What Is Privacy Management?
Today, your business must maintain compliance with a bevy of local and international legislation aimed at protecting individual data rights. The processes and activities supporting this are grouped into a discipline experts call privacy management.
As the privacy landscape has evolved, so have the key areas to include in a privacy management program. Because this area is so important for businesses that want to increase their clout with customers and protect themselves legally, it’s important to understand the major factors that contribute to a healthy privacy management program.
This Ultimate Guide to Privacy Management does just that. You’ll learn what areas to address, why they’re important, and how to implement specific tactics to support them.
Download The Ultimate Guide to Privacy Management eBook
Lawfulness, Fairness, and Nondiscrimination
A foundational standard for privacy management is being able to prove through records that you have a legal reason for collecting and processing personal data. This is called legal basis and it’s at the forefront of widely-followed privacy legislation, including the GDPR and LGPD.
To achieve legal basis, you must be following at least one of six parameters:
- Performance of a contract: You’re processing data in order to sign or make good on the terms of a contract.
- Compliance with a legal obligation: You’re processing data for legal purposes, e.g. verifying a new employee’s application and background information.
- Protection of vital interests (safety) of individuals: You’re processing data to help someone in an emergency situation, most likely a medical one.
- Performance of a task carried out in the public interest: You’re processing data as a government organization, or as someone who supports one.
- Legitimate interests: You’re processing data without users giving consent for a reason you deem valuable to those users. Complete a Legitimate Interests Assessment (LIA) to demonstrate you’re qualified to use this reason as a legal basis.
- Consent: You’re processing data because users have given you explicit consent to do so. To use this as a legal basis, make sure data collection follows the rules: It must be freely given, specific, informed, and unambiguous.
In addition to legal basis, there are four other qualifiers to follow when it comes to lawfulness, fairness, and nondiscrimination.
- Fairness: Personal data must be processed at the most conservative level of fairness. An example is to make sure privacy settings are easy to access and understand — and they’re set to the most protective by default.
- Protection of minors: Make sure the mechanics and processes are in place to protect the data of minors. One example encouraged by some privacy laws is gaining parental consent beforehand.
- Processing of sensitive data: Set up measures and appropriate levels of special treatment to process sensitive data safely such as racial or ethnic origin, health information, and religious affiliation properly.
- Nondiscrimination: You can’t discriminate against users based on their privacy preferences.
Transparency and Free Access
A modern privacy management program shouldn’t hide anything from its users. Not only is the opposite required by countless privacy laws, but it’s just good business. The most visible way you can create transparency is through a privacy policy.
A privacy policy should live permanently on your website for easy access by visitors. But it should also be stored and accessible by your employees on an intranet or cloud-based system. Create support materials to help your team more efficiently enact the privacy policy:
- Write procedures and playbooks for training and reference.
- Document activity and perform audits to ensure internal compliance.
- Assign a person and/or department responsibility for record-keeping and communicating policy changes.
The submission process for a user to submit individual feedback about a status change to their feedback should also be a part of your privacy policy.
Finally, enable free access — freely providing information about the form and duration of your data processing and integrity. This should be done by showing users a message at the time when you’re collecting their data: What information you’re collecting, using, storing, and transferring.
Download The Ultimate Guide to Privacy Management eBook
Purpose Specification, Use Limitation, and Suitability
It’s not enough you provide a good reason for and valid means of collecting personal data. Privacy management requires purpose specification: You use the data you collect — only and precisely — in the ways you said you would.
To ensure you follow this:
- Document the purpose of collecting data before you start doing it.
- Don’t collect data to have on hand in case you need it in the future. Only collect it to use for specified purpose(s).
In addition, you shouldn’t do more with the data than you said you would. Use limitation holds you accountable not to share data between departments, to minimize exposure to hackers, and to establish secure ID authentication, among other best practices.
You’re also obligated to comply with use suitability. You can’t color outside the lines of what you told data subjects about the processing of their data.
Data Minimization, Storage Limitation, and Accuracy
A privacy management program shouldn’t just focus on the preparation for and collection of personal data. You must also ensure once you collect data, it’s stored and maintained securely. The integrity of a person’s information must stay intact throughout its lifecycle with your company.
Data minimization is the practice of ensuring personal data processing is adequate, relevant, and limited to only what’s necessary. Implement data minimization by:
- Setting up a user interface (UI) that can distinguish between optional and required form fields.
- Using defined fields in a form instead of open text fields.
- Verifying data for adequacy and relevance to a specific purpose, prior to processing.
- Only collecting data needed to achieve a specific purpose.
- Limiting data transferred to what’s minimally necessary.
You also have to follow storage limitation best practices. Personal data must be kept in a way so when it’s no longer necessary to store for your purposes, you can easily delete it. Regularly review your data inventory. Set up triggers to delete data. And erase personal data immediately and securely when users deactivate or delete their accounts.
To keep the personal data you store accurate and updated, set up auditing processes dedicated to this task. Any temporary files created when storing Personal Identifiable Information (PII) must be completely and safely disposed of.
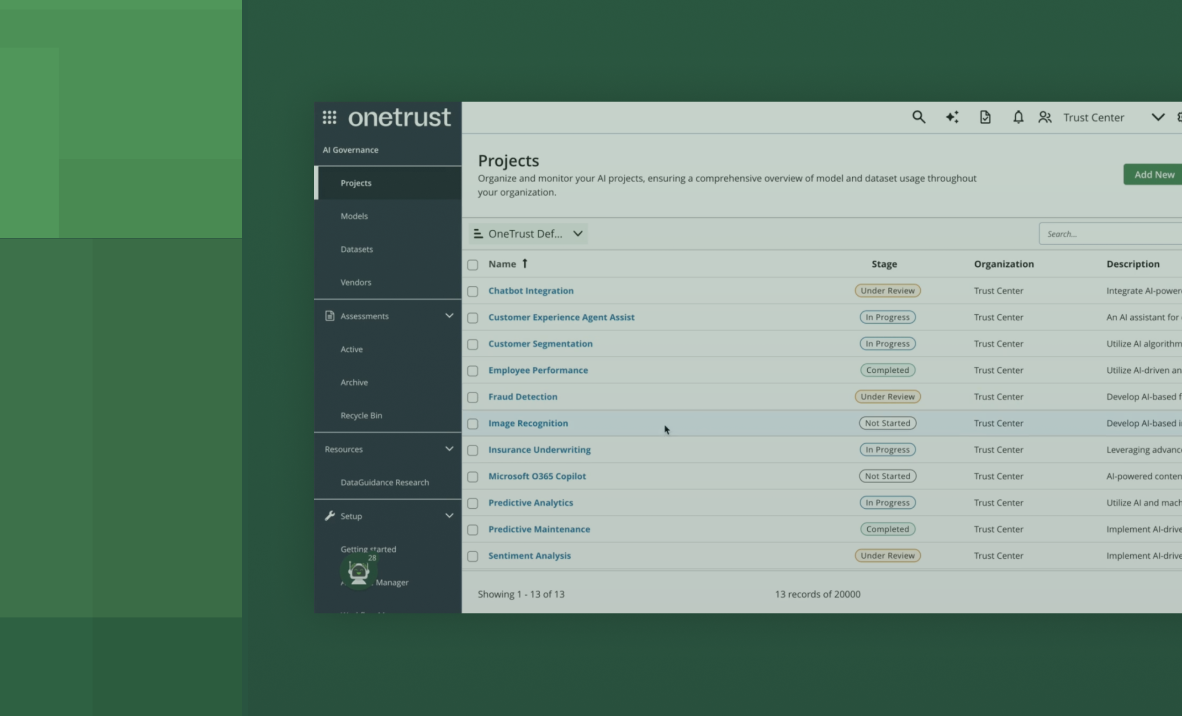
Management System
Executing a long-term privacy management program starts with understanding the legal context behind everything you do. Across the world, governments are releasing privacy legislation. You must be knowledgeable about these legal, regulatory, and contractual requirements in order to implement them.
Start with inventory and mapping. Carefully examine your stored data and how it’s handled. This includes processing activities, data actions, data elements, category of individuals, and data environment.
Doing this will help you understand what privacy framework to follow — such as the NIST Privacy Framework — and how to manage the associated privacy risks. Managing these risks is important. Create reporting functions and privacy controls to keep tabs on them.
Document everything:
- The internal and external factors that are — or have the potential to — affect your company’s privacy.
- The needs and expectations of the interested parties.
- The scope your privacy program needs to cover.
A trusted and capable privacy management platform is critical to success in this area. Onboard a formal and documented privacy and/or security system committed to continuous auditing and improvement.
Security
Privacy and security are different, but related, disciplines. They rely on each other in order to function effectively. For your privacy management program to succeed, make sure you’re following security best practices:
- Keep records of the media that contain personal data.
- Protect any biometric data by storing it outside personal data information systems and inside physical data storage media.
- Appoint an Information Security Officer (ISO).
- Conduct penetration tests and vulnerability assessments of information systems.
- Limit user access privileges on a need-to-know basis.
- Use multi-factor authentication and encryption to block unauthorized access to data.
- Install firewalls, system patches, malware, and virus protection software.
- Implement technical and organizational measures to ensure the continuous integrity, availability and resilience of processing systems, services and data.
Security is vital to the health of your privacy management program. You must get it right. As a way to double check your security processes and controls, you can go through this checklist of questions:
- When selecting your security controls, did you review legal and regulatory factors?
- When selecting your security controls, did you review contractual factors?
- When selecting your security controls, did you review business factors?
- Would you say that your organization has appropriate security controls in place equal to the risk and sensitivity of the data it processes?
Accountability and Recordkeeping
Accountability plays a major role in privacy management. You need to follow stringent practices about collecting, storing, and using data. But you also need to be able to prove it if a regulator were to ask for it.
Records of processing is the first way to establish accountability. Keep detailed records of your organization’s processing activities, data flows, and categories of data subjects. If you don’t have one, create a data map:
- Integrated inventories of personal data
- Processing activities
- Information assets
- Records of third-party disclosures
In addition, consult with your B2B customers before making any legally-binding personal data disclosures to third parties.
You also must have a way to prove you’re registered with the appropriate public authorities for processing activities or to gain approval for certain processing activities. And you have to show exactly who’s completing the activity — for external and internal purposes.
For external verification, you’ll need to determine who’s in charge of the processing of personal data when there’s a joint data controller. Subcontractors also represent an external body that needs to be authorized by customers to process data.
Ongoing and accurate record-keeping is the only way to be ready with sufficient evidence if you’re ever called to account. An amalgam of automated and manual internal reporting and audit mechanisms is essential. Monitor for new laws and regulations in order to update your policies and procedures.
Ensure you have open lines of communication between the privacy office and other departments within the organization.
DPO & Privacy by Design
Because privacy management is such an important part of a modern organization — and it’s such a massive undertaking to implement well — experts recommend assigning dedicated leadership roles committed to seeing it through.
A Data Protection Officer (DPO) is the team member responsible for privacy and data protection. The company should give this individual authority, means, and resources to launch and maintain a privacy program. In addition, the executive team needs to fully support the initiatives and programs this role sets forth.
One of the main tasks of the DPO is to consistently create and maintain team-wide channels of communication about privacy policies and procedures. Privacy champions from each department act as liaisons between the DPO and their specific teams:
- Information security
- Internal audit
- HR
- Vendor management
- Communications
- Business executives
- Product development
- Analytics
- Marketing
The other main task of the DPO is to create strategies — and make sure they’re executed properly — when it comes to the seven principles of Privacy by Design. These principles are:
- Proactive not Reactive; Preventative not Remedial
- Privacy as the Default
- Privacy Embedded into Design
- Full Functionality — Positive-Sum, not Zero-Sum
- End-to-End Security — Lifecycle Protection
- Visibility and Transparency
- Respect for User Privacy
Privacy Impact Assessments
Some privacy laws require privacy impact assessments (PIAs): You’re responsible for identifying risks associated with processing activities. Other privacy standards require PIAs to include different content. General must-haves include:
- The information to be collected (nature and source)
- Why the information is being collected
- The intended use of the information
- With whom the information will be shared
The result of creating a PIA is to understand risk. A risk treatment plan can help you assess and document the results of your PIAs. From these, you’ll better understand how to take action to decrease the risks you’ve identified.
If you’ve discovered high residual risks, it’s in your best interest to seek advice and approval from data protection authorities before continuing to process data. Some privacy laws even require it. When it comes to protecting personal data, it’s always better to be safe than sorry.
Data Subject Rights
Providing data rights to users is at the center of almost every international piece of privacy legislation. In other words, you must have a process and support mechanisms in place to address requests from individuals about their data.
It starts with a clear and conspicuous notice to data subjects telling them what rights they have and how to exercise them. There must be an easy way for them to submit requests. And your team should be prepared to handle them. Internal policies, procedures, and training on how to handle data subject requests are a must.
Data subjects rights fall into 10 areas:
- Right to be informed
- Right to withdraw or modify
- Right of access
- Right to rectification
- Right to be forgotten/erasure
- Right to restriction
- Right to security freeze
- Right to data portability
- Right to object
- Right to opt out of sale of data
If your company automates some decisions about user data, you have to provide a way for users to request a manual review of those automations. Likewise, any changes to a user’s data made via a data subjects rights request has to also be changed by any third parties with whom it’s shared.
Create open lines of communication to inform these entities about modification, withdrawal, or objection about personal data.
Vendor Management
It’s not uncommon for companies to outsource to third parties for a variety of services. If you use vendors, though, it’s your responsibility to ensure they’re following your privacy management policies. You’ll have to establish processes and supporting technology to dot your i’s and cross your t’s.
Contracts are key to effective vendor management. They should closely reflect your own privacy standards. A compliance checklist can help here. It provides a rundown of general privacy must-haves — such as a vendor privacy impact assessment — married with policies unique to your organization. You must tick off every box on this checklist in order to onboard a new vendor.
Vendor assessments are essential to monitor ongoing compliance. Double check all your processes to ensure they sufficiently cover technical and organizational measures — and that vendors are following them.
Cross-border Data Transfer and Data Localization
Whether you receive or send personal data outside the country in which you do business, privacy management requires you to track that activity. These cross-border data transfers have to be completed via lawful mechanisms such as binding corporate rules (BRC), standard contractual clauses, or consent of the data subject.
It’s important to understand the Schrems II Decision shut down the long-standing Privacy Shield EU-US personal data transfer mechanism. And although SCCs are allowed as a data transfer mechanism, they are only accepted on a case-by-case basis.
In addition to the responsibility of cross-border data transfers, some laws state personal data of citizens or residents of the geographic location addressed by the law be processed or stored within a specific country. Adhere closely to these data localization requirements.
Incident and Breach
You never want to face the situation when the personal data you store is compromised. Part of privacy management is preparing thoroughly for incidents and breaches in case they do happen.
- Establish reporting procedures to quickly and completely track incidents or weaknesses as soon as they’re detected.
- Document steps for finding out exactly what caused the event.
- Identify, collect, and preserve the information related to the incident and keep it as evidence.
- Create a checklist of remedial measures for correcting the effects of the incident.
Many privacy regulations require organizations to track incidents and breaches. You should make this a best practice to cover yourself legally.
Training your team on incident response processes and procedures will help them feel prepared for these events. Assign responsibilities to managers and their teams. When everyone knows what their jobs are, responses to breaches and incidents will be quicker.
Notifying affected parties is a core activity after a breach. Prepare notification messages in advance for fast delivery and clear communication to those affected, authorities, and data controllers.
Finally, hold a post-mortem. This post-security incident analysis should cover what the team learned, what updates or recurring negative patterns you need to address, and any other communication you need to send, if any.
Conclusion: Build Trust With Your Privacy Management Program
Including these 13 areas in your privacy management program won’t just ensure you’re following local and international privacy standards. They’ll additionally give you a competitive advantage, no matter what industry you’re in.
In fact, when you build around these principles — treating it as a living program to be continuously improved — customers will naturally trust the transparency and obvious care you take with their information. When users are becoming increasingly wary of business practices, gaining hard-won trust can help your business face the future with confidence.
A privacy management platform can help you foster trust with customers at scale. Automating the most important and time-consuming tasks, this software helps you deliver on your privacy promises to users — on time, every time. OneTrust Privacy Management software is designed to do just that. Reach out to schedule a demo or start your free trial today.