“Privacy means people know what they’re signing up for, in plain language, and repeatedly. I believe people are smart. Some people want to share more than other people do. Ask them.”
Steve Jobs said this back in 2010.
Over a decade later, those words are slowly but surely becoming a requirement for organizations that fall subject to privacy regulations such as the GDPR and the CCPA.
In addition to compliance with the law, smart businesses know having a privacy program in place is just good business.
84% of people say they care about the privacy and care of their data. They want more control over how it’s used. And 48% have already switched companies or providers because of their data policies or sharing practices.
This means your privacy program can be a competitive differentiator.
In fact, 69% of businesses are “very actively” looking to shape their data privacy policies. If your organization falls within that statistic, we’re here to help.
Here are 8 must-know best practices for building a world-class privacy program:
Step 1: Know Your Obligations
The first step is understanding what your organization should consider most important for your business.
Some obligations to consider are:
- The local, regional, and global privacy regulations your business must comply with, for example, CCPA, LGPD, and GDPR.
- Industry-specific codes of conduct for data guidance, for example, HIPAA.
- Contractual obligations your company may have with customers or third-party vendors regarding data processing.
- Requirements for handling employee data.
This process requires a gap analysis of all your company’s legal, regulatory, and reputational obligations. Determine what the risk of breaking those obligations might be, what risks your company is willing to take, and how your current efforts stack up.
Step 2: Understand Your Risks
Another best practice is understanding the chances a violation will occur. This involves an analysis of:
- Third-party vendors
- Data types (employee or customer)
- Data sensitivity
- Personnel access to data (internal and external)
- Security processes
- Historical breaches and how your organization managed them
This analysis will help provide an understanding of risks and potential impact of breaches. It will also open the door for discussion about what level of risk your business is willing to accept.
Step 3: Choose a Privacy Framework
Once you understand your obligations and risks, you’ll want to develop a privacy framework. A privacy framework is a structured set of guidelines to aggregate and harmonize – then integrate – all compliance requirements applicable to your organization.
Developing a framework will provide you with an implementation roadmap that outlines your privacy procedures and processes. It will help your organization:
- Identify high-risk areas.
- Reduce data loss.
- Measure against compliance to laws, regulations, and standards.
A few frameworks that provide initial guidance include:
Step 4: Create a Privacy-first Culture
To get everyone in the company on board with the data privacy program, you’ll need to set the tone from the top down.
Board & C-level buy-In: How your executives speak about privacy will set the tone for how the rest of the company views the expectations. Their input will also be crucial to getting a budget dedicated to training, technology, and personnel.
Human Resources support: Next, work with HR to dedicate a portion of the employee handbook to data privacy. From the moment employees are applying for a job in some cases, they need to understand the expectations of the company privacy policy.
Marketing: Your marketing team will play a critical role in communicating your privacy policy to your customers. Marketing will also need to ensure they’re complying with legislation.
All other departments: To ensure your privacy-first culture is successful, assign clear responsibility. Each department from IT to administration will play a role in your privacy program. Make sure each department understands its role and has the necessary resources to achieve outcomes. It’s also important that all departments have conversations with the privacy team about what projects or business decisions have an impact on privacy.
Step 5: Map Your Data
Data mapping tracks the flow of data to, through, and from your organization. When executed correctly, data mapping should clearly tell you a significant amount of information, such as:
- Where it came from (customers, staff, or third parties).
- Its purpose (order fulfillment or payroll).
- The specific entry point channel, aka how it enters your company (phone call, email, or form).
- Its format (Excel, Word, or CRM page).
- Where it’s stored (filing cabinet, in-house server, or in the cloud).
- The country it’s stored in.
- Where it’s accessible from and who has access to it.
Global privacy regulations such as GDPR require organizations to have comprehensive knowledge of how data is used, who has access to it, and where it’s being stored. Data mapping is the key to understanding your organizational data and ensuring compliance with regulations.
Step 6: Document Your Privacy Policies
Documenting your privacy policy is much more than a requirement under some laws. It’s also a chance for your brand to be transparent with consumers about how you’re collecting and using their data.
Your privacy policy document also sets the appropriate guidelines for key areas such as consent, access, and breach management for your employees.
Keep in mind, your privacy policy may overlap with other business policies. This includes security standards, records retention policies, and the management of confidential or intellectual property.
Step 7: Host Employee-wide Training
32% of security breaches involve phishing scams.
Something as simple as an email can cost your company its reputation, or worse, its existence. That’s why it’s so important to train your employees consistently.
Your training program should focus on the risk related to each employee’s role, as well as the known gaps in their knowledge and competence. For most of your employees, this will involve identifying the data they have access to, how a breach could take place, how to report incidents, and proper usage of work phones, laptops, etc.
Training should happen regularly, especially when changes to position, structures, risk, or obligations arise.
Step 8: Measure Performance
Set KPIs to ensure your program progresses as planned. Think about:
- What your organization needs to measure and why.
- The methods for monitoring, measuring, analyzing, and evaluating.
- When the monitoring and measuring should happen.
- When to analyze, evaluate, and report the results from monitoring.
Audits are a good way to ensure the program is effectively implemented and maintained. You’ll want to do both an internal audit to measure your performance, as well as an external audit to measure your vendors.
Your privacy program should measure:
- The percentage of employees trained effectively.
- The number of breaches and near misses.
- The number of transfers or impact assessments completed.
- The average time it takes to investigate and report breaches.
- The average time to respond to individual access requests.
Once the analysis comes to a close, results should turn into reports for upper management to review. This will allow improvements and changes to take place as needed.
Conclusion: Don’t Run Your Privacy Program Manually
The world of data privacy is always changing.
Today, 66% of countries have some sort of data privacy legislation, and 10% have legislation in the works.
This means your business must remain compliant with rapidly evolving laws, all while managing consumer requests and documenting processing activities and data transfers. It isn’t plausible for an organization to do it all manually.
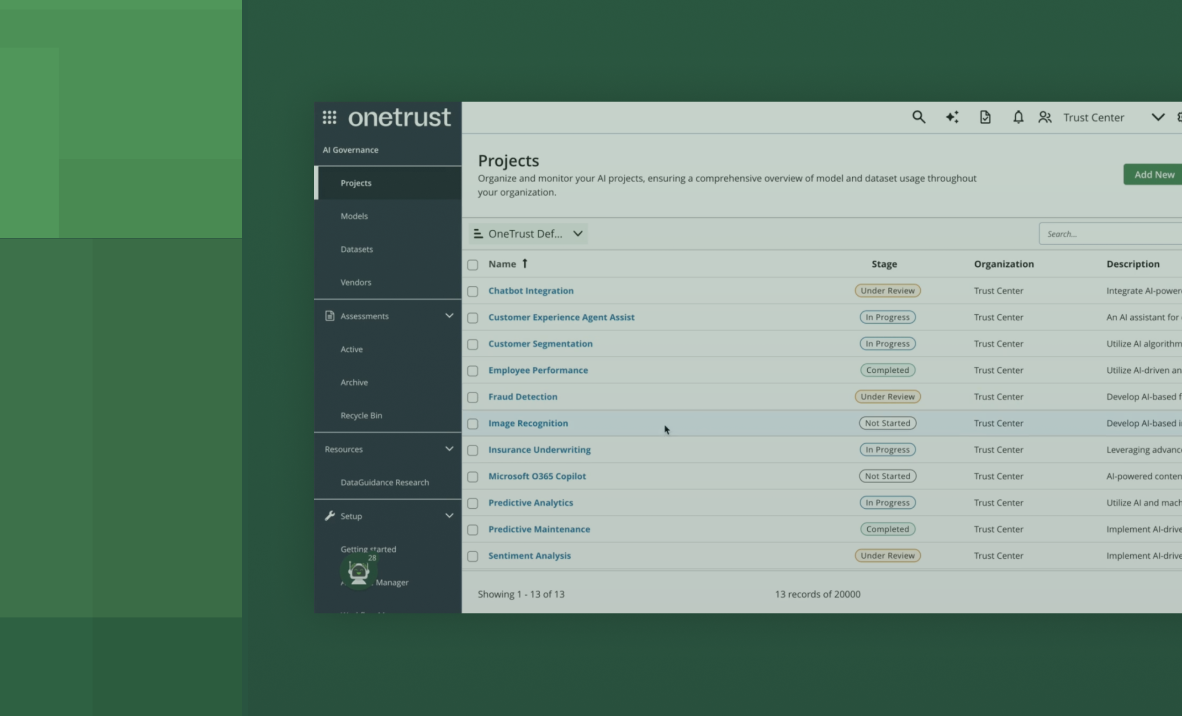
That’s where OneTrust Privacy comes in.
OneTrust Privacy offers your company a powerful and easy-to-use compliance solution that helps you manage your privacy program at scale. It’s privacy management, simplified. See it in action today or try it for free.