Cybersecurity teams are facing larger and more sophisticated cybersecurity threats than ever. In 2021, there was a 62% global attack spike in ransomware (158% increase in North American attacks alone), and an increased focus on attacks by regulatory bodies. Teams not only have to track vulnerabilities within their internal security posture but also ensure their prospective third parties are vetted before engaging in business.
Cloud adoption catalyzed by remote work has increased exposure to cyber threats. And it’s not just you that is at risk, your vendors are too. So, how do you know if your vendors have the right cybersecurity controls in place? Here are some common and emerging cyber threats to consider as you assess your program and vendor ecosystem:
Common and Emerging Cyber Threats
In the face of increased incidents, it’s important to understand not only how other organizations are preventing attacks, but the details of the attack types so that your organization can stand up an appropriate preparedness plan to deploy if or when it’s needed. Additionally, it’s crucial to understand the scope of your third and fourth parties and the impact they have on your internal security posture. When standing up a proactive security solution, it’s important to work with your vendors to ensure a plan is in place that considers each of the following attack types:
- Phishing: A common internal threat used by attackers to penetrate systems through fake or misleading communication to internal employees.
- C-Level Attacks (Whaling): Newer attacks target C-level executives who can have access to larger and more sensitive information.
- Insider Threats: Malicious employees or contractors who steal sensitive or confidential data from an organization for the purpose of reputational damage, financial consequences, and/or extortion.
- Ransomware: Attackers leverage network vulnerabilities to access data, block access, and hold the data for ransom. CISA’s recommendations address the increase in malicious cyber actors using ransomware to exfiltrate data and then threaten to sell or leak the exfiltrated data if the victim does not pay the ransom.
- Compromised or Weak Credentials: Things like common usernames and weak or reused passwords can lead to weaknesses in your system and leave your organization open to attacks. Monitor credential misuse and make sure your company has multi-factor authentication (MFA) in place.
Other common attack vectors include DDoS, brute force attacks, man-in-the-middle attacks, and exploitation of zero-day vulnerabilities. Emerging attacks and threats include:
- Supply Chain Hacks: Supply chain attacks have made headlines and wreaked havoc across businesses. These attacks, which often use ransomware, can impact thousands of organizations by targeting a single company.
- AI and ML Attacks: This is a new approach for attackers to infiltrate systems and more discretely access networks.
Tracking common and emerging cyber threats with new and upcoming regulations
While cyber threat defense is prioritized by organizations, global regulatory authorities are emphasizing attack preparedness through new and upcoming regulations. As security teams consider increased guidance from relevant governing bodies, it’s important to make sure that they’re also considering the ways third and fourth parties are impacting your compliance in addition to internal processes.
Regulation from China
In 2021 China released laws related to cybersecurity and personal information protection. The laws place broad expectations around the tracking of valuable data in the interest of the country’s national security and aim to regulate the collection and usage of personal information by companies operating in the country and offer data subjects a greater level of protection and control over their personal information.
Third and 4th party involvement:
What impact do your third and fourth parties have on personal information protection? If your vendor ecosystem isn’t under continual monitoring, it’s possible that a breach to a vendor or 4th party could compromise your organization’s integrity.
Regulation from NIST
The NIST Information Technology Laboratory (ITL) released a cybersecurity ransomware framework profile purposed to aid organizations in identifying and prioritizing use cases of security and resilience around ransomware threats. The document dovetails off recent regulatory action taken by the US government and outlines action items and basic preventative measures for organizations of all sizes.
Third and fourth-party involvement:
If a vendor or 4th party is affected by ransomware and goes offline, it’s possible that a crucial part of your supply chain can be left open to vulnerabilities. Understanding what to do in the face of ransomware affecting your organization is crucial to overall security.
Regulation from DHS
Following an impactful attack in the oil & gas industry earlier this year the US Department of Homeland Security released new cybersecurity requirements for critical pipeline owners and operators. The directive is a response to increased critical infrastructure attacks, showcasing the impact that major breaches can have on both a country’s security structure and day-to-day civilian life.
Third and 4th party involvement:
As attacks continue to rise, the severity of incidents and the impact they have on critical US infrastructure has not gone unnoticed. Impactful attacks showcase the ripple effect that successful cyberattacks have across industries, further highlighting the criticality of having a wide scope into your third and fourth parties.
Cybersecurity executive order
President Joe Biden issued an executive order on cybersecurity seeking to improve the state of national cybersecurity in the US and to increase the protection of government networks. The Executive Order outlines the need to modernize cybersecurity defenses in the country as well as opening channels for sharing information relating to cybersecurity threats and breach information. This highlights the importance of organizations ensuring that their supply chain is secure and that their vendors meet the necessary cybersecurity requirements.
Third and 4th party involvement:
The emphasis on cybersecurity doesn’t stop at the internal business level. As incidents occur, global authorities are passing regulations discussing the modernization of attack defense and emerging considerations. Modernizing the defense of your vendor ecosystem as governments push new regulations will ensure your security program stands out as a business differentiator.
How OneTrust can Help with Common and Emerging Cyber Threats
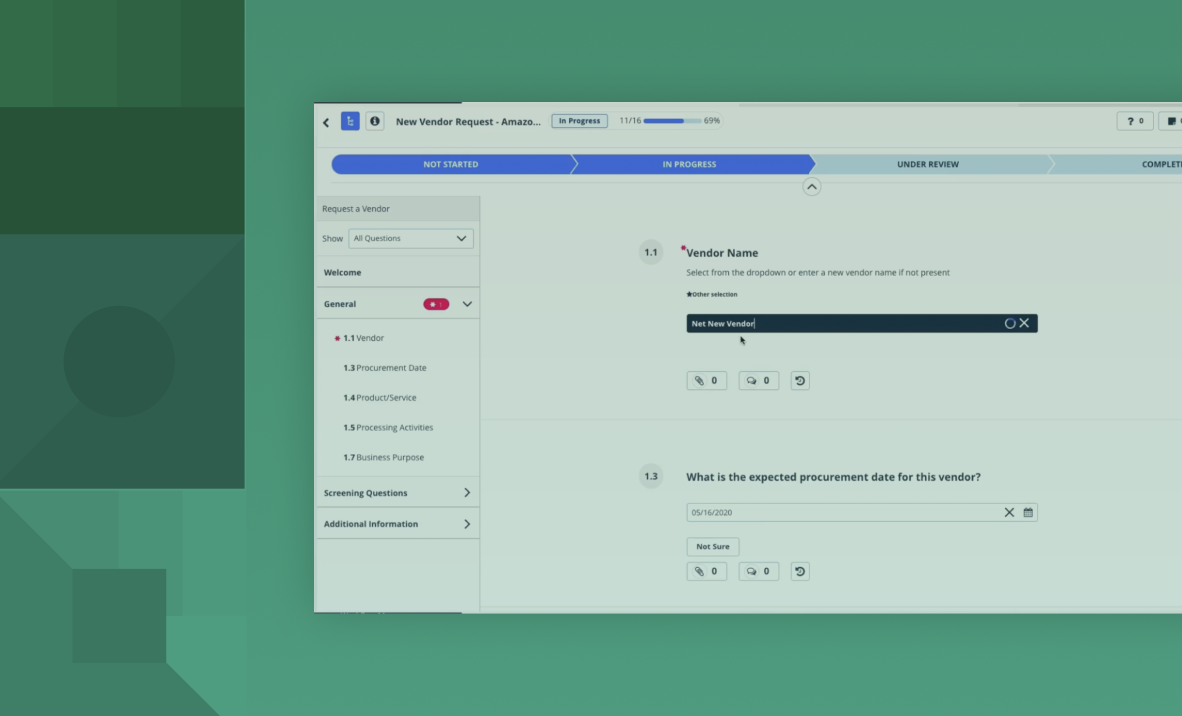
It’s important that cybersecurity teams take a proactive approach to risk mitigation by having a third-party risk management program in place to track and manage the security and compliance of your vendors. In order to address attacks on your third parties, cybersecurity teams need to implement appropriate contractual clauses and agreements to plan on potentional response plans and hold third parties accountable in the presence of a cyber threat. In addition to preemptive planning, it’s critical for organizations to continuously monitor and reassess their third parties as well as the vendors they use (4th parties).
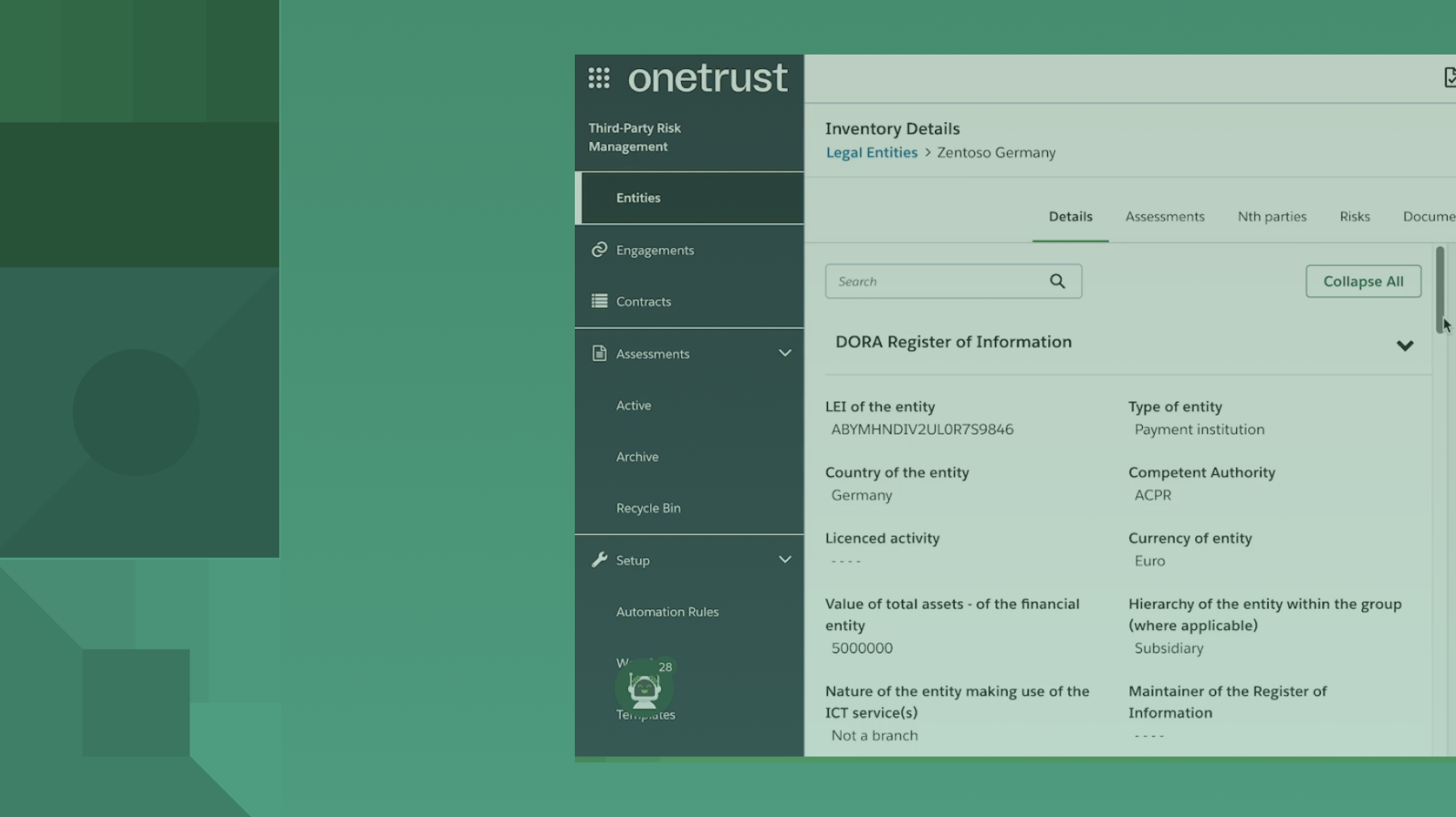
The OneTrust platform leverages expertise in third-party risk management, privacy, GRC, and many other categories to help organizations make trust a competitive advantage.
Specifically, OneTrust Third-Party Risk Management provides a global community where you can access risk analytics and control gap reports on thousands of vendors via their third-party risk exchange, enabling proactive preparedness internally and externally.
OneTrust enables you to gain visibility into all aspects of your organization’s security structure by building your third-party risk management program from the ground up, providing insight into your vendor inventory, vendor lifecycle management, and risk assessments. Request a demo today.