In an era where data privacy is paramount, organizations must prioritize the protection of personal information and Privacy by Design offers a proactive approach that embeds privacy considerations into the design and development of systems, products, and processes from the outset. By implementing Privacy by Design, organizations can ensure privacy protections are an integral part of their operations, rather than an afterthought.
The concept of Privacy by Design should be familiar to most privacy professionals. After all, the idea of Privacy by Design has been knocking around for nearly three decades and it has been included as a requirement in most modern privacy laws. And, while you might be familiar with Privacy by Design’s principles or what Privacy by Design should look like, understanding the practical steps for implementing it can be a different story. Adopting effective strategies will empower organizations to safeguard user privacy, comply with regulations, and build trust with their customers. In this article, we will explore the concept of Privacy by Design, its significance, and provide guidance on best practices for its successful implementation.
What Is Privacy by Design
Former Information and Privacy Commissioner of Ontario, Dr. Ann Cavoukian developed the idea of Privacy by Design framework in 1996 and based it upon a set of seven principles. Privacy by Design promotes embedding privacy considerations and protections into the design and architecture of systems and products from the outset of a project with a central aim to ensure that privacy is integrated into every stage of product development, rather than being an afterthought or add-on. It is a proactive approach that organizations should be taking - and in some cases are required to be taking - to protect personal information.
What Is Privacy by Default?
Privacy by Default is a concept related to Privacy by Design that requires organizations to make privacy the default setting and that only the personal information necessary for the purpose is being collected in any new product or service. This means that individuals should not have to take any action for their privacy to be protected.
What Are the 7 Principles of Privacy by Design?
When the concept of Privacy by Design was first developed, it was based upon seven foundational principles. These seven principles still hold true today and must underpin every organization’s approach to Privacy by Design.
The seven foundational principles of Privacy by Design are:
- Proactive not Reactive; Preventative not Remedial
- Privacy as the Default Setting
- Privacy Embedded into Design
- Full Functionality — Positive-Sum, not Zero-Sum
- End-to-End Security — Lifecycle Protection
- Visibility and Transparency – Keep it Open
- Respect for User Privacy – Keep it User-Centric
Why Is Privacy by Design Important?
The importance of Privacy by Design is obvious from a privacy perspective and its the benefits are far reaching. Organizations that implement strong Privacy by Design processes can prevent, or reduce the severity of data breaches, improve data security, transparency, and user control, and encourage teams to consider the ethical and social implications of data collection and use.
Here are five reasons why Privacy by Design is important:
- Data protection: By integrating privacy measures into the design process, organizations can enhance the security and protection of individuals' personal information, reducing the risk of data breaches, identity theft, and unauthorized access.
- Trust and user confidence: Privacy by Design helps build trust and confidence among users. When individuals know that their privacy is respected and protected, they are more likely to engage with products and services, share information, and maintain a positive relationship with the organization.
- Legal compliance: Privacy by Design requirements – or Data Protection by Design – can be found under various privacy laws and regulations, such as the General Data Protection Regulation (GDPR). By adopting Privacy by Design, organizations can meet their legal requirements and avoid penalties or legal issues related to privacy violations.
- Ethical considerations: Privacy by Design encourages organizations to think beyond legal compliance and consider the ethical implications of data collection and use. It promotes responsible and ethical practices, fostering a culture of privacy and data protection.
- Cost efficiency: Incorporating privacy protections into the design phase is generally more cost-effective than retrofitting privacy measures into existing systems. By considering privacy from the outset, organizations can avoid costly redesigns and mitigate potential privacy risks.
How to Implement Privacy by Design
When should privacy by design by implemented?
By its very nature, Privacy by Design should be incorporated into the design stages of any new project that uses personal information. While it is vital that Privacy by Design is first considered at the outset of a new project, it must also continue throughout the entire development process. In the initial planning stages privacy risks and requirements should be identified and strategies for addressing them should be developed. While designing system architecture you should ask yourself:
- What data is being collected
- How and where will it be storage
- How will it be processed
- Who will have access and what controls are in place to limited unauthorized access
- How does this data flow internally and in relation to third parties
Once this has been established privacy-enhancing technologies can be implemented to minimize the privacy risks associated with each response.
Privacy needs to be considered into the end-user experience too, this means drawing up clear, accessible, and understandable privacy notices, conspicuous consent management that does not mislead the user, and privacy-first settings should be presented to users to enable them to make informed choices about their personal information.
Considerations for the entire product design lifecycle
While there are specific privacy considerations that apply in different stages of the product design lifecycle, there are some that must be considered at every stage. Take the principle of data minimization for instance. When followed, it ensures that only the necessary data is collected in the first place and that it is governed by rules that mean it is only retained for as long as necessary and destroyed once it has fulfilled its original purpose. Another example is implementing robust security measures. It is necessary to consider this at several points through the design lifecycle to protect personal information from unauthorized access, breaches, and other threats. Encryption, access controls, authentication mechanisms, and regular security audits should be part of the ongoing implementation.
Finally, the measures implemented through Privacy by Design considerations should be continually tested and evaluated to ensure that they are being respected in practice. Privacy impact assessments, usability testing, and security audits can help identify any privacy issues or vulnerabilities that need to be addressed before deployment. It is important to note that while implementing Privacy by Design from the beginning is ideal, it is never too late to adopt privacy-enhancing measures. Even if a system or product is already in use, efforts can still be made to enhance privacy protections and mitigate privacy risks. However, retrofitting privacy measures into existing systems may be more challenging and costly compared to incorporating them from the outset.
Best practices for implementing Privacy by Design
Implementing Privacy by Design involves adhering to best practices that ensure the effective integration of privacy considerations into the design and development process. Here are some key best practices to follow:
- Incorporate privacy considerations from the very beginning
- Adopt a Privacy-First Mindset
- Make privacy a priority and consider it as a fundamental requirement
- Designate privacy champions within your organization
- Design capabilities allowing individuals to exercise their rights seamlessly
- Provide privacy training to relevant stakeholders
- Conduct Privacy Impact Assessments to identify potential privacy risks
- Collect and retain only the minimum amount of personal information needed
- Utilize privacy-enhancing technologies
- Implement regular, clear checkpoints to communicate how data is handled
- Conduct regular privacy audits and monitoring
By following these best practices, organizations can effectively implement Privacy by Design principles and protect individuals' privacy rights throughout the lifecycle of their systems, products, or processes.
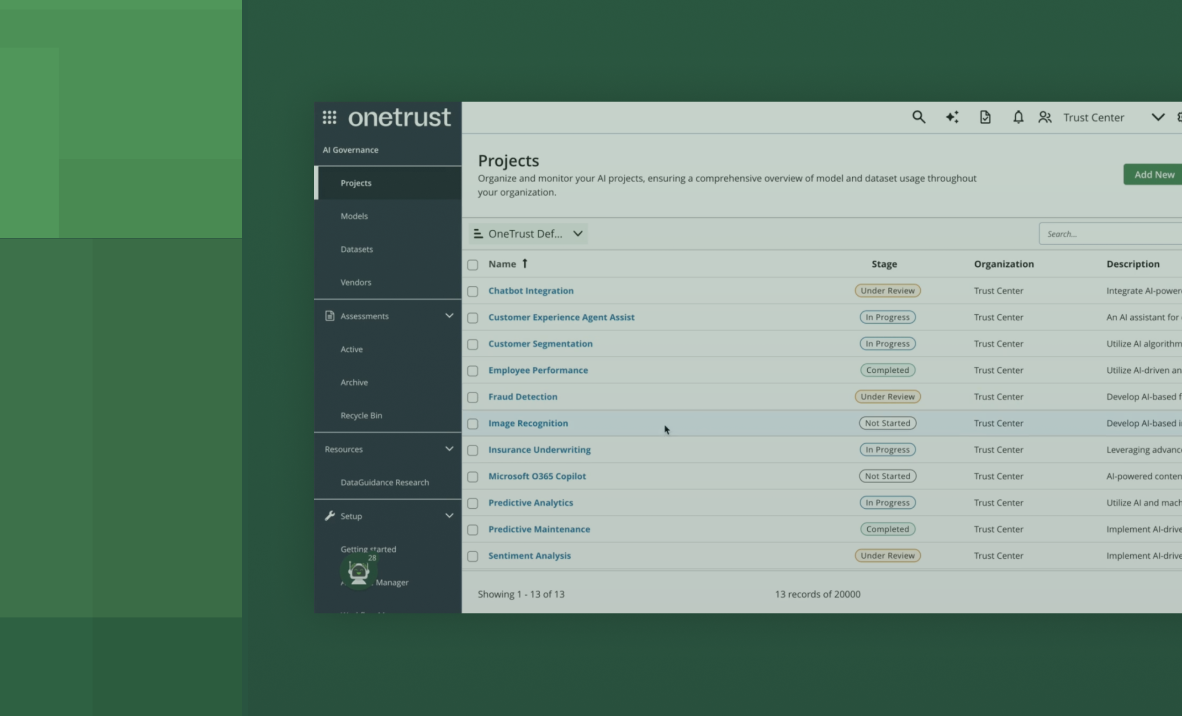
Can OneTrust Help You Implement Privacy by Design?
Privacy software can play a crucial role in supporting Privacy by Design principles by providing tools, technologies, and solutions that facilitate the implementation and management of privacy protections. The OneTrust Privacy & Data Governance Cloud can help with Privacy by Design in several ways from integrating assessments into the project design lifecycle, centralizing digital policy management, and streamlining privacy rights fulfillment.
By leveraging the OneTrust Privacy & Data Governance Cloud you can streamline your privacy management, automate compliance processes, and ensure consistent and effective implementation of Privacy by Design principles throughout your operations.