTrust Help?
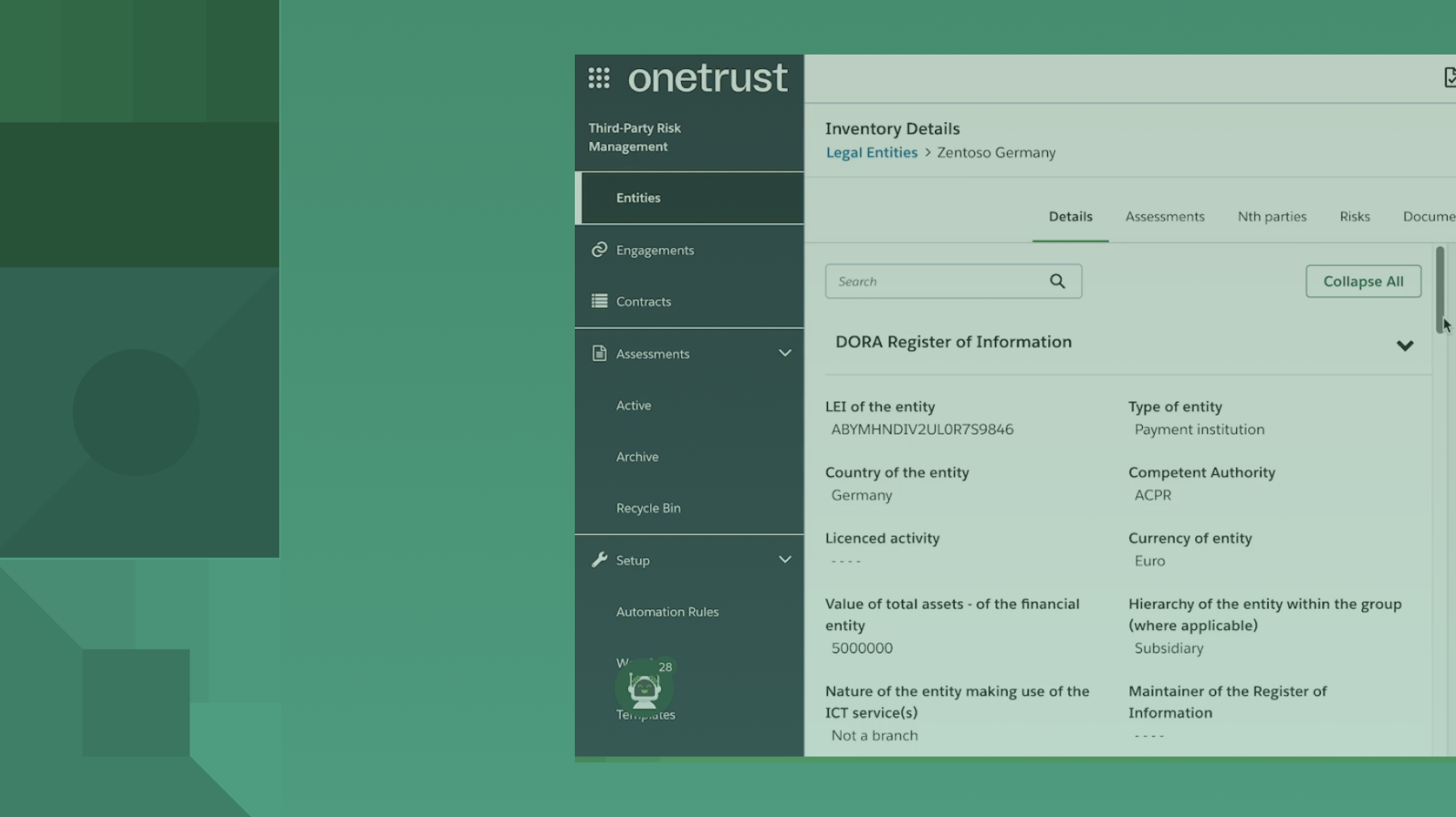
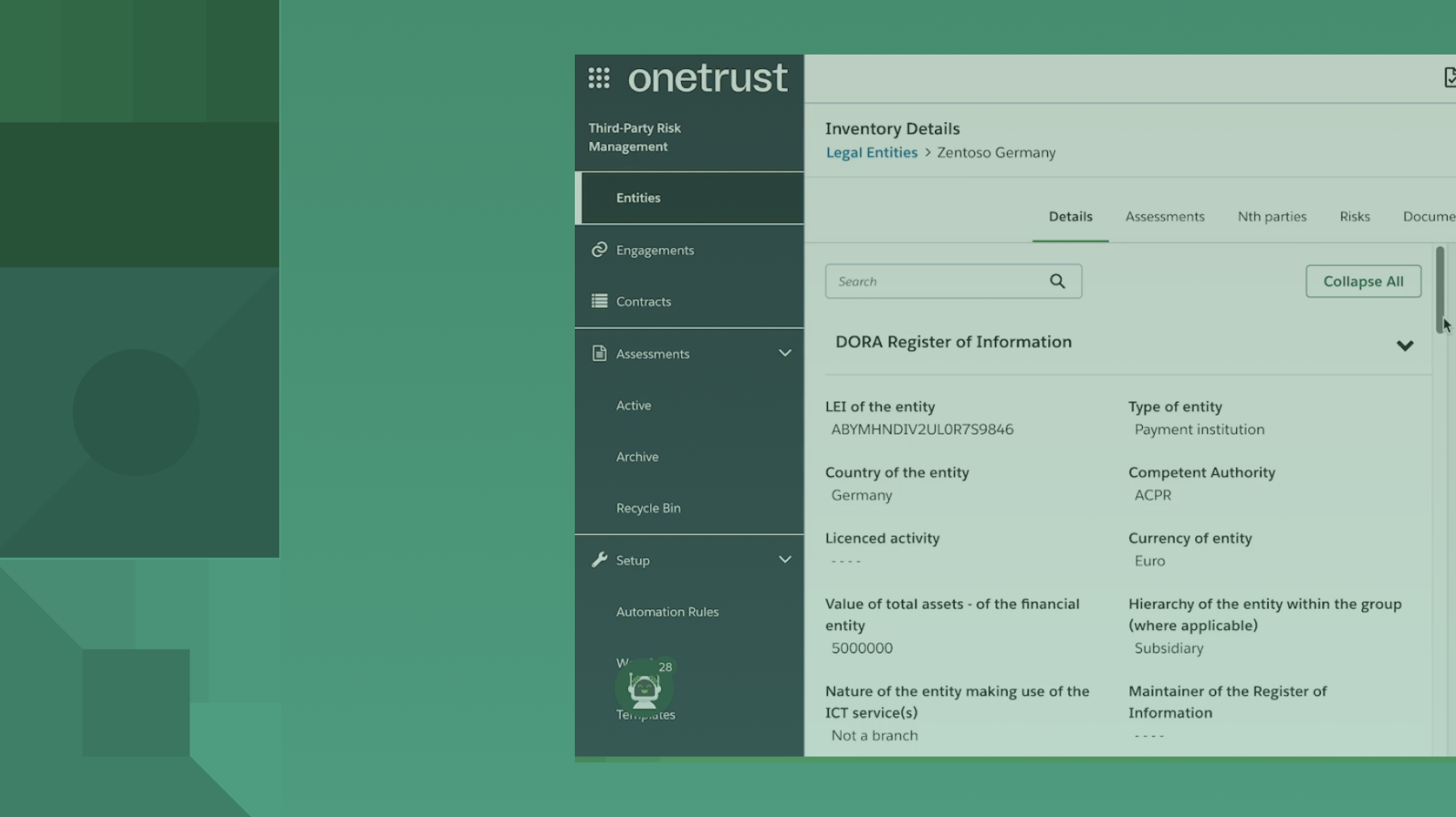
“The OneTrust platform leverages expertise in Tech Risk & Compliance, specializing in Third-Party Management, Privacy Automation, Incident Management, and many other categories to deliver an immersive security and privacy management experience. Reduce your vendor, supplier, and third-party risks with OneTrust Third-Party Management software. The software enables you to run compliance checks and screen vendors. Additionally, our software empowers organizations to conduct vendor risk assessments and mitigate risks through highly customizable workflow automation. The OneTrust Third-Party Risk Exchange enables businesses to access risk analytics and control gap reports on vendors, and provides vendors with an opportunity to centralize their compliance details and promote them to thousands of OneTrust customers to easily share.”
TPRM is important because organizations increasingly rely on a broad ecosystem of third parties, which expands the risk surface — including data breaches, service disruptions and regulatory exposure. Implementing strong TPRM allows organizations to maintain trust, continuity and regulatory compliance in complex vendor-driven environments.
A TPRM program should address a wide range of risks including cybersecurity/InfoSec risk (such as vendor data breaches), operational risk (service failures from third parties), financial risk (vendor insolvency or lost revenue), and compliance/legal risk (third parties failing to meet regulatory obligations). Each vendor relationship introduces a unique risk profile that must be evaluated accordingly.
An organization should build a TPRM program by first creating a comprehensive third-party inventory, conducting vendor risk assessments, implementing control frameworks, establishing ongoing monitoring and metrics, and ensuring cross-functional governance across procurement, IT, privacy and security teams. This structured lifecycle supports scalable vendor risk management and aligns with business objectives.
Continuous monitoring is critical because risk exposure from third parties evolves over time as business practices, technology, threat landscapes and regulatory requirements change. Ongoing monitoring enables timely detection of new or emerging vendor risks, supports proactive mitigation, and ensures that contractual and control obligations remain effective.
You May Also Like

Upcoming webinars
Third-Party Risk
Beyond ISO 27001: Building the Foundation for Scalable Risk and AI Governance Webinar | Resources | OneTrust
Join OneTrust’s fireside chat to learn why ISO 27001 is the baseline for modern governance and how to move beyond certification to scalable risk management, AI governance, and board-ready security programs—register now.
July 21, 2026

Upcoming webinars
Third-Party Risk
Beyond ISO 27001: Building the Foundation for Scalable Risk and AI Governance Webinar | Resources | OneTrust
Join OneTrust’s fireside chat to learn why ISO 27001 is the baseline for modern governance and how to move beyond certification to scalable risk management, AI governance, and board-ready security programs—register now.
July 21, 2026

Upcoming webinars
Third-Party Risk
AI Risk Management: Preparing for EU AI Act Compliance While Driving Innovation
Learn how to turn AI governance principles into action with this live webinar. We will discuss how organizations can operationalize AI governance, manage AI risk, and oversee third‑party AI to meet evolving regulations.
July 08, 2026

On-demand webinars
Technology Risk & Compliance
How OneTrust solves the ‘Why should I care?’ of risk insights
Discover how OneTrust aggregates and contextualizes risk data, models business and technical impact, and delivers board-ready dashboards that translate technical risk into clear, executive-level decisions.
May 19, 2026

On-demand webinars
Technology Risk & Compliance
How OneTrust solves the ‘Why should I care?’ of risk insights
Discover how OneTrust aggregates and contextualizes risk data, models business and technical impact, and delivers board-ready dashboards that translate technical risk into clear, executive-level decisions.
May 19, 2026

On-demand webinars
AI Governance
The AI Risk Maturity Journey: Embedding Continuous Governance Across the Lifecycle
Learn how leading teams move from reactive compliance to lifecycle-embedded governance — enabling better communication of AI risk to executives, stronger oversight, and measurable business value.
May 07, 2026

On-demand webinars
AI Governance
The AI Risk Maturity Journey: Embedding Continuous Governance Across the Lifecycle
Learn how leading teams move from reactive compliance to lifecycle-embedded governance — enabling better communication of AI risk to executives, stronger oversight, and measurable business value.
May 07, 2026

On-demand webinars
Third-Party Risk
How OneTrust solves inconsistent and subjective risk scoring
Learn how OneTrust enables structured, transparent risk scoring by standardizing questionnaires, distinguishing inherent and residual risk, creating explainable scores, and turning risk data into actionable business insights.
May 05, 2026

On-demand webinars
Third-Party Risk
How OneTrust solves inconsistent and subjective risk scoring
Learn how OneTrust enables structured, transparent risk scoring by standardizing questionnaires, distinguishing inherent and residual risk, creating explainable scores, and turning risk data into actionable business insights.
May 05, 2026

eBook
Technology Risk & Compliance
The Modern CISO Risk Surface: AI, Third Parties, Fourth Parties, and Beyond
Today’s enterprise operates across clouds, SaaS ecosystems, partner integrations, AI, and global supply chains. And that has expanded the digital ecosystem beyond anything we’ve ever seen.
April 27, 2026

eBook
Technology Risk & Compliance
The Modern CISO Risk Surface: AI, Third Parties, Fourth Parties, and Beyond
Today’s enterprise operates across clouds, SaaS ecosystems, partner integrations, AI, and global supply chains. And that has expanded the digital ecosystem beyond anything we’ve ever seen.
April 27, 2026

AI Governance
Agentes de IA: autonomia ou ameaça? O que as equipes de ciber-risco precisam saber
A IA agencial está evoluindo rapidamente — e a pergunta para você, que atua com risco e compliance, não é apenas o que é possível, mas o que é prático e seguro hoje.
Você vai acompanhar uma sessão com especialista da OneTrust, que analisa a diferença entre IA agente e o que chamamos de IA do tipo agente, mostrando claramente onde termina a autonomia e onde a supervisão humana continua sendo essencial.
abril 16, 2026

AI Governance
Agentes de IA: autonomia ou ameaça? O que as equipes de ciber-risco precisam saber
A IA agencial está evoluindo rapidamente — e a pergunta para você, que atua com risco e compliance, não é apenas o que é possível, mas o que é prático e seguro hoje.
Você vai acompanhar uma sessão com especialista da OneTrust, que analisa a diferença entre IA agente e o que chamamos de IA do tipo agente, mostrando claramente onde termina a autonomia e onde a supervisão humana continua sendo essencial.
abril 16, 2026

Deutsch
Risikobasierte Innovation: KI‑Governance und Risikomanagement vereinen, um verantwortungsvolles Wachstum zu beschleunigen
Entdecken Sie, wie KI‑Governance und KI‑Risiko effektiv zusammenspielen, um verantwortungsvolle Innovation zu stärken und Unternehmen zukunftssicher zu machen.
April 14, 2026

Deutsch
Risikobasierte Innovation: KI‑Governance und Risikomanagement vereinen, um verantwortungsvolles Wachstum zu beschleunigen
Entdecken Sie, wie KI‑Governance und KI‑Risiko effektiv zusammenspielen, um verantwortungsvolle Innovation zu stärken und Unternehmen zukunftssicher zu machen.
April 14, 2026

On-demand webinars
AI Governance
Operationalizing AI Governance: From Complexity to Control
Join our webinar to learn how to architect a scalable AI governance stack, connecting risk, compliance, and development for responsible AI adoption.
April 14, 2026

On-demand webinars
AI Governance
Operationalizing AI Governance: From Complexity to Control
Join our webinar to learn how to architect a scalable AI governance stack, connecting risk, compliance, and development for responsible AI adoption.
April 14, 2026

Infographic
Third-Party Risk
The Shift from Periodic Reviews to Continuous Risk Management
Digital supply chains are shifting daily and traditional risk management programs aren’t built to keep up.
April 09, 2026

On-demand webinars
Third-Party Risk
How OneTrust solves manual, ad-hoc third-party risk processes
See how OneTrust automates vendor onboarding, due diligence, and ongoing reviews—standardizing intake, speeding approvals, improving collaboration, and reducing risk so teams move faster without losing control.
April 08, 2026

On-demand webinars
Third-Party Risk
How OneTrust solves manual, ad-hoc third-party risk processes
See how OneTrust automates vendor onboarding, due diligence, and ongoing reviews—standardizing intake, speeding approvals, improving collaboration, and reducing risk so teams move faster without losing control.
April 08, 2026

On-demand webinars
Third-Party Risk
How OneTrust solves visibility gaps and standardizes risk management
Learn how OneTrust helps security and risk teams replace fragmented vendor data with a centralized risk architecture, delivering a single source of truth, mapped vendors, full visibility, and scalable, proactive risk management.
March 31, 2026

On-demand webinars
Third-Party Risk
How OneTrust solves visibility gaps and standardizes risk management
Learn how OneTrust helps security and risk teams replace fragmented vendor data with a centralized risk architecture, delivering a single source of truth, mapped vendors, full visibility, and scalable, proactive risk management.
March 31, 2026

Blog
Technology Risk & Compliance
A Day in the Life of a Risk Assessor: Yesterday, Today, Tomorrow
While tools and focus have changed in the past decade, the fundamentals have not.
Nick Geyer
March 25, 2026 5 min read

On-demand webinars
Technology Risk & Compliance
Smarter TPRM in action: Using AI to drive efficiency and better risk outcomes
See how AI‑enabled TPRM transforms traditional vendor risk programs in this live demo, showcasing faster assessments, reduced manual effort, clearer risk insights, and smarter prioritization across the third‑party lifecycle to build a more scalable, outcome‑driven TPRM program.
March 25, 2026

On-demand webinars
Technology Risk & Compliance
Smarter TPRM in action: Using AI to drive efficiency and better risk outcomes
See how AI‑enabled TPRM transforms traditional vendor risk programs in this live demo, showcasing faster assessments, reduced manual effort, clearer risk insights, and smarter prioritization across the third‑party lifecycle to build a more scalable, outcome‑driven TPRM program.
March 25, 2026

eBook
Privacy Automation
Data Protection Leader Magazine | March 2026
Data Protection Leader March 2026 explores EU digital reform, US and California AI regulation, NIS2 enforcement, ISO 42001, and modern AI governance.
March 24, 2026

Upcoming webinars
Technology Risk & Compliance
TPRM in the age of AI: Managing risk while scaling smarter programs
Discover how AI is transforming third‑party risk management in this webinar, exploring governance of third‑party AI from intake to monitoring and how TPRM leaders use AI.
March 11, 2026

Upcoming webinars
Technology Risk & Compliance
TPRM in the age of AI: Managing risk while scaling smarter programs
Discover how AI is transforming third‑party risk management in this webinar, exploring governance of third‑party AI from intake to monitoring and how TPRM leaders use AI.
March 11, 2026

Blog
ISO/IEC 27001 in der Praxis: Was deutsche Unternehmen nachweisen müssen
In Deutschland wird die Norm ISO/IEC 27001 als lebendes Risikomanagementsystem betrachtet und nicht als statische Zertifizierung.
Unternehmen, die die Norm in breitere Governance-Strukturen einbetten, sind besser aufgestellt, um den wachsenden regulatorischen Anforderungen der EU gerecht zu werden.
März 02, 2026

Blog
ISO/IEC 27001 in der Praxis: Was deutsche Unternehmen nachweisen müssen
In Deutschland wird die Norm ISO/IEC 27001 als lebendes Risikomanagementsystem betrachtet und nicht als statische Zertifizierung.
Unternehmen, die die Norm in breitere Governance-Strukturen einbetten, sind besser aufgestellt, um den wachsenden regulatorischen Anforderungen der EU gerecht zu werden.
März 02, 2026

Third-Party Risk
Third-Party Risk
ISO 27001 en pratique : ce que les organisations doivent prouver
mars 02, 2026

Third-Party Risk
Third-Party Risk
ISO 27001 en pratique : ce que les organisations doivent prouver
mars 02, 2026

On-demand webinars
Third-Party Risk
Simplifying Risk and Compliance: From Chaos to Clarity Webinar Series
Join our demo webinar series to see how OneTrust simplifies third-party management and technology risk & compliance.
March 02, 2026

On-demand webinars
Third-Party Risk
Simplifying Risk and Compliance: From Chaos to Clarity Webinar Series
Join our demo webinar series to see how OneTrust simplifies third-party management and technology risk & compliance.
March 02, 2026

Blog
Third-Party Risk
The shift from periodic reviews to continuous risk management
To enable innovation, risk programs must move away from point-in-time information gathering.
Nick Geyer
February 20, 2026 5 min read

Blog
Third-Party Risk
The shift from periodic reviews to continuous risk management
To enable innovation, risk programs must move away from point-in-time information gathering.
Nick Geyer
February 20, 2026 5 min read

Blog
Third-Party Risk
Fourth-party blind spots: Hidden risks, massive impacts
Deeper supply chain risks are posing the biggest problems, and continuous monitoring is the only way to reduce exposure.
Nick Geyer
February 17, 2026 3 min read

Blog
Third-Party Risk
Fourth-party blind spots: Hidden risks, massive impacts
Deeper supply chain risks are posing the biggest problems, and continuous monitoring is the only way to reduce exposure.
Nick Geyer
February 17, 2026 3 min read

Infographic
Third-Party Risk
Accelerate growth: Uniting AI governance and risk management
AI risk can’t be managed in silos. Effective AI governance brings security, privacy, risk, and the business together to reduce exposure and accelerate innovation.
February 16, 2026

On-demand webinars
Third-Party Risk
Third-Party operational risk: Shifting from reliance to resilience
In this session, we’ll explore how leading enterprises are moving from reactive vendor oversight to a programmatic, data-driven approach that strengthens resilience across the entire supply ecosystem.
January 27, 2026

On-demand webinars
Third-Party Risk
Third-Party operational risk: Shifting from reliance to resilience
In this session, we’ll explore how leading enterprises are moving from reactive vendor oversight to a programmatic, data-driven approach that strengthens resilience across the entire supply ecosystem.
January 27, 2026

On-demand webinars
Third-Party Risk
A day in the life of a risk assessor — Yesterday, today, tomorrow
Join seasoned practitioners from OneTrust as we explore how risk assessment has changed, where it stands today, and what the future will demand of risk professionals.
January 21, 2026

On-demand webinars
Privacy Automation
From compliance to impact: Embedding privacy across the tech lifecycle
In this webinar, learn how organizations operationalize privacy at scale by embedding privacy across the tech lifecycle.
January 20, 2026

On-demand webinars
Privacy Automation
From compliance to impact: Embedding privacy across the tech lifecycle
In this webinar, learn how organizations operationalize privacy at scale by embedding privacy across the tech lifecycle.
January 20, 2026
eBook
Third-Party Risk
The business value of automated third-party risk management
January 14, 2026
eBook
Third-Party Risk
The business value of automated third-party risk management
How OneTrust Manages Risk and Compliance
January 14, 2026

Webinaires à la demande
Third-Party Risk
Third-Party Management nouvelle génération : automatisation, IA et intégrations pour une vision continue des risques
Vous utilisez une CMP pour gérer les consentements ? Découvrez comment Compliance Assistant vous permet d'aller plus loin avec un suivi automatisé et quotidien de la conformité de vos sites web aux réglementations mondiales. Ce webinar vous présentera comment identifier, prioriser et corriger les risques liés aux technologies de suivi – sans configuration supplémentaire.
janvier 08, 2026

Webinaires à la demande
Third-Party Risk
Third-Party Management nouvelle génération : automatisation, IA et intégrations pour une vision continue des risques
Vous utilisez une CMP pour gérer les consentements ? Découvrez comment Compliance Assistant vous permet d'aller plus loin avec un suivi automatisé et quotidien de la conformité de vos sites web aux réglementations mondiales. Ce webinar vous présentera comment identifier, prioriser et corriger les risques liés aux technologies de suivi – sans configuration supplémentaire.
janvier 08, 2026

Blog
Third-Party Risk
Connecting risk insights enable smarter business decisions
Data fragmentation, paired with information overload, challenges today’s risk programs.
Kaitlyn Archibald
January 05, 2026 3 min read

On-demand webinars
Responsible AI
Future of Third-Party Risk Management: AI, Governance, and Strategic Transformation
Discover how AI, governance, and transformation frameworks are reshaping Third-Party Risk Management. Join OneTrust and Deloitte on Dec 9.
December 09, 2025

On-demand webinars
Responsible AI
Future of Third-Party Risk Management: AI, Governance, and Strategic Transformation
Discover how AI, governance, and transformation frameworks are reshaping Third-Party Risk Management. Join OneTrust and Deloitte on Dec 9.
December 09, 2025

On-demand webinars
AI Governance
Risk-enabled innovation: Uniting AI governance and risk management to accelerate responsible growth
Join OneTrust’s CISO and Head of AI Governance & Privacy to uncover how risk and governance alignment drives responsible AI innovation.
December 04, 2025

On-demand webinars
AI Governance
Risk-enabled innovation: Uniting AI governance and risk management to accelerate responsible growth
Join OneTrust’s CISO and Head of AI Governance & Privacy to uncover how risk and governance alignment drives responsible AI innovation.
December 04, 2025

eBook
Rischio terze parti
Conformità della privacy dei dati e gestione delle terze parti: un approccio unificato
Comprendere l'importanza della privacy dei dati nella gestione del rischio terze parti e le dieci pratiche consigliate per garantire la conformità quando si lavora con terze parti.
ottobre 29, 2025

On-demand webinars
Third-Party Risk
Highlights of the Fall OneTrust release for risk solutions
Watch how OneTrust’s latest Risk Solutions release empowers teams with AI-driven vendor onboarding and automated evidence analysis for smarter compliance.
October 28, 2025

On-demand webinars
Third-Party Risk
Highlights of the Fall OneTrust release for risk solutions
Watch how OneTrust’s latest Risk Solutions release empowers teams with AI-driven vendor onboarding and automated evidence analysis for smarter compliance.
October 28, 2025

On-demand webinars
Technology Risk & Compliance
How OneTrust supports NIS-2 compliance: On-demand demo of our solution
Watch now this on-demand webinar to see how OneTrust helps organizations identify, manage, and mitigate cybersecurity risks in alignment with NIS-2 compliance obligations.
October 23, 2025

On-demand webinars
Technology Risk & Compliance
How OneTrust supports NIS-2 compliance: On-demand demo of our solution
Watch now this on-demand webinar to see how OneTrust helps organizations identify, manage, and mitigate cybersecurity risks in alignment with NIS-2 compliance obligations.
October 22, 2025
eBook
Rischio terze parti
Conformità della privacy dei dati e gestione delle terze parti: un approccio unificato
Comprendere l'importanza della privacy dei dati nella gestione del rischio terze parti e le dieci pratiche consigliate per garantire la conformità quando si lavora con terze parti.
ottobre 21, 2025

On-demand webinars
Third-Party Risk
Agentic vs. Agentish AI — What risk teams need to know
Join our webinar to explore agentic vs. agentish AI, and learn how risk teams can adopt AI responsibly with transparency and control.
October 16, 2025

On-demand webinars
Third-Party Risk
Agentic vs. Agentish AI — What risk teams need to know
Join our webinar to explore agentic vs. agentish AI, and learn how risk teams can adopt AI responsibly with transparency and control.
October 16, 2025
Rapport
Technology Risk & Compliance
OneTrust nommé leader dans le rapport 2025 IDC MarketScape mondial sur les logiciels de GRC
La plateforme OneTrust réunit les équipes chargées des données, de la confidentialité et des risques au sein d’un système unifié, vous permettant d’anticiper les évolutions réglementaires et de soutenir une croissance responsable. Téléchargez l’extrait pour découvrir comment OneTrust vous permet d’aller plus vite, sans sacrifier la conformité.
octobre 09, 2025

Rapport
Technology Risk & Compliance
OneTrust nommé leader dans le rapport 2025 IDC MarketScape mondial sur les logiciels de GRC
La plateforme OneTrust réunit les équipes chargées des données, de la confidentialité et des risques au sein d’un système unifié, vous permettant d’anticiper les évolutions réglementaires et de soutenir une croissance responsable. Téléchargez l’extrait pour découvrir comment OneTrust vous permet d’aller plus vite, sans sacrifier la conformité.
octobre 09, 2025

On-demand webinars
Third-Party Risk
Building blocks of risk: Establishing TPRM best practices in a shifting regulatory environment
Join our webinar to explore TPRM best practices, from NIS2 and DORA to aligning privacy with risk in a shifting regulatory landscape.
September 30, 2025

On-demand webinars
Third-Party Risk
Building blocks of risk: Establishing TPRM best practices in a shifting regulatory environment
Join our webinar to explore TPRM best practices, from NIS2 and DORA to aligning privacy with risk in a shifting regulatory landscape.
September 30, 2025

Blog
Third-Party Risk
Build operational risk resilience in the age of DORA and NIS2
Internal and external networks continue to sprawl, making it more difficult to proactively manage risk.
Nick Geyer
September 29, 2025 5 min read

Blog
Third-Party Risk
Build operational risk resilience in the age of DORA and NIS2
Internal and external networks continue to sprawl, making it more difficult to proactively manage risk.
Nick Geyer
September 29, 2025 5 min read

Blog
AI Governance
Governing at the speed of AI: The future demands a new playbook
OneTrust’s 2025 AI-Ready Governance Report unveils key executive insights around the use and management of the latest technology.
September 08, 2025

Blog
AI Governance
Governing at the speed of AI: The future demands a new playbook
OneTrust’s 2025 AI-Ready Governance Report unveils key executive insights around the use and management of the latest technology.
September 08, 2025

Blog
GRC e garanzia di sicurezza
La trasformazione digitale e il panorama in continua evoluzione della sicurezza informatica
Con il continuo evolversi del panorama tecnologico, i team si trovano ad affrontare un aumento degli obblighi di conformità, delle normative e crescente utilizzo della tecnologia cloud.
Scott Solomon
settembre 03, 2025 3 min read

Blog
GRC e garanzia di sicurezza
La trasformazione digitale e il panorama in continua evoluzione della sicurezza informatica
Con il continuo evolversi del panorama tecnologico, i team si trovano ad affrontare un aumento degli obblighi di conformità, delle normative e crescente utilizzo della tecnologia cloud.
Scott Solomon
settembre 03, 2025 3 min read
Report
Technology Risk & Compliance
OneTrust è stata nominata leader nell'IDC MarketScape for Worldwide Software GRC Software Report 2025
La piattaforma OneTrust collega i team che si occupano di dati, privacy e rischio in un unico sistema in modo da poter stare al passo con i cambiamenti normativi e supportare una crescita responsabile. Scarica l'estratto per scoprire come OneTrust può aiutarti a velocizzare le tue operazioni senza sacrificare la conformità
settembre 03, 2025

Report
Technology Risk & Compliance
OneTrust è stata nominata leader nell'IDC MarketScape for Worldwide Software GRC Software Report 2025
La piattaforma OneTrust collega i team che si occupano di dati, privacy e rischio in un unico sistema in modo da poter stare al passo con i cambiamenti normativi e supportare una crescita responsabile. Scarica l'estratto per scoprire come OneTrust può aiutarti a velocizzare le tue operazioni senza sacrificare la conformità
settembre 03, 2025

Blog
Due Diligence di terze parti
La resilienza delle aziende si basa sulla gestione delle terze parti | Blog | OneTrust
Supervisionare le relazioni commerciali non significa solo controllare il rischio: le aziende devono capire come gestire le terze parti a tutto tondo.
Jason Koestenblatt
settembre 03, 2025

Blog
Due Diligence di terze parti
La resilienza delle aziende si basa sulla gestione delle terze parti | Blog | OneTrust
Supervisionare le relazioni commerciali non significa solo controllare il rischio: le aziende devono capire come gestire le terze parti a tutto tondo.
Jason Koestenblatt
settembre 03, 2025
Report
Technology Risk & Compliance
OneTrust named a leader in the 2025 IDC MarketScape for worldwide GRC software
The OneTrust platform connects data, privacy, and risk teams in one unified system, so you can stay ahead of regulatory change and support responsible growth. Download the excerpt to learn how OneTrust helps you move faster, without sacrificing compliance.
July 17, 2025

Report
Technology Risk & Compliance
OneTrust named a leader in the 2025 IDC MarketScape for worldwide GRC software
The OneTrust platform connects data, privacy, and risk teams in one unified system, so you can stay ahead of regulatory change and support responsible growth. Download the excerpt to learn how OneTrust helps you move faster, without sacrificing compliance.
July 17, 2025

Bericht
Technology Risk & Compliance
OneTrust ist „Leader“ im IDC MarketScape 2025 für GRC-Software
Die OneTrust Plattform bringt Daten- und Datenschutzteams sowie Risikomanager in einem zentralen System zusammen. Damit sind Sie regulatorischen Veränderungen stets einen Schritt voraus und können verantwortungsvolles Wachstum gezielt fördern. Laden Sie den Auszug herunter und erfahren Sie, wie OneTrust Sie dabei unterstützt, schneller voranzukommen – ohne Kompromisse bei der Compliance.
Juli 17, 2025

Bericht
Technology Risk & Compliance
OneTrust ist „Leader“ im IDC MarketScape 2025 für GRC-Software
Die OneTrust Plattform bringt Daten- und Datenschutzteams sowie Risikomanager in einem zentralen System zusammen. Damit sind Sie regulatorischen Veränderungen stets einen Schritt voraus und können verantwortungsvolles Wachstum gezielt fördern. Laden Sie den Auszug herunter und erfahren Sie, wie OneTrust Sie dabei unterstützt, schneller voranzukommen – ohne Kompromisse bei der Compliance.
Juli 17, 2025

Seminarios web bajo demanda
Third-Party Risk Management
Cómo OneTrust usa OneTrust: Gestión de terceros y proveedores
El enfoque del departamento de nuestra directora de seguridad de la información es evaluar y mitigar los riesgos de terceros a través de nuestra plataforma.
julio 09, 2025

Seminarios web bajo demanda
Third-Party Risk Management
Cómo OneTrust usa OneTrust: Gestión de terceros y proveedores
El enfoque del departamento de nuestra directora de seguridad de la información es evaluar y mitigar los riesgos de terceros a través de nuestra plataforma.
julio 09, 2025

On-demand webinars
Third-Party Risk
OneTrust Using OneTrust: Managing third parties & vendors
Our Chief Information Security Officer (CISO) department's approach to assessing and mitigating third-party risks using our platform.
July 09, 2025

On-demand webinars
Third-Party Risk
OneTrust Using OneTrust: Managing third parties & vendors
Our Chief Information Security Officer (CISO) department's approach to assessing and mitigating third-party risks using our platform.
July 09, 2025

On-demand webinars
Technology Risk & Compliance
Unifying third-party and tech risk in an AI-driven world
Join our webinar to learn how risk and security leaders are aligning third-party and tech risk for scalable, AI-ready compliance programs.
July 08, 2025

On-demand webinars
Technology Risk & Compliance
Unifying third-party and tech risk in an AI-driven world
Join our webinar to learn how risk and security leaders are aligning third-party and tech risk for scalable, AI-ready compliance programs.
July 08, 2025
E-Book
Third-Party Risk
Der umfassende Leitfaden für das Drittparteienmanagement
Für Sicherheitsteams ist es unerlässlich, einen ganzheitlichen Ansatz für das Drittparteienmanagement zu implementieren.
Juli 07, 2025
E-Book
Third-Party Risk
Kompetent durch den Lebenszyklus des Drittparteienrisikomanagements
Laden Sie unser E-Book zum Thema „Drittparteienrisikomanagement“ (TPRM) herunter und erhalten Sie eine umfassende Roadmap für den gesamten TPRM-Lebenszyklus.
Juli 07, 2025

E-Book
Third-Party Risk
Der umfassende Leitfaden für das Drittparteienmanagement
Für Sicherheitsteams ist es unerlässlich, einen ganzheitlichen Ansatz für das Drittparteienmanagement zu implementieren.
Juli 07, 2025

E-Book
Third-Party Risk
Kompetent durch den Lebenszyklus des Drittparteienrisikomanagements
Laden Sie unser E-Book zum Thema „Drittparteienrisikomanagement“ (TPRM) herunter und erhalten Sie eine umfassende Roadmap für den gesamten TPRM-Lebenszyklus.
Juli 07, 2025

Upcoming webinars
Third-Party Risk
DORA: Evidencing compliance with minimal effort
Join Protiviti and OneTrust where we’ll explore how to evidence DORA compliance effectively and with minimal effort. You’ll gain practical advice on aligning your third-party risk program to regulatory expectations—without slowing down innovation.
June 17, 2025

Upcoming webinars
Third-Party Risk
DORA: Evidencing compliance with minimal effort
Join Protiviti and OneTrust where we’ll explore how to evidence DORA compliance effectively and with minimal effort. You’ll gain practical advice on aligning your third-party risk program to regulatory expectations—without slowing down innovation.
June 17, 2025
Blog
Third-Party Risk
Agentic vs. Agentish AI: What it Means for Third-Party Risk Management
Company size and maturity plays a pivotal role in how you deploy AI for vendor oversight.
June 10, 2025 4 min read
Blog
Third-Party Risk
Agentic vs. Agentish AI: What it Means for Third-Party Risk Management
Company size and maturity plays a pivotal role in how you deploy AI for vendor oversight.
June 10, 2025 4 min read
eBook
Third-Party Risk
Maîtriser le cycle de vie de la gestion du risque tiers
Téléchargez notre eBook sur la gestion du risque tiers et obtenez une feuille de route complète pour le cycle de vie de votre gestion des risques tiers.
juin 02, 2025

eBook
Third-Party Risk
Maîtriser le cycle de vie de la gestion du risque tiers
Téléchargez notre eBook sur la gestion du risque tiers et obtenez une feuille de route complète pour le cycle de vie de votre gestion des risques tiers.
juin 02, 2025

eBook
Third-Party Risk
Le guide complet de la gestion des tiers
Il est impératif que les équipes en charge de la sécurité mettent en œuvre une approche holistique de la gestion des tiers.
juin 02, 2025

Blog
Rischio terze parti
Il malfunzionamento di CrowdStrike mette in evidenza l'importanza della gestione del rischio terze parti
Scopri i nostri approfondimenti e perché una solida gestione del rischio terze parti, quarte parti e parti aggiuntive è fondamentale.
Hannah Middleton
maggio 28, 2025 3 min read

Blog
Rischio terze parti
Il malfunzionamento di CrowdStrike mette in evidenza l'importanza della gestione del rischio terze parti
Scopri i nostri approfondimenti e perché una solida gestione del rischio terze parti, quarte parti e parti aggiuntive è fondamentale.
Hannah Middleton
maggio 28, 2025 3 min read
eBook
Third-Party Risk
Data privacy compliance and Third-Party Risk Management: A unified approach
These days, organizations are required to safeguard their customer data and comply with privacy regulations — a task that becomes even more challenging with the increase in third-party relationships.
May 23, 2025

eBook
Third-Party Risk
Data privacy compliance and Third-Party Risk Management: A unified approach
These days, organizations are required to safeguard their customer data and comply with privacy regulations — a task that becomes even more challenging with the increase in third-party relationships.
May 23, 2025

Demo
Third-Party Risk
OneTrust Demo-Video zum Digital Operational Resilience Act
Erfahren Sie, wie OneTrust das Management von IKT-Risiken und IKT-Drittanbietern vereinfacht und Finanzinstituten dabei hilft, die DORA-Verordnung wirkungsvoll umzusetzen.
Mai 22, 2025
Demo
Third-Party Risk
OneTrust Digital Operational Resilience Act DORA demo video
Discover how OneTrust helps financial institutions comply with the DORA regulation by streamlining ICT risk and third-party management at scale.
May 21, 2025
Demo
Third-Party Risk
OneTrust Digital Operational Resilience Act DORA demo video
Discover how OneTrust helps financial institutions comply with the DORA regulation by streamlining ICT risk and third-party management at scale.
May 21, 2025

On-demand webinars
Third-Party Risk
Integrated risk management: Aligning third party risk across the enterprise
Join this session to explore strategies for breaking down silos, integrating risk insights, and strengthening security and compliance postures with a unified risk management approach.
May 21, 2025

On-demand webinars
Third-Party Risk
Integrated risk management: Aligning third party risk across the enterprise
Join this session to explore strategies for breaking down silos, integrating risk insights, and strengthening security and compliance postures with a unified risk management approach.
May 21, 2025
eBook
Rischio terze parti
Ciclo di vita della gestione del rischio terze parti
Scarica il nostro eBook sulla gestione del rischio terze parti e ottieni un piano d'azione per il ciclo di vita del programma.
maggio 21, 2025

eBook
Rischio terze parti
Guida completa alla gestione del rischio terze parti
L'implementazione di un approccio globale alla gestione delle terze parti è essenziale per i team che si occupano di sicurezza.
maggio 21, 2025

eBook
Rischio terze parti
Ciclo di vita della gestione del rischio terze parti
Scarica il nostro eBook sulla gestione del rischio terze parti e ottieni un piano d'azione per il ciclo di vita del programma.
maggio 21, 2025
Infographic
Third-Party Risk
Spring 2025 product release for third-party management
OneTrust’s spring 2025 product release introduces three powerful features designed to accelerate contextual risk visibility by streamlining third-party risk assessment processes.
May 09, 2025

Infographic
Third-Party Risk
Spring 2025 product release for third-party management
OneTrust’s spring 2025 product release introduces three powerful features designed to accelerate contextual risk visibility by streamlining third-party risk assessment processes.
May 09, 2025

On-demand webinars
Third-Party Risk
Beyond compliance: Scaling third-party risk management with automation
Join this live webinar to explore how automated vendor assessments, real-time monitoring, and compliance workflows can enhance risk insights and operational efficiency.
May 07, 2025

On-demand webinars
Third-Party Risk
Beyond compliance: Scaling third-party risk management with automation
Join this live webinar to explore how automated vendor assessments, real-time monitoring, and compliance workflows can enhance risk insights and operational efficiency.
May 07, 2025

On-demand webinars
Third-Party Risk
Laying the foundation for effective third-party risk management
Join this webinar to discover how automation enhances third-party risk management. Learn best practices for vendor risk assessment, due diligence, and compliance.
April 30, 2025

On-demand webinars
Third-Party Risk
Laying the foundation for effective third-party risk management
Join this webinar to discover how automation enhances third-party risk management. Learn best practices for vendor risk assessment, due diligence, and compliance.
April 30, 2025

On-demand webinars
Third-Party Risk
Navigating the U.S. DOJ Cybersecurity Rule on Cross-Border Data Transfers: Key insights & compliance strategies
Join OneTrust and Deloitte to explore the U.S. DOJ Cybersecurity Rule, key risks, and best practices for managing cross-border data transfers and ensuring compliance.
April 21, 2025

On-demand webinars
Third-Party Risk
Navigating the U.S. DOJ Cybersecurity Rule on Cross-Border Data Transfers: Key insights & compliance strategies
Join OneTrust and Deloitte to explore the U.S. DOJ Cybersecurity Rule, key risks, and best practices for managing cross-border data transfers and ensuring compliance.
April 21, 2025

Blog
Rischio terze parti
Perché il team che si occupa della privacy e quello che gestisce il rischio terze parti devono lavorare insieme
La condivisione di informazioni e risorse tra i diversi compartimenti aziendali è utile per tutti i team che hanno l'obiettivo di mitigare i rischi per la privacy dei dati.
Scott Solomon
aprile 04, 2025 6 min read

Blog
Rischio terze parti
Perché il team che si occupa della privacy e quello che gestisce il rischio terze parti devono lavorare insieme
La condivisione di informazioni e risorse tra i diversi compartimenti aziendali è utile per tutti i team che hanno l'obiettivo di mitigare i rischi per la privacy dei dati.
Scott Solomon
aprile 04, 2025 6 min read

Blog
Rischio terze parti
Come scalare il tuo ecosistema di terze parti in modo sicuro
La tua azienda si affida molto a organizzazioni esterne per ottenere successo: un forte processo di gestione del rischio terze parti è quindi un requisito operativo fondamentale.
Jason Koestenblatt
aprile 04, 2025 6 min read

Blog
Rischio terze parti
Come scalare il tuo ecosistema di terze parti in modo sicuro
La tua azienda si affida molto a organizzazioni esterne per ottenere successo: un forte processo di gestione del rischio terze parti è quindi un requisito operativo fondamentale.
Jason Koestenblatt
aprile 04, 2025 6 min read

On-demand webinars
Third-Party Risk
Empowering business with Unified Data Privacy & TPRM
Join our webinar to explore actionable strategies powered by OneTrust solutions to foster collaboration across privacy and TPRM stakeholders to better support your organizations.
April 03, 2025

On-demand webinars
Third-Party Risk
Empowering business with Unified Data Privacy & TPRM
Join our webinar to explore actionable strategies powered by OneTrust solutions to foster collaboration across privacy and TPRM stakeholders to better support your organizations.
April 03, 2025

On-demand webinars
Third-Party Risk
Understanding the DORA: Unpacking risk and compliance requirements and best practices
Join our expert panel to explore DORA compliance post-deadline. Learn key lessons, risk challenges, and best practices for operational resilience.
April 01, 2025

On-demand webinars
Third-Party Risk
Understanding the DORA: Unpacking risk and compliance requirements and best practices
Join our expert panel to explore DORA compliance post-deadline. Learn key lessons, risk challenges, and best practices for operational resilience.
April 01, 2025

Webinar su richiesta
Rischio terze parti
Live Demo: Costruire un solido programma di gestione del rischio terze parti con OneTrust
Partecipa al nostro webinar per scoprire come la soluzione TPRM di OneTrust può rivoluzionare il tuo approccio alla gestione del rischio terze parti.
marzo 27, 2025

Webinar su richiesta
Rischio terze parti
Live Demo: Costruire un solido programma di gestione del rischio terze parti con OneTrust
Partecipa al nostro webinar per scoprire come la soluzione TPRM di OneTrust può rivoluzionare il tuo approccio alla gestione del rischio terze parti.
marzo 27, 2025

Blog
Third-Party Risk Management
Cómo escalar tu ecosistema de terceros de forma segura
Tu negocio depende en gran medida de organizaciones externas a la hora de ayudar a impulsar el éxito, lo que viene a significar que un sólido proceso de gestión de riesgos de terceros es un requisito operativo clave.
Jason Koestenblatt
marzo 26, 2025 6 min read

Blog
Third-Party Risk
Comment faire évoluer son écosystème de tiers en toute sécurité
Votre entreprise s’appuie largement sur des organisations externes pour assurer sa réussite, ce qui rend indispensable la mise en place d’un solide processus de gestion des risques liés aux tiers.
Jason Koestenblatt
mars 26, 2025 6 min read

Blog
Third-Party Risk
Comment faire évoluer son écosystème de tiers en toute sécurité
Votre entreprise s’appuie largement sur des organisations externes pour assurer sa réussite, ce qui rend indispensable la mise en place d’un solide processus de gestion des risques liés aux tiers.
Jason Koestenblatt
mars 26, 2025 6 min read

Blog
Third-Party Risk
Wachstum mit Weitblick: Drittparteien sicher managen
Für viele Unternehmen sind externe Partnerschaften heute ein entscheidender Erfolgsfaktor. Um diesen Erfolg nachhaltig zu sichern, ist ein strukturiertes und wirkungsvolles Risikomanagement im Umgang mit Drittparteien unverzichtbar.
Jason Koestenblatt
März 26, 2025 6 min read

Blog
Third-Party Risk Management
Cómo escalar tu ecosistema de terceros de forma segura
Tu negocio depende en gran medida de organizaciones externas a la hora de ayudar a impulsar el éxito, lo que viene a significar que un sólido proceso de gestión de riesgos de terceros es un requisito operativo clave.
Jason Koestenblatt
marzo 26, 2025 6 min read

Blog
Third-Party Risk
How to scale your third-party ecosystem securely
Your business relies heavily on external organizations to help drive success, which means a strong third-party risk management process is an operational requirement.
Jason Koestenblatt
March 26, 2025 6 min read

Blog
Third-Party Risk
Wachstum mit Weitblick: Drittparteien sicher managen
Für viele Unternehmen sind externe Partnerschaften heute ein entscheidender Erfolgsfaktor. Um diesen Erfolg nachhaltig zu sichern, ist ein strukturiertes und wirkungsvolles Risikomanagement im Umgang mit Drittparteien unverzichtbar.
Jason Koestenblatt
März 26, 2025 6 min read

Blog
Third-Party Risk
How to scale your third-party ecosystem securely
Your business relies heavily on external organizations to help drive success, which means a strong third-party risk management process is an operational requirement.
Jason Koestenblatt
March 26, 2025 6 min read

Blog
Third-Party Risk
Wie Sie ein Programm zum Management von Drittparteienrisiken starten: Leistung im Blick behalten und kontinuierlich optimieren
Wie Sie ein Programm zum Management von Drittparteienrisiken starten: Leistung im Blick behalten und kontinuierlich optimieren
Katrina Dalao
März 17, 2025 5 min read

Blog
Third-Party Risk
Wie Sie ein Programm zum Management von Drittparteienrisiken starten: Leistung im Blick behalten und kontinuierlich optimieren
Wie Sie ein Programm zum Management von Drittparteienrisiken starten: Leistung im Blick behalten und kontinuierlich optimieren
Katrina Dalao
März 17, 2025 5 min read

Blog
Third-Party Risk
Comprendre la directive NIS2 : renforcer la résilience opérationnelle dans toute l’Europe
Quel est l’impact de la réglementation NIS2 élargie sur la cybersécurité dans l’UE et quelles sont les conséquences pour les entreprises ?
mars 17, 2025

Blog
Third-Party Risk
Comprendre la directive NIS2 : renforcer la résilience opérationnelle dans toute l’Europe
Quel est l’impact de la réglementation NIS2 élargie sur la cybersécurité dans l’UE et quelles sont les conséquences pour les entreprises ?
mars 17, 2025

Blog
Third-Party Risk
Stellen Ihre Drittparteien ein Risiko für Ihre Datenschutz-Compliance dar?
Welche Rolle spielen Drittanbieter bei Ihren Datenschutzbemühungen? Erfahren Sie, wie sich beide Bereiche überschneiden und wie Sie Ihre Daten in Ihrer gesamten Lieferkette schützen können.
Katrina Dalao
März 17, 2025 10 min read

Blog
Third-Party Risk
Stellen Ihre Drittparteien ein Risiko für Ihre Datenschutz-Compliance dar?
Welche Rolle spielen Drittanbieter bei Ihren Datenschutzbemühungen? Erfahren Sie, wie sich beide Bereiche überschneiden und wie Sie Ihre Daten in Ihrer gesamten Lieferkette schützen können.
Katrina Dalao
März 17, 2025 10 min read

Blog
Rischio terze parti
Comprendere la normativa NIS2: rafforzamento della resilienza operativa in tutta Europa
In che modo l'espansione delle normative influisce sulla sicurezza informatica nell'UE e cosa significa per le aziende?
Jason Koestenblatt
marzo 07, 2025 5 min read

Blog
Rischio terze parti
Comprendere la normativa NIS2: rafforzamento della resilienza operativa in tutta Europa
In che modo l'espansione delle normative influisce sulla sicurezza informatica nell'UE e cosa significa per le aziende?
Jason Koestenblatt
marzo 07, 2025 5 min read

Webinar su richiesta
Rischio terze parti
DORA in Azione: Garantire la Compliance e il Successo con OneTrust
Partecipa al nostro webinar sul Digital Operational Resilience Act (DORA), ora attivo da oltre un mese.
marzo 06, 2025

Webinar su richiesta
Rischio terze parti
DORA in Azione: Garantire la Compliance e il Successo con OneTrust
Partecipa al nostro webinar sul Digital Operational Resilience Act (DORA), ora attivo da oltre un mese.
marzo 06, 2025

Blog
Third-Party Risk
Why privacy and third-party risk teams need to work together
Sharing information and resources across organizational silos is mutually beneficial for teams with the common goal of mitigating data privacy risk
Jason Koestenblatt
February 27, 2025 6 min read

Blog
Third-Party Risk
Why privacy and third-party risk teams need to work together
Sharing information and resources across organizational silos is mutually beneficial for teams with the common goal of mitigating data privacy risk
Jason Koestenblatt
February 27, 2025 6 min read
eBook
Rischio terze parti
Utilizzare la gestione delle terze parti per orientarsi nel panorama del rischio in diversi settori
Scarica questo eBook per esplorare la gestione delle terze parti in diversi settori e scoprire le considerazioni più importanti prima di implementare questo approccio nella tua organizzazione.
febbraio 21, 2025

Check-list
Third-Party Risk
6 étapes pour une gestion efficace des risques tiers
Découvrez notre check-list en six étapes pour un programme de gestion des risques tiers solide.
février 21, 2025

Check-list
Third-Party Risk
Êtes-vous prêt pour la conformité DORA ?
La loi Digital Operational Resilience Act (DORA) est la première réglementation à contrôler les fonctions de sécurité des entités financières dans l’Union Européenne. Découvrez notre check-list pour assurer votre mise en conformité !
février 21, 2025

eBook
Rischio terze parti
Utilizzare la gestione delle terze parti per orientarsi nel panorama del rischio in diversi settori
Scarica questo eBook per esplorare la gestione delle terze parti in diversi settori e scoprire le considerazioni più importanti prima di implementare questo approccio nella tua organizzazione.
febbraio 21, 2025

Check-list
Third-Party Risk
6 étapes pour une gestion efficace des risques tiers
Découvrez notre check-list en six étapes pour un programme de gestion des risques tiers solide.
février 21, 2025

Check-list
Third-Party Risk
Êtes-vous prêt pour la conformité DORA ?
La loi Digital Operational Resilience Act (DORA) est la première réglementation à contrôler les fonctions de sécurité des entités financières dans l’Union Européenne. Découvrez notre check-list pour assurer votre mise en conformité !
février 21, 2025

Blog
Rischio terze parti
Rischio terze parti per quanto riguarda l'intelligenza artificiale: un approccio globale alla valutazione dei vendor
La valutazione del rischio terze parti per quanto riguarda i vendor di intelligenza artificiale è di fondamentale importanza per la governance dell'IA, ma non è necessario iniziare questo processo da zero. Scopri di più su come adottare un approccio globale alle valutazioni dei vendor di intelligenza artificiale.
febbraio 13, 2025 4 min read

Blog
Rischio terze parti
Rischio terze parti per quanto riguarda l'intelligenza artificiale: un approccio globale alla valutazione dei vendor
La valutazione del rischio terze parti per quanto riguarda i vendor di intelligenza artificiale è di fondamentale importanza per la governance dell'IA, ma non è necessario iniziare questo processo da zero. Scopri di più su come adottare un approccio globale alle valutazioni dei vendor di intelligenza artificiale.
febbraio 13, 2025 4 min read

Lista di controllo
Rischio terze parti
6 passaggi per un'efficace gestione del rischio terze parti
Scopri il percorso relativo alla gestione efficace dei rischi terze parti grazie a una lista di controllo che delinea le sei fasi di un solido programma TPRM.
febbraio 12, 2025

Lista di controllo
Rischio terze parti
Hai tutto pronto per conformati al DORA?
Il regolamento sulla resilienza operativa digitale (Digital Operational Resilience Act, DORA) è il primo regolamento redatto per supervisionare la sicurezza delle entità finanziarie in tutta l'Unione europea.
febbraio 12, 2025

Lista di controllo
Rischio terze parti
6 passaggi per un'efficace gestione del rischio terze parti
Scopri il percorso relativo alla gestione efficace dei rischi terze parti grazie a una lista di controllo che delinea le sei fasi di un solido programma TPRM.
febbraio 12, 2025

Lista di controllo
Rischio terze parti
Hai tutto pronto per conformati al DORA?
Il regolamento sulla resilienza operativa digitale (Digital Operational Resilience Act, DORA) è il primo regolamento redatto per supervisionare la sicurezza delle entità finanziarie in tutta l'Unione europea.
febbraio 12, 2025

Blog
Rischio terze parti
Perché scegliere OneTrust per la gestione delle terze parti?
OneTrust semplifica la gestione delle terze parti, offrendo controllo e visibilità sul loro intero ciclo di vita.
Scott Solomon, Senior Manager, Product Marketing
febbraio 12, 2025 5 min read

Blog
Rischio terze parti
Perché scegliere OneTrust per la gestione delle terze parti?
OneTrust semplifica la gestione delle terze parti, offrendo controllo e visibilità sul loro intero ciclo di vita.
Scott Solomon, Senior Manager, Product Marketing
febbraio 12, 2025 5 min read

Blog
Rischio terze parti
Le terze parti costituiscono un ostacolo al conseguimento della conformità in materia di privacy?
Quale ruolo svolgono le terze parti nel tuo impegno a rispettare le normative sulla protezione della privacy? Scopri il modo in cui queste due aspetti coincidono e come garantire la sicurezza dei dati lungo tutta la catena di fornitura.
Katrina Dalao
febbraio 07, 2025 10 min read

Blog
Rischio terze parti
Le terze parti costituiscono un ostacolo al conseguimento della conformità in materia di privacy?
Quale ruolo svolgono le terze parti nel tuo impegno a rispettare le normative sulla protezione della privacy? Scopri il modo in cui queste due aspetti coincidono e come garantire la sicurezza dei dati lungo tutta la catena di fornitura.
Katrina Dalao
febbraio 07, 2025 10 min read
eBook
Third-Party Due Diligence
Understanding and implementing APRA's CPS 230 Standard
For financial institutions in Australia, the Australian Prudential Regulation Authority’s (APRA) CPS 230 standard is a clarion call to fortify cyber resilience.
February 05, 2025

eBook
Third-Party Due Diligence
Understanding and implementing APRA's CPS 230 Standard
For financial institutions in Australia, the Australian Prudential Regulation Authority’s (APRA) CPS 230 standard is a clarion call to fortify cyber resilience.
February 05, 2025

On-demand webinars
Third-Party Risk
Live Demo: Building a more resilient Third-Party Management program
Register for our live demo webinar to see how OneTrust Third-Party Management can revolutionize your third-party risk management approach.
January 30, 2025

Report
OneTrust è stata nominata leader nel report "Operational Resilience Software 2024"
Scarica il report di Verdantix per scoprire l'importanza della resilienza operativa per la tua azienda e perché OneTrust è stata nominata leader nel settore.
gennaio 28, 2025

Report
OneTrust è stata nominata leader nel report "Operational Resilience Software 2024"
Scarica il report di Verdantix per scoprire l'importanza della resilienza operativa per la tua azienda e perché OneTrust è stata nominata leader nel settore.
gennaio 28, 2025
Report
Privacy Automation
Una nuova direzione per i dati
Se da un lato l'intelligenza artificiale continua a offrire opportunità impareggiabili per l'innovazione aziendale, dall'altro presenta anche rischi che le organizzazioni devono affrontare con decisione attraverso programmi di governance scalabili che abbraccino più origini dati. Sei tendenze principali stanno determinando queste sfide.
gennaio 22, 2025
eBook
Rischio terze parti
Semplifica la gestione del rischio terze parti
Semplifica le relazioni con le terze parti ed evita errori comuni.
gennaio 22, 2025

eBook
Rischio terze parti
Semplifica la gestione del rischio terze parti
Semplifica le relazioni con le terze parti ed evita errori comuni.
gennaio 22, 2025

Report
Privacy Automation
Una nuova direzione per i dati
Se da un lato l'intelligenza artificiale continua a offrire opportunità impareggiabili per l'innovazione aziendale, dall'altro presenta anche rischi che le organizzazioni devono affrontare con decisione attraverso programmi di governance scalabili che abbraccino più origini dati. Sei tendenze principali stanno determinando queste sfide.
gennaio 22, 2025

Checklist
Third-Party Risk
Are you ready for DORA compliance?
The Digital Operational Resilience Act (DORA) is the first regulation to oversee the security functions of financial entities across the European Union.
January 16, 2025

Lista de comprobación
Third-Party Risk Management
¿Listo para cumplir con el reglamento DORA?
El Reglamento sobre resiliencia operativa digital (DORA) es la primera normativa que supervisa las funciones de seguridad de las entidades financieras en toda la Unión Europea.
enero 16, 2025

On-demand webinars
Third-Party Risk
DORA Compliance Countdown: Are you ready?
Join us to learn more about the Digital Operational Resilience Act (DORA) and how OneTrust can help organizations research, implement, and monitor compliance at scale with DORA and other related regulations and standards like NIS2 and ISO.
January 16, 2025

On-demand webinars
Third-Party Risk
DORA Compliance Countdown: Are you ready?
Join us to learn more about the Digital Operational Resilience Act (DORA) and how OneTrust can help organizations research, implement, and monitor compliance at scale with DORA and other related regulations and standards like NIS2 and ISO.
January 16, 2025

Checklist
Third-Party Risk
Are you ready for DORA compliance?
The Digital Operational Resilience Act (DORA) is the first regulation to oversee the security functions of financial entities across the European Union.
January 16, 2025

Checkliste
Third-Party Risk
DORA-Compliance: Ist Ihr Unternehmen vorbereitet?
Der Digital Operational Resilience Act (DORA) ist die erste EU-Verordnung, die die Sicherheitsfunktionen von Finanzunternehmen regelt.
Januar 16, 2025

Lista de comprobación
Third-Party Risk Management
¿Listo para cumplir con el reglamento DORA?
El Reglamento sobre resiliencia operativa digital (DORA) es la primera normativa que supervisa las funciones de seguridad de las entidades financieras en toda la Unión Europea.
enero 16, 2025

Próximos seminarios web
Third-Party Risk Management
Live Demo: Desarrollando un programa integral para la gestión de riesgos de terceros
¿Te resulta difícil mantenerte a la vanguardia en el siempre cambiante panorama de la gestión de riesgos de terceros (TPRM)? ¿Te gustaría automatizar tareas tediosas, ahorrar tiempo y reducir costes, todo mientras mejoras tu programa de TPRM? No estás solo. En el entorno empresarial actual, gestionar el riesgo de terceros es más crítico que nunca. Con tantas herramientas y procesos disponibles, saber por dónde empezar puede ser abrumador.
enero 16, 2025

Próximos seminarios web
Third-Party Risk Management
Live Demo: Desarrollando un programa integral para la gestión de riesgos de terceros
¿Te resulta difícil mantenerte a la vanguardia en el siempre cambiante panorama de la gestión de riesgos de terceros (TPRM)? ¿Te gustaría automatizar tareas tediosas, ahorrar tiempo y reducir costes, todo mientras mejoras tu programa de TPRM? No estás solo. En el entorno empresarial actual, gestionar el riesgo de terceros es más crítico que nunca. Con tantas herramientas y procesos disponibles, saber por dónde empezar puede ser abrumador.
enero 16, 2025

Blog
Third-Party Risk
Navigating Australia's CPS 230 to combat third-party risk
Learn about Australia's CPS 230, it's effects on cybersecurity in financial institutions, and recommendations on how business leaders can address compliance and third-party risk.
December 19, 2024 3 min read

Blog
Third-Party Risk
Navigating Australia's CPS 230 to combat third-party risk
Learn about Australia's CPS 230, it's effects on cybersecurity in financial institutions, and recommendations on how business leaders can address compliance and third-party risk.
December 19, 2024 3 min read

On-demand webinars
Third-Party Risk
Virtual Lunch and Learn: A deep dive into OneTrust's Third Party Management capabilities
Join us for a virtual Lunch & Learn session and explore how OneTrust’s Third Party Management solution can streamline your risk management processes.
December 17, 2024

On-demand webinars
Third-Party Risk
Virtual Lunch and Learn: A deep dive into OneTrust's Third Party Management capabilities
Join us for a virtual Lunch & Learn session and explore how OneTrust’s Third Party Management solution can streamline your risk management processes.
December 17, 2024

On-Demand-Webinare
Third-Party Risk
From reliance to resilience: Building a strong third-party risk management
With this webinar, you'll learn how to tackle the complexities of Third-Party Risk Management (TPRM). Explore real-world incidents, widespread challenges, regulatory expectations, and the key components of a robust TPRM framework.
Dezember 17, 2024

On-Demand-Webinare
Third-Party Risk
From reliance to resilience: Building a strong third-party risk management
With this webinar, you'll learn how to tackle the complexities of Third-Party Risk Management (TPRM). Explore real-world incidents, widespread challenges, regulatory expectations, and the key components of a robust TPRM framework.
Dezember 17, 2024

On-demand webinars
Technology Risk & Compliance
The PDPL in Saudi Arabia is now in effect: is your business ready?
Join our Saudi Arabia PDPL webinar for an overview on the data protection law, its requirements, and how to prepare for full enforcement.
December 12, 2024

On-demand webinars
Technology Risk & Compliance
The PDPL in Saudi Arabia is now in effect: is your business ready?
Join our Saudi Arabia PDPL webinar for an overview on the data protection law, its requirements, and how to prepare for full enforcement.
December 12, 2024

On-demand webinars
Third-Party Risk
Unpacking global regulatory frameworks to enhance third-party operational resilience
Register for this OneTrust webinar to learn about the relevant resilience focused requirements of DORA, NIS 2, and other global regulations.
December 11, 2024

On-demand webinars
Third-Party Risk
Unpacking global regulatory frameworks to enhance third-party operational resilience
Register for this OneTrust webinar to learn about the relevant resilience focused requirements of DORA, NIS 2, and other global regulations.
December 11, 2024

Bericht
OneTrust zum führenden Anbieter für Operational Resilience Software 2024 ernannt
Laden Sie diesen Verdantix-Bericht herunter und erfahren Sie, warum operative Resilienz für Ihr Unternehmen entscheidend ist - und warum OneTrust als führender Anbieter ausgezeichnet wurde.
Dezember 05, 2024

Bericht
OneTrust zum führenden Anbieter für Operational Resilience Software 2024 ernannt
Laden Sie diesen Verdantix-Bericht herunter und erfahren Sie, warum operative Resilienz für Ihr Unternehmen entscheidend ist - und warum OneTrust als führender Anbieter ausgezeichnet wurde.
Dezember 05, 2024

Actualités
OneTrust nommé leader dans le domaine du logiciel de résilience opérationnelle 2024
Rapport Verdantix : nommé leader de la résilience opérationnelle
décembre 05, 2024

Actualités
OneTrust nommé leader dans le domaine du logiciel de résilience opérationnelle 2024
Rapport Verdantix : nommé leader de la résilience opérationnelle
décembre 05, 2024

On-demand webinars
Technology Risk & Compliance
Understanding the NIS 2 Directive: Compliance insights and best practices
This DataGuidance webinar explores the latest and expected developments in the implementation of the NIS 2 Directive, focusing on practical compliance strategies to ensure your organization is prepared.
December 04, 2024

On-demand webinars
Technology Risk & Compliance
Understanding the NIS 2 Directive: Compliance insights and best practices
This DataGuidance webinar explores the latest and expected developments in the implementation of the NIS 2 Directive, focusing on practical compliance strategies to ensure your organization is prepared.
December 04, 2024

Blog
Third-Party Risk
Understanding NIS2: Strengthening operational resilience across Europe
How does expanded regulation impact cybersecurity in the EU and what will it mean for businesses?
Jason Koestenblatt
November 27, 2024 5 min read

Blog
Third-Party Risk
Understanding NIS2: Strengthening operational resilience across Europe
How does expanded regulation impact cybersecurity in the EU and what will it mean for businesses?
Jason Koestenblatt
November 27, 2024 5 min read

Blog
Third-Party Risk
NIS2 im Fokus: Stärkung der Cybersicherheit in Europa
Wie wirkt sich die verschärfte Regulierung auf die Cybersicherheit in der EU aus - und was bedeutet das für Ihr Unternehmen?
Jason Koestenblatt
November 27, 2024 5 min read

Blog
Third-Party Risk
NIS2 im Fokus: Stärkung der Cybersicherheit in Europa
Wie wirkt sich die verschärfte Regulierung auf die Cybersicherheit in der EU aus - und was bedeutet das für Ihr Unternehmen?
Jason Koestenblatt
November 27, 2024 5 min read

Blog
Third-Party Risk Management
Directiva NIS2: fortalecimiento de la resiliencia operativa en toda Europa
¿Cómo afecta la ampliación de la normativa a la ciberseguridad en la UE y qué significará esto para las empresas?
Jason Koestenblatt
noviembre 27, 2024 5 min read

Blog
Third-Party Risk Management
Directiva NIS2: fortalecimiento de la resiliencia operativa en toda Europa
¿Cómo afecta la ampliación de la normativa a la ciberseguridad en la UE y qué significará esto para las empresas?
Jason Koestenblatt
noviembre 27, 2024 5 min read

Próximos seminarios web
GRC y garantía de seguridad
Cumplimiento de NIS2: cómo resolver los retos de la normativa con una demostración práctica
Acompáñanos en esta sesión dónde repasaremos los principales requisitos de la normativa NIS2 y su impacto. Además, podrás asistir a una demostración práctica y conocer cómo OneTrust te ayuda a resolver los retos de gobernanza, gestión de riesgos y terceros, gestión de incidentes y cumplimiento asociados a la normativa.
noviembre 26, 2024

Próximos seminarios web
GRC y garantía de seguridad
Cumplimiento de NIS2: cómo resolver los retos de la normativa con una demostración práctica
Acompáñanos en esta sesión dónde repasaremos los principales requisitos de la normativa NIS2 y su impacto. Además, podrás asistir a una demostración práctica y conocer cómo OneTrust te ayuda a resolver los retos de gobernanza, gestión de riesgos y terceros, gestión de incidentes y cumplimiento asociados a la normativa.
noviembre 26, 2024
Infographic
Third-Party Risk
Rise above risk: Third-party management in technology
This infographic gives an overview on how third-party management affects technology, growing threats, and how OneTrust Third-Party Management can help combat them.
November 21, 2024

Infographic
Third-Party Risk
Rise above risk: Third-party management in technology
This infographic gives an overview on how third-party management affects technology, growing threats, and how OneTrust Third-Party Management can help combat them.
November 21, 2024

Evento presencial
Trust intelligence
OneTrust End of Year Lisboa
Pensamos que este é um ótimo momento para estarmos com vocês e, por isso, estamos muito felizes em anunciar a 1ª edição do OneTrust Day Portugal, um evento exclusivo para todo o país, onde vamos falar sobre os temas mais atuais e relevantes no mundo da Privacidade, Inteligência Artificial, Consentimento e Preferências e Gestão de Riscos de Terceiros.
novembro 21, 2024

Evento presencial
Trust intelligence
OneTrust End of Year Lisboa
Pensamos que este é um ótimo momento para estarmos com vocês e, por isso, estamos muito felizes em anunciar a 1ª edição do OneTrust Day Portugal, um evento exclusivo para todo o país, onde vamos falar sobre os temas mais atuais e relevantes no mundo da Privacidade, Inteligência Artificial, Consentimento e Preferências e Gestão de Riscos de Terceiros.
novembro 21, 2024
Informe
Privacy Automation
Definiendo la nueva dirección que están tomando los datos
Aunque la IA continúa ofreciendo oportunidades inigualables para la innovación empresarial, también presenta riesgos de los que las organizaciones deben ocuparse de manera proactiva a través de programas de gobernanza escalables que abarquen múltiples fuentes de datos. Hay seis tendencias clave que definen estos desafíos.
noviembre 13, 2024

Report
Privacy Automation
Defining a new direction for data
As AI continues to offer unparalleled opportunities for business innovation, it also presents risks that organizations must tackle head-on through scalable governance programs that span multiple data sources. Six key trends are defining these challenges.
November 13, 2024

Informe
Privacy Automation
Definiendo la nueva dirección que están tomando los datos
Aunque la IA continúa ofreciendo oportunidades inigualables para la innovación empresarial, también presenta riesgos de los que las organizaciones deben ocuparse de manera proactiva a través de programas de gobernanza escalables que abarquen múltiples fuentes de datos. Hay seis tendencias clave que definen estos desafíos.
noviembre 13, 2024

On-demand webinars
Third-Party Risk
Bill S-211: Will you be ready by May 31?
In this webinar, our experts will discuss the Canadian regulation and others like it globally, while providing actionable insights into building a robust and mature Third-party program.
November 07, 2024

On-demand webinars
Third-Party Risk
Bill S-211: Will you be ready by May 31?
In this webinar, our experts will discuss the Canadian regulation and others like it globally, while providing actionable insights into building a robust and mature Third-party program.
November 07, 2024

On-demand webinars
Third-Party Risk
Tackling IT security risks for banks in South Africa
Join our OneTrust webinar on tackling IT security risks for banks in South Africa. Explore strategies for safeguarding sensitive data, ensuring POPIA compliance, and managing cyber threats. Gain actionable insights to strengthen your security posture and build customer trust.
October 31, 2024

On-demand webinars
Third-Party Risk
Tackling IT security risks for banks in South Africa
Join our OneTrust webinar on tackling IT security risks for banks in South Africa. Explore strategies for safeguarding sensitive data, ensuring POPIA compliance, and managing cyber threats. Gain actionable insights to strengthen your security posture and build customer trust.
October 31, 2024

GRC e garanzia di sicurezza
Navigare la conformità al NIS2 con OneTrust
Partecipa al nostro webinar per approfondire i principali requisiti della Direttiva NIS2 e il suo impatto sul territorio italiano.
ottobre 24, 2024

GRC e garanzia di sicurezza
Navigare la conformità al NIS2 con OneTrust
Partecipa al nostro webinar per approfondire i principali requisiti della Direttiva NIS2 e il suo impatto sul territorio italiano.
ottobre 24, 2024

On-demand webinars
Privacy Automation
Build resiliency and operationalize compliance with OneTrust: Fall product release recap, 2024
Join our upcoming product release webinar to explore how these new capabilities can help your organization navigate complex frameworks, streamline third-party management, and accelerate AI and data innovation.
October 22, 2024

On-demand webinars
Privacy Automation
Build resiliency and operationalize compliance with OneTrust: Fall product release recap, 2024
Join our upcoming product release webinar to explore how these new capabilities can help your organization navigate complex frameworks, streamline third-party management, and accelerate AI and data innovation.
October 22, 2024
Libro electrónico
Third-Party Risk Management
Gestión de terceros y cumplimiento normativo de la privacidad de los datos: un enfoque unificado
Comprende la importancia de la privacidad de los datos en la gestión de riesgos de terceros y las 10 prácticas recomendadas para lograr el cumplimiento normativo en privacidad a la hora de trabajar con terceros.
octubre 21, 2024

Libro electrónico
Third-Party Risk Management
Gestión de terceros y cumplimiento normativo de la privacidad de los datos: un enfoque unificado
Comprende la importancia de la privacidad de los datos en la gestión de riesgos de terceros y las 10 prácticas recomendadas para lograr el cumplimiento normativo en privacidad a la hora de trabajar con terceros.
octubre 21, 2024

On-demand webinars
Third-Party Risk
Live Demo EMEA: Building a robust third-party risk management program with OneTrust
Join to explore how OneTrust's TPRM solution can revolutionize your third-party risk management approach. We will cover best practices for implementing and leveraging the software to minimize risks.
October 10, 2024

On-demand webinars
Third-Party Risk
Live Demo EMEA: Building a robust third-party risk management program with OneTrust
Join to explore how OneTrust's TPRM solution can revolutionize your third-party risk management approach. We will cover best practices for implementing and leveraging the software to minimize risks.
October 10, 2024

eBook
Third-Party Risk
Simplifying vendor risk management
Streamline third-party relationships and avoid common mistakes in the process.
October 03, 2024
Libro electrónico
Third-Party Risk Management
Cómo simplificar la gestión de riesgos de terceros
Simplifica las relaciones con terceros y evita los errores más comunes en el proceso.
octubre 03, 2024

Libro electrónico
Third-Party Risk Management
Cómo simplificar la gestión de riesgos de terceros
Simplifica las relaciones con terceros y evita los errores más comunes en el proceso.
octubre 03, 2024

Checklist
Third-Party Risk
Essential checklist for simplifying third-party risk management
Third-party management doesn’t have to be a complicated process for your business.
October 02, 2024

Checklist
Third-Party Risk
Essential checklist for simplifying third-party risk management
Third-party management doesn’t have to be a complicated process for your business.
October 02, 2024
Infographic
Third-Party Risk
Navigating risk in financial services with third-party management
Working with third parties introduces privacy and security risks, making compliance and business growth a balancing act.
October 01, 2024

Infographic
Third-Party Risk
Navigating risk in financial services with third-party management
Working with third parties introduces privacy and security risks, making compliance and business growth a balancing act.
October 01, 2024
Infographic
Third-Party Risk
Manufacturing risk: Managing third parties in the supply chain
Third-party management keeps manufacturing operations running smoothly by verifying vendor and supplier compliance with regulations.
September 30, 2024

Infographic
Third-Party Risk
Manufacturing risk: Managing third parties in the supply chain
Third-party management keeps manufacturing operations running smoothly by verifying vendor and supplier compliance with regulations.
September 30, 2024

Blog
Diligencia debida de terceros
La gestión de terceros es clave para la resiliencia empresarial | Blog | OneTrust
Supervisar las relaciones empresariales no consiste solo en controlar el riesgo, sino que las empresas deben comprender cómo gestionar a terceros de manera integral.
Jason Koestenblatt
septiembre 27, 2024

Blog
Diligencia debida de terceros
La gestión de terceros es clave para la resiliencia empresarial | Blog | OneTrust
Supervisar las relaciones empresariales no consiste solo en controlar el riesgo, sino que las empresas deben comprender cómo gestionar a terceros de manera integral.
Jason Koestenblatt
septiembre 27, 2024
eBook
Third-Party Risk
The complete guide to third-party management
It’s imperative for security teams to implement a holistic approach to third-party management.
September 27, 2024

Blog
Third-Party Due Diligence
Third-Party Management is Key to Business Resilience | Blog | OneTrust
Overseeing business relationships isn’t just about controlling risk — companies must understand how to manage third parties holistically.
Jason Koestenblatt
September 27, 2024

Blog
Third-Party Due Diligence
Third-Party Management is Key to Business Resilience | Blog | OneTrust
Overseeing business relationships isn’t just about controlling risk — companies must understand how to manage third parties holistically.
Jason Koestenblatt
September 27, 2024

Blog
Devoir de vigilance sur les tiers
Gestion des tiers : un élément essentiel pour la résilience des entreprises | Blog | OneTrust
Superviser les relations commerciales ne consiste pas seulement à contrôler les risques : les entreprises doivent comprendre comment gérer les tiers de manière holistique.
Jason Koestenblatt
septembre 27, 2024

Blog
Drittparteien-Due-Diligence
Drittparteienmanagement als Schüssel zur Unternehmensresilienz | Blog | OneTrust
Die effektive Steuerung von Geschäftsbeziehungen erfordert mehr als nur die Kontrolle von Risiken. Für ein erfolgreiches Drittparteienmanagement ist ein ganzheitlicher Ansatz erforderlich.
Jason Koestenblatt
September 27, 2024

eBook
Third-Party Risk
The complete guide to third-party management
It’s imperative for security teams to implement a holistic approach to third-party management.
September 27, 2024

Blog
Due diligence de terceiros
A gestão de terceiros é fundamental para a resiliência dos negócios | Blog | OneTrust
Supervisionar as relações comerciais não se trata apenas de controlar os riscos. As empresas precisam entender como gerenciar os terceiros de forma holística.
Jason Koestenblatt
setembro 27, 2024

Blog
Devoir de vigilance sur les tiers
Gestion des tiers : un élément essentiel pour la résilience des entreprises | Blog | OneTrust
Superviser les relations commerciales ne consiste pas seulement à contrôler les risques : les entreprises doivent comprendre comment gérer les tiers de manière holistique.
Jason Koestenblatt
septembre 27, 2024

Blog
Drittparteien-Due-Diligence
Drittparteienmanagement als Schüssel zur Unternehmensresilienz | Blog | OneTrust
Die effektive Steuerung von Geschäftsbeziehungen erfordert mehr als nur die Kontrolle von Risiken. Für ein erfolgreiches Drittparteienmanagement ist ein ganzheitlicher Ansatz erforderlich.
Jason Koestenblatt
September 27, 2024

Blog
Due diligence de terceiros
A gestão de terceiros é fundamental para a resiliência dos negócios | Blog | OneTrust
Supervisionar as relações comerciais não se trata apenas de controlar os riscos. As empresas precisam entender como gerenciar os terceiros de forma holística.
Jason Koestenblatt
setembro 27, 2024
Libro electrónico
Third-Party Risk Management
Guía completa sobre la gestión de terceros
Para los equipos de seguridad, es clave implementar un enfoque exhaustivo en lo que respecta a la gestión de terceros.
septiembre 27, 2024

Libro electrónico
Third-Party Risk Management
Guía completa sobre la gestión de terceros
Para los equipos de seguridad, es clave implementar un enfoque exhaustivo en lo que respecta a la gestión de terceros.
septiembre 27, 2024

On-demand webinars
Third-Party Risk
Strengthen your third-party ecosystem: Strategies to combat modern slavery, anti-bribery, and corruption
Join our upcoming webinar to learn how to navigate the complexities of managing modern slavery, anti-bribery, and corruption within your third-party ecosystem.
September 26, 2024

On-demand webinars
Third-Party Risk
Strengthen your third-party ecosystem: Strategies to combat modern slavery, anti-bribery, and corruption
Join our upcoming webinar to learn how to navigate the complexities of managing modern slavery, anti-bribery, and corruption within your third-party ecosystem.
September 26, 2024

On-demand webinars
Third-Party Risk
PDPL and third-party risk
Join us in a webinar where we will discuss PDPL, third-party risk, and compliance best practices. Learn how you can automate and simplify your third-party management program with OneTrust.
September 19, 2024

On-demand webinars
Third-Party Risk
PDPL and third-party risk
Join us in a webinar where we will discuss PDPL, third-party risk, and compliance best practices. Learn how you can automate and simplify your third-party management program with OneTrust.
September 19, 2024

On-demand webinars
Third-Party Risk
APAC - Third-party risk management and due diligence: What’s the difference and why does it matter?
Join this APAC webinar to learn the unique competencies of third-party risk and due diligence programs and examine when and how to align them to maximize the effectiveness of each.
September 18, 2024

On-demand webinars
Third-Party Risk
Navigating the intersection: Third-party risk management in South Africa's evolving data landscape
Amidst South Africa's dynamic AI terrain and evolving data privacy regulations like POPIA, mastering third-party risk management is paramount. This session explores the balance between AI innovation and data protection.
September 18, 2024

On-demand webinars
Third-Party Risk
APAC - Third-party risk management and due diligence: What’s the difference and why does it matter?
Join this APAC webinar to learn the unique competencies of third-party risk and due diligence programs and examine when and how to align them to maximize the effectiveness of each.
September 18, 2024

On-demand webinars
Third-Party Risk
Navigating the intersection: Third-party risk management in South Africa's evolving data landscape
Amidst South Africa's dynamic AI terrain and evolving data privacy regulations like POPIA, mastering third-party risk management is paramount. This session explores the balance between AI innovation and data protection.
September 18, 2024

Blog
Rischio terze parti
Come gestire e misurare i rischi da parte di terzi in tutta l'azienda
Scopri come rafforzare il tuo programma di conformità con un programma unificato di gestione delle terze parti.
Jason Koestenblatt
settembre 11, 2024 5 min read

Blog
Rischio terze parti
Come gestire e misurare i rischi da parte di terzi in tutta l'azienda
Scopri come rafforzare il tuo programma di conformità con un programma unificato di gestione delle terze parti.
Jason Koestenblatt
settembre 11, 2024 5 min read

Blog
Third-Party Risk Management
Cómo gestionar y medir el riesgo de terceros en tu negocio
Aprende a potenciar tu programa de cumplimiento normativo con un programa de gestión de terceros unificado.
Jason Koestenblatt
septiembre 11, 2024 5 min read

Blog
Third-Party Risk Management
Cómo gestionar y medir el riesgo de terceros en tu negocio
Aprende a potenciar tu programa de cumplimiento normativo con un programa de gestión de terceros unificado.
Jason Koestenblatt
septiembre 11, 2024 5 min read

Blog
Third-Party Risk
Comment gérer et mesurer le risque tiers dans l’ensemble de votre entreprise
Découvrez comment renforcer votre programme de conformité grâce à un programme de gestion tiers unifié.
Jason Koestenblatt
septembre 11, 2024 5 min read
E-Book
Third-Party Risk
Leitfaden für das Drittparteienrisikomanagement
Dieser Leitfaden zum Risikomanagement für Dritte gibt Ihnen einen Überblick über die Voraussetzungen für den Aufbau eines erfolgreichen Risikomanagementprogramms für Dritte.
September 03, 2024

E-Book
Third-Party Risk
Leitfaden für das Drittparteienrisikomanagement
Dieser Leitfaden zum Risikomanagement für Dritte gibt Ihnen einen Überblick über die Voraussetzungen für den Aufbau eines erfolgreichen Risikomanagementprogramms für Dritte.
September 03, 2024
eBook
Third-Party Risk
Deploying third-party management to navigate risk across industries
Download this eBook to explore third-party management across industries and key considerations before bringing this approach organization-wide.
August 06, 2024
E-Book
Third-Party Risk
Erfolgreiches Drittparteienmanagement: Risiken branchenübergreifend managen
Erfahren Sie in diesem E-Book, wie Sie Drittparteiemanagement erfolgreich in Ihrem Unternehmen etablieren - mit praxisnahen Einblicken aus verschiedenen Branchen.
August 06, 2024

eBook
Third-Party Risk
Deploying third-party management to navigate risk across industries
Download this eBook to explore third-party management across industries and key considerations before bringing this approach organization-wide.
August 06, 2024

E-Book
Third-Party Risk
Erfolgreiches Drittparteienmanagement: Risiken branchenübergreifend managen
Erfahren Sie in diesem E-Book, wie Sie Drittparteiemanagement erfolgreich in Ihrem Unternehmen etablieren - mit praxisnahen Einblicken aus verschiedenen Branchen.
August 06, 2024
Libro electrónico
Third-Party Risk Management
Implementación de la gestión de terceros para administrar el riesgo en todos los sectores
Descarga este eBook para explorar la gestión de terceros en todos los sectores y las consideraciones clave antes de aplicar este enfoque a toda la organización.
agosto 06, 2024
eBook
Third-Party Risk
Déployer la gestion des tiers pour gérer les risques dans tous les secteurs
Téléchargez cet eBook pour explorer la gestion des tiers dans tous les secteurs et les considérations clés pour adopter cette approche à l’échelle de l’organisation.
août 06, 2024

Libro electrónico
Third-Party Risk Management
Implementación de la gestión de terceros para administrar el riesgo en todos los sectores
Descarga este eBook para explorar la gestión de terceros en todos los sectores y las consideraciones clave antes de aplicar este enfoque a toda la organización.
agosto 06, 2024

eBook
Third-Party Risk
Déployer la gestion des tiers pour gérer les risques dans tous les secteurs
Téléchargez cet eBook pour explorer la gestion des tiers dans tous les secteurs et les considérations clés pour adopter cette approche à l’échelle de l’organisation.
août 06, 2024

Blog
Third-Party Risk
Preparing for DORA: Updated rules for the EU resilience regulation
Explore DORA's goals, the new requirements, and how organizations can prepare now to meet the framework ahead of the January 2025 deadline.
Hannah Middleton
August 02, 2024 2 min read

Blog
Third-Party Risk Management
Cómo prepararse frente a la DORA: Reglas actualizadas para la Ley de Resiliencia Operativa Digital
Analiza los objetivos de la DORA, los nuevos requisitos y cómo las organizaciones pueden prepararse en la actualidad para cumplir con el marco antes del plazo de enero de 2025.
Hannah Middleton
agosto 02, 2024 2 min read

Blog
Third-Party Risk
Preparing for DORA: Updated rules for the EU resilience regulation
Explore DORA's goals, the new requirements, and how organizations can prepare now to meet the framework ahead of the January 2025 deadline.
Hannah Middleton
August 02, 2024 2 min read

Blog
Third-Party Risk Management
Cómo prepararse frente a la DORA: Reglas actualizadas para la Ley de Resiliencia Operativa Digital
Analiza los objetivos de la DORA, los nuevos requisitos y cómo las organizaciones pueden prepararse en la actualidad para cumplir con el marco antes del plazo de enero de 2025.
Hannah Middleton
agosto 02, 2024 2 min read

Blog
Third-Party Risk
Se préparer à DORA : règles actualisées du règlement sur la résilience opérationnelle numérique dans le secteur financier
Explorez les objectifs de DORA, les nouvelles exigences et la manière dont les organisations peuvent se préparer dès maintenant à respecter le cadre de référence avant l’échéance de janvier 2025.
Hannah Middleton
août 02, 2024 2 min read

Blog
Third-Party Risk
Se préparer à DORA : règles actualisées du règlement sur la résilience opérationnelle numérique dans le secteur financier
Explorez les objectifs de DORA, les nouvelles exigences et la manière dont les organisations peuvent se préparer dès maintenant à respecter le cadre de référence avant l’échéance de janvier 2025.
Hannah Middleton
août 02, 2024 2 min read

Blog
Third-Party Risk
CrowdStrike-Vorfall rückt Drittparteirisiken ins Rampenlicht
Unsere zentralen Erkenntnisse machen deutlich, warum ein starkes Risikomanagement entlang der gesamten Lieferkette heute unverzichtbar ist.
Hannah Middleton
Juli 25, 2024 3 min read

Blog
Third-Party Risk
CrowdStrike-Vorfall rückt Drittparteirisiken ins Rampenlicht
Unsere zentralen Erkenntnisse machen deutlich, warum ein starkes Risikomanagement entlang der gesamten Lieferkette heute unverzichtbar ist.
Hannah Middleton
Juli 25, 2024 3 min read

Blog
Third-Party Risk Management
La interrupción de CrowdStrike pone en el foco el riesgo de terceros
Consulta nuestra información clave y descubre por qué es esencial una gestión de riesgos sólida para los terceros, las cuartas partes y demás.
Hannah Middleton
julio 25, 2024 3 min read

Blog
Third-Party Risk Management
La interrupción de CrowdStrike pone en el foco el riesgo de terceros
Consulta nuestra información clave y descubre por qué es esencial una gestión de riesgos sólida para los terceros, las cuartas partes y demás.
Hannah Middleton
julio 25, 2024 3 min read

Blog
Third-Party Risk
La panne CrowdStrike met en évidence les risques liés aux tiers
Découvrez nos informations clés et pourquoi une gestion robuste des risques tiers, des quatrièmes parties et au-delà est cruciale.
Hannah Middleton
juillet 25, 2024 3 min read

Blog
Third-Party Risk
La panne CrowdStrike met en évidence les risques liés aux tiers
Découvrez nos informations clés et pourquoi une gestion robuste des risques tiers, des quatrièmes parties et au-delà est cruciale.
Hannah Middleton
juillet 25, 2024 3 min read

Blog
Third-Party Risk
CrowdStrike outage highlights third-party risk
See our key insights and discover why robust risk management across third parties, fourth parties, and beyond is crucial.
Hannah Middleton
July 25, 2024 3 min read

On-demand webinars
Third-Party Risk
Third-Party AI: Procurement and risk management best practices
As innovation teams race to integrate AI into their products and services, new challenges arise for development teams leveraging third-party models. Join the webinar to gain insights on how to navigate AI vendors while mitigating third-party risks.
July 25, 2024

On-demand webinars
Third-Party Risk
Third-Party AI: Procurement and risk management best practices
As innovation teams race to integrate AI into their products and services, new challenges arise for development teams leveraging third-party models. Join the webinar to gain insights on how to navigate AI vendors while mitigating third-party risks.
July 25, 2024

Blog
Third-Party Risk
CrowdStrike outage highlights third-party risk
See our key insights and discover why robust risk management across third parties, fourth parties, and beyond is crucial.
Hannah Middleton
July 25, 2024 3 min read

On-demand webinars
Privacy Management
New European cyber laws: What you need to know
The EU has adopted several new Cyber Laws that will impact many businesses and will come into force over the next few months (in October in the case of NISD2) and require actions now. Join the webinar to learn about the latest cyber developments.
July 23, 2024

On-demand webinars
Privacy Management
New European cyber laws: What you need to know
The EU has adopted several new Cyber Laws that will impact many businesses and will come into force over the next few months (in October in the case of NISD2) and require actions now. Join the webinar to learn about the latest cyber developments.
July 23, 2024

On-demand webinars
Third-Party Risk
Master Third-Party Risk Management with OneTrust: Live Demo and Secrets to Success
Join this free demo session to learn the ins an outs of OneTrust’s Third-Party Management solution.
July 02, 2024

Evento presencial
Trust intelligence
OneTrust Day Portugal
Pensamos que este é um ótimo momento para estarmos com vocês e, por isso, estamos muito felizes em anunciar a 1ª edição do OneTrust Day Portugal, um evento exclusivo para todo o país, onde vamos falar sobre os temas mais atuais e relevantes no mundo da Privacidade, Inteligência Artificial, Consentimento e Preferências e Gestão de Riscos de Terceiros.
junho 27, 2024

Evento presencial
Trust intelligence
OneTrust Day Portugal
Pensamos que este é um ótimo momento para estarmos com vocês e, por isso, estamos muito felizes em anunciar a 1ª edição do OneTrust Day Portugal, um evento exclusivo para todo o país, onde vamos falar sobre os temas mais atuais e relevantes no mundo da Privacidade, Inteligência Artificial, Consentimento e Preferências e Gestão de Riscos de Terceiros.
junho 27, 2024

On-demand webinars
Third-Party Risk
Protecting your reputation: 3 ways a unified third-party management program can help
This webinar will show you how to develop strategies for assessing reputational risks as it relates to third parties and the impact of third-party relationships.
June 12, 2024

On-demand webinars
Third-Party Risk
Protecting your reputation: 3 ways a unified third-party management program can help
This webinar will show you how to develop strategies for assessing reputational risks as it relates to third parties and the impact of third-party relationships.
June 12, 2024

On-demand webinars
Third-Party Risk
Third-Party risk management and due diligence: What's the difference and why does it matter?
In this webinar, we’ll discuss the unique competencies of third-party risk and due diligence programs and examine when and how to align them.
May 08, 2024

On-demand webinars
Third-Party Risk
Third-Party risk management and due diligence: What's the difference and why does it matter?
In this webinar, we’ll discuss the unique competencies of third-party risk and due diligence programs and examine when and how to align them.
May 08, 2024

Blog
Rischio terze parti
Esplora il regolamento sulla resilienza operativa digitale (DORA) con OneTrust
Leggi il nostro articolo sul regolamento sulla resilienza operativa digitale (Digital Operational Resilience Act, DORA) e su come le aziende possono gestire efficacemente i rischi legati alle TIC e alle terze parti per garantire la conformità
Katrina Dalao
aprile 29, 2024 5 min read

Blog
Rischio terze parti
Esplora il regolamento sulla resilienza operativa digitale (DORA) con OneTrust
Leggi il nostro articolo sul regolamento sulla resilienza operativa digitale (Digital Operational Resilience Act, DORA) e su come le aziende possono gestire efficacemente i rischi legati alle TIC e alle terze parti per garantire la conformità
Katrina Dalao
aprile 29, 2024 5 min read

Blog
Third-Party Risk Management
Explorando el Reglamento sobre resiliencia operativa digital (DORA) con OneTrust
Consulta nuestro artículo sobre el Reglamento sobre resiliencia operativa digital (DORA) y cómo las organizaciones pueden gestionar de forma eficaz el riesgo de las TIC y el riesgo de terceros con objeto de garantizar el cumplimiento normativo
Katrina Dalao
abril 29, 2024 5 min read

Blog
Third-Party Risk Management
Explorando el Reglamento sobre resiliencia operativa digital (DORA) con OneTrust
Consulta nuestro artículo sobre el Reglamento sobre resiliencia operativa digital (DORA) y cómo las organizaciones pueden gestionar de forma eficaz el riesgo de las TIC y el riesgo de terceros con objeto de garantizar el cumplimiento normativo
Katrina Dalao
abril 29, 2024 5 min read
Infographic
Third-Party Risk
Streamline compliance with the Digital Operational Resilience Act (DORA)
Download our infographic to learn about the new DORA regulation, who needs to comply, and how OneTrust can help streamline the process.
April 29, 2024

Infographic
Third-Party Risk
Streamline compliance with the Digital Operational Resilience Act (DORA)
Download our infographic to learn about the new DORA regulation, who needs to comply, and how OneTrust can help streamline the process.
April 29, 2024

Blog
Third-Party Risk
Navigating the Digital Operational Resilience Act (DORA) with OneTrust
Read our article on the Digital Operational Resilience Act (DORA) and how organizations can effectively manage ICT risk and third-party risk to ensure compliance
Katrina Dalao
April 29, 2024 5 min read

Blog
Third-Party Risk
Navigating the Digital Operational Resilience Act (DORA) with OneTrust
Read our article on the Digital Operational Resilience Act (DORA) and how organizations can effectively manage ICT risk and third-party risk to ensure compliance
Katrina Dalao
April 29, 2024 5 min read

Webinaires à la demande
Third-Party Risk
Les Top challenges en matière de Gestion des Risques Tiers
Webinar : comment relever les défis de la gestion des risques tiers tels que : la complexité croissante des réseaux de fournisseurs, la conformité réglementaire changeante et la nécessité de gérer efficacement les relations avec les tiers pour atténuer les risques et maintenir la continuité des activités.
avril 25, 2024

Webinaires à la demande
Third-Party Risk
Les Top challenges en matière de Gestion des Risques Tiers
Webinar : comment relever les défis de la gestion des risques tiers tels que : la complexité croissante des réseaux de fournisseurs, la conformité réglementaire changeante et la nécessité de gérer efficacement les relations avec les tiers pour atténuer les risques et maintenir la continuité des activités.
avril 25, 2024

Seminarios web bajo demanda
Third-Party Risk Management
DORA y sus estándares: una sesión práctica con OneTrust y Deloitte
Acompáñanos el próximo 24 de abril a esta sesión y descubre como OneTrust y Deloitte facilitan la adopción de DORA y sus estándares asociados en una sesión práctica donde veremos desde la Gestión de Riesgos y la Gestión de Incidentes, hasta el Registro de Información de la cadena de suministro.
abril 24, 2024

Seminarios web bajo demanda
Third-Party Risk Management
DORA y sus estándares: una sesión práctica con OneTrust y Deloitte
Acompáñanos el próximo 24 de abril a esta sesión y descubre como OneTrust y Deloitte facilitan la adopción de DORA y sus estándares asociados en una sesión práctica donde veremos desde la Gestión de Riesgos y la Gestión de Incidentes, hasta el Registro de Información de la cadena de suministro.
abril 24, 2024

On-demand webinars
Third-Party Risk
5 Best practices for increasing resilience when working with third parties webinar
Learn how to leverage financial, operations, compliance, ESG, and cyber scores to drive resilience insights and detect possible supply chain disruptions.
April 18, 2024

On-demand webinars
Third-Party Risk
5 Best practices for increasing resilience when working with third parties webinar
Learn how to leverage financial, operations, compliance, ESG, and cyber scores to drive resilience insights and detect possible supply chain disruptions.
April 18, 2024
Infographie
Third-Party Risk
4 enjeux majeurs pour les RSSI
Quels sont les principaux défis auxquels les RSSI sont confrontés ? Téléchargez cette infographie pour connaître l'avis d'experts de tous les secteurs d'activité.
avril 16, 2024

Infographie
Third-Party Risk
4 enjeux majeurs pour les RSSI
Quels sont les principaux défis auxquels les RSSI sont confrontés ? Téléchargez cette infographie pour connaître l'avis d'experts de tous les secteurs d'activité.
avril 16, 2024

Checklist
Third-Party Risk
6 steps to effective third-party risk management
See the path to managing third-party risk effectively with a checklist that outlines the six steps for a sound TPRM program.
March 29, 2024

Checkliste
Third-Party Risk
6 Schritte zu einem effektiven Drittparteien-Risikomanagement
Nutzen Sie unsere Checkliste mit den sechs Schritten zu einem robusten TPRM-Programm, um Drittparteienrisiken effektiv zu managen.
März 29, 2024

Checklist
Third-Party Risk
6 steps to effective third-party risk management
See the path to managing third-party risk effectively with a checklist that outlines the six steps for a sound TPRM program.
March 29, 2024

On-demand webinars
Third-Party Risk
TPRM privacy compliance: 10 best practices when working with third parties
How can you build a privacy-focused TPRM program? In this webinar, we discuss best practices for privacy compliance when working with third parties, from onboarding to offboarding.
March 13, 2024

On-demand webinars
Third-Party Risk
TPRM privacy compliance: 10 best practices when working with third parties
How can you build a privacy-focused TPRM program? In this webinar, we discuss best practices for privacy compliance when working with third parties, from onboarding to offboarding.
March 13, 2024

Blog
Third-Party Risk
IA & risques tiers : Une approche complète de l'évaluation des fournisseurs
Risques tiers liés à l'IA - Comment rester en contrôle ? Découvrez notre approche complète pour l'évaluation de vos fournisseurs
mars 04, 2024 4 min read

Blog
Third-Party Risk
IA & risques tiers : Une approche complète de l'évaluation des fournisseurs
Risques tiers liés à l'IA - Comment rester en contrôle ? Découvrez notre approche complète pour l'évaluation de vos fournisseurs
mars 04, 2024 4 min read

Video
Third-Party Risk
6 must-know trends in third-party management
Watch this video for the five top trends shaping the third-party management industry this year.
February 15, 2024

Video
Third-Party Risk
6 must-know trends in third-party management
Watch this video for the five top trends shaping the third-party management industry this year.
February 15, 2024

Blog
Third-Party Risk
KI-Risiken durch Drittparteien: Ein ganzheitlicher Ansatz zur Bewertung von Anbietern
Die Risikobewertung von KI-Anbietern ist ein wichtiger Bestandteil der KI-Governance, aber Sie müssen Ihren Bewertungsprozess nicht bei Null beginnen. Erfahren Sie mehr darüber, wie Sie einen ganzheitlichen Ansatz bei der Bewertung von KI-Anbietern verfolgen.
Marco Barone
Februar 06, 2024 4 min read

Blog
Third-Party Risk
KI-Risiken durch Drittparteien: Ein ganzheitlicher Ansatz zur Bewertung von Anbietern
Die Risikobewertung von KI-Anbietern ist ein wichtiger Bestandteil der KI-Governance, aber Sie müssen Ihren Bewertungsprozess nicht bei Null beginnen. Erfahren Sie mehr darüber, wie Sie einen ganzheitlichen Ansatz bei der Bewertung von KI-Anbietern verfolgen.
Marco Barone
Februar 06, 2024 4 min read

Blog
Third-Party Risk Management
Riesgo de IA de terceros: un enfoque integral para las evaluaciones de proveedores
Evaluar el riesgo de terceros de los proveedores de IA es fundamental para la gobernanza de la IA, pero no tienes por qué iniciar tu proceso de evaluación desde cero. Obtén más información sobre cómo adoptar un enfoque integral con respecto a las evaluaciones de proveedores para la IA.
Marco Barone
febrero 06, 2024 4 min read

Blog
Third-Party Risk Management
Riesgo de IA de terceros: un enfoque integral para las evaluaciones de proveedores
Evaluar el riesgo de terceros de los proveedores de IA es fundamental para la gobernanza de la IA, pero no tienes por qué iniciar tu proceso de evaluación desde cero. Obtén más información sobre cómo adoptar un enfoque integral con respecto a las evaluaciones de proveedores para la IA.
Marco Barone
febrero 06, 2024 4 min read

Blog
Third-Party Risk
Risque tiers lié à l’IA : une approche holistique de l’évaluation des fournisseurs
L’évaluation du risque tiers pour les fournisseurs d’IA est essentielle à la gouvernance de l’IA, mais vous n’avez pas à commencer votre processus d’évaluation à partir de zéro. Pour en savoir plus sur l’adoption d’une approche holistique de l’évaluation des fournisseurs pour l’IA.
Marco Barone
février 06, 2024 4 min read

Blog
Third-Party Risk
Risque tiers lié à l’IA : une approche holistique de l’évaluation des fournisseurs
L’évaluation du risque tiers pour les fournisseurs d’IA est essentielle à la gouvernance de l’IA, mais vous n’avez pas à commencer votre processus d’évaluation à partir de zéro. Pour en savoir plus sur l’adoption d’une approche holistique de l’évaluation des fournisseurs pour l’IA.
Marco Barone
février 06, 2024 4 min read

Blog
Third-Party Risk
Third-Party AI Risk: A Holistic Approach to Vendor Assessment
Assessing third-party risk for AI vendors is critical to AI governance, but you don’t have to start your assessment process from scratch. Learn more about taking a holistic approach to vendor assessments for AI.
Marco Barone
February 06, 2024 4 min read

Blog
Third-Party Risk
Third-Party AI Risk: A Holistic Approach to Vendor Assessment
Assessing third-party risk for AI vendors is critical to AI governance, but you don’t have to start your assessment process from scratch. Learn more about taking a holistic approach to vendor assessments for AI.
Marco Barone
February 06, 2024 4 min read

Checklist
AI Governance
Questions to add to existing vendor assessments for AI
Managing third-party risk is a critical part of AI governance, but you don’t have to start from scratch. Use these questions to adapt your existing vendor assessments to be used for AI.
January 31, 2024

Checklist
AI Governance
Questions to add to existing vendor assessments for AI
Managing third-party risk is a critical part of AI governance, but you don’t have to start from scratch. Use these questions to adapt your existing vendor assessments to be used for AI.
January 31, 2024
Infographic
Third-Party Risk
4 top-of-mind challenges for CISOs
What key challenges do CISOs face going into the new year? Download this infographic to hear what experts from industries across the board have to say.
January 30, 2024

Infographic
Third-Party Risk
4 top-of-mind challenges for CISOs
What key challenges do CISOs face going into the new year? Download this infographic to hear what experts from industries across the board have to say.
January 30, 2024

On-demand webinars
Third-Party Risk
A look back at 2023 & third-party management trends for the new year
Join this webinar as we discuss key trends for third-party management and lessons learned over the last year.
January 24, 2024

On-demand webinars
Third-Party Risk
A look back at 2023 & third-party management trends for the new year
Join this webinar as we discuss key trends for third-party management and lessons learned over the last year.
January 24, 2024

On-demand webinars
Third-Party Risk
Utilizing inherent risk for more efficient third-party management
Insight into your third parties’ inherent risks can change the way you run your TPM program.
November 30, 2023

On-demand webinars
Third-Party Risk
Utilizing inherent risk for more efficient third-party management
Insight into your third parties’ inherent risks can change the way you run your TPM program.
November 30, 2023

On-demand webinars
Third-Party Risk
Elevating third-party safety: The art of TPRM and TPDD integration
Join our webinar to learn the primary goals of successful Third-Party Risk and Third-Party Due Diligence programs.
November 21, 2023

On-demand webinars
Third-Party Risk
Elevating third-party safety: The art of TPRM and TPDD integration
Join our webinar to learn the primary goals of successful Third-Party Risk and Third-Party Due Diligence programs.
November 21, 2023

Blog
Third-Party Risk Management
¿Son tus terceros una obligación en cuanto al cumplimiento normativo en materia de privacidad?
¿Qué papel desempeñan los terceros en tus esfuerzos de cumplimiento normativo en materia de privacidad? Descubre cómo se solapan las dos funciones y cómo mantener los datos seguros a lo largo de toda tu cadena de suministros.
Katrina Dalao
noviembre 07, 2023 10 min read

Blog
Third-Party Risk Management
¿Son tus terceros una obligación en cuanto al cumplimiento normativo en materia de privacidad?
¿Qué papel desempeñan los terceros en tus esfuerzos de cumplimiento normativo en materia de privacidad? Descubre cómo se solapan las dos funciones y cómo mantener los datos seguros a lo largo de toda tu cadena de suministros.
Katrina Dalao
noviembre 07, 2023 10 min read

Blog
Third-Party Risk
Vos tiers constituent-ils un risque pour votre conformité en termes de confidentialité ?
Quel rôle les tiers jouent-ils dans votre conformité en matière de confidentialité ? Découvrez les connections entre les deux fonctions et comment garantir la sécurité des données dans votre chaîne d’approvisionnement.
Katrina Dalao
novembre 07, 2023 10 min read

Blog
Third-Party Risk
Vos tiers constituent-ils un risque pour votre conformité en termes de confidentialité ?
Quel rôle les tiers jouent-ils dans votre conformité en matière de confidentialité ? Découvrez les connections entre les deux fonctions et comment garantir la sécurité des données dans votre chaîne d’approvisionnement.
Katrina Dalao
novembre 07, 2023 10 min read

Blog
Third-Party Risk
Are your third parties a privacy compliance liability?
What role do third parties play in your privacy compliance efforts? Learn how the two functions overlap and ways to keep data secure across your supply chain.
Katrina Dalao
November 07, 2023 10 min read

Blog
Third-Party Risk
Are your third parties a privacy compliance liability?
What role do third parties play in your privacy compliance efforts? Learn how the two functions overlap and ways to keep data secure across your supply chain.
Katrina Dalao
November 07, 2023 10 min read

On-demand webinars
Third-Party Risk
5 Ways to save time when assessing third parties for privacy and security risks webinar
Join our webinar and learn how to save time and streamline third-party risk assessment throughout the TPRM lifecycle.
October 25, 2023

On-demand webinars
Third-Party Risk
5 Ways to save time when assessing third parties for privacy and security risks webinar
Join our webinar and learn how to save time and streamline third-party risk assessment throughout the TPRM lifecycle.
October 25, 2023

E-Book
Third-Party Risk
Datenschutz und Drittparteien-Risiken: Ein integrierter Ansatz
Erfahren Sie, warum Datenschutz im Drittparteien-Risikomanagement unverzichtbar ist, und lernen Sie 10 Best Practices kennen, mit denen Sie die Datenschutz-Compliance bei der Zusammenarbeit mit Drittanbietern erfolgreich umsetzen.
Oktober 12, 2023

eBook
Third-Party Risk
Data privacy compliance and Third-Party Management: A unified approach
Understand the importance of data privacy in third-party risk management, and 10 best practices for achieving privacy compliance when working with third parties.
October 12, 2023

eBook
Third-Party Risk
Data privacy compliance and Third-Party Management: A unified approach
Understand the importance of data privacy in third-party risk management, and 10 best practices for achieving privacy compliance when working with third parties.
October 12, 2023

Blog
Third-Party Risk
A confiança fala: segurança cibernética do indivíduo à empresa
A equipe de segurança tem um papel importante na construção e na promoção da confiança dentro da organização, mesmo com a existência de silos entre departamentos.
Jason Koestenblatt
outubro 09, 2023 4 min read

Blog
GRC e garantia de segurança
A transformação digital e a evolução da segurança cibernética
Com a evolução constante do cenário tecnológico, as empresas se deparam com o crescimento da regulamentação e das exigências de conformidade, além da proliferação da computação em nuvem.
Scott Solomon
outubro 09, 2023 3 min read

Blog
Third-Party Risk
A confiança fala: segurança cibernética do indivíduo à empresa
A equipe de segurança tem um papel importante na construção e na promoção da confiança dentro da organização, mesmo com a existência de silos entre departamentos.
Jason Koestenblatt
outubro 09, 2023 4 min read

Blog
GRC e garantia de segurança
A transformação digital e a evolução da segurança cibernética
Com a evolução constante do cenário tecnológico, as empresas se deparam com o crescimento da regulamentação e das exigências de conformidade, além da proliferação da computação em nuvem.
Scott Solomon
outubro 09, 2023 3 min read

Blog
Rischio terze parti
Conversazioni sulla fiducia: implementazione della sicurezza informatica basata sulla fiducia dal livello individuale a quello aziendale
Nonostante le divisioni tra i vari reparti, i team addetti alla sicurezza possono contribuire a creare e promuovere la fiducia all'interno delle organizzazioni.
Jason Koestenblatt
ottobre 09, 2023 4 min read

Blog
Rischio terze parti
Conversazioni sulla fiducia: implementazione della sicurezza informatica basata sulla fiducia dal livello individuale a quello aziendale
Nonostante le divisioni tra i vari reparti, i team addetti alla sicurezza possono contribuire a creare e promuovere la fiducia all'interno delle organizzazioni.
Jason Koestenblatt
ottobre 09, 2023 4 min read

Blog
Third-Party Risk
Vertrauensbasierte Cybersicherheit: So stärken Sie Ihr Unternehmen von innen heraus
Sicherheitsteams können dazu beitragen, Vertrauen im Unternehmen zu schaffen und zu festigen – selbst wenn einzelne Abteilungen voneinander abgeschottet arbeiten.
Jason Koestenblatt
Oktober 09, 2023 4 min read

Blog
GRC & Security Assurance
Digitale Transformation und die neue Cybersicherheitslandschaft
Die digitale Transformation bringt nicht nur Chancen, sondern auch neue Herausforderungen mit sich: Mehr Compliance-Vorgaben, komplexere Regularien und die zunehmend wichtigere Rolle der Cloud.
Scott Solomon
Oktober 09, 2023 3 min read

Blog
Third-Party Risk
Vertrauensbasierte Cybersicherheit: So stärken Sie Ihr Unternehmen von innen heraus
Sicherheitsteams können dazu beitragen, Vertrauen im Unternehmen zu schaffen und zu festigen – selbst wenn einzelne Abteilungen voneinander abgeschottet arbeiten.
Jason Koestenblatt
Oktober 09, 2023 4 min read

Blog
GRC & Security Assurance
Digitale Transformation und die neue Cybersicherheitslandschaft
Die digitale Transformation bringt nicht nur Chancen, sondern auch neue Herausforderungen mit sich: Mehr Compliance-Vorgaben, komplexere Regularien und die zunehmend wichtigere Rolle der Cloud.
Scott Solomon
Oktober 09, 2023 3 min read

Blog
Third-Party Risk Management
La confianza es clave: Propulsar la ciberseguridad basada en la confianza de los individuos a toda la empresa
Los equipos de seguridad pueden ayudar a generar y promover la confianza dentro de toda la empresa a pesar de los silos entre departamentos
Jason Koestenblatt
octubre 09, 2023 4 min read

Blog
GRC y garantía de seguridad
La transformación digital y el panorama de ciberseguridad en evolución
A medida que el panorama tecnológico continúa evolucionando, los equipos están experimentando un aumento en las obligaciones de cumplimiento normativo, las regulaciones y la proliferación de tecnologías en la nube.
Scott Solomon
octubre 09, 2023 3 min read

Blog
Third-Party Risk Management
La confianza es clave: Propulsar la ciberseguridad basada en la confianza de los individuos a toda la empresa
Los equipos de seguridad pueden ayudar a generar y promover la confianza dentro de toda la empresa a pesar de los silos entre departamentos
Jason Koestenblatt
octubre 09, 2023 4 min read

Blog
GRC y garantía de seguridad
La transformación digital y el panorama de ciberseguridad en evolución
A medida que el panorama tecnológico continúa evolucionando, los equipos están experimentando un aumento en las obligaciones de cumplimiento normativo, las regulaciones y la proliferación de tecnologías en la nube.
Scott Solomon
octubre 09, 2023 3 min read

Blog
Third-Party Risk
Parlons confiance : mettre en œuvre une cybersécurité basée sur la confiance, de l’individu à l’entreprise
Même dans un environnement fragmenté, les équipes de cybersécurité sont les catalyseurs d’une confiance forte et durable
Jason Koestenblatt
octobre 09, 2023 4 min read

Blog
Third-Party Risk
Parlons confiance : mettre en œuvre une cybersécurité basée sur la confiance, de l’individu à l’entreprise
Même dans un environnement fragmenté, les équipes de cybersécurité sont les catalyseurs d’une confiance forte et durable
Jason Koestenblatt
octobre 09, 2023 4 min read

Blog
Third-Party Risk
Trust talks: Actioning trust-based cybersecurity from individual to enterprise
Security teams can help create and champion organizational trust despite interdepartmental silos
Jason Koestenblatt
October 09, 2023 4 min read

Blog
GRC & Security Assurance
Digital transformation and the evolving cybersecurity landscape
As the technological landscape continues to evolve, teams are seeing increases in compliance obligations, regulations, and the proliferation of cloud technology.
Scott Solomon
October 09, 2023 3 min read

Blog
GRC & Security Assurance
Digital transformation and the evolving cybersecurity landscape
As the technological landscape continues to evolve, teams are seeing increases in compliance obligations, regulations, and the proliferation of cloud technology.
Scott Solomon
October 09, 2023 3 min read

Blog
Third-Party Risk
Trust talks: Actioning trust-based cybersecurity from individual to enterprise
Security teams can help create and champion organizational trust despite interdepartmental silos
Jason Koestenblatt
October 09, 2023 4 min read

Blog
GRC & Security Assurance
Transformation numérique et évolution du contexte de la cybersécurité
Alors que le paysage technologique continue d’évoluer, on constate une augmentation des obligations en termes de conformité et de réglementations ainsi qu’une prolifération des technologies cloud.
Scott Solomon
octobre 09, 2023 3 min read

Blog
GRC & Security Assurance
Transformation numérique et évolution du contexte de la cybersécurité
Alors que le paysage technologique continue d’évoluer, on constate une augmentation des obligations en termes de conformité et de réglementations ainsi qu’une prolifération des technologies cloud.
Scott Solomon
octobre 09, 2023 3 min read

Blog
GRC & Security Assurance
Cybersecurity Awareness Month resource hub
The cybersecurity awareness hub pulls resources from our experts on the Security CoE, GRC, Privacy, DataGuidance, and TPRM teams to a central resource.
Jason Koestenblatt, Team Lead, Content Marketing
October 02, 2023 3 min read

Blog
GRC & Security Assurance
Cybersecurity Awareness Month resource hub
The cybersecurity awareness hub pulls resources from our experts on the Security CoE, GRC, Privacy, DataGuidance, and TPRM teams to a central resource.
Jason Koestenblatt, Team Lead, Content Marketing
October 02, 2023 3 min read

On-demand webinars
Third-Party Risk
Where contracting fits in the third-party risk lifecycle: 5 opportunities for optimization
Join this webinar to learn how to manage the third-party risk lifecycle across teams while optimizing your processes with automation.
September 07, 2023

On-demand webinars
Third-Party Risk
Where contracting fits in the third-party risk lifecycle: 5 opportunities for optimization
Join this webinar to learn how to manage the third-party risk lifecycle across teams while optimizing your processes with automation.
September 07, 2023

On-demand webinars
Third-Party Risk
Staying vigilant: 7 practical tips for ongoing third-party risk monitoring
In this webinar, we'll share seven practical tips for effective third-party risk monitoring, helping you to identify new risks and take timely action to protect your business.
August 01, 2023

On-demand webinars
Third-Party Risk
Staying vigilant: 7 practical tips for ongoing third-party risk monitoring
In this webinar, we'll share seven practical tips for effective third-party risk monitoring, helping you to identify new risks and take timely action to protect your business.
August 01, 2023
Infographic
Third-Party Risk
What are your third parties not telling you?
Learn how to actively screen and monitor your third parties in the OneTrust Third-Party Risk Exchange.
July 24, 2023

Infographic
Third-Party Risk
What are your third parties not telling you?
Learn how to actively screen and monitor your third parties in the OneTrust Third-Party Risk Exchange.
July 24, 2023

On-demand webinars
Third-Party Due Diligence
Driving excellence in third-party risk management: An in-depth look at different due diligence approaches
Join our in-depth webinar and learn how to define third-party due dilligence levels and when to apply them during your vendor management lifecycle.
July 20, 2023

On-demand webinars
Third-Party Due Diligence
Driving excellence in third-party risk management: An in-depth look at different due diligence approaches
Join our in-depth webinar and learn how to define third-party due dilligence levels and when to apply them during your vendor management lifecycle.
July 20, 2023

On-demand webinars
Third-Party Risk
Automating third-party management workflows: 5 ways to drive alignment across teams
Join us as we explore how automating third-party management workflows streamlines processes, drives alignment across teams, and reduces reduntant work.
July 19, 2023

On-demand webinars
Third-Party Risk
Automating third-party management workflows: 5 ways to drive alignment across teams
Join us as we explore how automating third-party management workflows streamlines processes, drives alignment across teams, and reduces reduntant work.
July 19, 2023

Bevorstehende Webinare
Third-Party Risk
Sind Ihre Auslagerungspartner und Drittparteien eine Belastung für Ihre Datenschutz Compliance? 5 Tipps, um Ihr Risiko zu reduzieren
Dieses Webinar erläutert, wie Sie mit einem Third Party Risk Management-Programm datenschutzbezogene Risiken verringern, Compliance Records mit Leichtigkeit führen und die Zusammenarbeit von Geschäftseinheiten fördern können.
Juli 19, 2023

On-Demand-Webinare
Third-Party Risk
Sind Ihre Auslagerungspartner und Drittparteien eine Belastung für Ihre Datenschutz Compliance? 5 Tipps, um Ihr Risiko zu reduzieren
Dieses Webinar erläutert, wie Sie mit einem Third Party Risk Management-Programm datenschutzbezogene Risiken verringern, Compliance Records mit Leichtigkeit führen und die Zusammenarbeit von Geschäftseinheiten fördern können.
Juli 19, 2023

On-demand webinars
Third-Party Due Diligence
A shortcut to third party due diligence fundamentals
In this webinar, we examine the scope of third-party due dilligence, best practices, and industry trends driving greater scrutiny on third parties.
July 13, 2023

On-demand webinars
Third-Party Due Diligence
A shortcut to third party due diligence fundamentals
In this webinar, we examine the scope of third-party due dilligence, best practices, and industry trends driving greater scrutiny on third parties.
July 13, 2023

Blog
Third-Party Risk
Como iniciar um programa de gestão de riscos de terceiros: monitoramento e manutenção do desempenho
Como iniciar um programa de gestão de riscos de terceiros: monitoramento e manutenção do desempenho
Katrina Dalao
julho 11, 2023 5 min read

Blog
Third-Party Risk Management
Cómo iniciar un programa de gestión de riesgos de terceros: Implementa procesos eficaces en toda tu organización
Aprende a implementar un programa de gestión de riesgos de terceros efectivo que satisfaga las necesidades de tu organización.
Katrina Dalao
julio 11, 2023 5 min read

Blog
Third-Party Risk Management
Cómo iniciar un programa de gestión de riesgos de terceros: monitorizar y mantener el rendimiento
Cómo iniciar un programa de gestión de riesgos de terceros: monitorizar y mantener el rendimiento
Katrina Dalao
julio 11, 2023 5 min read

Blog
Third-Party Risk Management
Cómo iniciar un programa de gestión de riesgos de terceros: monitorizar y mantener el rendimiento
Cómo iniciar un programa de gestión de riesgos de terceros: monitorizar y mantener el rendimiento
Katrina Dalao
julio 11, 2023 5 min read

Blog
Third-Party Risk Management
Cómo iniciar un programa de gestión de riesgos de terceros: Implementa procesos eficaces en toda tu organización
Aprende a implementar un programa de gestión de riesgos de terceros efectivo que satisfaga las necesidades de tu organización.
Katrina Dalao
julio 11, 2023 5 min read

Blog
Third-Party Risk
Lancer son programme de gestion des risques tiers : mettre en œuvre des processus efficaces dans l’organisation
Découvrez comment mettre en œuvre un programme efficace de gestion du risque tiers qui répond aux besoins de votre organisation.
Katrina Dalao
juillet 11, 2023 5 min read

Blog
Third-Party Risk
Lancer un programme de gestion des risques tiers : surveiller et maintenir les performances
Lancer un programme de gestion des risques tiers : surveiller et maintenir les performances
Katrina Dalao
juillet 11, 2023 5 min read

Blog
Third-Party Risk
Lancer son programme de gestion des risques tiers : mettre en œuvre des processus efficaces dans l’organisation
Découvrez comment mettre en œuvre un programme efficace de gestion du risque tiers qui répond aux besoins de votre organisation.
Katrina Dalao
juillet 11, 2023 5 min read

Blog
Third-Party Risk
Lancer un programme de gestion des risques tiers : surveiller et maintenir les performances
Lancer un programme de gestion des risques tiers : surveiller et maintenir les performances
Katrina Dalao
juillet 11, 2023 5 min read

Blog
Third-Party Risk
How to start a third-party risk management program: Monitor and maintain performance
How to start a third-party risk management program: Monitor and maintain performance
Katrina Dalao
July 11, 2023 5 min read

Blog
Third-Party Risk
How to start a third-party risk management program: Implement effective processes across your organization
Learn how to implement an effective third-party risk management program that meets your organization's needs.
Katrina Dalao
July 11, 2023 5 min read

Blog
Third-Party Risk
How to start a third-party risk management program: Get leadership buy-in
Create a TPRM program that addresses your organization’s highest security risks and aligns with strategic objectives
Katrina Dalao
July 11, 2023 5 min read

Blog
Third-Party Risk
How to start a third-party risk management program: Get leadership buy-in
Create a TPRM program that addresses your organization’s highest security risks and aligns with strategic objectives
Katrina Dalao
July 11, 2023 5 min read

Blog
Third-Party Risk
How to start a third-party risk management program: Implement effective processes across your organization
Learn how to implement an effective third-party risk management program that meets your organization's needs.
Katrina Dalao
July 11, 2023 5 min read

Blog
Third-Party Risk
How to start a third-party risk management program: Monitor and maintain performance
How to start a third-party risk management program: Monitor and maintain performance
Katrina Dalao
July 11, 2023 5 min read

Blog
Rischio terze parti
Come avviare un programma di gestione del rischio terze parti: monitora e gestisci le prestazioni
Come avviare un programma di gestione del rischio terze parti: monitora e gestisci le prestazioni
Katrina Dalao
luglio 11, 2023 5 min read

Blog
Rischio terze parti
Come avviare un programma di gestione del rischio terze parti: monitora e gestisci le prestazioni
Come avviare un programma di gestione del rischio terze parti: monitora e gestisci le prestazioni
Katrina Dalao
luglio 11, 2023 5 min read

On-demand webinars
Third-Party Risk
Are your third parties a privacy compliance liability? 5 tips to reduce your exposure
Join our webinar and learn how to create an effective, privacy-focused third-party risk management (TPRM) program that streamlines recordkeeping and reduces your risk exposure.
July 05, 2023

On-demand webinars
Third-Party Risk
Are your third parties a privacy compliance liability? 5 tips to reduce your exposure
Join our webinar and learn how to create an effective, privacy-focused third-party risk management (TPRM) program that streamlines recordkeeping and reduces your risk exposure.
July 05, 2023

Blog
Third-Party Risk Management
Cómo iniciar un programa de gestión de riesgos de terceros: tipos de riesgos de terceros
Conoce los diferentes tipos de riesgos de terceros y cómo abordar cada uno.
Katrina Dalao
junio 29, 2023 6 min read

Blog
Third-Party Risk Management
Cómo iniciar un programa de gestión de riesgos de terceros: tipos de riesgos de terceros
Conoce los diferentes tipos de riesgos de terceros y cómo abordar cada uno.
Katrina Dalao
junio 29, 2023 6 min read

Blog
Third-Party Risk
How to start a third-party risk management program: Understand the types of third-party risks
Learn about the different types of third-party risks and how to address each one
Katrina Dalao
June 29, 2023 6 min read

Blog
Third-Party Risk
How to start a third-party risk management program: Understand the types of third-party risks
Learn about the different types of third-party risks and how to address each one
Katrina Dalao
June 29, 2023 6 min read

Video
GRC & Security Assurance
Third-party risk exchange demo
The OneTrust Vendor Risk Management provides businesses access to pre-completed vendor risk assessments while supporting industry standards.
June 22, 2023

Video
GRC & Security Assurance
Third-party risk exchange demo
The OneTrust Vendor Risk Management provides businesses access to pre-completed vendor risk assessments while supporting industry standards.
June 22, 2023

On-demand webinars
Third-Party Risk
Third-party data breach incident response: Essential workflows for effective recovery
Join OneTrust and HackNotice as we discuss effective ways to protect your organization from third-party data breaches and build strong incident response workflows.
June 13, 2023

On-demand webinars
Third-Party Risk
Third-party data breach incident response: Essential workflows for effective recovery
Join OneTrust and HackNotice as we discuss effective ways to protect your organization from third-party data breaches and build strong incident response workflows.
June 13, 2023

On-demand webinars
Third-Party Risk
Bridging the gap: How procurement and InfoSec can work together to reduce third-party risks
Join our upcoming webinar as we explore the pivotal ways procurement and InfoSec teams can collaborate to reduce third-party risks.
June 08, 2023

On-demand webinars
Third-Party Risk
Bridging the gap: How procurement and InfoSec can work together to reduce third-party risks
Join our upcoming webinar as we explore the pivotal ways procurement and InfoSec teams can collaborate to reduce third-party risks.
June 08, 2023

Seminarios web bajo demanda
Third-Party Risk Management
Secretos del éxito en la gestión de terceros: controlar la diligencia debida y la gestión de riesgos
Dominar el arte de la diligencia debida y la gestión de riesgos y cómo armonizarlos para maximizar su eficacia.
junio 08, 2023
eBook
Third-Party Risk
InfoSec's guide to third-party risk management: Key considerations and best practices
Download our eBook to learn practical advice on how to approach third-party risk management like an InfoSec expert.
June 05, 2023

eBook
Third-Party Risk
InfoSec's guide to third-party risk management: Key considerations and best practices
Download our eBook to learn practical advice on how to approach third-party risk management like an InfoSec expert.
June 05, 2023

Blog
Third-Party Risk
HackNotice and OneTrust partner for deeper third-party threat intelligence
OneTrust customers can take advantage of HackNotice’s near real-time breach alerts.
June 01, 2023 3 min read

Blog
Privacy Management
Assessing your international data transfers post-DPC ruling
The recent decision cast fresh doubt over the effectiveness of transfer safeguards and supplementary measures in conjunction with the practical application of third-country surveillance laws.
Linda Thielova
June 01, 2023 8 min read

Blog
Privacy Management
Assessing your international data transfers post-DPC ruling
The recent decision cast fresh doubt over the effectiveness of transfer safeguards and supplementary measures in conjunction with the practical application of third-country surveillance laws.
Linda Thielova
June 01, 2023 8 min read

Blog
Third-Party Risk
HackNotice and OneTrust partner for deeper third-party threat intelligence
OneTrust customers can take advantage of HackNotice’s near real-time breach alerts.
June 01, 2023 3 min read

Blog
Inteligencia para la confianza
OneTrust presenta innovaciones para habilitar el uso responsable de los datos y el trust intelligence a gran escala
OneTrust anuncia nuevas innovaciones dentro de su plataforma de Trust Intelligence para ayudar a las empresas a utilizar los datos de forma responsable y desarrollar inteligencia de confianza a escala.
mayo 23, 2023 5 min read

On-demand webinars
Third-Party Risk
Save time, save money: A practical guide to automating third-party risk management
In this webinar, you will learn how to reduce the use of spreadsheets for third-party risk management and cut costs when building your TPRM program.
May 03, 2023

On-demand webinars
Third-Party Risk
Save time, save money: A practical guide to automating third-party risk management
In this webinar, you will learn how to reduce the use of spreadsheets for third-party risk management and cut costs when building your TPRM program.
May 03, 2023

On-demand webinars
Third-Party Risk
Third-Party management secrets: Aligning risk management and due diligence
Watch this webinar to learn how to align your TPRM and TPDD programs to achieve workflow efficiencies and the distinction between the two discipline areas.
April 20, 2023

On-demand webinars
Third-Party Risk
Third-Party management secrets: Aligning risk management and due diligence
Watch this webinar to learn how to align your TPRM and TPDD programs to achieve workflow efficiencies and the distinction between the two discipline areas.
April 20, 2023

Blog
Third-Party Risk Management
¿Por qué elegir OneTrust para la gestión de terceros?
abril 13, 2023 6 min read

In-Person Event
Third-Party Risk
Risk on the Road: Navigating data management, compliance automation and third-party risk
Join this OneTrust live event series, which will address critical topics such as navigating data management, compliance automation and third-party risk.
April 11, 2023

In-Person Event
Third-Party Risk
Risk on the Road: Navigating data management, compliance automation and third-party risk
Join this OneTrust live event series, which will address critical topics such as navigating data management, compliance automation and third-party risk.
April 11, 2023
Infographic
Third-Party Risk
Third-party risk: A growing spiderweb
The number of businesses and third-party suppliers has increased, widening the risk landscape. This infographic shows how businesses are managing that risk.
April 03, 2023

Infographic
Third-Party Risk
Third-party risk: A growing spiderweb
The number of businesses and third-party suppliers has increased, widening the risk landscape. This infographic shows how businesses are managing that risk.
April 03, 2023

On-demand webinars
Privacy Management
The US privacy landscape for third-party risk: a program prototype time
Learn how to balance the intricacies of CPRA, VCDPA, CPA, CTDPA, and UCPA when managing third parties and understanding privacy-related risks.
March 28, 2023

On-demand webinars
Privacy Management
The US privacy landscape for third-party risk: a program prototype time
Learn how to balance the intricacies of CPRA, VCDPA, CPA, CTDPA, and UCPA when managing third parties and understanding privacy-related risks.
March 28, 2023

Blog
Third-Party Risk Management
Por qué los equipos de privacidad de datos y riesgos de terceros tienen que colaborar
Compartir información y recursos entre los silos dentro de la organización es mutuamente beneficioso para los equipos con el objetivo común de mitigar el riesgo de privacidad de los datos.
Scott Solomon
marzo 07, 2023 6 min read

Blog
Third-Party Risk Management
Por qué los equipos de privacidad de datos y riesgos de terceros tienen que colaborar
Compartir información y recursos entre los silos dentro de la organización es mutuamente beneficioso para los equipos con el objetivo común de mitigar el riesgo de privacidad de los datos.
Scott Solomon
marzo 07, 2023 6 min read

Blog
Third-Party Risk
Supply Wisdom risk intelligence is now available in OneTrust’s Third-Party Risk Exchange
The partnership with Supply Wisdom brings compliance, financial, location-based ESG, and cyber risk data to Exchange customers and their third parties.
Chet Devchand, Director, Business Development Management
February 14, 2023 3 min read

Blog
Third-Party Risk
Supply Wisdom risk intelligence is now available in OneTrust’s Third-Party Risk Exchange
The partnership with Supply Wisdom brings compliance, financial, location-based ESG, and cyber risk data to Exchange customers and their third parties.
Chet Devchand, Director, Business Development Management
February 14, 2023 3 min read

On-demand webinars
Third-Party Risk
Efficient third-party risk management: 10 Best practices for streamlining workflows
Attend this webinar to learn about Third-Party Risk Management (TPRM) workflow definition and maintenance best practices you can apply to your business.NEED
February 13, 2023

On-demand webinars
Third-Party Risk
Efficient third-party risk management: 10 Best practices for streamlining workflows
Attend this webinar to learn about Third-Party Risk Management (TPRM) workflow definition and maintenance best practices you can apply to your business.NEED
February 13, 2023

On-demand webinars
Third-Party Risk
Third-Party Management roundtable: 3 strategies for aligning Security, Privacy, Ethics, and ESG teams
In this webinar, you will learn how to utilize TPRM to help to optimize workflows, leverage data, and increase accountability across sourcing and procurement.
February 01, 2023

On-demand webinars
Third-Party Risk
Third-Party Management roundtable: 3 strategies for aligning Security, Privacy, Ethics, and ESG teams
In this webinar, you will learn how to utilize TPRM to help to optimize workflows, leverage data, and increase accountability across sourcing and procurement.
February 01, 2023

On-Demand-Webinare
Third-Party Risk
Trends im IT-Risikomanagement – Behandeln Sie schon oder bewerten Sie noch?
Dieses Webinar thematisiert einen strukturierten und effektiven Umgang mit IT-/IS- Risikomanagement.
Januar 18, 2023

On-Demand-Webinare
Third-Party Risk
Trends im IT-Risikomanagement – Behandeln Sie schon oder bewerten Sie noch?
Dieses Webinar thematisiert einen strukturierten und effektiven Umgang mit IT-/IS- Risikomanagement.
Januar 18, 2023

Blog
Third-Party Risk
Build trust, promote your program in the Third-Party Risk Exchange
The Third-Party Risk Exchange allows businesses to learn more about each other's security posture, offer SIG Lite assessments on-demand, and more.
Pranav Menem
January 10, 2023 3 min read

Blog
Third-Party Risk
Build trust, promote your program in the Third-Party Risk Exchange
The Third-Party Risk Exchange allows businesses to learn more about each other's security posture, offer SIG Lite assessments on-demand, and more.
Pranav Menem
January 10, 2023 3 min read

Blog
Third-Party Risk
As third-party needs sprawl, so do risk management investments
From a new focus on ESG to a renewed need for cybersecurity, third-party and vendor risk management solutions have become a priority for organizations.
Jason Koestenblatt
January 04, 2023 3 min read

On-demand webinars
Third-Party Risk
Third-party risk management demo
Our third-party risk software helps you build a vendor inventory, conduct vendor assessments, mitigate risks, monitor vendors over time, and more.
January 04, 2023

On-demand webinars
Third-Party Risk
Third-party risk management demo
Our third-party risk software helps you build a vendor inventory, conduct vendor assessments, mitigate risks, monitor vendors over time, and more.
January 04, 2023

Blog
Third-Party Risk
As third-party needs sprawl, so do risk management investments
From a new focus on ESG to a renewed need for cybersecurity, third-party and vendor risk management solutions have become a priority for organizations.
Jason Koestenblatt
January 04, 2023 3 min read

Seminarios web bajo demanda
Third-Party Risk Management
Academia RGPD: Los riesgos de terceros
En la tercera sesión de la Academia RGPD hablaremos sobre los riesgos de proveedores (y empleados), crítico en los programas de privacidad.
diciembre 22, 2022

Seminarios web bajo demanda
Third-Party Risk Management
Academia RGPD: Los riesgos de terceros
En la tercera sesión de la Academia RGPD hablaremos sobre los riesgos de proveedores (y empleados), crítico en los programas de privacidad.
diciembre 22, 2022

Blog
Diligencia debida de terceros
Prácticas recomendadas para efectuar la diligencia debida de terceros en cuanto a ética y cumplimiento normativo
Todo programa de cumplimiento normativo bien diseñado debe aplicar la diligencia debida basada en riesgos y disponer de un proceso para todo el ciclo de vida de gestión de riesgos de terceros.
Kelly Maxwell
diciembre 08, 2022 9 min read

Blog
Diligencia debida de terceros
Prácticas recomendadas para efectuar la diligencia debida de terceros en cuanto a ética y cumplimiento normativo
Todo programa de cumplimiento normativo bien diseñado debe aplicar la diligencia debida basada en riesgos y disponer de un proceso para todo el ciclo de vida de gestión de riesgos de terceros.
Kelly Maxwell
diciembre 08, 2022 9 min read

Blog
Third-Party Due Diligence
Best practices for conducting third-party due diligence for ethics and compliance
A well-designed compliance program should apply risk-based due diligence and have a process for the full lifecycle of third-party risk management
Kelly Maxwell
December 08, 2022 9 min read

Blog
Third-Party Due Diligence
Best practices for conducting third-party due diligence for ethics and compliance
A well-designed compliance program should apply risk-based due diligence and have a process for the full lifecycle of third-party risk management
Kelly Maxwell
December 08, 2022 9 min read

On-demand webinars
Third-Party Risk
OneTrust third-party risk management for privacy professionals
Watch the demo video to learn how OneTrust Third-Party Risk Management can help your TPRM program meet your privacy team's expectations.
December 07, 2022

On-demand webinars
Third-Party Risk
OneTrust third-party risk management for privacy professionals
Watch the demo video to learn how OneTrust Third-Party Risk Management can help your TPRM program meet your privacy team's expectations.
December 07, 2022

On-demand webinars
Third-Party Risk
How do you manage your third-party cyber risks? 5 best practices to improve your cyber resilience webinar
In this session, we’ll outline how to identify, reduce, and monitor cyber risk as it relates to your third parties including methods for tracking cyber risks over time.
December 06, 2022

On-demand webinars
Third-Party Risk
How do you manage your third-party cyber risks? 5 best practices to improve your cyber resilience webinar
In this session, we’ll outline how to identify, reduce, and monitor cyber risk as it relates to your third parties including methods for tracking cyber risks over time.
December 06, 2022

Blog
Third-Party Risk
Ironclad, OneTrust partner to streamline and secure third-party procurement processes
To help organizations take a holistic approach to the third-party contracting and risk management process, OneTrust has partnered with Ironclad.
Chet Devchand
November 30, 2022 4 min read

On-demand webinars
Third-Party Risk
Canada and ISO 27001:2022: How automation streamlines compliance
Join OneTrust for a demo on how our privacy management platform helps Canadian businesses streamline ISO 27001:2022 compliance.
November 30, 2022

On-demand webinars
Third-Party Risk
Canada and ISO 27001:2022: How automation streamlines compliance
Join OneTrust for a demo on how our privacy management platform helps Canadian businesses streamline ISO 27001:2022 compliance.
November 30, 2022

Blog
Third-Party Risk
Ironclad, OneTrust partner to streamline and secure third-party procurement processes
To help organizations take a holistic approach to the third-party contracting and risk management process, OneTrust has partnered with Ironclad.
Chet Devchand
November 30, 2022 4 min read

Blog
Third-Party Risk
What every Chief Privacy Officer should know about third-party risk management
CPOs track risk via data mapping, in which data is discovered, assessed, and tracked as it flows throughout the organization, including to third parties.
Jason Koestenblatt, Team Lead, Content Marketing
November 18, 2022 6 min read

Blog
Third-Party Risk
What every Chief Privacy Officer should know about third-party risk management
CPOs track risk via data mapping, in which data is discovered, assessed, and tracked as it flows throughout the organization, including to third parties.
Jason Koestenblatt, Team Lead, Content Marketing
November 18, 2022 6 min read

On-demand webinars
GRC & Security Assurance
Analyzing ISO 27001:2022 reinforcing privacy and security compliance with automation webinar
Learn how InfoSec teams can automate scoping mandatory requirements and streamline generating evidence to prove compliance across ISO.
November 17, 2022

On-demand webinars
GRC & Security Assurance
Analyzing ISO 27001:2022 reinforcing privacy and security compliance with automation webinar
Learn how InfoSec teams can automate scoping mandatory requirements and streamline generating evidence to prove compliance across ISO.
November 17, 2022

On-demand webinars
Third-Party Risk
Do You Know Your third-party cyber risks? How to take a data-driven approach to reduce risk
In this webinar session, we’ll outline how to take a data-driven approach to understand, reduce, and monitor cyber risks as it relates to your third parties.
November 15, 2022

On-demand webinars
Third-Party Risk
Do You Know Your third-party cyber risks? How to take a data-driven approach to reduce risk
In this webinar session, we’ll outline how to take a data-driven approach to understand, reduce, and monitor cyber risks as it relates to your third parties.
November 15, 2022

Blog
Third-Party Risk
Thousands of RiskRecon grades now available in the OneTrust Third-Party Risk Exchange
We are partnering with RiskRecon, a Mastercard Company to make cybersecurity ratings available out-of-the-box to all Third-Party Risk Exchange customers.
Chet Devchand
November 01, 2022 3 min read

Blog
Third-Party Risk
Thousands of RiskRecon grades now available in the OneTrust Third-Party Risk Exchange
We are partnering with RiskRecon, a Mastercard Company to make cybersecurity ratings available out-of-the-box to all Third-Party Risk Exchange customers.
Chet Devchand
November 01, 2022 3 min read

On-demand webinars
Third-Party Risk
TPRM program blueprint: Your 5 step guide to third-party risk management success
This webinar focuses on the fundamental considerations when managing third parties and enables your organization to build a solid and scalable foundation.
October 31, 2022

On-demand webinars
Third-Party Risk
TPRM program blueprint: Your 5 step guide to third-party risk management success
This webinar focuses on the fundamental considerations when managing third parties and enables your organization to build a solid and scalable foundation.
October 31, 2022

Blog
Third-Party Risk
Put a hold on hacks: Fight the phish and other emerging cyber threats
In 2021, there was a 62% global attack spike in ransomware (158% increase in North America), and an increased focus on attacks by regulatory bodies.
Jason Koestenblatt, Team Lead, Content Marketing
October 21, 2022 6 min read

Blog
Third-Party Risk
Put a hold on hacks: Fight the phish and other emerging cyber threats
In 2021, there was a 62% global attack spike in ransomware (158% increase in North America), and an increased focus on attacks by regulatory bodies.
Jason Koestenblatt, Team Lead, Content Marketing
October 21, 2022 6 min read

On-demand webinars
Third-Party Risk
How OneTrust can help scale your Third-Party Risk program
In this webinar, we provide a live product demonstration to show you how your organization can optimize and scale a third-party risk program.
October 18, 2022

On-demand webinars
Third-Party Risk
How OneTrust can help scale your Third-Party Risk program
In this webinar, we provide a live product demonstration to show you how your organization can optimize and scale a third-party risk program.
October 18, 2022

Blog
Third-Party Risk Management
¿Por qué elegir OneTrust para la gestión de terceros?
OneTrust simplifica la gestión de terceros al permitir el control y la visibilidad a lo largo de todo el ciclo de vida de los terceros mientras tú los administras.
Scott Solomon, Senior Manager, Product Marketing
septiembre 23, 2022 5 min read

Blog
Third-Party Risk Management
¿Por qué elegir OneTrust para la gestión de terceros?
OneTrust simplifica la gestión de terceros al permitir el control y la visibilidad a lo largo de todo el ciclo de vida de los terceros mientras tú los administras.
Scott Solomon, Senior Manager, Product Marketing
septiembre 23, 2022 5 min read

Blog
Third-Party Risk
Why choose OneTrust for third-party management?
OneTrust simplifies third-party management by enabling control and visibility throughout the entire third-party lifecycle while you manage third parties.
Scott Solomon, Senior Manager, Product Marketing
September 23, 2022 5 min read

Blog
Third-Party Risk
Why choose OneTrust for third-party management?
OneTrust simplifies third-party management by enabling control and visibility throughout the entire third-party lifecycle while you manage third parties.
Scott Solomon, Senior Manager, Product Marketing
September 23, 2022 5 min read

Blog
Third-Party Risk
Pourquoi choisir OneTrust pour gérer ses tiers ?
OneTrust simplifie la gestion des tiers en permettant de contrôler et d’avoir une visibilité sur l’ensemble du cycle de vie de la relation avec les tiers.
Scott Solomon, Senior Manager, Product Marketing
septembre 23, 2022 5 min read

Blog
Third-Party Risk
Pourquoi choisir OneTrust pour gérer ses tiers ?
OneTrust simplifie la gestion des tiers en permettant de contrôler et d’avoir une visibilité sur l’ensemble du cycle de vie de la relation avec les tiers.
Scott Solomon, Senior Manager, Product Marketing
septembre 23, 2022 5 min read

On-demand webinars
Third-Party Risk
Do you know your riskiest third parties? 7 warning signs you shouldn’t ignore
Learn the top 7 red flags for risky third parties, mitigation tactics for reducing third-party risk, and key ways to streamline risk identification, and more.
September 22, 2022

On-demand webinars
Third-Party Risk
Do you know your riskiest third parties? 7 warning signs you shouldn’t ignore
Learn the top 7 red flags for risky third parties, mitigation tactics for reducing third-party risk, and key ways to streamline risk identification, and more.
September 22, 2022
eBook
Technology Risk & Compliance
The art of the enterprise IT risk assessment
Ensure your enterprise IT risk assessment is a success with a top-down approach that gets executive buy-in from the start
September 16, 2022

eBook
Technology Risk & Compliance
The art of the enterprise IT risk assessment
Ensure your enterprise IT risk assessment is a success with a top-down approach that gets executive buy-in from the start
September 16, 2022

On-demand webinars
GRC & Security Assurance
Supply Chain Due Diligence Best Practices: A Practical Implementation Guide to LkSG Webinar
Watch our LkSG webinar to understand the scope of LkSG, how your company will need to adjust, and the repercussions of noncompliance.
September 07, 2022

On-demand webinars
GRC & Security Assurance
Supply Chain Due Diligence Best Practices: A Practical Implementation Guide to LkSG Webinar
Watch our LkSG webinar to understand the scope of LkSG, how your company will need to adjust, and the repercussions of noncompliance.
September 07, 2022

Blog
Third-Party Risk
Reduce unnecessary risk with third-party risk management controls
As more tasks are outsourced to third-party providers, risk management programs become critical to securing sensitive data
September 03, 2022 4 min read

Blog
Third-Party Risk
Reduce unnecessary risk with third-party risk management controls
As more tasks are outsourced to third-party providers, risk management programs become critical to securing sensitive data
September 03, 2022 4 min read

On-demand webinars
Third-Party Risk
Security & privacy C-Level panel: Best practices for building your TPRM program
In this webinar, we discuss best practices for how privacy and security teams can work better to eliminate redundant work, save time, and be more efficient.
August 30, 2022

On-demand webinars
Third-Party Risk
Security & privacy C-Level panel: Best practices for building your TPRM program
In this webinar, we discuss best practices for how privacy and security teams can work better to eliminate redundant work, save time, and be more efficient.
August 30, 2022

On-demand webinars
Third-Party Risk
10 best practices for streamlining your third-party risk management workflows
Watch this webinar to hear how to leverage third-party risk management workflow creation and maintenance best practices.
August 30, 2022

On-demand webinars
Third-Party Risk
10 best practices for streamlining your third-party risk management workflows
Watch this webinar to hear how to leverage third-party risk management workflow creation and maintenance best practices.
August 30, 2022

On-demand webinars
Third-Party Risk
Cybersecurity panel: How well do you know the threats posed by your third parties?
In this panel discussion, we address critical points such as defining the metrics to track in relation to third parties and their cybersecurity risks.
August 28, 2022

On-demand webinars
Third-Party Risk
Cybersecurity panel: How well do you know the threats posed by your third parties?
In this panel discussion, we address critical points such as defining the metrics to track in relation to third parties and their cybersecurity risks.
August 28, 2022

On-demand webinars
Third-Party Risk
Third-Party risk and the U.S. privacy landscape: the top 5 things you need to know
In this webinar, we’ll review services providers under the ADPPA and outline how you can ready your third-party risk program to align with privacy regulations.
July 31, 2022

On-demand webinars
Third-Party Risk
Third-Party risk and the U.S. privacy landscape: the top 5 things you need to know
In this webinar, we’ll review services providers under the ADPPA and outline how you can ready your third-party risk program to align with privacy regulations.
July 31, 2022

Checklist
Third-Party Risk
LkSG readiness checklist: Is your company prepared for the German supply chain due diligence act?
Download our LkSG readiness checklist to understand your readiness for risk management systems and responsibilities, and due diligence obligations.
July 26, 2022

Checklist
Third-Party Risk
LkSG readiness checklist: Is your company prepared for the German supply chain due diligence act?
Download our LkSG readiness checklist to understand your readiness for risk management systems and responsibilities, and due diligence obligations.
July 26, 2022

On-demand webinars
Third-Party Risk
Better by tomorrow: 7 third-party risk assessment best practices you can implement today
In this webinar, we’ll explore these questions and layout 7 must-know best practices to conduct more meaningful third-party risk assessments.
July 15, 2022

On-demand webinars
Third-Party Risk
Better by tomorrow: 7 third-party risk assessment best practices you can implement today
In this webinar, we’ll explore these questions and layout 7 must-know best practices to conduct more meaningful third-party risk assessments.
July 15, 2022

Blog
Diligencia debida de terceros
Cómo gestionar y medir los riesgos de terceros
Para convertirte en un negocio que se base en la confianza, proteger la reputación de tu marca y garantizar el cumplimiento normativo, tendrás que examinar y monitorizar tus relaciones con terceros.
Kelly Maxwell
julio 11, 2022 6 min read

Blog
Diligencia debida de terceros
Cómo gestionar y medir los riesgos de terceros
Para convertirte en un negocio que se base en la confianza, proteger la reputación de tu marca y garantizar el cumplimiento normativo, tendrás que examinar y monitorizar tus relaciones con terceros.
Kelly Maxwell
julio 11, 2022 6 min read

Blog
Devoir de vigilance sur les tiers
Comment gérer et mesurer le risque tiers
Pour devenir une entreprise digne de confiance, protéger la réputation de votre marque et garantir votre conformité, vous devrez vérifier et surveiller vos relations avec vos tiers.
Kelly Maxwell
juillet 11, 2022 6 min read

Blog
Third-Party Due Diligence
How to manage and measure third-party risk
To become a trust-based business, protect your brand's reputation, and ensure compliance, you'll need to vet and monitor your third-party relationships.
Kelly Maxwell
July 10, 2022 6 min read

Blog
Third-Party Due Diligence
How to manage and measure third-party risk
To become a trust-based business, protect your brand's reputation, and ensure compliance, you'll need to vet and monitor your third-party relationships.
Kelly Maxwell
July 10, 2022 6 min read

eBook
Third-Party Risk
Building your third-party risk management program
Understand what it takes to build a successful third-party risk management program through OneTrust's third-party risk management guide.
July 08, 2022

eBook
Third-Party Risk
Building your third-party risk management program
Understand what it takes to build a successful third-party risk management program through OneTrust's third-party risk management guide.
July 08, 2022

On-demand webinars
Third-Party Risk
How to comply: German supply chain Due Diligence act and Forthcoming EU rules
Join our panel of experts as we discuss the German Supply Chain Due Dilligence Act and the best practices for compliance.
June 15, 2022

On-demand webinars
Third-Party Risk
How to comply: German supply chain Due Diligence act and Forthcoming EU rules
Join our panel of experts as we discuss the German Supply Chain Due Dilligence Act and the best practices for compliance.
June 15, 2022

Blog
Third-Party Risk
10 steps to improving your security questionnaire responses
The information gathered from security questionnaires is critical in the evaluation of business and security practices, and is crucial for compliance.
Daniela Villarreal
June 12, 2022 7 min read

Blog
Third-Party Risk
10 steps to improving your security questionnaire responses
The information gathered from security questionnaires is critical in the evaluation of business and security practices, and is crucial for compliance.
Daniela Villarreal
June 12, 2022 7 min read

On-demand webinars
Third-Party Risk
Third-Party risk best practices: How to align privacy & security teams for greater productivity
This webinar will discuss best practices for how privacy and security teams can work together to eliminate redundant work, save time, and be more efficient.
June 06, 2022

On-demand webinars
Third-Party Risk
Third-Party risk best practices: How to align privacy & security teams for greater productivity
This webinar will discuss best practices for how privacy and security teams can work together to eliminate redundant work, save time, and be more efficient.
June 06, 2022

On-demand webinars
GRC & Security Assurance
Elevating your third party risk program with an integrated infosec platform
Join this webinar to learn how you can integrate your Third-Party Risk Management program within a broader IT Security platform
May 26, 2022

On-demand webinars
GRC & Security Assurance
Elevating your third party risk program with an integrated infosec platform
Join this webinar to learn how you can integrate your Third-Party Risk Management program within a broader IT Security platform
May 26, 2022

Blog
Third-Party Risk
OneTrust Third-Party Risk Exchange now provides SecurityScorecard Cybersecurity Rating
OneTrust is expanding its partnership with SecurityScorecard to enable Third-Party Risk Exchange customers to view complementary Cybersecurity Ratings.
Scott Solomon
May 17, 2022 4 min read

Blog
Third-Party Risk
OneTrust Third-Party Risk Exchange now provides SecurityScorecard Cybersecurity Rating
OneTrust is expanding its partnership with SecurityScorecard to enable Third-Party Risk Exchange customers to view complementary Cybersecurity Ratings.
Scott Solomon
May 17, 2022 4 min read
Infographic
Third-Party Risk
Integrating IT, security & third-party risk
Download this infographic and learn how a central platform can integrate IT, security, and risk-management and streamline collaboration across your business.
April 27, 2022

On-demand webinars
Third-Party Risk
Accelerating automation: How the pandemic forced third-party management to scale
Watch this webinar and see how the COVID-19 pandemic forced companies to accelerate automation and scale their third-party management.
April 26, 2022

On-demand webinars
Third-Party Risk
Accelerating automation: How the pandemic forced third-party management to scale
Watch this webinar and see how the COVID-19 pandemic forced companies to accelerate automation and scale their third-party management.
April 26, 2022

On-demand webinars
Third-Party Risk
Secrets to Success: The winning game plan for security questionnaire response
Discover effective strategies for preparing security questionaire responses with our free webinar.
April 04, 2022

On-demand webinars
Third-Party Risk
Secrets to Success: The winning game plan for security questionnaire response
Discover effective strategies for preparing security questionaire responses with our free webinar.
April 04, 2022

Blog
Third-Party Risk
Java framework ‘Spring4Shell’ vulnerability leads to potential exploit
A zero-day Java vulnerability, "Spring4Shell" surfaced and experts believe it could be as impactful as 2021's Log4j. Read to learn more.
Justin Henkel, Head of CISO Center of Excellence
April 04, 2022 3 min read

Blog
Third-Party Risk
Java framework ‘Spring4Shell’ vulnerability leads to potential exploit
A zero-day Java vulnerability, "Spring4Shell" surfaced and experts believe it could be as impactful as 2021's Log4j. Read to learn more.
Justin Henkel, Head of CISO Center of Excellence
April 04, 2022 3 min read
eBook
Third-Party Risk
The shift to third-party management
Download our guide on third-party management and learn what you need to know to shift your buisness to TPM.
March 29, 2022

eBook
Third-Party Risk
The shift to third-party management
Download our guide on third-party management and learn what you need to know to shift your buisness to TPM.
March 29, 2022
Report
Third-Party Risk
OneTrust becomes only IT VRM vendor to receive the Gartner Peer Insights™ Customers’ Choice distinction for three years in a row
Download the 2022 Gartner Peer Insights Customers' Choice for IT VRM Tools to see why customers choose OneTrust Vendorpedia.
March 08, 2022

Blog
Third-Party Risk
OneTrust becomes only IT VRM vendor to receive the Gartner Peer Insights™ Customers’ Choice Distinction for three years in a row
OneTrust has been named a Customers' Choice in the 2022 Gartner Peer Insights ‘Voice of the Customer': IT Vendor Risk Management Tools.
March 08, 2022 6 min read

Blog
Third-Party Risk
OneTrust becomes only IT VRM vendor to receive the Gartner Peer Insights™ Customers’ Choice Distinction for three years in a row
OneTrust has been named a Customers' Choice in the 2022 Gartner Peer Insights ‘Voice of the Customer': IT Vendor Risk Management Tools.
March 08, 2022 6 min read

Blog
Third-Party Risk
Answer any security questionnaire with enhanced cell detection for Questionnaire Response Automation
Introducing QRA cell detection – a powerful QRA enhancement that eases the spreadsheet-based questionnaire response process for vendors.
March 02, 2022 2 min read

Blog
Third-Party Risk
Answer any security questionnaire with enhanced cell detection for Questionnaire Response Automation
Introducing QRA cell detection – a powerful QRA enhancement that eases the spreadsheet-based questionnaire response process for vendors.
March 02, 2022 2 min read

Blog
Third-Party Risk
Mastering the TPRM lifecycle
Third-party risk management is key to any business. Learn how to master the TPRM lifecycle across your organization in our newest video blog!
February 14, 2022 2 min read

Blog
Third-Party Risk
Mastering the TPRM lifecycle
Third-party risk management is key to any business. Learn how to master the TPRM lifecycle across your organization in our newest video blog!
February 14, 2022 2 min read

Blog
Third-Party Risk
Buy-In Guide: Making the case for TPRM software
Make the business case for TPRM in your organization and get access to our TPRM buy-in guide to learn how! Read the blog to learn more.
February 04, 2022 4 min read

Blog
Third-Party Risk
Buy-In Guide: Making the case for TPRM software
Make the business case for TPRM in your organization and get access to our TPRM buy-in guide to learn how! Read the blog to learn more.
February 04, 2022 4 min read
eBook
Third-Party Risk
The business value of third-party risk management software
In this eBook, learn the business value of TPRM software and why all leading organizations rely on it when working with third-party vendors.
February 03, 2022

eBook
Third-Party Risk
The business value of third-party risk management software
In this eBook, learn the business value of TPRM software and why all leading organizations rely on it when working with third-party vendors.
February 03, 2022

On-demand webinars
Third-Party Risk
5 Ways to step-up your business resilience with better third-party management
Join this webinar to learn best practices on how your organization can step-up business resilience with better third-party risk management.
February 02, 2022

On-demand webinars
Third-Party Risk
Optimizing third-party risk: enhance automation with an integrated IT risk platform
Watch our free webinar to discover how to optimize your third-party risk program and reduce manual data management with automation.
February 02, 2022

On-demand webinars
Third-Party Risk
Optimizing third-party risk: enhance automation with an integrated IT risk platform
Watch our free webinar to discover how to optimize your third-party risk program and reduce manual data management with automation.
February 02, 2022

On-demand webinars
Third-Party Risk
5 Ways to step-up your business resilience with better third-party management
Join this webinar to learn best practices on how your organization can step-up business resilience with better third-party risk management.
February 02, 2022

Blog
Third-Party Risk Management
El cambio a la gestión de terceros: ¿Qué es la gestión de terceros y por qué es importante?
La gestión de la confianza de terceros es el siguiente paso evolutivo del riesgo de terceros y se trata de una estrategia clave de confianza de la empresa. ¡Consulta más información en nuestro blog!
enero 25, 2022 9 min read

Blog
Third-Party Risk Management
El cambio a la gestión de terceros: ¿Qué es la gestión de terceros y por qué es importante?
La gestión de la confianza de terceros es el siguiente paso evolutivo del riesgo de terceros y se trata de una estrategia clave de confianza de la empresa. ¡Consulta más información en nuestro blog!
enero 25, 2022 9 min read

Blog
Third-Party Risk
The shift to third-party management (TPM): What is TPM and why does it matter?
Third-Party Trust Management (TPTM) is the next evolution of third-party risk and is key enterprise trust strategy. Learn more in our blog!
January 25, 2022 9 min read

Blog
Third-Party Risk
The shift to third-party management (TPM): What is TPM and why does it matter?
Third-Party Trust Management (TPTM) is the next evolution of third-party risk and is key enterprise trust strategy. Learn more in our blog!
January 25, 2022 9 min read

Upcoming webinars
Privacy Management
2022 Third-party trust predictions and preparations
Prepare for 2022 Trends in Third-Party Risk Management and future-proof your Third-Party Trust program.
January 04, 2022

Upcoming webinars
Privacy Management
2022 Third-party trust predictions and preparations
Prepare for 2022 Trends in Third-Party Risk Management and future-proof your Third-Party Trust program.
January 04, 2022

On-demand webinars
Third-Party Risk
Are your third parties a privacy compliance liability? 5 Tips to reduce your exposure
This webinar will discuss how to create a Third-Party Risk Management (TPRM) program that prioritizes privacy compliance and simplifies record-keeping.
December 31, 2021

On-demand webinars
Third-Party Risk
Are your third parties a privacy compliance liability? 5 Tips to reduce your exposure
This webinar will discuss how to create a Third-Party Risk Management (TPRM) program that prioritizes privacy compliance and simplifies record-keeping.
December 31, 2021

Blog
Third-Party Risk
The future of TPRM: Third party risk management predictions for 2022
In 2021, TPRM and cybersecurity remained at the forefront of business strategy, so what's next? Learn about 2022 TPRM predictions in our blog!
December 19, 2021 5 min read

Blog
Third-Party Risk
The future of TPRM: Third party risk management predictions for 2022
In 2021, TPRM and cybersecurity remained at the forefront of business strategy, so what's next? Learn about 2022 TPRM predictions in our blog!
December 19, 2021 5 min read

Blog
Third-Party Risk
Build the business case: The importance of business resilience and TPRM
Learn about the impact of third-party service outages and how to stand up a TPRM-informed business resilience strategy in our latest blog.
December 16, 2021 4 min read

Blog
Third-Party Risk
Build the business case: The importance of business resilience and TPRM
Learn about the impact of third-party service outages and how to stand up a TPRM-informed business resilience strategy in our latest blog.
December 16, 2021 4 min read
eBook
GRC & Security Assurance
Vendor risk management for privacy professionals
Download the OneTrust Vendor Risk Management Handbook for an in-depth understanding of updated regulations, requirements and more.
November 17, 2021

eBook
GRC & Security Assurance
Vendor risk management for privacy professionals
Download the OneTrust Vendor Risk Management Handbook for an in-depth understanding of updated regulations, requirements and more.
November 17, 2021

Blog
Third-Party Risk
OneTrust Vendorpedia offers same-day support for the 2022 Shared Assessments SIG
Learn how to manage risk in a time-friendly, cost-effective way with low effort for your vendors with our SIG 2022 shared assessments support.
September 28, 2021 3 min read

Blog
Third-Party Risk
OneTrust Vendorpedia offers same-day support for the 2022 Shared Assessments SIG
Learn how to manage risk in a time-friendly, cost-effective way with low effort for your vendors with our SIG 2022 shared assessments support.
September 28, 2021 3 min read

Blog
GRC & Security Assurance
The ultimate security questionnaire guide
Implementing a consistent security questionnaire answering process will save your organization time and money. Read our guide to learn more.
Brianna Smith, Content Marketing Specialist, OneTrust | GRCP
August 17, 2021 15 min read

Blog
GRC & Security Assurance
The ultimate security questionnaire guide
Implementing a consistent security questionnaire answering process will save your organization time and money. Read our guide to learn more.
Brianna Smith, Content Marketing Specialist, OneTrust | GRCP
August 17, 2021 15 min read
eBook
Third-Party Risk
Mastering the third-party risk management lifecycle
Download our third-party risk management eBook and get a complete roadmap to your TPRM lifecycle.
July 13, 2021

Libro electrónico
Third-Party Risk Management
Cómo dominar el ciclo de vida de la gestión de riesgos de terceros
Descarga nuestro libro electrónico sobre gestión de riesgos de terceros y recibe una hoja de ruta completa sobre el ciclo de vida de gestión de riesgos de terceros.
julio 13, 2021

eBook
Third-Party Risk
Mastering the third-party risk management lifecycle
Download our third-party risk management eBook and get a complete roadmap to your TPRM lifecycle.
July 13, 2021

Blog
GRC & Security Assurance
How AutoZone goes the extra mile with OneTrust Vendorpedia
AutoZone Goes the Extra Mile and drives TPRM operations with OneTrust Third-Party Risk Management. Learn more from Auto Zone TPRM, Ryan Walker.
July 07, 2021 3 min read

Blog
GRC & Security Assurance
How AutoZone goes the extra mile with OneTrust Vendorpedia
AutoZone Goes the Extra Mile and drives TPRM operations with OneTrust Third-Party Risk Management. Learn more from Auto Zone TPRM, Ryan Walker.
July 07, 2021 3 min read
eBook
GRC & Security Assurance
What you need to know when building your VRM program
Download our guide to building an effective vendor risk management program and how risk exchanges are vital to your business.
June 13, 2021

Blog
Third-Party Risk
What is vendor risk management?
Vendor risk management (VRM) is a form of risk management that focuses on identifying and reducing risks relating to vendors.
June 09, 2021 14 min read

Blog
Third-Party Risk
What is vendor risk management?
Vendor risk management (VRM) is a form of risk management that focuses on identifying and reducing risks relating to vendors.
June 09, 2021 14 min read

Blog
Third-Party Risk Management
¿Qué es la gestión de riesgos de terceros?
La gestión de riesgos de terceros es un método de gestión de riesgos que se centra en identificar y reducir los riesgos que están relacionados con los proveedores.
junio 09, 2021 14 min read

Blog
Third-Party Risk Management
¿Qué es la gestión de riesgos de terceros?
La gestión de riesgos de terceros es un método de gestión de riesgos que se centra en identificar y reducir los riesgos que están relacionados con los proveedores.
junio 09, 2021 14 min read

Blog
Third-Party Risk Management
¿Qué es la gestión de riesgos de terceros?
La gestión de riesgos de terceros es un método de gestión de riesgos que se centra en identificar y reducir los riesgos que están relacionados con el uso de terceros.
junio 01, 2021 6 min read

Blog
Third-Party Risk Management
¿Qué es la gestión de riesgos de terceros?
La gestión de riesgos de terceros es un método de gestión de riesgos que se centra en identificar y reducir los riesgos que están relacionados con el uso de terceros.
junio 01, 2021 6 min read

Blog
Rischio terze parti
Che cos'è la gestione dei rischi terze parti?
La gestione dei rischi terze parti (Third-party Risk Management, TPRM) è una forma di gestione dei rischi che si concentra sull'identificazione e la riduzione dei rischi relativi all'utilizzo di terze parti.
giugno 01, 2021 6 min read

Blog
Rischio terze parti
Che cos'è la gestione dei rischi terze parti?
La gestione dei rischi terze parti (Third-party Risk Management, TPRM) è una forma di gestione dei rischi che si concentra sull'identificazione e la riduzione dei rischi relativi all'utilizzo di terze parti.
giugno 01, 2021 6 min read

Blog
GRC & Security Assurance
CCPA compliance: Your most frequent CCPA questions answered
The CCPA is only days away from taking effect, and OneTrust has all the resources you need to be CCPA ready by January 1, 2020.
December 24, 2019 24 min read

Blog
GRC & Security Assurance
CCPA compliance: Your most frequent CCPA questions answered
The CCPA is only days away from taking effect, and OneTrust has all the resources you need to be CCPA ready by January 1, 2020.
December 24, 2019 24 min read

Blog
Third-Party Risk
Centralizing your risk register
Companies can integrate their information across systems and data collection points to centralize their risk register and reporting efforts.
December 19, 2019 4 min read

Blog
Third-Party Risk
Centralizing your risk register
Companies can integrate their information across systems and data collection points to centralize their risk register and reporting efforts.
December 19, 2019 4 min read

Blog
Third-Party Risk
Maintain updated data maps with OneTrust vendor risk management
With the OneTrust Vendor Risk Management platform and data mapping, companies sustain an up-to-date data map and automate alerts and actions.
May 07, 2019 4 min read

Blog
Third-Party Risk
Maintain updated data maps with OneTrust vendor risk management
With the OneTrust Vendor Risk Management platform and data mapping, companies sustain an up-to-date data map and automate alerts and actions.
May 07, 2019 4 min read
Third-Party Management | Request Demo | OneTrust
Request a free demo of OneTrust Third Party Management and get personalized best practice advice from a third-party risk expert.

Customer Story
Third-Party Risk
Rochester Regional Health
Learn how Rochester Regional Health creates a patient-centric privacy program with OneTrust third-party risk management solutions.
3 min read

Cybersecurity
Third-Party Risk
BitSight
The integration between BitSight and OneTrust Third-Party Risk is a powerful tool that can help organizations to manage third-party risk and to protect their data.

File Storage & Sharing
Privacy Management
DocuSign
OneTrust integrates with DocuSign to automatically send eSignature envelopes and request attestation of responses from customers and vendors.

Cybersecurity
Supplier Sustainability & Responsibility
Supply Wisdom
By using Supply Wisdom and OneTrust together, organizations can get a comprehensive view of third-party risk and take proactive steps to mitigate it.
Herramienta de gestión de riesgos de terceros de OneTrust y la CSA | OneTrust
Hazte con la herramienta de gestión de riesgos de terceros de OneTrust y de la CSA, y aprende a automatizar todo el ciclo de vida de la gestión de proveedores.
Outil de gestion des risques fournisseur OneTrust-CSA | OneTrust
Avec l’outil OneTrust-CSA, découvrez comment automatiser l’ensemble du cycle de vie de la gestion de vos fournisseurs.
Third-Party Management | Demande de démo | OneTrust
Demandez une démonstration gratuite de la solution OneTrust Third Party Management et obtenez des conseils personnalisés sur les bonnes pratiques avec un expert en gestion des risques tiers.
Gestión de terceros | Demostración de solicitud | OneTrust
Solicita una demostración gratuita de OneTrust Third Party Management y recibe consejos personalizados sobre prácticas recomendadas de un experto.
Third-Party Management | Demo anfordern | OneTrust
Fordern Sie eine kostenfreie Demo zu OneTrust Third-Party Management an und lassen Sie sich von einem Experten für Drittparteienrisiken persönlich beraten.
OneTrust-CSA Lieferantenrisikomanagement-Tool | OneTrust
Holen Sie sich das OneTrust-CSA Lieferantenrisikomanagement-Tool und erfahren Sie, wie Sie den gesamten Lebenszyklus des Lieferantenmanagements automatisieren.
Third Party Management | Solicitar demonstração | OneTrust
Solicite uma demonstração gratuita da solução OneTrust Third Party Management e obtenha o aconselhamento personalizado sobre boas práticas na gestão de riscos de terceiros.
Ferramenta de Gerenciamento de Riscos de Fornecedores OneTrust-CSA | OneTrust
Obtenha a ferramenta de gerenciamento de riscos de fornecedores OneTrust-CSA e saiba como automatizar todo o ciclo de vida da gestão de fornecedores.
Third-Party Management | Richiedi una demo | OneTrust
Richiedi una demo gratuita di Third Party Management di OneTrust e ricevi pratiche consigliate personalizzate da un esperto dei rischi da parte di terzi.
Strumento Gestione del rischio fornitore OneTrust e CSA | OneTrust
Ottieni lo strumento Gestione del rischio fornitore OneTrust e CSA e scopri come automatizzare l'intero ciclo di vita della gestione dei fornitori.
Third-Party Management | Richiedi una demo | OneTrust
Richiedi una demo gratuita di Third Party Management di OneTrust e ricevi pratiche consigliate personalizzate da un esperto dei rischi da parte di terzi.
Strumento Gestione del rischio fornitore OneTrust e CSA | OneTrust
Ottieni lo strumento Gestione del rischio fornitore OneTrust e CSA e scopri come automatizzare l'intero ciclo di vita della gestione dei fornitori.
Third-Party Management | Demo anfordern | OneTrust
Fordern Sie eine kostenfreie Demo zu OneTrust Third-Party Management an und lassen Sie sich von einem Experten für Drittparteienrisiken persönlich beraten.
OneTrust-CSA Lieferantenrisikomanagement-Tool | OneTrust
Holen Sie sich das OneTrust-CSA Lieferantenrisikomanagement-Tool und erfahren Sie, wie Sie den gesamten Lebenszyklus des Lieferantenmanagements automatisieren.
Third Party Management | Solicitar demonstração | OneTrust
Solicite uma demonstração gratuita da solução OneTrust Third Party Management e obtenha o aconselhamento personalizado sobre boas práticas na gestão de riscos de terceiros.
Ferramenta de Gerenciamento de Riscos de Fornecedores OneTrust-CSA | OneTrust
Obtenha a ferramenta de gerenciamento de riscos de fornecedores OneTrust-CSA e saiba como automatizar todo o ciclo de vida da gestão de fornecedores.
OneTrust Partner Webinar: Overview of Q1 UCPM & Q2 TPRM Sales Plays Webinar | Resources | OneTrust

Compliance
Third-Party Risk
Valence Security
Valence Security and OneTrust have partnered to create a seamless integration between SSPM and TPRM, bridging the gap between risk managers and security analysts.

Analytics
Privacy Management
Tableau
Ingest OneTrust data into Tableau for customized dashboards and analytics to drive insight into the privacy program’s activity and create custom reports.

Cybersecurity
Third-Party Risk
Upguard
UpGuard and OneTrust Third-Party Risk Management integrate so organizations have a comprehensive view of third-party risk to help prevent data breaches.

Compliance
Privacy Management
LexisNexis Risk Solutions
The integration with LexisNexis Risk Solutions and OneTrust can help complete consumer requests requirements under the CCPA and other state privacy laws.

Compliance
Third-Party Risk
Bureau Van Dijk
Integrating OneTrust with Bureau van Dijk and RDC can help organizations to identify and assess risks, including financial, operational, and reputational risks.

AML & KYC
Third-Party Risk
Dun & Bradstreet
Dun & Bradstreet and OneTrust offer a powerful solution for third-party risk management by integrating data and insights to help organizations identify and monitor risks.

AML & KYC
Third-Party Risk
Dow Jones
Together, Dow Jones and OneTrust offer a powerful solution for third-party risk management, enabling organizations to reduce critical vulnerabilities, improve compliance, and build trust.

Cybersecurity
Third-Party Due Diligence
Recorded Future
Stay up-to-date on the latest threat intelligence about your organizations third-party vendors by integrating OneTrust with Recorded Future.

Cybersecurity
Third-Party Risk
Black Kite
Integrating OneTrust and BlackKite helps organizations streamline third-party risk assessments while gaining more visibility over technical, financial, and compliance risks.

Cybersecurity
Third-Party Risk
RiskRecon
RiskRecon integrates with OneTrust to provide organizations with cybersecurity scores and more, which can be pulled on a scheduled basis.

Identity Access Management & Identity Verification
Consent & Preferences
SecurityScorecard
SecurityScorecard and OneTrust integrate to provide a comprehensive view of third-party cybersecurity posture and automate risk mitigation.

Customer Story
Third-Party Risk
Southern Veterinary Partners (SVP)
See how this Southern Veterinary Partners improved third-party risk management and enhanced its security and efficiency.
Gestión de terceros | Demostración de solicitud | OneTrust
Solicita una demostración gratuita de OneTrust Third Party Management y recibe consejos personalizados sobre prácticas recomendadas de un experto.
Herramienta de gestión de riesgos de terceros de OneTrust y la CSA | OneTrust
Hazte con la herramienta de gestión de riesgos de terceros de OneTrust y de la CSA, y aprende a automatizar todo el ciclo de vida de la gestión de proveedores.

Upcoming webinars
Third-Party Risk
Building a strong security posture: managing compliance, risk and business engagement in a dynamic landscape
Watch our webinar and gain insight on how to navigate InfoSec's evolving compliance landscape.
Third-Party Management | Demande de démo | OneTrust
Demandez une démonstration gratuite de la solution OneTrust Third Party Management et obtenez des conseils personnalisés sur les bonnes pratiques avec un expert en gestion des risques tiers.
E-Book
Third-Party Risk
DORA verstehen: Auswirkungen des Digital Operational Resilience Act auf das Third-Party Risk Management
Third-Party Management | Request Demo | OneTrust
Request a free demo of OneTrust Third Party Management and get personalized best practice advice from a third-party risk expert.

Customer Story
Third-Party Risk
Southern Veterinary Partners (SVP)
See how this Southern Veterinary Partners improved third-party risk management and enhanced its security and efficiency.

Customer Story
Third-Party Risk
Rochester Regional Health
Learn how Rochester Regional Health creates a patient-centric privacy program with OneTrust third-party risk management solutions.
3 min read

Customer Story
Technology Risk & Compliance
Sara Assicurazioni
Discover how Sara Assicurazioni, one of Italy’s oldest insurance companies, leverages OneTrust to enhance cybersecurity, privacy, and regulatory compliance under evolving frameworks like DORA and NIS2.

Customer Story
Technology Risk & Compliance
Sara Assicurazioni
Discover how Sara Assicurazioni, one of Italy’s oldest insurance companies, leverages OneTrust to enhance cybersecurity, privacy, and regulatory compliance under evolving frameworks like DORA and NIS2.

Customer Story
Privacy Management
Amplifon
See how Amplifon built a robust privacy management system for their global business with OneTrust Solutions.

Customer Story
Privacy Management
Amplifon
See how Amplifon built a robust privacy management system for their global business with OneTrust Solutions.

Customer Story
Privacy & Data Governance
Drax Group
See how the Drax Group uses the OneTrust Privacy and Data Governance Cloud to manage privacy requirements and support growth.

Customer Story
Privacy & Data Governance
Drax Group
See how the Drax Group uses the OneTrust Privacy and Data Governance Cloud to manage privacy requirements and support growth.

Customer Story
Third-Party Risk
Mews
At Mews, staying ahead in compliance and security is a priority. To explore this further, we spoke with Jan Tauš, Director of Internal IT, Security, and Compliance at Mews, about how the company leverages OneTrust solutions to navigate regulatory challenges and enhance efficiency.

Customer Story
Third-Party Risk
Mews
At Mews, staying ahead in compliance and security is a priority. To explore this further, we spoke with Jan Tauš, Director of Internal IT, Security, and Compliance at Mews, about how the company leverages OneTrust solutions to navigate regulatory challenges and enhance efficiency.

Upcoming webinars
Third-Party Risk
Third-party management academy series
Join this webinar series, which will focus on the four foundational pillars of Third-Party Risk Management: Automation, Compliance, Reporting, and Collaboration.

Upcoming webinars
Third-Party Risk
Third-party management academy series
Join this webinar series, which will focus on the four foundational pillars of Third-Party Risk Management: Automation, Compliance, Reporting, and Collaboration.

Blog
Third-Party Risk
Aufbau eines effektiven Third Party Managements
Dieser Blog diskutiert, wie ein effektives Third Party Management etabliert werden kann, das Sicherheit für Datenschutz-, Sicherheits-, Ethik- und ESG-Teams schafft.
5 min read

Blog
Third-Party Risk
Aufbau eines effektiven Third Party Managements
Dieser Blog diskutiert, wie ein effektives Third Party Management etabliert werden kann, das Sicherheit für Datenschutz-, Sicherheits-, Ethik- und ESG-Teams schafft.
5 min read
OneTrust Partner Webinar: Overview of Q1 UCPM & Q2 TPRM Sales Plays Webinar | Resources | OneTrust

E-Book
Third-Party Risk
DORA verstehen: Auswirkungen des Digital Operational Resilience Act auf das Third-Party Risk Management
Outil de gestion des risques fournisseur OneTrust-CSA | OneTrust
Avec l’outil OneTrust-CSA, découvrez comment automatiser l’ensemble du cycle de vie de la gestion de vos fournisseurs.

On-demand webinars
Third-Party Risk
Building a strong security posture: managing compliance, risk and business engagement in a dynamic landscape
Watch our webinar and gain insight on how to navigate InfoSec's evolving compliance landscape.

Cybersecurity
Third-Party Risk
Black Kite
Integrating OneTrust and BlackKite helps organizations streamline third-party risk assessments while gaining more visibility over technical, financial, and compliance risks.

Compliance
Third-Party Risk
Bureau Van Dijk
Integrating OneTrust with Bureau van Dijk and RDC can help organizations to identify and assess risks, including financial, operational, and reputational risks.

Cybersecurity
Third-Party Risk
BitSight
The integration between BitSight and OneTrust Third-Party Risk is a powerful tool that can help organizations to manage third-party risk and to protect their data.

AML & KYC
Third-Party Risk
Dow Jones
Together, Dow Jones and OneTrust offer a powerful solution for third-party risk management, enabling organizations to reduce critical vulnerabilities, improve compliance, and build trust.

File Storage & Sharing
Privacy Management
DocuSign
OneTrust integrates with DocuSign to automatically send eSignature envelopes and request attestation of responses from customers and vendors.

AML & KYC
Third-Party Risk
Dun & Bradstreet
Dun & Bradstreet and OneTrust offer a powerful solution for third-party risk management by integrating data and insights to help organizations identify and monitor risks.

Compliance
Privacy Management
LexisNexis Risk Solutions
The integration with LexisNexis Risk Solutions and OneTrust can help complete consumer requests requirements under the CCPA and other state privacy laws.

Cybersecurity
Third-Party Risk
RiskRecon
RiskRecon integrates with OneTrust to provide organizations with cybersecurity scores and more, which can be pulled on a scheduled basis.

Cybersecurity
Third-Party Due Diligence
Recorded Future
Stay up-to-date on the latest threat intelligence about your organizations third-party vendors by integrating OneTrust with Recorded Future.

Cybersecurity
Third-Party Risk
Upguard
UpGuard and OneTrust Third-Party Risk Management integrate so organizations have a comprehensive view of third-party risk to help prevent data breaches.

Analytics
Privacy Management
Tableau
Ingest OneTrust data into Tableau for customized dashboards and analytics to drive insight into the privacy program’s activity and create custom reports.

Cybersecurity
Supplier Sustainability & Responsibility
Supply Wisdom
By using Supply Wisdom and OneTrust together, organizations can get a comprehensive view of third-party risk and take proactive steps to mitigate it.

Identity Access Management & Identity Verification
Consent & Preferences
SecurityScorecard
SecurityScorecard and OneTrust integrate to provide a comprehensive view of third-party cybersecurity posture and automate risk mitigation.

Compliance
Third-Party Risk
Valence Security
Valence Security and OneTrust have partnered to create a seamless integration between SSPM and TPRM, bridging the gap between risk managers and security analysts.

Témoignage client
Technology Risk & Compliance
Sara Assicurazioni
Découvrez comment Sara Assicurazioni, l’une des plus anciennes compagnies d’assurance italienne, utilise OneTrust pour améliorer la cybersécurité, la confidentialité et la conformité réglementaire au regard de cadres de référence en évolution tels que DORA ou NIS2.

Témoignage client
Third-Party Risk
Mews
Chez Mews, garder une longueur d’avance en matière de conformité et de sécurité est une priorité. Pour en savoir plus, nous avons discuté avec Jan Tauš, Director of IT, Security, and Compliance chez Mews, de la manière dont l’entreprise utilise les solutions OneTrust pour relever les défis réglementaires et améliorer son efficacité.

Caso di successo
Rischio terze parti
Mews
Per Mews, stare al passo con conformità e sicurezza è una priorità assoluta. Per approfondire ulteriormente la questione, abbiamo parlato con Jan Tauš, Director di internal IT, security e compliance di Mews, di come l'azienda sfrutti le soluzioni di OneTrust per affrontare le problematiche normative e aumentare l'efficienza.

Caso di successo
Rischio terze parti
Mews
Per Mews, stare al passo con conformità e sicurezza è una priorità assoluta. Per approfondire ulteriormente la questione, abbiamo parlato con Jan Tauš, Director di internal IT, security e compliance di Mews, di come l'azienda sfrutti le soluzioni di OneTrust per affrontare le problematiche normative e aumentare l'efficienza.

Kundenbericht
Third-Party Risk
Mews
Bei Mews haben die Einhaltung gesetzlicher Vorgaben und maximale Sicherheit höchste Priorität. Wir haben mit Jan Tauš, Director für interne IT, Sicherheit und Compliance bei Mews, gesprochen, um mehr darüber zu erfahren. Er erklärt, wie das Unternehmen die Lösungen von OneTrust nutzt, um regulatorische Anforderungen zu erfüllen und gleichzeitig die Effizienz im Tagesgeschäft zu steigern.

Kundenbericht
Technology Risk & Compliance
Sara Assicurazioni
Erfahren Sie, wie Sara Assicurazioni – eines der traditionsreichsten Versicherungsunternehmen Italiens – OneTrust nutzt, um die Cybersicherheit, den Datenschutz und die regulatorische Compliance gezielt zu stärken, insbesondere im Hinblick auf die neuen Anforderungen durch DORA und NIS2.
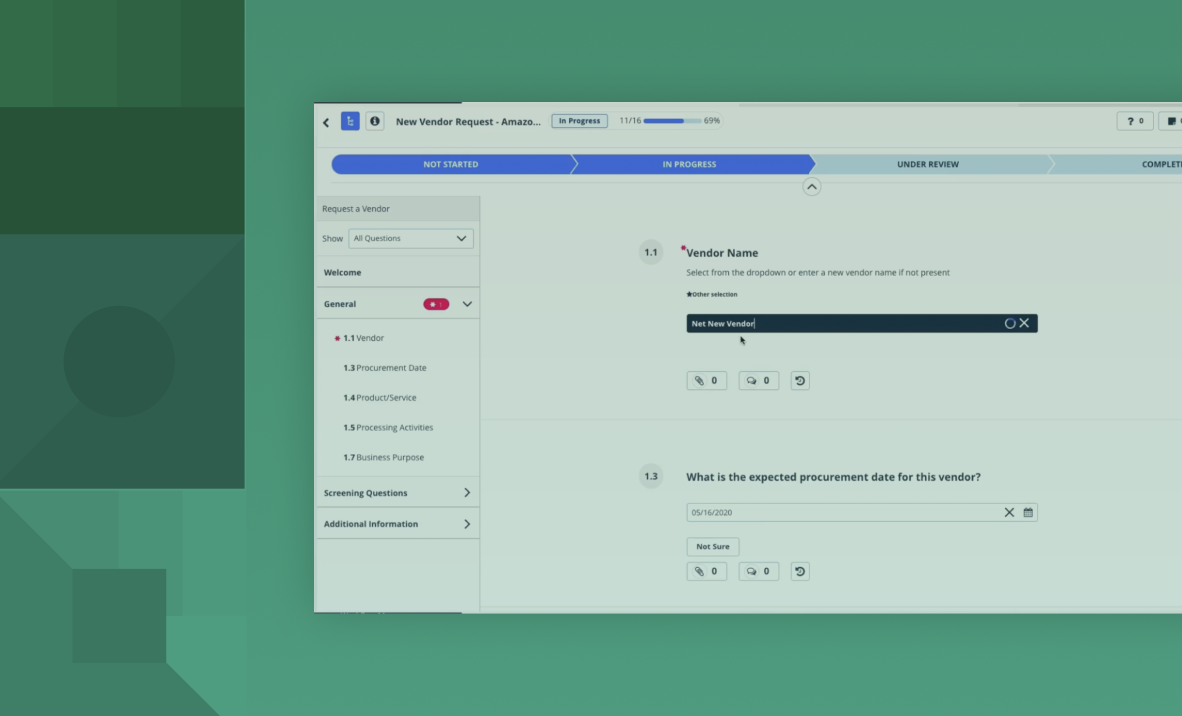
Demo
Third-Party Risk
OneTrust Third-party Management demo
Discover how our Third-Party Management solution helps you assess, monitor, and mitigate vendor risks while ensuring compliance.
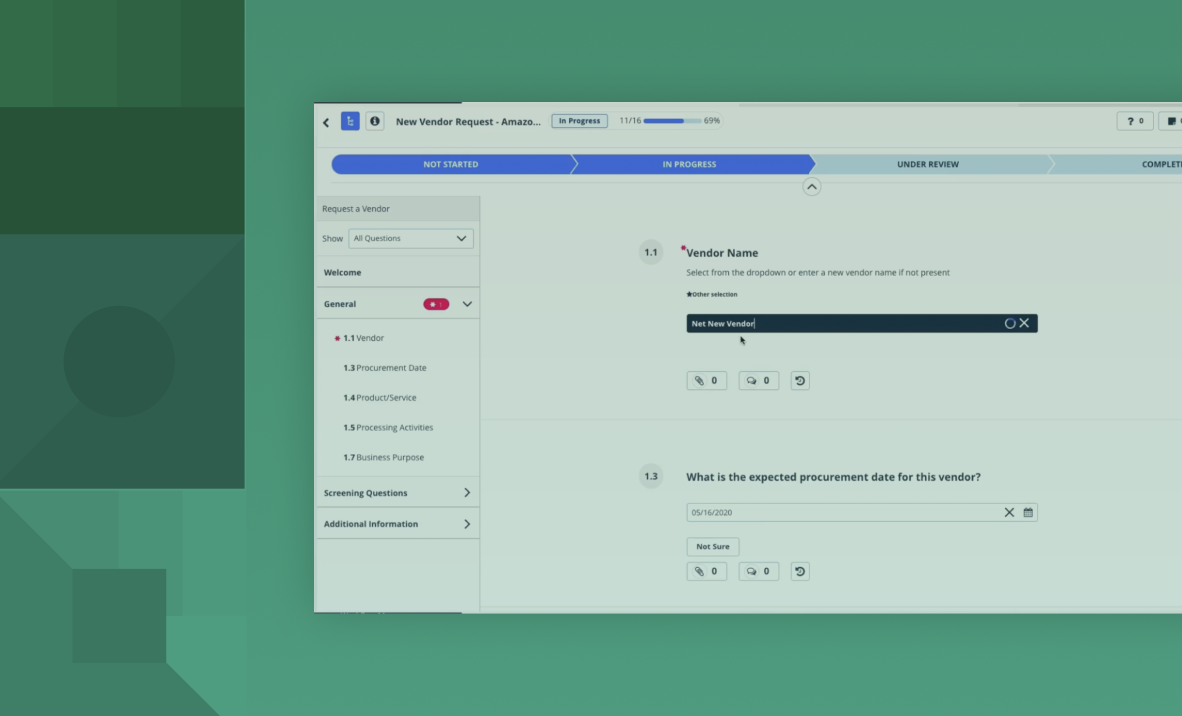
Demo
Third-Party Risk
OneTrust Third-party Management demo
Discover how our Third-Party Management solution helps you assess, monitor, and mitigate vendor risks while ensuring compliance.

História do cliente
Third-Party Risk
Mews
Na Mews, antecipar os desafios em conformidade regulatória e segurança de dados é uma prioridade. Jan Tauš, diretor de TI, segurança e conformidade da empresa, explica como as soluções da OneTrust são usadas para enfrentar os desafios regulatórios e melhorar a eficiência.

História do cliente
Technology Risk & Compliance
Sara Assicurazioni
Saiba como a Sara Assicurazioni, uma das mais antigas seguradoras italianas, usa a plataforma OneTrust para aprimorar a segurança cibernética, a privacidade e a conformidade com regulamentos e marcos normativos em evolução, como DORA e NIS2.

Testimonio de cliente
Third-Party Risk Management
Mews
En Mews, ir un paso por delante en lo que respecta a seguridad y cumplimiento normativo es una prioridad. Para ahondar sobre este tema, hablamos con Jan Tauš, director de TI, seguridad y cumplimiento normativo de Mews, sobre cómo su empresa saca partido de las soluciones de OneTrust a la hora de superar los desafíos normativos y mejorar la eficiencia.

Testimonio de cliente
Technology Risk & Compliance
Sara Assicurazioni
Descubre cómo Sara Assicurazioni, una de las compañías de seguros más antiguas de Italia, saca partido de OneTrust para mejorar la ciberseguridad, la privacidad y el cumplimiento normativo según marcos en continua evolución, como la DORA y la NIS2.

Témoignage client
Privacy Management
Amplifon
Découvrez comment Amplifon a établi un système de gestion de la confidentialité robuste pour son activité mondiale avec les solutions OneTrust.

Témoignage client
Privacy Management
Amplifon
Découvrez comment Amplifon a établi un système de gestion de la confidentialité robuste pour son activité mondiale avec les solutions OneTrust.

História do cliente
Gestão da privacidade
Amplifon
Saiba como a Amplifon usou as as soluções da OneTrust para construir um sistema robusto de gestão de privacidade para seus negócios internacionais.

História do cliente
Gestão da privacidade
Amplifon
Saiba como a Amplifon usou as as soluções da OneTrust para construir um sistema robusto de gestão de privacidade para seus negócios internacionais.

Testimonio de cliente
Gestión de la privacidad
Amplifon
Descubre cómo Amplifon desarrolló un sólido sistema de gestión de la privacidad para su negocio global con las soluciones de OneTrust.

On-demand webinars
Technology Risk & Compliance
Risk in 30'
Join our risk management webinar series to learn how AI, NIS2, and modern TPRM practices help teams reduce manual work and strengthen resilience.

On-demand webinars
Technology Risk & Compliance
Risk in 30'
Join our risk management webinar series to learn how AI, NIS2, and modern TPRM practices help teams reduce manual work and strengthen resilience.

Kundenbericht
Privacy Management
Amplifon
Erfahren Sie, wie Amplifon mithilfe von OneTrust Lösungen ein leistungsstarkes Datenschutzmanagement für sein globales Geschäft aufgebaut hat.

Customer Story
Technology Risk & Compliance
StormGeo
StormGeo combines data-driven weather intelligence with strong cybersecurity governance by using OneTrust to enhance third-party risk management, compliance, and scalable innovation across its global operations.

Customer Story
Technology Risk & Compliance
StormGeo
StormGeo combines data-driven weather intelligence with strong cybersecurity governance by using OneTrust to enhance third-party risk management, compliance, and scalable innovation across its global operations.
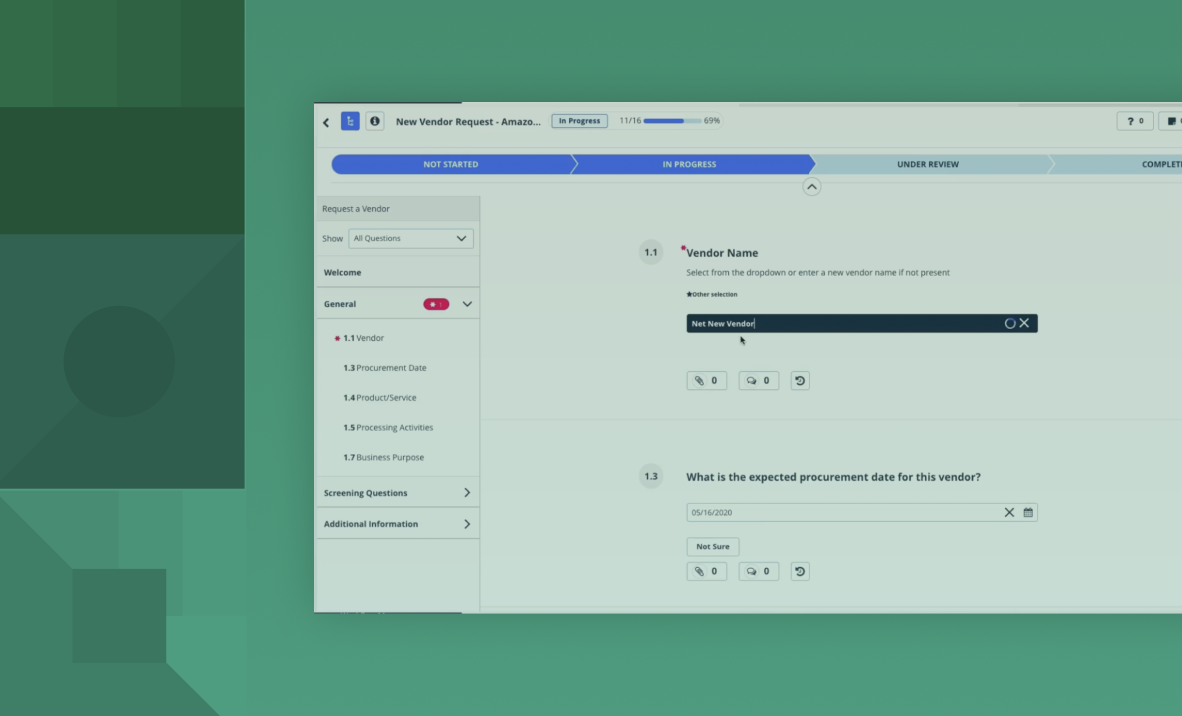
Demo
Rischio terze parti
Demo di OneTrust Third-Party Management
Scopri in che modo la soluzione Third-Party Management può aiutarti a valutare, monitorare e mitigare i rischi correlati ai fornitori, garantendo allo stesso tempo la conformità normativa.
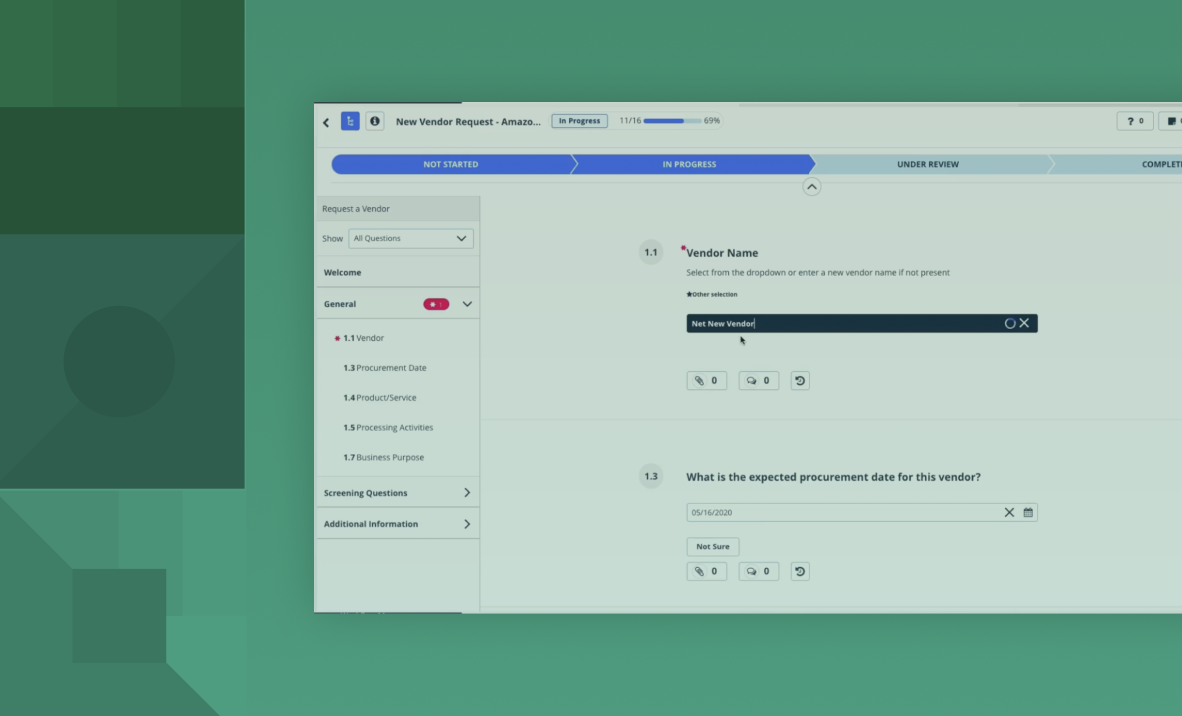
Demo
Rischio terze parti
Demo di OneTrust Third-Party Management
Scopri in che modo la soluzione Third-Party Management può aiutarti a valutare, monitorare e mitigare i rischi correlati ai fornitori, garantendo allo stesso tempo la conformità normativa.
Third-Party Management | Solutions | OneTrust
Manage third-party risk at scale with data-led and risk-based solutions and empower your business to create a resilient and secure third-party ecosystem.
Third-Party Management | Solutions | OneTrust
Manage third-party risk at scale with data-led and risk-based solutions and empower your business to create a resilient and secure third-party ecosystem.
Third-Party Management | Soluciones | OneTrust
Gestiona el riesgo de terceros a escala con soluciones basadas en datos y riesgos, y permite que tu empresa pueda crear un ecosistema de terceros resiliente y seguro.
Third-Party Management | Soluciones | OneTrust
Gestiona el riesgo de terceros a escala con soluciones basadas en datos y riesgos, y permite que tu empresa pueda crear un ecosistema de terceros resiliente y seguro.
Third-Party Management | Soluzioni | OneTrust
Gestisci il rischio terze parti su larga scala con soluzioni basate su dati e rischi e consenti alla tua azienda di creare un ecosistema resiliente e sicuro.
Third-Party Management | Soluzioni | OneTrust
Gestisci il rischio terze parti su larga scala con soluzioni basate su dati e rischi e consenti alla tua azienda di creare un ecosistema resiliente e sicuro.
Third-Party Management | Solutions | OneTrust
Gérez le risque tiers à grande échelle grâce à des solutions basées sur les données et les risques et donnez à votre entreprise les moyens de créer un écosystème de tiers résilient et sécurisé.
Third-Party Management | Solutions | OneTrust
Gérez le risque tiers à grande échelle grâce à des solutions basées sur les données et les risques et donnez à votre entreprise les moyens de créer un écosystème de tiers résilient et sécurisé.
Third-Party Management | Soluções | OneTrust
Gerencie o risco de terceiros em escala com soluções baseadas em dados e riscos e crie um ecossistema de parceiros resiliente e seguro.
Third-Party Management | Soluções | OneTrust
Gerencie o risco de terceiros em escala com soluções baseadas em dados e riscos e crie um ecossistema de parceiros resiliente e seguro.
Third-Party Management | Lösungen | OneTrust
Managen Sie Drittanbieterrisiken in großem Umfang mit daten- und risikobasierten Lösungen und befähigen Sie Ihr Unternehmen, ein widerstandsfähiges und sicheres Drittanbieter-Ökosystem zu schaffen.
Third-Party Management | Lösungen | OneTrust
Managen Sie Drittanbieterrisiken in großem Umfang mit daten- und risikobasierten Lösungen und befähigen Sie Ihr Unternehmen, ein widerstandsfähiges und sicheres Drittanbieter-Ökosystem zu schaffen.
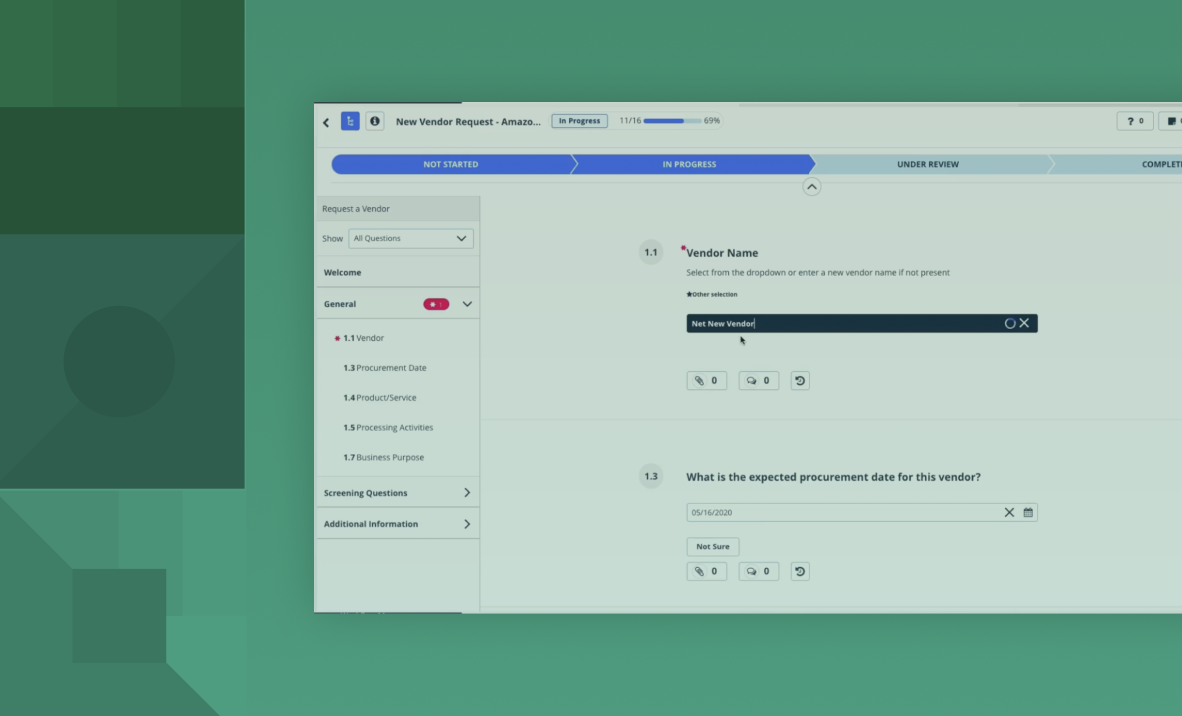
Demo
Third-Party Risk
OneTrust Third-Party Management – Demo
Erfahren Sie, wie unsere Third-Party Management-Lösung Sie dabei unterstützt, Lieferantenrisiken zu bewerten, kontinuierlich zu überwachen und gezielt zu reduzieren und gleichzeitig die Einhaltung regulatorischer Anforderungen sicherzustellen.
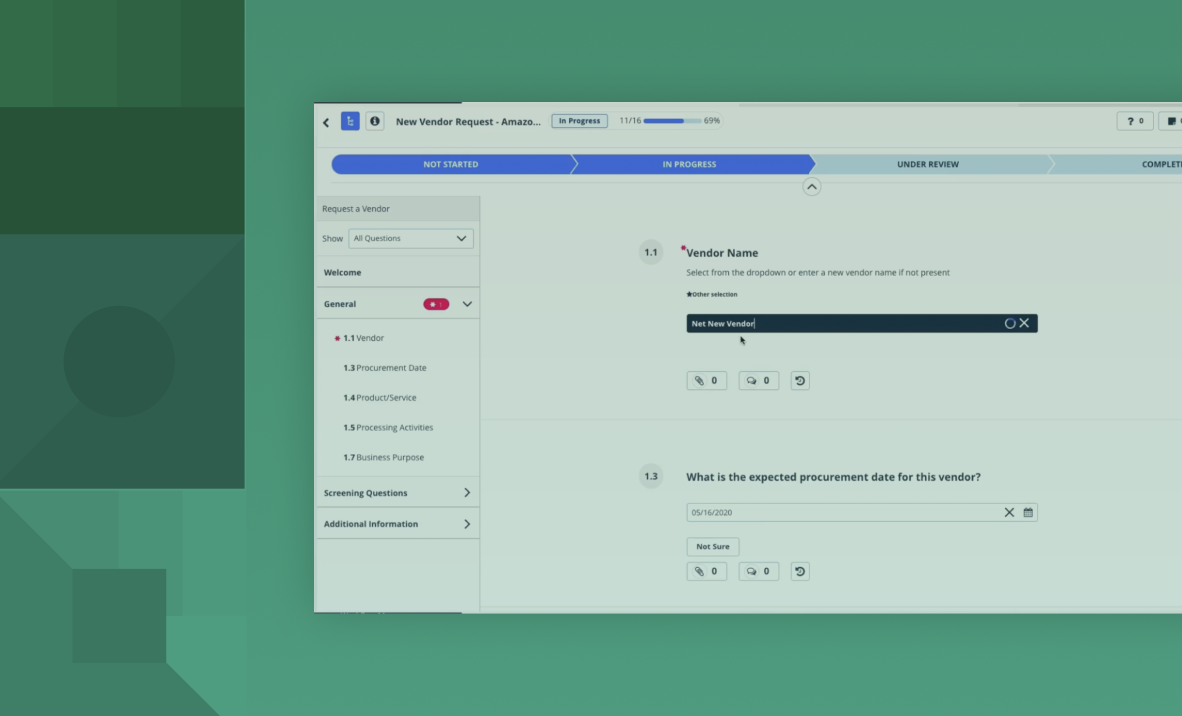
Demo
Third-Party Risk
OneTrust Third-Party Management – Demo
Erfahren Sie, wie unsere Third-Party Management-Lösung Sie dabei unterstützt, Lieferantenrisiken zu bewerten, kontinuierlich zu überwachen und gezielt zu reduzieren und gleichzeitig die Einhaltung regulatorischer Anforderungen sicherzustellen.
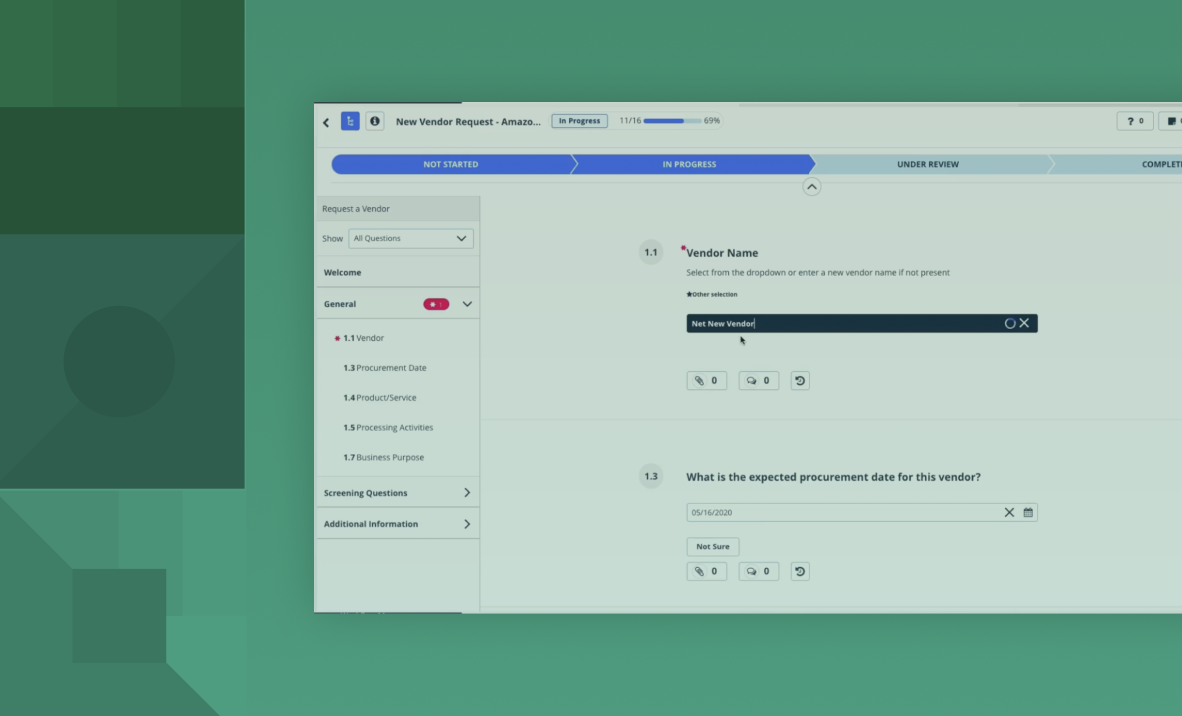
Demo
Third-Party Risk
Démo de OneTrust Third-Party Management
Découvrez comment notre solution Third-Party Management vous aide à évaluer, à surveiller et à atténuer les risques tiers tout en garantissant la conformité.
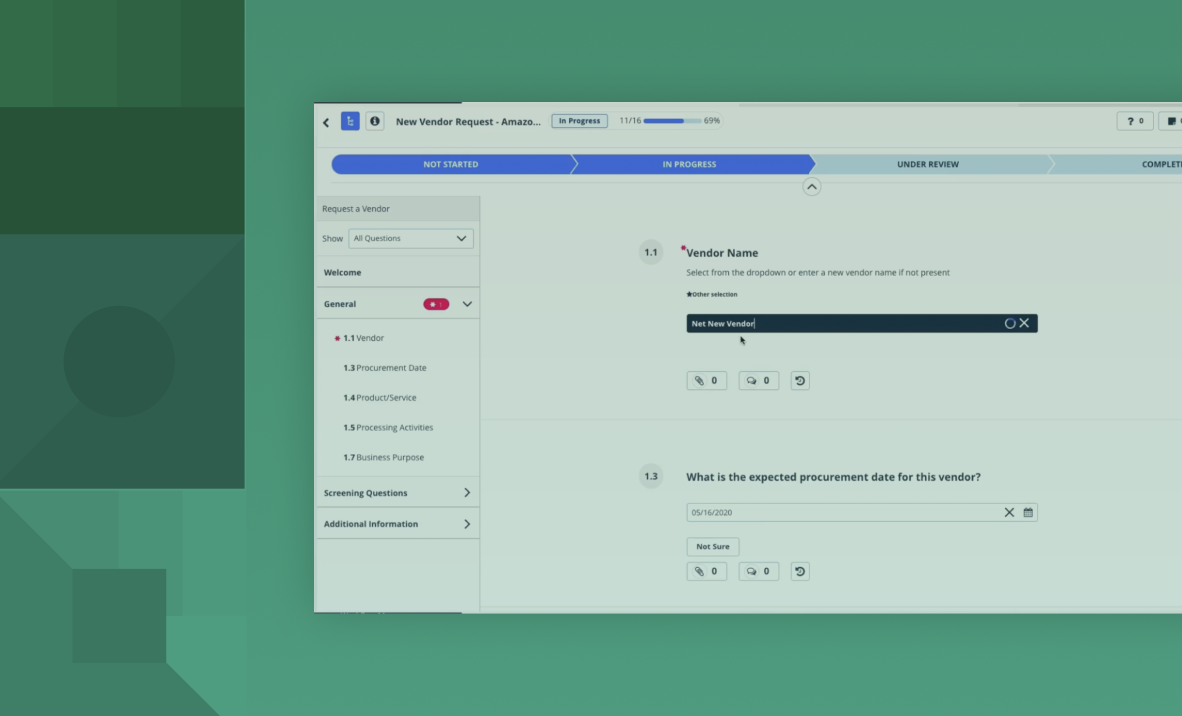
Demo
Third-Party Risk
Démo de OneTrust Third-Party Management
Découvrez comment notre solution Third-Party Management vous aide à évaluer, à surveiller et à atténuer les risques tiers tout en garantissant la conformité.
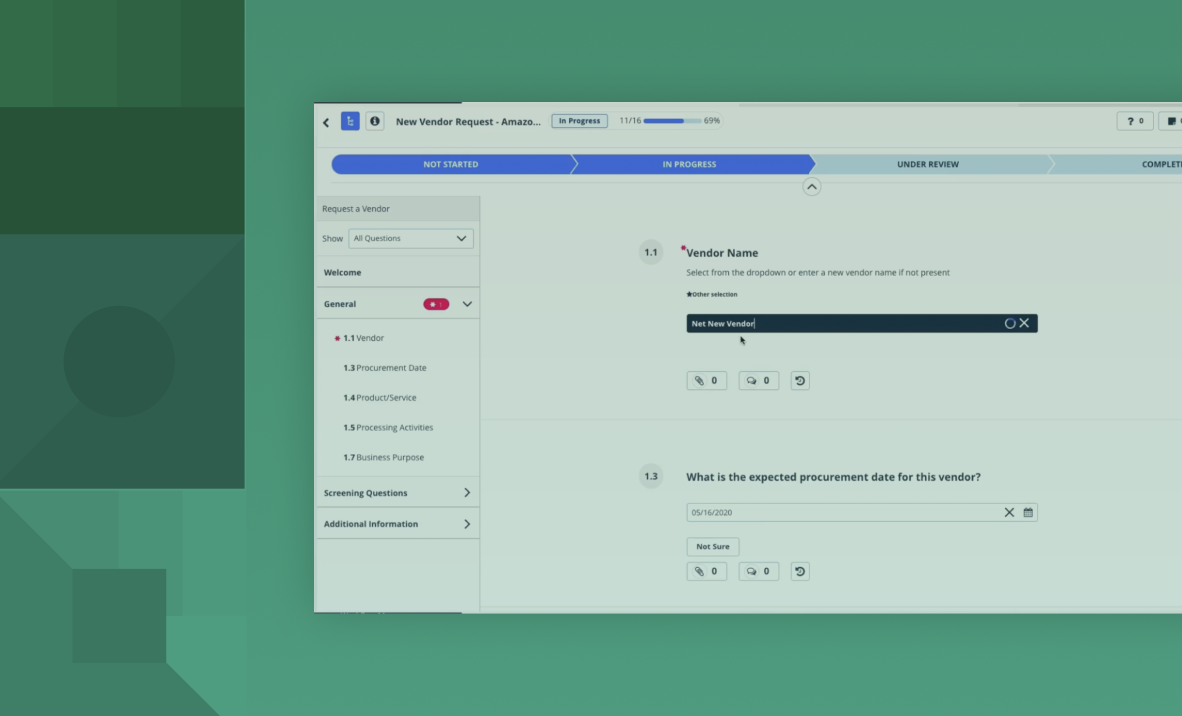
Demo
Third-Party Risk Management
Demo de OneTrust Third-Party Management
Descubre cómo nuestra solución de gestión de terceros te ayuda a evaluar, monitorizar y mitigar los riesgos de los proveedores, al mismo tiempo que garantiza el cumplimiento normativo.
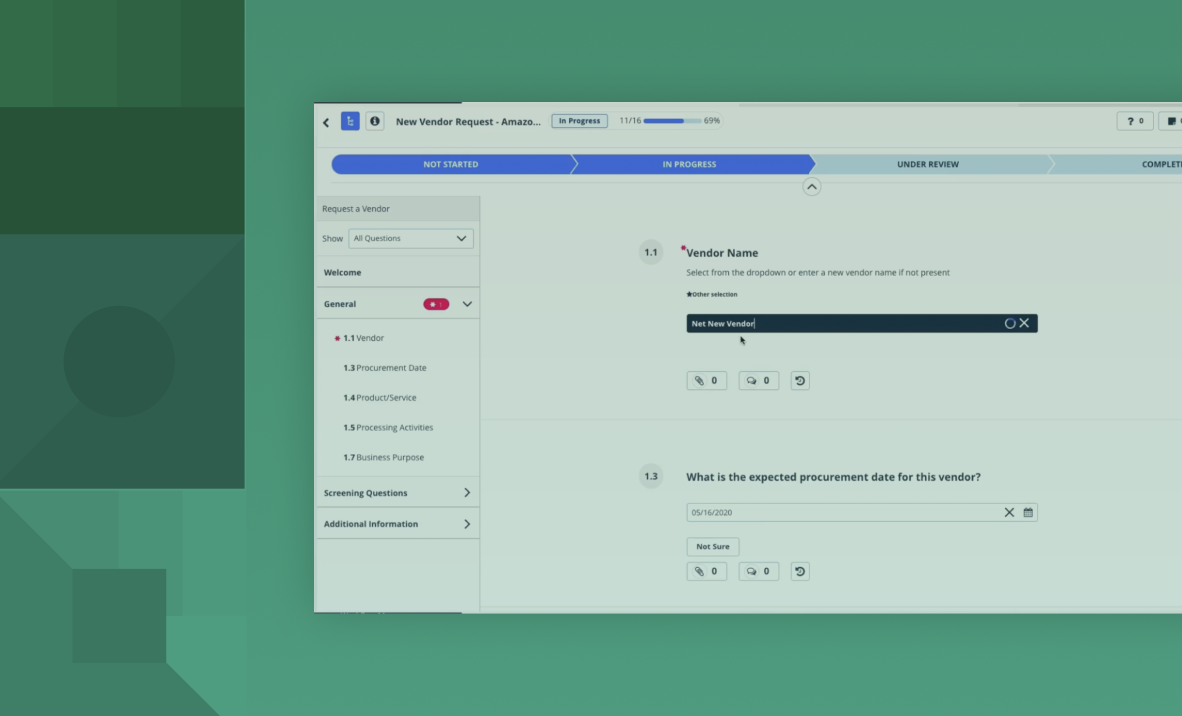
Demo
Third-Party Risk Management
Demo de OneTrust Third-Party Management
Descubre cómo nuestra solución de gestión de terceros te ayuda a evaluar, monitorizar y mitigar los riesgos de los proveedores, al mismo tiempo que garantiza el cumplimiento normativo.
