Outsourcing key business functions to third parties is – and will remain – a monumental shift in the way companies operate. This has been accelerated by the transition to remote work and will remain an important shift to address. As a result, more vendor risk assessments are conducted. Paired with increasing security, privacy, and regulatory concerns, the number of questions posed also rises.
But the challenges don’t stop there. Once a vendor risk assessment is completed, it must be reviewed to identify risks, understand an organization’s controls, and ultimately, determine if working with the vendor is worth the risk. This is an enormous and time-consuming task that often lacks automation and leaves employees focusing on busy work instead of executing on strategic initiatives.
Shouldn’t these assessment reviews just be done automatically?
From Questions and Answers to Automated Risk Analytics and Control Gap Analysis
While evidence of risk assessments is critical to compliance, oftentimes those assessments are stored away and never actioned. Security, privacy, ethics, and ESG teams, as well as other key executives, have little visibility into what matters most: How much risk does this vendor pose to your business? What security controls are they missing? What does a vendor need to do to help protect your organization?
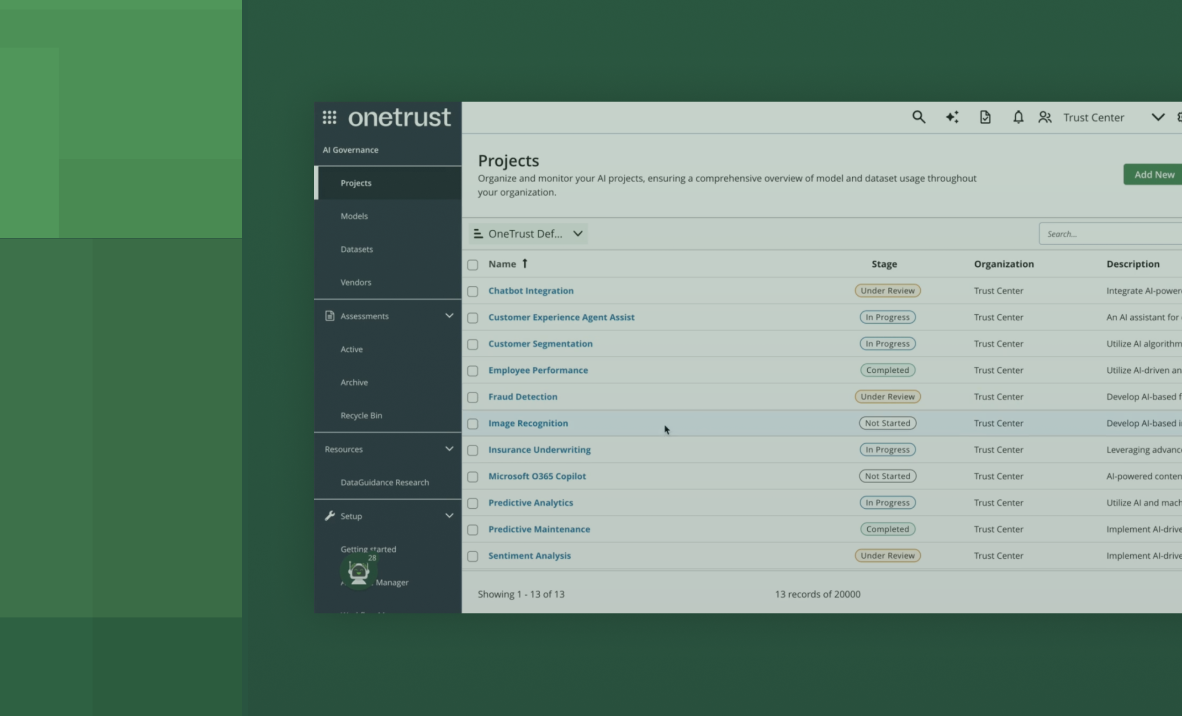
With the Third-Party Risk Exchange, we take a “output-focused” approach to assessments. We don’t just tell you how a vendor answered a question, we show you why it matters. This is the fundamental difference between traditional assessments and our automated risk analytics and control gap reports.
With the Exchange, your company will have access to thousands of these reports. No longer will your team spend time handling the back-and-forth monotony of conducting an assessment. Instead, you simply make a request, and pending approval from the vendor, receive a slice-and-dice view of critical information across 18 risk domains and key industry standards, frameworks, and regulations.
How It Works
When a vendor joins the Exchange, they provide information about their organization’s security controls only once. Then, the next time they receive a request, they simply review and approve. It’s that easy. Vendors can edit their information at any time and automatically push updates to their customers to show security improvements over time. Additionally, vendors can create Trust Profiles to proactively share security, privacy, and compliance information with their customers through a secure portal.
Solving Third-party Risk, Together
To reduce the burden of custom questionnaires, the Exchange has standardized on the Shared Assessments SIG Lite, which maps to dozens of industry standards, frameworks, and laws. As a result, vendors provide security control information just once, and Exchange customers can view the results in the context of the standard, framework, or law most applicable to them.
With our community-based approach, the Exchange is bringing together thousands of companies and third-party risk professionals to seamlessly share information without having to answer endless assessments. While the Exchange has grown organically and exponentially over the last two years, we continue to bring more vendors into the fold. So, if you’d like to help move the world away from custom questionnaires, then you’re in the right place. Join the Exchange today!