Simplify compliance, improve operational efficiency, and enable risk-informed decisions.
Privacy Operations
Simplify Privacy Compliance
Operationalize privacy program activities to manage risk, demonstrate accountability, and meet regulatory requirements.
Connect to data assets to detect personal data, automate recordkeeping, monitor risk posture, and trigger remediation.

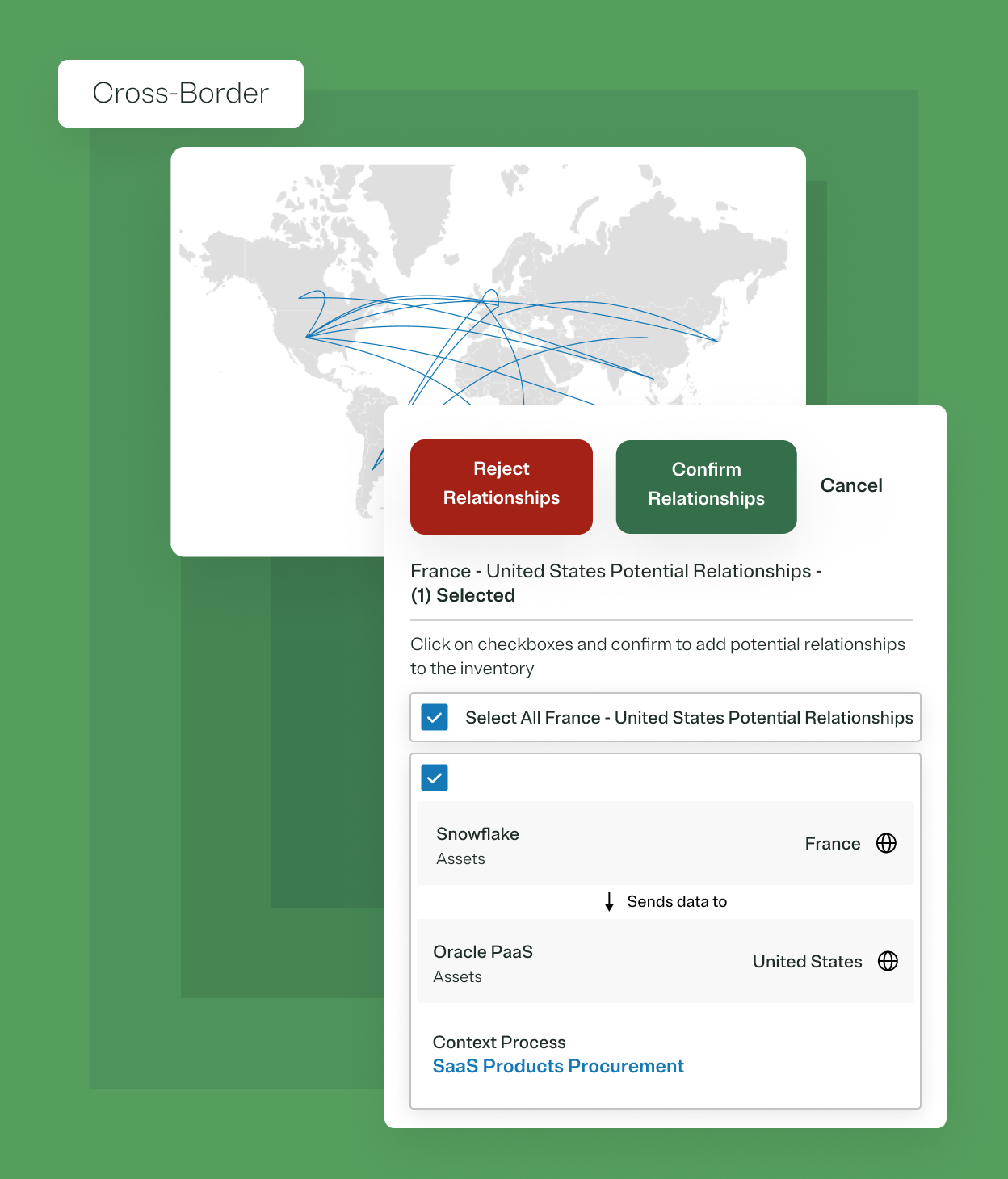
Get a central view into your personal data processing across your data assets, processing activities, and vendors to auto-generate record of processing activities (RoPA), identify data transfers, and manage privacy posture.

Automate privacy impact, vendor, and AI risk assessments (PIA, DPIA, TIA, etc.) and manage risk mitigation workflows.

Manage incident response workflows and get automated notification guidance per jurisdiction.

Pre-populate notice sections with real-time OneTrust data (e.g. cookie table) and easily publish updates across multiple websites and apps.

Do More With OneTrust Privacy Automation

“OneTrust exponentially grew my team's bandwidth. I'd estimate that we're now operating as if we had four to five more people than we do.”
Director of Digital Trust, Pharmaceuticals
Source: Forrester Total Economic Impact™ study




