As data privacy legislation has expanded in recent years, so has the scope of the privacy programs that support it.
Though regulation has been and still is one of the top drivers for privacy programs, the days of “tick-the-box” compliance alone are no more. As the lines continue to blur between privacy, security, and data governance, privacy teams have shifted focus beyond just their obligations for regulatory compliance and reporting to embedding governance more strategically into the data lifecycle within the business. This comes as a result of the quickly evolving regulatory landscape, but also the pace at which data use occurs and evolves as well as the technologies that support it.
This presents challenges for privacy teams to be able to adapt continuously to these regulatory and data environments. One of the most significant of these challenges is the ability to easily find, understand, and protect data.
Data lives in many digital and analog locations — and in many formats — in most organizations today. This translates into manual, time-consuming, and often disjointed compliance and governance processes.
Without a way to find and populate data in a centralized location, privacy teams’ hands are tied. They can’t create effective governance policies or collaborate with internal stakeholders to meet compliance standards. Addressing this problem should be a privacy team’s priority.
The place to start is with automation. It allows teams to integrate all their systems, discover and classify data, and create a central data inventory. From there, privacy teams can address broader aspects of their privacy programs such as data subject access requests (DSARs), incident management, and privacy impact assessments (PIAs), among other things.
Step 1: Know Your Data
A central view into the personal data held and processed by an organization, often called a “Data Map”, serves as the foundation of any privacy program and has been since organizations began preparing for the EU General Data Protection Regulation (GDPR). What has changed is that many organizations now realize that in order to have a more accurate, up-to-date data map manual steps must be replaced with automation.
Data discovery is the answer. It uses automation to scan multiple systems, data sources, and data assets. It locates the personal data stored within those systems and classifies it, and leverages scheduled incremental scans to identify changes as they occur.
The result of an organized data discovery process is a data map. Data mapping creates central inventories and a visual representation of the entire data lifecycle that Privacy teams can leverage knowing they have a near-real-time view into their data. They can also easily identify gaps in their data, security, and compliance processes and remediate policy violations to reduce risk. If you don’t know about the data, how can you effectively protect it?
With data discovery and data mapping in place, a privacy team has a central inventory of data that they can use to make decisions and take action no matter what area they’re addressing including privacy management, consent management, or data security. A data map can also help privacy teams to understand what data privacy laws, such as the California Consumer Privacy Act (CCPA), apply to their data.
Step 2: Data Privacy Automation
Once a privacy team has standardized data discovery and data mapping, they can tackle other areas of their privacy program, such as data subject rights, with ease.
DSARs are increasing in volume and complexity. They require privacy teams to locate, collect, and redact sensitive data quickly. With data discovery and data maps in place, a privacy team understands exactly where they store an individual’s data. They can target that data, automatically perform redaction, and deliver it to the DSAR requester in a timely manner.
Another area data discovery supports is incident management. Addressing risks and incidents becomes less of a burden for the security team because they can now easily access the data they need for remediation.
Data discovery automation also sets the stage for next-generation privacy and data governance efforts such as privacy policy management. Since privacy teams can easily access data, they can track beyond who’s received and acknowledged privacy policies, but begin to detect violations of those policies, remediate issues, and reduce overall risk.
Conclusion: Go Beyond Manual Workflows to a Fully Automated Platform
More and more privacy regulations are in the works or being passed every month. These, and existing data protection and privacy laws, are increasing in complexity, too. Add this to the continuous expansion and importance of data use within organizations, and the new technologies they are leveraging to do this, and Privacy teams have their work cut out for them.
Privacy teams need technology that goes beyond just workflow to help automate tasks that traditionally have taken time and effort only to deliver inaccurate information. This technology enables Privacy programs to become more embedded into the technologies used by the business, instead of just bolted on, to further streamline organizations’ privacy, security, and data governance initiatives.
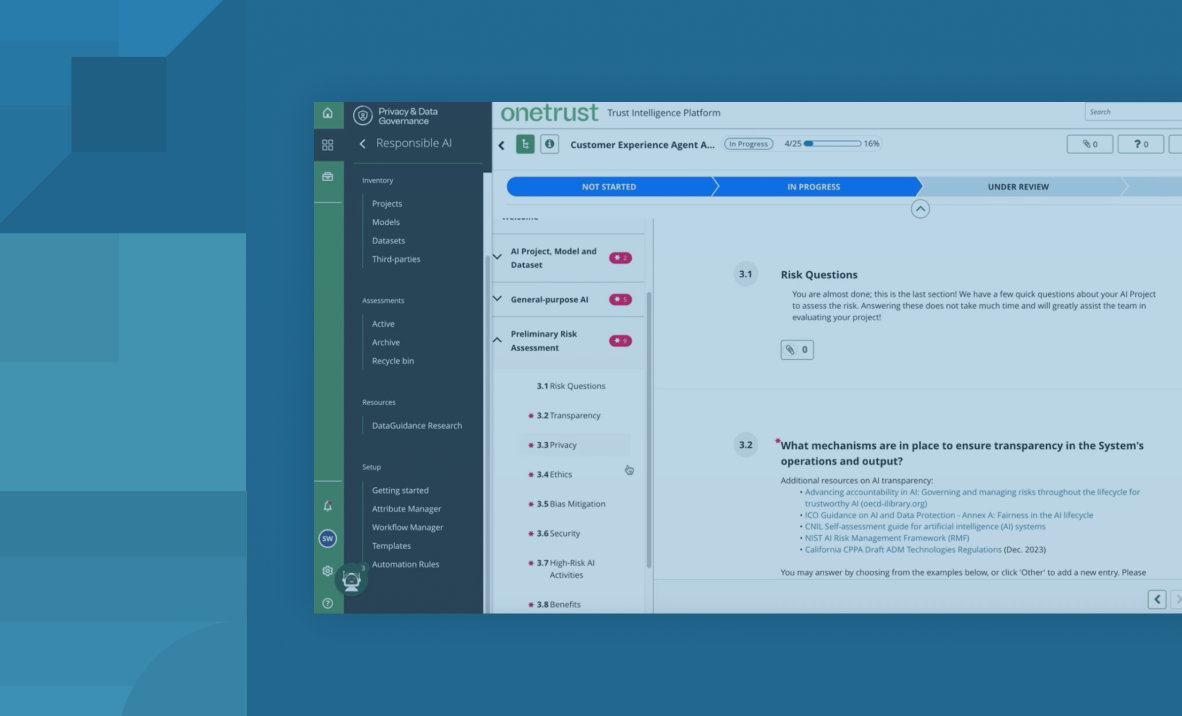
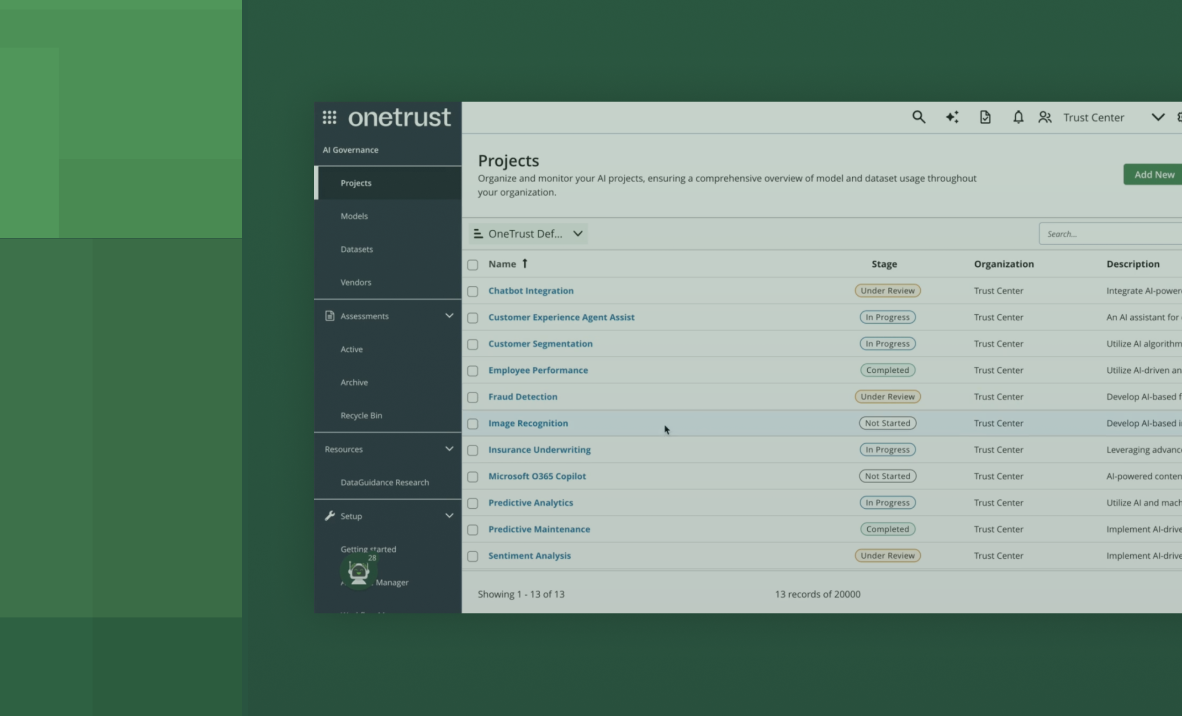
OneTrust’s software is designed to integrate privacy automation from start to finish, including:
- Discovery & classification of personal data across the IT ecosystem, applying both business and regulatory contexts through OneTrust DataGuidance research.
- The population of a central data inventory & catalog to serve as the foundation of privacy, security & data governance initiatives.
- Powering of privacy workflows, such as records of processing creation, incident response, and automated fulfillment of DSARs.
- Enforcement of policies such as data retention, data minimization, and data access by applying controls such as redaction, deletion, and access governance across the IT ecosystem.
With these tools in place, privacy teams can make more informed decisions and automate downstream privacy and governance processes, and simplify privacy compliance and risk management efforts. In addition, they’re easy to use, so everyone on the team can leverage them to increase the efficiency and effectiveness of their day-to-day tasks.
See how OneTrust can help. Request a demo today!