Tensions between employee and employer can be commonplace at any company. And there are many scenarios that can lead to these tensions becoming more than just conversations of dissatisfaction by the water cooler.
Employees are becoming more aware of their rights, and both the GDPR and CPRA explicitly provide employees with the right to know what data the employer has and understand how the employer is using their data. As such, requests to access personal information held by employers are on the rise. And while avoiding employment tensions are often unavoidable, being prepared for access requests is not.
Let’s take a look into some of the top reasons why employees might turn to requesting access to their data and how employers can prepare for when they do.
Top Reasons Employees Submit Access Requests
In truth, there is a multitude of reasons why an employee might request access to their personal information, but some of these reasons may be less obvious than others. Circumstances that may lead to an employee requesting access to their personal information include:
- A dispute with their employer
- An employee not receiving an expected pay raise or promotion
- Cases of harassment and/or discrimination
- An unsuccessful job application
- A general understanding of their rights/curiosity
- Rumors relating to acquisitions, mergers, IPOs etc.
- Events that lead to press coverage
On the surface, it may seem as though employee access requests are just the same as consumer DSARs. However, instances of employee access requests include access to personal information, inquiries on how their data was collected, and names of third parties their information is shared with, among other things. The challenge here is that employee data is often commingled with the personal information of others and large quantities of personal data are stored in unstructured data sources such as emails and PDFs. Not to mention that employee requests will often come out of the blue. Therefore, organizations should be prepared and have the systems, processes, and tools in place as the next employee access request might be just around the corner.
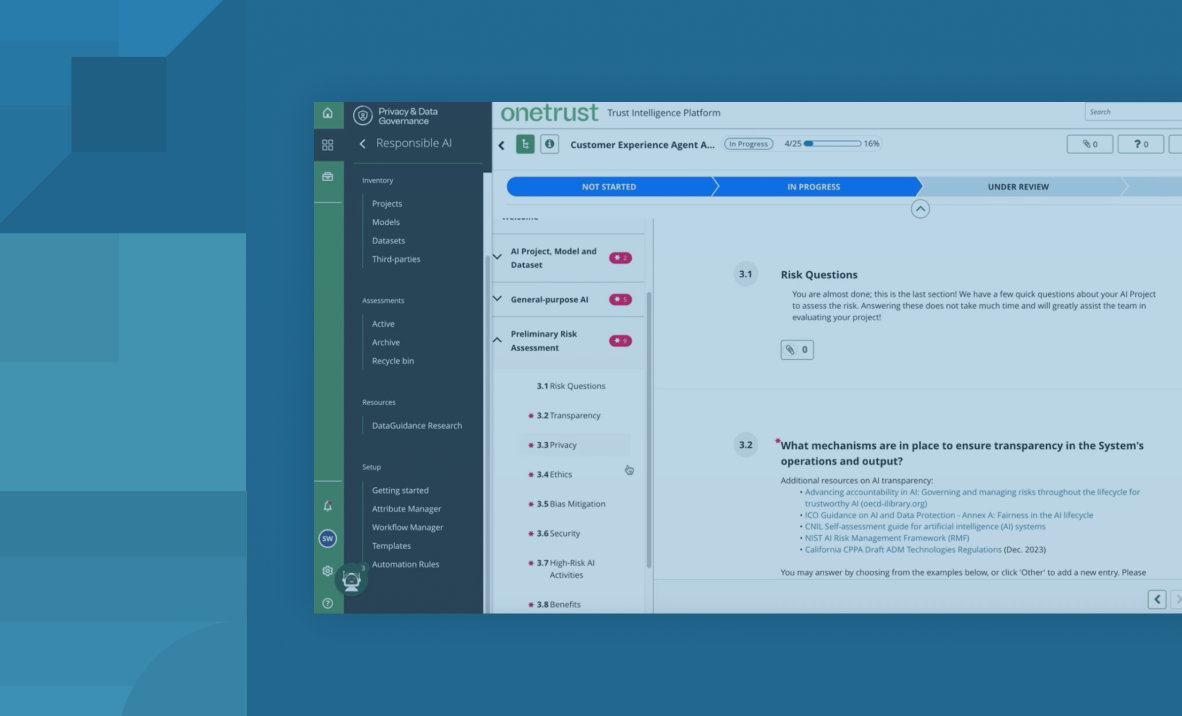
How You Should Prepare for an Employee Access Request
Intake
The first thing to consider when preparing for employee access requests is ensuring you have easily accessible intake methods embedded into websites and/or employee portals.
Verification
You will need to verify the identity of the requestor before you can proceed with the request. Therefore, organizations should implement methods for attaching proof of identity to the initial request and cross-validate this evidence with the employee database.
Discovery
When you have set the groundwork for receiving employee access requests, the next step is to employ data discovery processes to help find personal information related to the requestor. This is where the unique complexities of employee access requests rear their heads. Large quantities of employees’ personal information will be found within unstructured data sources. However, manually combing through email archives and chat logs will be time-consuming, if not impossible to complete efficiently and accurately.
Organizations should then look to catalog this data in a centralized inventory. A comprehensive, up-to-date data inventory should act as the foundation for access requests, help organizations to understand what laws apply to personal information, and help prevent duplicate or repetitive requests.
Redaction
Having automated redaction solutions in place is the next step organizations can take in preparation for employee access requests. Discovery tools will help you find all the information your organization holds on the requestor. But remember that their data will almost certainly be intertwined with the personal information of other employees and proprietary business information; both of which should not be disclosed to the requestor. Automated redaction can find instances of commingled and sensitive information and remove them from the final documents ready for review before fulfilling the request.
Fulfillment
Finally, organizations should ensure they have a secure method of sharing the final, reviewed documents with the requestor via an encrypted or secure messaging portal.
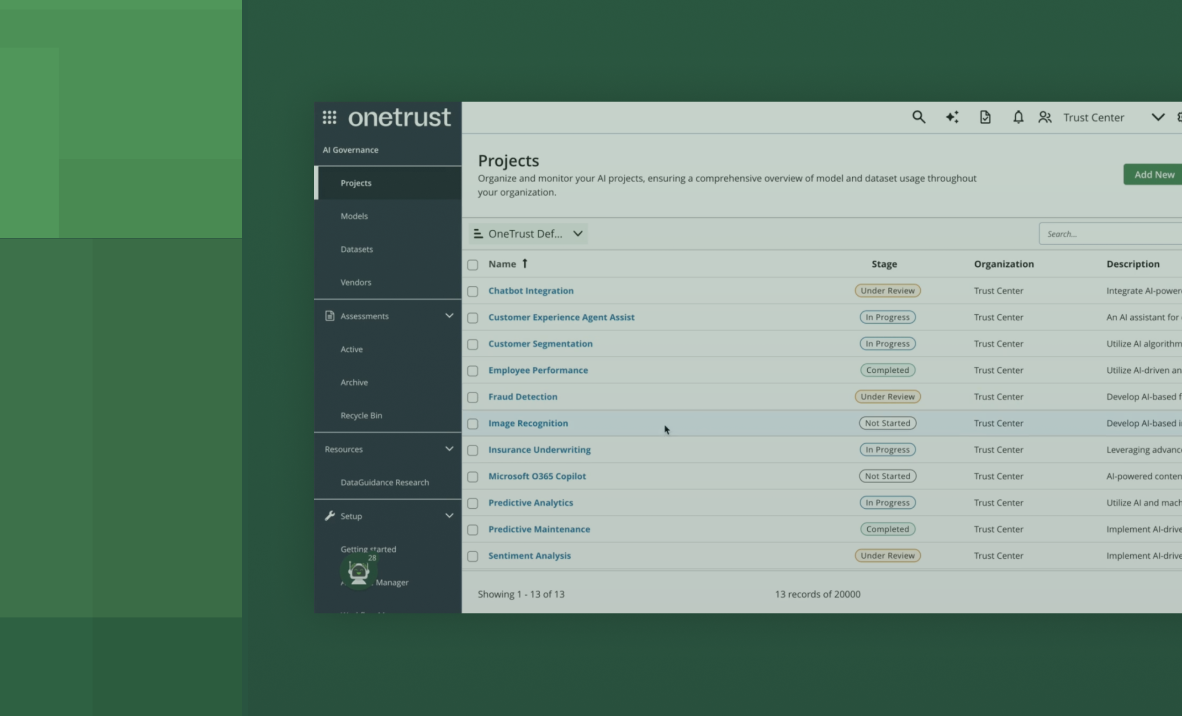
Request a demo to talk to our experts about how OneTrust can automate the employee access request process through a suite of AI and ML-backed solutions.