In the face of increased ransomware and overall security incidents, weaving the fabric of trust throughout your organization is an opportunity for business differentiation. While the intricacies of each sector and business may vary, one thing reigns true: trust talks, and is key in empowering efficient workflow in every business dynamic.
So, where should you begin? The answer lies in establishing a trust-based cybersecurity program.
Security is often siloed. To have a truly holistic program your organization needs to approach its internal and supply chain security from a singular standpoint: trust. Facilitating a trustful security posture empowers your organization to align privacy, third-party risk management (TPRM), governance, risk, and compliance (GRC); and environment, social, and governance (ESG) business needs collectively.
Trust can be created and championed by the security team. Learn how to build trust and drive growth with this eBook.
What Is Trust-based Cybersecurity?
In the wake of increased successful and high-profile attacks, ransomware incidents, and the newfound fragility of critical infrastructure systems, areas like GRC and TPRM are emerging as undeniably necessary components of instilling trust throughout enterprises. This includes a shift in focus to the importance of the individual and requires each of these areas to align with the pillars of an organization’s risk posture: security, compliance, and privacy.
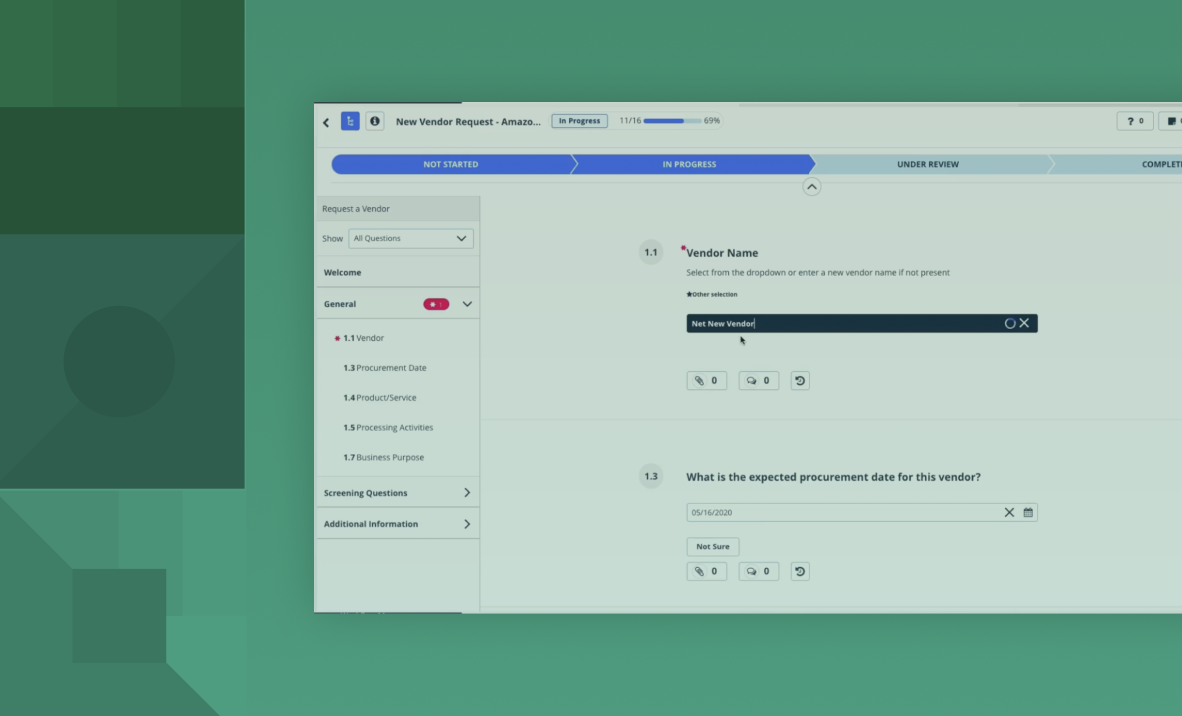
Establishing trust-based cybersecurity means organizations must conduct thorough due diligence. This includes everything from identifying key assets and weaknesses in your security posture to understanding threats to your vendor ecosystem. This strategy will empower individual stakeholders to implement risk-based security measures into their day-to-day processes.
The Silos of Trust and Their Interplay
Siloed business units are not as effective as cross-team collaboration; each area must work collaboratively to facilitate organizational trust. This aligns goals and duties, allowing each facet of an organization to work toward a common goal, giving an organization the autonomy to proactively tackle industry-related issues and showcase dedication to its stakeholders. Business leaders working to build a trust-based organization should emphasize collaboration across the following business units:
- Governance, Risk, Compliance (GRC): GRC enables organizations to analyze risk, scale compliance, and reinforce governance while identifying, tracking, remediating, and monitoring risk across its operations and IT infrastructure.
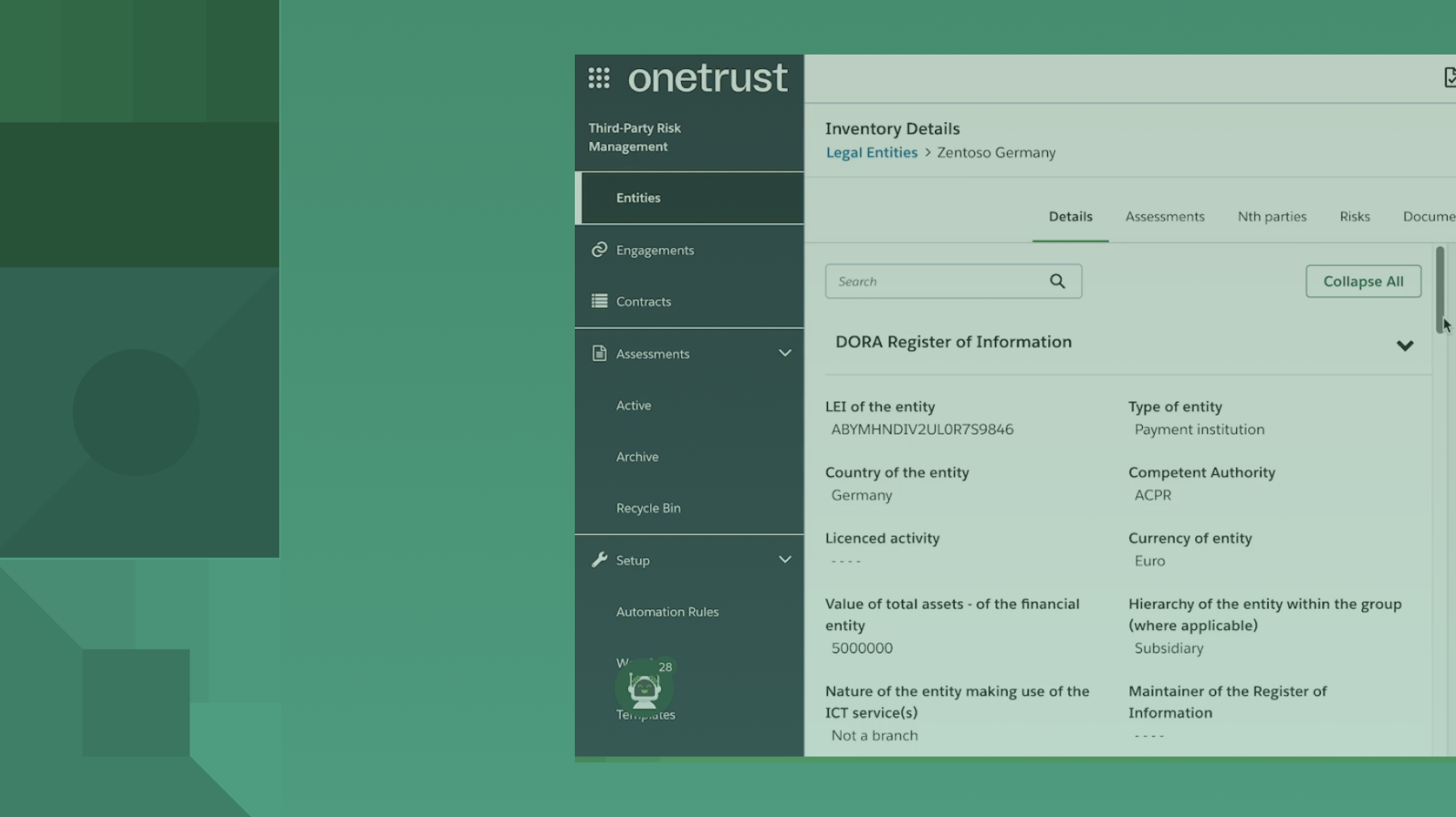
- Third-Party Risk Management (TPRM): TPRM serves to enable visibility into all aspects of an organization’s security structure from the ground up, giving insight into vendor inventory, lifecycle, and risk.
- Environmental, Social, and Governance (ESG) and Ethics: ESG and Ethics programs are emerging as key components of cross-organizational strategy. This includes comprehensive monitoring of environmental and social impact, reporting on and reducing emissions, contributing to the creation of environmental regulations, and implementing holistic diversity, ethics, and inclusion training throughout all levels of the business.
- Consent and Preference Management: Consent and preference management allow organizations to prioritize choice and transparency in the user experience across web, mobile, and CTV platforms through the application of a privacy-first approach.
- Privacy and Data Governance: Privacy and Data Governance allow organizations to prioritize appropriate data gathering, usage, and storage practices while staying aligned to industry-relevant regulations.
Overall, it’s key that business units collaborate to address the growing challenge of protecting organizational and consumer data by strengthening trust through each of these workflows.
Third-party relationships to your business are necessary but pose plenty of risks. Understand more in this research report and download here.
Trust As a Competitive Advantage and Key Business Differentiator
Enabling your organization to stand up a trust-based cybersecurity model will allow you to provide a seamless, trust-centered experience both internally and externally. Additional benefits include:
- Fiscal savings: Trust enables your organization to align and work smarter, not harder. Integrating trust and transparency into the internal and external user experience by looking at trust from the bottom-up, and opens this opportunity.
- Increased brand reputation: Fiscal savings enables your business to work smarter, lessening lift across the enterprise while maintaining a seamless user experience. This improves customer-facing processes and increases brand reputation in the marketplace as trust becomes a key buying decision for global users.
- Consistent compliance: By and large, standing up a holistic solution will allow your company to prioritize regulatory compliance in a way that’s streamlined for the entire organization establishing trust from the inside out.
Why Cybersecurity Awareness Month Matters to OneTrust
OneTrust has a commitment to trust that begins and ends with privacy, security, sustainability, and ethics. We strive to not only comply and implement best practices but to stay one step ahead, pioneering the future of trust as technology continues to evolve.
Learn more about OneTrust and our unique ability to keep your organization secure. Request a demo today.