Reduce regulatory risk by up to 75% and streamline compliance by operationalizing all privacy use cases in one platform with intelligence from 2,000 trusted experts.
Privacy Automation
Scale privacy with AI
Our platform automates privacy operations to scale compliance and accelerate the responsible use of data across your business.
Comply
Automate
Improve productivity by up to 75% by leveraging AI to automate time-consuming tasks to scale compliance and free time for more strategic activities.
Accelerate
Improve time-to-value by up to 87% while ensuring responsible use by embedding privacy by design and removing roadblocks for the business.
The future of privacy: AI agents and automation
Govern well or move fast — you’ve never been able to do both. Now you can. AI removes the tradeoff.
Understand the operational impact of regulatory changes
Save hours of research each week with intelligence from DataGuidance, powering your privacy program with the most up-to-date, accurate, and trusted source of regulatory research.
KEY CAPABILITIES
Navigate complex regulations faster with OneTrust Copilot
Collaborate with personalized, shareable collections
Get started and react to change quickly with pre-built templates, workflows, and guidance


Manage and report on privacy compliance initiatives
Manage your entire compliance program in one platform with an intelligence engine that unifies privacy regulations, streamlines planning, and simplifies evidence collection.
Automate data subject request (DSR) fulfillment
Reduce the cost to fulfill a request with automation from intake through fulfillment.
KEY CAPABILITIES
Deploy dynamic workflows automated by request and regulatory context
Automate data retrieval and deletion, without having to scan your entire data estate
Use a secure communication channel for request updates and data sharing


Create, maintain, and publish privacy notices
Streamline notice compliance with automated updates across all sites and apps. Use templates to align with regulations, publish via an SDK, enforce approval workflows, and integrate with privacy tools for seamless data processing transparency.
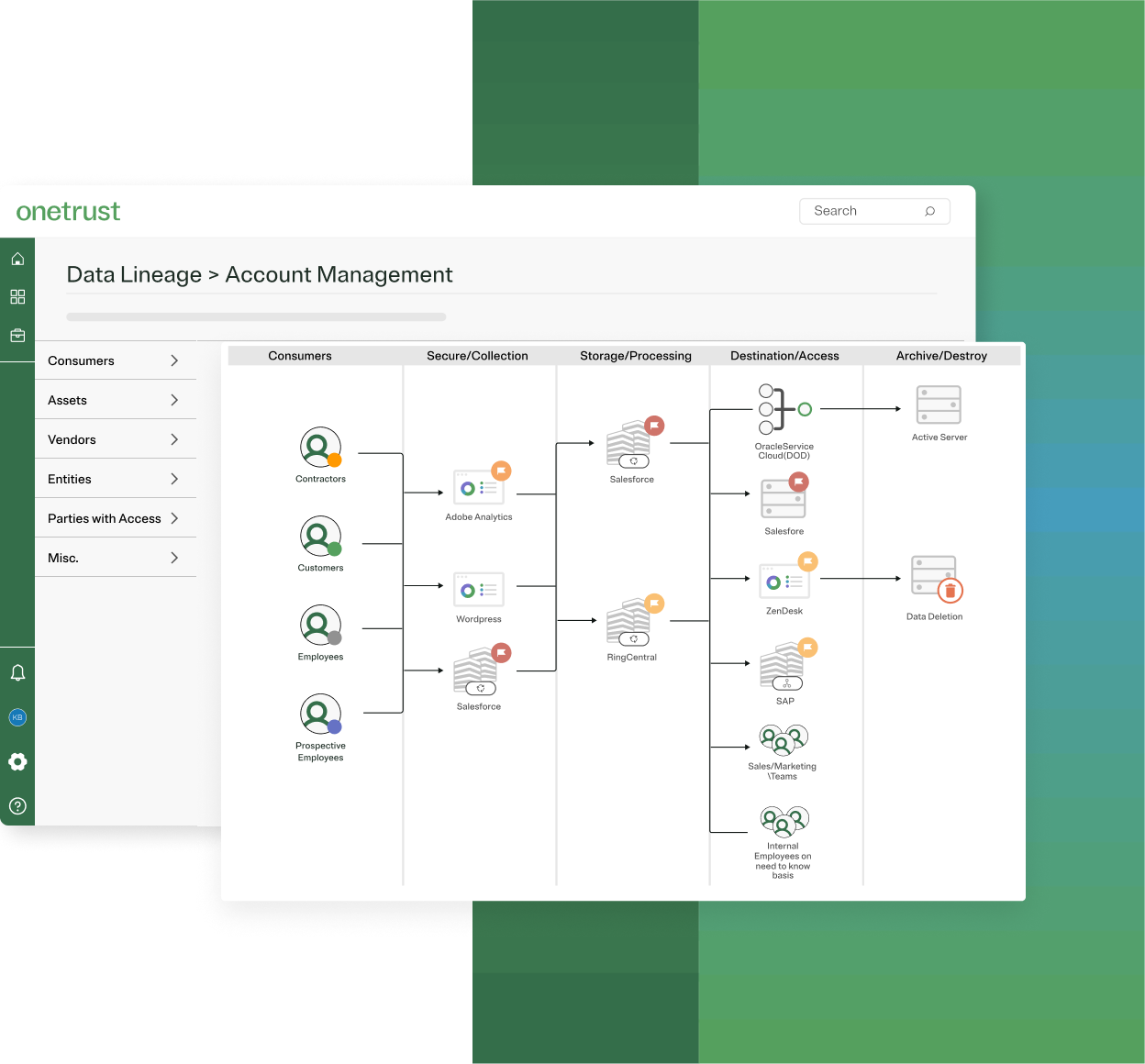
Build an evergreen data & activity map
Centrally map the data, business, and regulatory context of your personal data processing to automate workflows, enforce policy, and manage risk.
KEY CAPABILITIES
Automate record-keeping and downstream workflows like PIAs and incident response with purpose-built data discovery & classification
Get a central view into your privacy posture across all assets, processing activities, and vendors
Create a foundation for additional use cases like AI Governance, Third-Party Risk, and Data Use Governance


Operationalize privacy risk assessments and mitigation workflows
Leverage AI-assisted workflows to capture business context, proactively identify risks, and streamline mitigation efforts across your organization.
KEY CAPABILITY
Auto-populate questionnaires with information from business plans, contracts, security documents, inventory records, and more with AI Document Scanning and AI Inventory Record Analysis
Assess vendor privacy risk and manage DPAs
Centralize your inventory of all vendors, relevant attributes, and documentation. Use AI-driven assessments to streamline vendor onboarding, saving time and costs while mitigating risk.


Manage privacy incidents and notification requirements
Identify new incidents involving personal data, capture data to understand the impact and root cause, and get automated guidance on when notification is required.
KEY CAPABILITIES
Integration with existing privacy records (PIAs and data inventories) to understand context and impact
Automated notification guidance to meet regulatory requirements
Featured products
Privacy Operations
Simplify privacy program activities like data & activity mapping, privacy risk assessments, incident response, and more.
Learn moreDSR Automation
Automate DSRs from intake through fulfillment, including ID verification, data discovery & deletion, and secure response.
Learn moreDataGuidance
Leverage OneTrust Copilot to understand regulatory updates from 1,700 legal experts across 300 jurisdictions and how they apply to your business.
Learn moreProven results

“We now have full control over the processing of personal data that we do, with an intuitive tool that facilitates risk assessment and reporting.”
Marta Cañas Miralles, Data Protection Officer (DPO), Iberia Airlines

“OneTrust differentiates with an unrivaled vision for the future of privacy…”
Enza Iannapollo, Principal Analyst, Forrester
The Forrester Wave: Privacy Management Software, Q4 2023
75%
Productivity boost
Automated workflows allowed privacy teams to accomplish more with fewer resources.
Partnering with the best
Our Privacy Automation service partners and seamless technology partner integrations make it even easier for you to enable the responsible use of data.
Service partners:



Technology partners:



You may also like

Webinar
AI Governance
AI in B2C: Managing compliance, consent & consumer trust
Join our expert panel as we cover how businesses can create AI-driven experiences while maintaining compliance.
July 24, 2025

Webinar
Privacy Management
OneTrust Using OneTrust: Managing data privacy
Learn how how our Privacy department leverages OneTrust's tools to automate privacy workflows, ensuring compliance and efficiency.
July 16, 2025

Webinar
Privacy Management
Northeast data privacy laws: Insights & compliance strategies
This session will provide a practical roadmap to address Northeast data privacy laws, from understanding consent requirements to implementing compliant consent workflows within your operations.
July 10, 2025

Webinar
AI Governance
Bringing privacy to the AI table with data protection by design
Join our webinar to see how privacy professionals are embedding compliance and trust into AI governance programs from the start.
June 24, 2025

Webinar
Privacy Management
OneTrust Using OneTrust: A platform overview
Get an inside look at how OneTrust uses its own platform to connect teams, simplify workflows, and turn complexity into clarity.
June 18, 2025

Webinar
AI Governance
AI literacy 101: Building a privacy-conscious workforce
Learn how to build AI literacy across your organization to support responsible AI use, ensure privacy compliance, and reduce risk. Join our expert-led discussion on training strategies, best practices, and real-world applications.
June 17, 2025

Webinar
Privacy Automation
Automating privacy touchpoints: Notices, consent, and DSRs made easy
Join us and learn how to simplify and scale privacy compliance by automating key consumer touchpoints.
June 12, 2025

Webinar
Privacy Automation
Live demo: Scale privacy with automation
Join our live demo and see how OneTrust Privacy Automation empowers privacy teams to simplify compliance, reduce manual work, and scale programs efficiently.
May 29, 2025

Webinar
Privacy Management
Celebrating the GDPR's 7th anniversary
Join us as we celebrate the GDPR's 7th anniversay and discuss the landmark's privacy law's milestones and compliance challenges.
May 28, 2025

Webinar
Privacy Management
OneTrust Spring Release
We explore the latest release which introduces AI-assisted features that help privacy and third-party risk teams scale by reducing manual effort and friction, so they can focus on the work that matters most.
May 27, 2025

Webinar
AI Governance
Navigating AI in business functions: Risk, responsibility & compliance
In this webinar, industry experts will explore key AI risks, regulatory considerations, and best practices for aligning AI initiatives with privacy, security, and ethical frameworks.
May 08, 2025

Webinar
Privacy Automation
Scaling privacy: Inside OneTrust’s AI agents and automation
Learn how OneTrust's latest AI innovations, including Privacy AI Agents, are enabling privacy teams to govern effectively and move quickly.
May 01, 2025

Webinar
Privacy Automation
Driving value through automation: Practical steps to scale your privacy program
Learn how to transition from compliance to scalable automation, enhancing efficiency, reducing risks, and improving compliance outcomes.
April 24, 2025
eBook
Privacy Management
7 steps toward Thai PDPA compliance
Download our Thai PDPA compliance guide to learn seven essential steps for meeting regulatory requirements and reducing privacy risk.
April 09, 2025

Webinar
Third-Party Risk
Empowering business with Unified Data Privacy & TPRM
Join our webinar to explore actionable strategies powered by OneTrust solutions to foster collaboration across privacy and TPRM stakeholders to better support your organizations.
April 03, 2025
eBook
Privacy Management
Your guide to compliance with India’s Digital Personal Data Protection Act (DPDPA)
Download this eBook on India's Digital Personal Data Protection Act (DPDPA) and learn about the act's key provisions.
March 26, 2025

Webinar
Privacy Management
NIS2 in practice: Implementation of technical measures
Join experts from Sidley Austin LLP and ENISA for a webinar on the practical implementation of NIS2 technical measures. Gain insights on compliance, technical strategies, and the latest EU legislation to strengthen your NIS2 readiness.
March 20, 2025

Webinar
Privacy Management
Navigating India’s DPDP Act: Practical insights and compliance strategies
Join our expert panel for an in-depth discussion on India's Digital Personal Data Protection Act (DPDPA) and gain insights on staying ahead of evolving data protection regulations in India
March 19, 2025

Webinar
Privacy Management
Privacy roadmap 2025: What organizations need to prioritize
Join our webinar, Privacy Roadmap 2025 – What Organizations Need to Prioritize, to explore key privacy trends, regulatory updates, and AI governance challenges
March 04, 2025

Webinar
Privacy Automation
Turn compliance into your competitive edge with Privacy Automation
This webinar explores the evolving privacy landscape, the future of compliance, and real-world examples of effective privacy automation.
February 27, 2025

Webinar
Privacy Automation
IAPP hosted webinar: Discovering the ROI of Privacy Automation
Discover how OneTrust Privacy Automation transforms privacy programs from compliance-focused to strategic assets. Learn how automation maximizes ROI, boosts efficiency, mitigates privacy risks, and drives competitive advantage.
February 06, 2025

Webinar
Privacy Management
APAC Data Privacy Day 2025
Join us for a special Data Privacy Daty 2025 webinar as we look back on 2024's data protection and privacy trends across Asia Pacific and Japan (APAC), as well as what to expect in the region for 2025.
January 30, 2025

Webinar
Privacy Automation
OneTrust in Action: Building Seamless and Trusted User Journeys - Live Demo
Learn how to streamline data privacy compliance with OneTrust Consent & Preferences. Build trust, enhance user experience, and align with global regulations through user-driven consent management.
January 29, 2025

Webinar
Privacy Management
2024 to 2025: Preparing for the next wave of privacy regulations
Prepare for 2025's privacy changes with this recap webinar on 2024's regulations and explore upcoming laws, trends, and compliance strategies.
January 23, 2025

Webinar
Privacy Management
Data Privacy Day 2025
Join this webinar to hear from a panel of expert privacy professionals as they dissect the key happenings in 2024 and how privacy professionals can approach what may occur in 2025.
January 21, 2025
eBook
Privacy Management
Your Data Privacy Day handbook
This guide give you a range of information and resources to raise privacy awareness this Data Privacy Day.
January 21, 2025

Checklist
Privacy Management
Thai PDPA compliance checklist
Compliance with the PDPA means data controllers and processors covered by the law must take the necessary steps to meet the data protection obligations it defines. This checklist serves as a framework for building a PDPA compliance program and addressing the law’s requirements.
January 16, 2025
eBook
Privacy Management
Comparing Personal Data Protection Acts in the APAC region
Download our eBook for a comparison of the different Personal Data Protection Acts in the Asian-Pacific region.
January 06, 2025

Webinar
Privacy Management
Top 10 privacy moments that shaped 2024
In this webinar, DataGuidance privacy analysts will review of privacy enforcement trends in 2024, explore global AI regulations, including the EU AI Act, and discuss global privacy legislation developments in 2024.
December 19, 2024

Webinar
Privacy Management
Emerging privacy laws in the Northeast: Key insights and compliance strategies
Join our webinar to explore key 2025 data privacy laws in the Northeast US, including New Jersey’s Senate Bill 332, New Hampshire Senate Bill 255, and Rhode Island's Data Data Transparency and Privacy Protection Act.
December 18, 2024
Infographic
Consent & Preferences
Deliver hyper-personalized experiences with a privacy-first approach to first-party data
Download our infographic to earn how to navigate new privacy laws and deprecating cookies with Adobe CDP and OneTrust.
December 18, 2024

Webinar
Third-Party Risk
Virtual Lunch and Learn: A deep dive into OneTrust's Third Party Management capabilities
Join us for a virtual Lunch & Learn session and explore how OneTrust’s Third Party Management solution can streamline your risk management processes.
December 17, 2024

Webinar
Cookie Consent
How to handle opt-outs for tracking pixels under Australian privacy law
Join our webinar to learn how to master consent management and handle opt-outs for tracking pixels.
December 12, 2024

Webinar
Privacy Management
Revisiting IAPP DPC 2024: Top trends on the latest data protection developments
Join OneTrust and PA Consulting as we dive deeper into the key takeaways from the IAPP Europe Data Protection Congress 2024. Our speakers will provide actionable insights from the event on the latest developments in data protection, privacy, and AI.
December 12, 2024

Webinar
Responsible AI
Overcoming the privacy pitfalls of GenAI
This webinar will explore the key privacy pitfalls organizations face when implementing GenAI, focusing on purpose limitation, data proportionality, and business continuity.
December 10, 2024
Infographic
Privacy Automation
GDPR: Dos and don'ts
Navigating GDPR compliance can feel daunting, especially for businesses with limited resources. This quick infographic guide of actionable “dos” and “don’ts” will help you develop the foundation of a broader privacy-first approach that keeps you aligned with your GDPR compliance goals.
December 10, 2024
Infographic
Privacy Management
An overview of the Thailand Personal Data Protection Act
Download our infographic overview of Thailand's Personal Data Protection Act and get the basic facts on the scope, key definitions, data subject rights, and more on the data protection law.
December 10, 2024
eBook
Privacy Management
A quick guide to the Thai PDPA
Download our ebook on understanding the Personal Data Protection Act (PDPA), Thailand's first comprehensive data protection law, and get a quick guide on the legistation's requirements, definitions, and other key points.
December 10, 2024
Interactive Tool
Privacy Management
Privacy risk assessment workbook
Privacy risk assessments are a tool that organizations use to assess the level of risk that a data processing activity will potentially have on the individuals involved and consider risks from several angles. This workbook will walk you through the different areas of privacy that must be considered in a PIA through a comprehensive range of questions about your processing activity.
December 10, 2024

Webinar
Privacy Management
Staying equipped for compliance: A global recap of emerging privacy laws
Join us for a global regulatory recap, where we will explore the latest privacy regulations and key developments impacting compliance in 2024 and beyond. This webinar will offer a streamlined analysis of newly adopted privacy laws, emerging AI regulations, and the evolving cyber regulations such as the NIS2 Directive.
November 20, 2024

Webinar
Privacy Automation
From request to resolution: Simplifying DSRs with automation
Learn how OneTrust's Data Subject Rights (DSR) Automation solution can automate DSRs from intake through fulfillment including ID verification, data detection and deletion, redaction, and secure response.
November 06, 2024

Checklist
Privacy Management
EU-US DPF self-certification and compliance checklist
The European Commission’s first review of the EU-US DPF highlighted several areas that organizations should focus on when looking to self-certify or maintain compliance with the framework. This checklist helps you monitor compliance and demonstrate accountability with the framework’s principles.
November 04, 2024
eBook
Consent & Preferences
Chrome's new path for privacy
Explore our guide on Chrome's new privacy approach, covering cookie management changes, consumer behavior, and strategies for advertisers in a cookieless future.
October 31, 2024
Infographic
Privacy Management
How OneTrust partners with Artefact to enable responsible data strategies
The rise in technology development against the backdrop of increased privacy regulation has made responsible data use a crucial consideration for marketing and AI initiatives. Learn how OneTrust and Artefact partner to create and implement strategies for responsible data use.
October 29, 2024

Webinar
Privacy Automation
Explore the future of regulatory intelligence: A DataGuidance demo
In this live demo webinar, we will showcase the advancements in regulatory intelligence embedded within the DataGuidance platform, which offers comprehensive and updated regulatory research across 300+ jurisdictions.
October 29, 2024

Video
Privacy Automation
Transforming data privacy and governance with OneTrust and Snowflake
OneTrust’s privacy platform, powered by Snowflake, ensures secure data sharing and governance, helping organizations manage privacy without compromising collaboration.
October 18, 2024
Report
Consent & Preferences
OneTrust acknowledged as a Representative Vendor in the Gartner® Market Guide for Consent and Preference Management
Explore key insights from the 2024 Gartner® Market Guide Gartner® Market Guide for Consent and Preference Management.
October 10, 2024
eBook
Consent & Preferences
Operationalizing first-party data in advertizing
Learn how to harness the power of first-party data in digital marketing. Discover strategies to operationalize data, ensure accuracy, and drive decision-making in this comprehensive guide for marketing organizations.
October 10, 2024

Webinar
Privacy Automation
Privacy automation 101: Simplifying data mapping and risk assessments
Join this webinar to learn how OneTrust helps you automate Data Mapping and Privacy Risk Assessments and how to overcome maintenance challenges.
September 25, 2024

Report
Privacy Automation
Proven ROI with OneTrust
Learn how a composite organization achieved a 227% return on investment over 3 years and payback in just 7 months by leveraging OneTrust to streamline privacy, data governance, and consent management.
September 24, 2024
Report
Privacy Automation
Discover the economic benefits of OneTrust
Download this 2024 Forrester Consulting Total Economic Impact™ study to see how OneTrust has helped organizations navigate data management complexities, generate significant ROI, and enable the responsible use of data and AI.
September 24, 2024

Webinar
Privacy Automation
Global regulatory update: Recent privacy developments and compliance trends
Join us for a webinar on the latest updates and emerging trends in global privacy regulations.
September 12, 2024
eBook
Privacy Management
Maturing your GDPR compliance program
This comprehensive eBook explores the key elements of a GDPR compliance program.
September 11, 2024

Webinar
Privacy Management
OneTrust Live: Unlocking the power of automation for privacy programs
Join us for a live demo where we will discuss the advanced capabilities of OneTrust solutions in data privacy enforcement, first-party data collection, and AI innovation.
August 21, 2024

Webinar
Privacy Management
Preparing for child data protection laws in the US
Join DataGuidance and a panel of experts as we discuss US privacy laws the protection of minors' data.
August 07, 2024

Webinar
Privacy Management
CPRA in action: OneTrust Live Demo
Join us for a deep dive tour of our suite of technology solutions for operationalizing and automating CPRA requirements across Do Not Share, Consumer Rights and privacy governance operations.
August 01, 2024
eBook
Privacy Automation
Moving through the Data Privacy Maturity Model
Explore the Data Privacy Maturity Model to evolve your data privacy program from compliance-focused to a strategic, value-driven framework.
July 29, 2024

Webinar
Privacy Management
Going beyond CCPA
Join us for an in-depth webinar on "Going Beyond CCPA," where we will explore the intricacies of privacy laws, compare major regulations, and provide guidance on enhancing your privacy policy.
July 25, 2024

Webinar
Privacy Management
New European cyber laws: What you need to know
The EU has adopted several new Cyber Laws that will impact many businesses and will come into force over the next few months (in October in the case of NISD2) and require actions now. Join the webinar to learn about the latest cyber developments.
July 23, 2024

Webinar
Privacy Management
The evolution of CCPA
Join us for an insightful webinar on "The Evolution of CCPA" where we will delve into the latest amendments, understand their impact, and explore the new requirements and implications for businesses.
July 18, 2024

Webinar
Privacy Management
Mastering data privacy: Navigating CCPA, CPRA, and beyond
Mastering Data Privacy: Expert Guidance on CCPA, CPRA, GDPR Compliance, Privacy Policy Best Practices, and Live Demo Insights
July 18, 2024

Webinar
Privacy Management
OneTrust Live: Complying with US Privacy Laws Effective July 2024
Join us on July 17th for a live demo of OneTrust's solutions, providing you with practical tools and strategies to ensure your organization is compliant with both new and existing data privacy laws in the US.
July 17, 2024

Webinar
Privacy Management
The road to 50 states: Rhode Island joins the US privacy landscape with a new law
Rhode Island has become the 20th US State to pass a privacy law. On June 25, 2024, the Governor of Rhode Island transmitted the Data Transparency and Privacy Protection Act (RIDTPPA) without signature allowing the Act to become law. Join the webinar to learn more.
July 16, 2024

Webinar
Privacy Management
Unpacking the latest in APAC privacy trends and regulatory developments
Join DataGuidance and expert contributors for a webinar to unpack the latest developments and regulatory landscapes in the APAC region.
July 11, 2024

Webinar
Privacy Management
Scaling to new heights with AI Governance
Join OneTrust experts to learn about how to enforce responsible use policies and practice “shift-left” AI governance to reduce time-to-market.
June 25, 2024

Webinar
Privacy Management
The road to 50 states: Minnesota and Vermont join the US privacy landscape
In this webinar, OneTrust DataGuidance and expert contributors unpack the MCPA and VDPA, examining the requirements, exceptions, and practical implications of the legislations on the data controllers and processors.
June 17, 2024
Infographic
Privacy Management
Building consumer trust through privacy by design
Build consumer trust with Privacy by Design. Learn how embedding privacy can enhance compliance, security, and brand loyalty with our detailed infographic.
June 14, 2024

Webinar
Privacy Management
OneTrust Live: Revolutionizing Your Data Strategy with Enhanced Privacy and AI
Join us for a live demo showcasing the cutting-edge capabilities of OneTrust solutions in the realms of data privacy enforcement, first-party data collection, and AI innovation.
June 12, 2024

Webinar
Privacy Management
From legislation to operation: How to prepare for the new wave of US Privacy laws
Prepare your organization for the new wave of US privacy laws.
June 06, 2024
eBook
Privacy Management
Understanding data transfers under the GDPR ebook
In the ebook, we delve into the fallout from Schrems II and explore how organizations based in Europe can best navigate international data transfers under the GDPR.
June 05, 2024
Checklist
Third-Party Risk
TPRM privacy compliance: Questions to ask when working with third parties
Download this checklist to learn what questions to ask when designing a third-party risk management program that enables privacy compliance.
May 31, 2024

Webinar
Privacy Management
Unlocking data as a strategic asset
Learn how to enhance your privacy program maturity to deliver strategic business value with first-party data, create dynamic end-user experiences, and more.
May 29, 2024

Webinar
Privacy Management
Preparing for a new regulation: Lesson learned from the GDPR businesses can apply to the EU AI act?
Join our panel of experts as we celebrate GDPR Anniversary and take a closer look at the relationship between the GDPR and AI Act.
May 23, 2024

Webinar
Privacy Management
DSAR Product Demo with Data Privacy Group
Join our webinar to learn the practical tips and use cases for automating DSAR requests.
May 21, 2024
Infographic
Comparing US state privacy law requirements
Download our infographic and compare the many US state privacy law requirements that have been enacted or will soon come into effect.
May 14, 2024

Webinar
Trust Transformation
Privacy and trust in action: Implementing best practices in today's privacy landscape
Join OneTrust and Red Clover to discuss how earning trust is the key strategic objective of a mature data privacy program.
May 14, 2024

Webinar
GRC & Security Assurance
Empowering your cyber defense: Key insights into the latest NIST CSF update with PwC
Join this webinar with OneTrust and PwC and gain insights into the upcoming NIST CSF update and learn how to effectively deploy it across your organization.
May 08, 2024

Webinar
Privacy Management
Best practices for managing employee DSARs in the EU and UK
In this webinar, our panel of experts will explore best practices for managing common complexities experienced when managing DSARs in the EU and UK.
May 08, 2024

Webinar
Privacy Management
Integrating privacy strategically into your business
Join this session to learn how to take your data privacy program to the next level by building upon your existing capabilities, automating core privacy workflows, and more.
April 24, 2024
Infographic
Privacy Management
US state privacy laws timeline
View our timeline to understand the progression of current US state privacy laws and key dates.
April 23, 2024

Webinar
Privacy Management
Federal US privacy bill on the horizon? Exploring the draft APRA & new state privacy legislation
Join OneTrust DataGuidance and expert contributors for an overview of the Kentucky Consumer Privacy Act (KCPA), Maryland's Senate Bill 0541, and the draft American Privacy Rights Act and explore how a federal bill could shape the US privacy landscape.
April 23, 2024

Video
Privacy Management
Navigating the data lifecycle with OneTrust Privacy & Data Governance
Explore how OneTrust solutions help you navigate the information lifecycle, ensure compliance, mitigate risks, and enhance data governance practices.
April 22, 2024

Webinar
Privacy Management
April Privacy & Data Governance Cloud demo webinar
See how OneTrust's Privacy & Data Governance Cloud operationalizes regulatory compliance and helps ensure privacy and responsible data use.
April 17, 2024
Resource Kit
Privacy Management
Privacy by Design resource kit
This resource kit offers a range of content to help you understand the concept of Privacy by Design and provide guidance on best practices for its successful implementation.
April 04, 2024
Interactive Tool
Privacy Management
OneTrust Data Privacy Maturity Model self-assessment
This self-assessment will help you to gauge the maturity of your privacy program and understand the areas the areas of improvement that can further mature your privacy operations.
April 01, 2024

Webinar
Privacy Management
Building foundational data privacy compliance
Join this session to learn how to build a strong privacy foundation to achieve your compliance objectives and lay the groundwork for more strategic privacy programs.
March 26, 2024

Checklist
Privacy Management
Preparing to self-certify with the EU-US DPF checklist
Self-certify for the EU-US DPF framework and comply with its seven core principles with this checklist.
March 26, 2024

Webinar
Privacy Management
Spring into action! Navigating CPRA: Ensuring compliance and protecting privacy
Join us for an interactive webinar we dive into the CPRA, which will go into force on March 29th.
March 21, 2024

Webinar
Privacy Management
Navigating data privacy in 2024: Global regulatory updates & compliance strategies
Join our webinar for a comprehensive overview of the latest global data privacy regulations and updates impacting businesses in 2024 and how to prepare.
March 20, 2024

Webinar
AI Governance
AI in (re)insurance: Balancing innovation and legal challenges
Learn the challenges AI technology poses for the (re)insurance industry and gain insights on balancing regulatory compliance with innovation.
March 14, 2024

Webinar
Privacy Management
Fintech, data protection, AI and risk management
Watch this session for insights and strategies on buiding a strong data protection program that empowers innovation and strengthens consumer trust.
March 13, 2024

Webinar
Third-Party Risk
TPRM privacy compliance: 10 best practices when working with third parties
How can you build a privacy-focused TPRM program? In this webinar, we discuss best practices for privacy compliance when working with third parties, from onboarding to offboarding.
March 13, 2024

Webinar
Privacy Management
Managing cybersecurity in financial services
Get the latest insights from global leaders in cybersecurity managment in this webinar from our Data Protection in Financial Services Week 2024 series.
March 12, 2024

Webinar
AI Governance
Government keynote: The state of AI in financial services
Join the first session for our Data Protection in Financial Services Week 2024 series where we discuss the current state of AI regulations in the EU.
March 11, 2024
Report
Data Discovery & Classification
The KuppingerCole Leadership Compass on Data Governance
OneTrust has been named a leader in the 2024 KuppingerCole Leadership Compass on Data Governance, receiving the highest rating for Product, Innovation, and Market.
March 08, 2024

Infographic
Data Discovery & Classification
OneTrust Privacy & Data Governance Cloud gains momentum with widespread industry recognition
OneTrust maintains its leading position in Privacy & Data Governance, with a record number of recognitions in the last six months from KuppingerCole and Forrester
March 07, 2024
eBook
Privacy Management
Preparing to self-certify with the EU-US DPF
The EU-US DPF represents an important mechanism for US-based companies to lawfully transfer personal data form the EU to the US. Use this eBook to learn more about how to self-certify with the framework and its seven core principles.
March 07, 2024

Webinar
Privacy & Data Governance
Unlocking value through responsible use of data
Learn about the data privacy maturity model and how your privacy teams can move beyond compliance to become strategic enablers for their business.
February 28, 2024
eBook
Privacy Management
Quebec's Law 25: What the CPO wants the CTO to know
Quebec’s Law 25 is a major legislative development in Canadian privacy that will have a significant effect on IT systems. Learn more about what the CPO wants the CTO to know.
February 26, 2024
Infographic
Privacy Management
OneTrust named a leader in The Forrester Wave™: Privacy Management Software, Q4 2023 report
See why OneTrust was named a Leader in The Forrester Wave™: Privacy Management Software, Q4 2023 report.
February 07, 2024
eBook
Privacy Management
Understanding the Data Privacy Maturity Model
Data privacy is a journey that has evolved from a regulatory compliance initiative to a customer trust imperative. This eBook provides an in-depth look at the Data Privacy Maturity Model and how the business value of a data privacy program can realised as it matures.
February 07, 2024

Webinar
Privacy Management
The road to 50 states: New Jersey and New Hampshire join the US privacy landscape
oin OneTrust DataGuidance for a webinar highlighting the key requirements within the new US laws, New Jersey Senate Bill 332 and New Hampshire Senate Bill 255.
February 01, 2024

Webinar
Privacy Management
Data Privacy Day 2024: Reflecting on the past year and anticipating the next
Join our panel of expert privacy professionals as they dissect the key happenings in 2023 and how privacy professionals can approach what may occur in 2024.
January 31, 2024

Webinar
Privacy Automation
Embedding Privacy by Design through PIA Automation
Join us for a webinar on Embedding Privacy by Design through PIA Automation.
January 11, 2024

Report
Privacy Management
The Forrester Wave™: Privacy Management Software, Q4 2023
Download the report see why OneTrust is named a leader in The Forrester Wave™: Privacy Management Software, Q4 2023 Report.
December 14, 2023
Infographic
Privacy Management
OneTrust announces partnership with Europrivacy
Learn how OneTrust and Europrivacy's partnership can help your organization achieve GDPR compliance and build trust with your customers.
December 06, 2023

Webinar
Privacy Management
Automating fulfillment of subject rights requests in the US
Learn how Privacy Rights Automation helps to fully automate privacy rights requests.
December 06, 2023

Webinar
Privacy Management
Live Demo: How to holistically manage data transfers and data sharing requirements
Live demo of the OneTrust Privacy Cloud, exploring how to manage Data Transfers, perform TIAs, and enforce consumer opt-out of the sale/share of personal data.
December 05, 2023

Webinar
AI Governance
Revisiting IAPP DPC: Top trends from IAPP's privacy conference in Brussels
Join OneTrust and KPMG webinar to learn more about the top trends from this year’s IAPP Europe DPC.
November 28, 2023

Webinar
Privacy Management
December's deadline: Ensuring compliance with Utah's privacy regulation
Join us for a webinar as we explore the impending implementation of the Utah Privacy Law, set to take effect on December 31, 2023.
November 14, 2023
eBook
Privacy Management
Data privacy and data protection: The basics explained
Whether you’re new to privacy or have been working in the space for some time, it can be a confusing place. In this eBook we explain the basics.
November 01, 2023

Webinar
Privacy Management
Managing data transfers within the UK & EU
Join our experts as we discuss ways to effectively manage data transfers between the UK & EU while staying compliant with the latest privacy regulations.
October 31, 2023
Infographic
Privacy Management
The principles of the EU-US DPF
The EU-US Data Privacy Framework is based upon seven core principles that organizations must comply with to certify with the framework.
October 30, 2023

Webinar
Privacy Management
Revisiting the ICO Data Protection Practitioner's Conference: Addressing your top challenges
Join OneTrust and KPMG UK to discuss the challenges of employee SARs, managing your breach response with third parties, and incident management.
October 25, 2023

Webinar
Third-Party Risk
5 Ways to save time when assessing third parties for privacy and security risks webinar
Join our webinar and learn how to save time and streamline third-party risk assessment throughout the TPRM lifecycle.
October 25, 2023

Webinar
Privacy Management
Embedding privacy by design to enforce responsible use of data
In this webinar, we explore the latest in Privacy by Design standards and how to effectively manage the balance between Privacy and Data Governance.
October 18, 2023
eBook
Third-Party Risk
Data privacy compliance and Third-Party Management: A unified approach
Understand the importance of data privacy in third-party risk management, and 10 best practices for achieving privacy compliance when working with third parties.
October 12, 2023

Webinar
The Shifting US Privacy Landscape: Lessons learned from enforcement actions and emerging trends
Stay ahead of US privacy laws as we explore the lessons learned from CCPA and FTC enforcement and how AI is effecting the regulatory landscape.
October 12, 2023

Webinar
Privacy Management
The Finalization of the UK-U.S. Data Bridge
A webinar discussion of significant points and implications of the new UK-US Data Bridge.
October 10, 2023
eBook
Privacy Management
A look at processing principles under the GDPR, CCPA, and the EU-US DPF
Download this ebook to understand the principles of the GDPR, CCPA (as amended), and the EU-US DPF and to compare their similarities and differences.
October 02, 2023

Webinar
Privacy Management
Privacy in practice: DSAR with PA Consulting
Join OneTrust and PA Consulting as we deep dive into the latest ICO requirements on SARs, handling DSARs, and the benefits of automation.
September 28, 2023
Infographic
Privacy & Data Governance
Understanding the EU Data Boundary
Download our free infographic and get the information you need to understand the EU Data Boundary and how to properly handle data in the European Union.
September 22, 2023

Webinar
Privacy Management
Privacy in practice: PIA & DPIA with PA Consulting
Join OneTrust and PA Consulting as we discuss what makes an effective PIA, best practices, and the benefits of automation.
September 21, 2023

Webinar
Privacy Management
The road to privacy compliance: A spotlight on Oregon & Delaware legislation
We explore the new Oregon and Delaware privacy laws, how they differ from other US privacy laws, and what they mean for your business.
September 14, 2023

Webinar
Privacy & Data Governance
Privacy in practice for data mapping: With PA Consulting and Syngenta
Join OneTrust and panelists from PA Consulting and Syngenta as we explore practical ways to build an effective data mapping program, best practices, and the need for automation.
September 14, 2023

Webinar
Privacy Management
India's DPDPA: What you need to know
In this webinar, legal experts discuss India's newly enacted comprehensive privacy law, the Digital Personal Data Protection Act, 2023 ('DPDPA')
September 12, 2023

Infographic
Privacy Automation
The ROI of privacy notice management infographic
Download this infographic and see the ROI benefits of privacy notice management automation with OneTrust Privacy Notice Management.
September 05, 2023
Regulation Book
Privacy Management
Utah Consumer Privacy Act law book
Download the Utah Consumer Privacy Act law book and have the official UCPA text at your fingertips for when the law takes effect on December 31, 2023.
September 04, 2023
eBook
Privacy Management
Responsible data use: Navigating privacy in the information lifecycle eBook
Download this eBook and get the insights you need to safeguard customer privacy and ensure responsible data use in the information lifecycle.
August 22, 2023

Webinar
Privacy Management
August Privacy & Data Governance Cloud Demo Webinar
See how OneTrust's Privacy & Data Governance Cloud operationalizes regulatory compliance and helps ensure privacy and responsible data use.
August 16, 2023

Blog
Privacy Management
The road to 50 states: Delaware and Oregon join the US privacy landscape
Get in-depth analysis on two upcoming US Privacy laws, the Oregon Consumer Privacy Act (OCPA) and the Delaware Personal Data Privacy Act (DPDPA), with OneTrust DataGuidence and a panel of experts.
August 10, 2023
Resource Kit
Technology Risk & Compliance
PCI DSS essentials: A resource collection for compliance
Achieve PCI DSS standard compliance with our comprehsive guide to safeguarding your organization's payment card data.
August 09, 2023
eBook
Privacy Management
EU-US Data Privacy Framework: Your questions answered
What you need to know about the new EU-US Data Privacy Framework and international data transfers.
July 26, 2023
Resource Kit
Privacy Management
EU-US Data Privacy Framework resource kit
Download our EU-US Data Privacy Framework resource kit to better understand the new aggreement for cross-border personal data transfers and how to educate your stakeholders.
July 20, 2023

Webinar
Privacy Management
Managing data transfers
Register for this free webinar to learn how to effectively manage international data transfers in the wake of Schrems II.
July 18, 2023

Webinar
Privacy Management
The finalization of the EU-US Data Privacy Framework
Join us for an expert panel as we discuss the finalized EU-US Data Policy Framework and what it means for organizations managing international data transfers.
July 13, 2023

Webinar
Privacy Management
Privacy & Data Governance monthly demo webinar
Watch a demo of our Privacy & Data Governance Cloud and discover how to operationalize compliance and enable trusted data use.
July 12, 2023

Webinar
Responsible AI
Unpacking the EU AI Act and its impact on the UK
Prepare your business for EU AI Act and its impact on the UK with this expert webinar. We explore the Act's key points and requirements, building an AI compliance program, and staying ahead of the rapidly changing AI regulatory landscape.
July 12, 2023

Webinar
Privacy Management
Now in effect: Colorado and Connecticut privacy laws
In this free webinar, our privacy experts delve into the new Colorado and Connecticut privacy laws and how they differ from other US state regulations.
July 12, 2023

Infographic
Governance & Policy Management
The 6 principles of data responsibility
Download the infographic to learn more about the 6 guiding principles for data responsibility and why it is crucial that you follow them.
July 11, 2023
eBook
Privacy Management
The 7 principles of Privacy by Design
Learn about the seven fundamental principles of Privacy by Design and how to apply them to your business.
July 10, 2023

Data Sheet
Technology Risk & Compliance
Certification Automation: Managing PCI DSS compliance
See how OneTrust Certification Automation streamlines PCI DSS compliance by identifying controls and requirements with automation.
July 05, 2023

Webinar
Third-Party Risk
Are your third parties a privacy compliance liability? 5 tips to reduce your exposure
Join our webinar and learn how to create an effective, privacy-focused third-party risk management (TPRM) program that streamlines recordkeeping and reduces your risk exposure.
July 05, 2023

Webinar
Privacy Management
Unpacking the EU-US DPF
In this webinar, we cover the new EU-US Data Privacy Framework (EU-US DPF) and what privacy program managers need to know for post-Schrems II data transfers.
June 28, 2023

Webinar
Privacy Management
New states, new dates: Preparing for Indiana, Montana, Tennessee and Florida state privacy laws
Join our expert panel where we examine upcoming privacy legislation in Indiana, Montana, Tennessee, and Florida and the key requirements of each law.
June 20, 2023
Checklist
Privacy Management
The Revised FADP: 7 steps toward preparedness
Prepare for Switzerland’s Revised Federal Act on Data Protection (Revised FADP) when it comes into force on September 1, 2023 with our free compliance checklist.
June 15, 2023

Webinar
Privacy Management
Vietnam PDPD: What you need to know
Join our expert webinar as we discuss the Vietnam PDPD, its key requirements, and how your organization should prepare for its July 1, 2023 effective date.
June 06, 2023

Webinar
Privacy Management
Orchestrate data retention & minimization for compliance with US state privacy laws
Join this interactive webinar to learn how OneTrust helps orchestrate data retention and minimization for compliance with US privacy laws.
June 06, 2023

Webinar
Privacy Management
Staying compliant: How to manage data transfers around the globe
In this webinar, we look at the subject of internation data transfers and how to effectively navigate regional laws and mitigate the risk of non-compliance.
June 06, 2023
Infographic
Privacy Automation
The ROI of DSAR automation
Learn how DSAR automation streamlines privacy rights requests and saves your organization time and resources.
June 01, 2023

Webinar
Privacy Management
EU-US data transfers: Breaking down DPC’s Meta decision
Join us for this webinar as we break down the May 22, 2023 DPC Meta decision and cover the key takaways for EU-US data transfers.
June 01, 2023
Regulation Book
Privacy Management
Colorado Privacy Act law book
The Colorado Privacy Act (CPA) comes into force on July 1. Get the law's official text right at your fingertips.
May 30, 2023
eBook
Privacy Management
Connecticut Data Privacy Act law book
Get the complete text of the Connecticut Data Privacy Act (CTDPA) for your reference.
May 30, 2023

Webinar
AI Governance
The EU's AI Act and developing an AI compliance program
Join Sidley and OneTrust DataGuidence as we discuss the proposed EU AI Act, the systems and organizations that it covers, and how to stay ahead of upcoming AI regulations.
May 30, 2023

Report
Privacy & Data Governance
Gartner® Innovation Insights: Data Security Posture Management (DSPM)
Read this report from Gartner® that highlights some of the key capabilities needed in a DSPM.
May 30, 2023

Webinar
Privacy Management
Saudi Arabia's PDPL latest amendments: Are you ready?
Join OneTrust and Deloitte Middle East as we cover the latest changes to Saudia Arabia's Personal Data Protection Law (PDPL) and what it means for organizations in the KSA region.
May 30, 2023

Infographic
Privacy & Data Governance
The 3 priorities of the French DPO: Gain visibility, take action, automate
Download our infographic and learn about the 3 priorities of the French DPO.
May 30, 2023

Webinar
Privacy Management
GDPR turns 5: Celebrating data protection
Northern Europe panel - Join our panel of experts as they recap the GDPR, its key concepts, and what it means for organizations and compliance.
May 25, 2023

Webinar
Privacy Management
Global Panel — GDPR & Tech: Key considerations of Privacy by Design and AI in tech
Join our panel of experts as we discuss the impact GDPR had on the tech industry during the past five years, the importance of privacy by design, and what to expect with AI and regulation.
May 25, 2023

Webinar
Trust Intelligence
How the Onetrust platform is innovating to unlock the value of trust
Join this webinar to learn how OneTrust is enhancing its privacy management, data governance, and consent and preferences solutions to help organizations tackle data sprawl and enable regulatory agility.
May 24, 2023

Webinar
Privacy & Data Governance
Global Panel — GDPR & Healthcare: current regulatory guidance and enforcement
In this live webinar, our expert panel examines the first five years of the GDPR, how it changed the healthcare industry, and the changing global regulatory landscape.
May 24, 2023

Webinar
Privacy Management
5 years of GDPR: Milestones, challenges, and opportunities
Eastern European panel - Watch our webinar as we look back on 5 years of the GDPR, AI, and their impact on Europe, the world, and your organization.
May 24, 2023
Infographic
Privacy Management
Comparing the FADP, Revised FADP, and the GDPR
Download our infographic to see how the Revised FADP compares with its original version and the GDPR.
May 23, 2023

Webinar
Privacy Management
Global Panel — GDPR & Retail: building customer loyalty and trust with consent and privacy
Join us for a live panel as we discuss GDPR's impact on the retail and eCommerce industry and how companies evolved to meet the global regulatory landscape.
May 23, 2023
eBook
Privacy Management
Getting started with GDPR compliance
This eBook covers the fundamental information you need to know in order to get your GDPR compliance program started and how OneTrust helps.
May 23, 2023

Webinar
Privacy Management
Global Panel — GDPR & Finance: Staying ahead of the regulatory and cyber landscape
How has the GDPR affected the financial industry? Join our live panel as we examine how it companies evolved to meet the regulatory challenges and what can be done to stay ahead of the curve.
May 22, 2023

Webinar
Privacy Management
Understanding Washington's My Health My Data Act
The Washington My Health My Data Act was signed into law on April 27, 2023 and will be enacted the following year. Join OneTrust DataGuidance and a team of legal experts and get the knowledge you need for compliance.
May 18, 2023
Infographic
Privacy Management
Comparing Canada's privacy laws infographic
Download this infographic to compare provisions in Alberta, British Colombia, and Quebec with those found at a federal level in PIPEDA and those proposed under the Consumer Privacy Protection Act.
May 18, 2023
Infographic
Privacy Management
Top tips for Law 25 compliance
Download this infographic to learn more about Law 25’s provisions, their effective dates, and what you can do for compliance.
May 18, 2023

Webinar
Privacy & Data Governance
Operationalizing the Iowa Consumer Data Protection Act
Join the Privacy experts at OneTrust for an update on the new law and learn key requirements of Iowa’s new privacy law and more.
May 16, 2023

Webinar
Privacy Management
Operationalizing employee privacy for CPRA compliance
Join this interactive webinar to learn how OneTrust helps to operationalize employee privacy for the California Privacy Rights Act (CPRA) compliance.
May 10, 2023

In-Person Event
Privacy & Data Governance
Privacy in practice
Join us for a deep dive into embedding privacy by design into the fabric of your business to promote the responsible use of data.
May 09, 2023

Webinar
Privacy Automation
Bridging borders: How to manage international data transfers
This session will cover the regulatory landscape, TIA guidance, and mitigation measures for international data transfers in the wake of the Schrems II case.
April 19, 2023 1 min read

In-Person Event
Third-Party Risk
Risk on the Road: Navigating data management, compliance automation and third-party risk
Join this OneTrust live event series, which will address critical topics such as navigating data management, compliance automation and third-party risk.
April 11, 2023

Webinar
Privacy Management
The US privacy landscape for third-party risk: a program prototype time
Learn how to balance the intricacies of CPRA, VCDPA, CPA, CTDPA, and UCPA when managing third parties and understanding privacy-related risks.
March 28, 2023

Webinar
Privacy Management
Unpacking the new UK Data Protection and Digital Information Bill
Learn more about the UK's new data protection bill, which introduces changes to build a more business-friendly framework while ensuring data adequacy.
March 22, 2023
Infographic
De-risking data through visibility and action
The rapid growth of data has increased the risk of data breaches, learn how IT and security teams can secure, monitor, and de-risk that digital information.
March 09, 2023

Infographic
Privacy Management
US privacy in 2023: Top 3 compliance priorities
Businesses at different stages of privacy maturity will need to approach US privacy compliance in different ways. Download the infographic to learn more.
March 08, 2023
eBook
Privacy Management
The 3 Priorities for DPOs in France: Gain Visibility, Take Action, Automate eBook | Resources | OneTrust
French DPOs should take three priorities into account when building their data protection and compliance programs and processes in 2023.
February 21, 2023

Webinar
Privacy Automation
Privacy by design becomes an ISO standard: What you need to know and how to implement for your business
Get an overview of ISO 31700, learn considerations for implementing a PbD framework for your organization, and a look at our Privacy by Design solutions.
February 16, 2023

Webinar
Privacy & Data Governance
Data Protection in Financial Services Week: Insurance – the privacy and cyber issues
This session focuses on emerging issues impacting data privacy and cybersecurity in the insurance and reinsurance industry and its cyber insurance products.
February 08, 2023

Webinar
Privacy & Data Governance
Data Protection in Financial Services Week: Government keynote and international transfers
This session will examine some key issues and recent developments on international data transfers with contributions from key EU, UK, and US regulators.
February 07, 2023

Webinar
Privacy Management
Data Protection in Financial Services Week: Managing cybersecurity in financial services
This first session will provide a real-time view from the trenches from a globally-recognized leader in cyber operational collaboration and defense.
February 07, 2023

Webinar
Privacy Management
Meet opt-out and opt-in consent requirements under US state privacy laws
Join this interactive webinar to learn how OneTrust Consent and Preferences help to enable consumers to opt-out of third-party trackers.
February 06, 2023

Report
Privacy & Data Governance
Privacy on the horizon: What organizations need to watch in 2023
The Privacy on the horizon: What organizations need to watch in 2023 report highlights the views of privacy experts and industry leaders at OneTrust.
February 03, 2023

Webinar
Privacy Management
Data Privacy Day: Protiviti & OneTrust
Join industry experts at OneTrust & Protiviti for an operational deep dive and interactive Q&A on the upcoming US State laws set to go into effect in 2023.
January 26, 2023

Checklist
Privacy Management
7 steps to CPRA compliance
Download this checklist to make sure your organization follows the right steps to implement processes that achieve California Privacy Rights Act compliance.
January 24, 2023

Webinar
Consent & Preferences
Expert panel: So you think you have a consent strategy?
As Quebec Bill 64 - also known as Law 25 - takes effect it's important to have a consent strategy that takes you beyond compliance.
January 20, 2023

Webinar
Privacy Management
Unpacking new digital data laws across europe: addressing the digital services act
This webinar discusses what companies fall within the DSA's scope, key things companies need to know about the DSA and its obligations, and challenges.
January 10, 2023
eBook
Privacy & Data Governance
The ultimate guide to US privacy
Learn more about the three priorities for managing US privacy requirements, including addressing the most visible aspects of US privacy compliance.
December 12, 2022

Webinar
Privacy Automation
DSARS: Utilising privacy automation to build a measurable ROI program
We’ll discuss three facets of this problem, such as how to discover, classify and automate your data processes to streamline records of processing activities.
December 07, 2022

Webinar
Privacy Management
California’s CPRA enters into effect – Are you compliant?
Watch this on-demand webinar to get an overview of the CPRA including new obligations for businesses and exemptions for select organizations.
December 06, 2022

Webinar
Privacy Management
Managing expectations under the UAE’s Personal Data Protection Law webinar
Join this webinar to hear from experts at Simmons & Simmons Middle East LLP and OneTrust about practical tips on complying with the UAE PDPL.
November 28, 2022

Webinar
Privacy Automation
Minimization, retention, and purpose-limitation: Evolving privacy to data governance
Join this OneTrust webinar to gain insight into how to operationalize and automate retention and minimization requirements.
November 22, 2022

Webinar
GRC & Security Assurance
Analyzing ISO 27001:2022 reinforcing privacy and security compliance with automation webinar
Learn how InfoSec teams can automate scoping mandatory requirements and streamline generating evidence to prove compliance across ISO.
November 17, 2022

Webinar
Privacy Management
Minimization, retention, and purpose-limitation: Evolving privacy to data governance
In this webinar, OneTrust Privacy experts discuss requirements and best practices for governing personal and sensitive data under US state privacy laws.
November 17, 2022

Webinar
Privacy & Data Governance
Japan APPI: Are you ready for the upcoming amendments?
Watch this webinar for an overview of the upcomining Japan APPI amendments and what it means for your organization.
October 31, 2022

Webinar
Privacy Management
Expert Panel: Navigating Quebec Bill 64 (Law 25)
Our industry experts discuss what makes Law 25 unique and how the impending changes will influence business decisions across industries in Canada.
October 20, 2022

Webinar
Third-Party Risk
How OneTrust can help scale your Third-Party Risk program
In this webinar, we provide a live product demonstration to show you how your organization can optimize and scale a third-party risk program.
October 18, 2022

Webinar
Third-Party Risk
7 core metrics every third-party risk program must track (and how to track them)
We’ll discuss the 7 core metrics successful third-party risk programs track and how to track them, such as critical metrics to track as your program matures.
September 28, 2022

Webinar
Privacy & Data Governance
Operationalizing quebec bill 64 (Law 25): Steps to take & pitfalls to avoid
In this video, you will learn how OneTrust allows you to operationalize in detail the top practical elements of Bill 64 and how to maintain these practices.
September 26, 2022

Webinar
Privacy Management
California Age-Appropriate Design Code Act: What you need to know
Watch our webinar, where legal experts from Latham and Watkins LLP discussed an overview of the recently signed Assembly Bill 2273 and its requirements.
September 26, 2022

Webinar
Privacy Management
Unpacking new digital data laws across Europe: Addressing the digital markets act
Learn challenges related to the enforcement of the DMA, such as the interplay between the DMA’s data-related obligations and other regulatory instruments.
September 20, 2022

Webinar
Privacy Automation
Establishing and enforcing retention policies
In this webinar, we will cover data policy requirements across the EU and discuss steps to automate data policy management and operational considerations.
September 05, 2022

Webinar
Privacy Automation
Don’t just document it, enforce it. Embedding privacy by design into cloud migrations
Learn how businesses can implement governance policies like retention, minimization, and open access through integrating technologies to minimize risks.
September 05, 2022

Webinar
Third-Party Risk
10 best practices for streamlining your third-party risk management workflows
Watch this webinar to hear how to leverage third-party risk management workflow creation and maintenance best practices.
August 30, 2022

Webinar
Third-Party Risk
Cybersecurity panel: How well do you know the threats posed by your third parties?
In this panel discussion, we address critical points such as defining the metrics to track in relation to third parties and their cybersecurity risks.
August 28, 2022

Webinar
Privacy Management
Employee vs. consumer rights: Same concept, different reality
Join this webinar to learn about the rights request fulfillment complexities introduced by the end of the employee exclusion in the CPRA.
August 25, 2022

Webinar
Privacy Management
Expanded US consumer rights: What’s new and what should you do?
Join our experts to understand the operational impact of these newly-expanded US consumer rights and how to automate consumer rights request fulfillment.
August 25, 2022

Webinar
Privacy Management
A look at the US privacy landscape
This webinar will cover requirements, governing bodies, enforcement expectations for CPRA, VACDPA, CPA, CTDPA, and UCPA, and updates on the ADPPA.
August 25, 2022

Webinar
Privacy Management
Privacy risk assessments in the US: Why, when, and what?
In this webinar, OneTrust experts discuss requirements for conducting PIAs: why they exist, when you should do them, and what they should include.
August 24, 2022
Regulation Book
Privacy Management
Comprehensive US Privacy Law Book
Download our Comprehensive US Privacy Law Book to easily refer to the law text from all current regulations in the US privacy landscape, such as the CPRA.
August 23, 2022

Webinar
Third-Party Risk
Third-Party risk and the U.S. privacy landscape: the top 5 things you need to know
In this webinar, we’ll review services providers under the ADPPA and outline how you can ready your third-party risk program to align with privacy regulations.
July 31, 2022

Webinar
Privacy Management
Establishing and enforcing retention policies
Attend our webinar, "Establishing and enforcing retention policies," part of the US Privacy Laws Masterclass Series.
July 27, 2022

Webinar
Third-Party Risk
Better by tomorrow: 7 third-party risk assessment best practices you can implement today
In this webinar, we’ll explore these questions and layout 7 must-know best practices to conduct more meaningful third-party risk assessments.
July 15, 2022

Webinar
Privacy Management
Utah and Connecticut: Latest additions to the US Privacy landscape
Watch our webinars on the latest privacy laws from Utah and Connecticut and what you need to know to prepare in 2023.
June 17, 2022
eBook
Privacy & Data Governance
Comparing US state privacy laws
Download this eBook and explore the key areas of US state privacy laws and how they compare.
June 15, 2022

Webinar
Privacy Management
How to identify & respond to privacy incidents
Join this webinar and learn how to build an Incident Management Playbook to address global privacy incidents.
June 07, 2022

Webinar
Third-Party Risk
Third-Party risk best practices: How to align privacy & security teams for greater productivity
This webinar will discuss best practices for how privacy and security teams can work together to eliminate redundant work, save time, and be more efficient.
June 06, 2022

Webinar
Privacy Management
Incident management: How European companies can build trust
Watch this webinar to learn how responding to all kinds of incidents big and small creates a culture of trust.
May 24, 2022

Webinar
Data Discovery & Security
Rethinking trusted data
Join us for a discussion on the latest trends in trusted data and how you can take critical steps to build trust in data practices
May 24, 2022

Webinar
Privacy Management
Data regulation ramps up in Europe: DMA, DSA, and the UK Online Safety Bill
Watch this webinar as we discuss the EU's Digital Markets Act (DMA) and the Digital Services Act (DSA) as well as the UK Online Safety Bill (UK OSB)
May 19, 2022

Webinar
Privacy Management
Thailand privacy landscape: Enforcement of the PDPA & New developments
Watch our webinar on Thailand Personal Data Proctection Act (PDPA) and what it means for data processors and controllers.
May 15, 2022

Webinar
Privacy Automation
OneTrust and Microsoft come together to automate employee rights requests
Join OneTrust and Microsoft in this webinar where we discuss our automated tool for processesing DSAR requests.
May 11, 2022
Resource Kit
Privacy Management
Your US privacy masterclass resource kit
These resources provide key information on US privacy law through blogs, webinars, and eBooks.
April 26, 2022
eBook
Privacy Automation
The ultimate guide to privacy program automation
Download our guide and learn how automation allows teams to address broader aspects of their privacy programs such as DSARs, incident management, and more.
April 26, 2022

Webinar
Third-Party Risk
Accelerating automation: How the pandemic forced third-party management to scale
Watch this webinar and see how the COVID-19 pandemic forced companies to accelerate automation and scale their third-party management.
April 26, 2022

Webinar
Data Discovery & Classification
UK panel: What are data subject access requests and how do you manage them?
Join our UK legal experts as they discuss data subject rights access requests (DSAR) and how automation streamlines fulfilment and protects privacy.
April 19, 2022

Webinar
Privacy Management
Privacy rights poland: Enhance Your DSAR process with automation, discovery & redaction
As part of our Privacy Automation webinar series, we discuss why it's important to automate DSAR fulfillment and the latest regulatory trends.
April 03, 2022

Webinar
Privacy Management
Employee rights: Prepare for the CPRA’s Employee Inclusion
Watch this webinar and prepare for compliance with the CPRA's employee rights requirements.
March 24, 2022

Webinar
Privacy Management
Consumer rights: What’s new in 2023
Watch this webinar to learn about US consumer privacy rights in 2023 and practical steps you can take to make compliance.
March 24, 2022

Webinar
Privacy Management
Managing sensitive personal information (SPI)
Watch our masterclass webinar for a deep dive on sensitive personal information (SPI) and best practices for compliance.
March 24, 2022

Webinar
Privacy Management
Overview: Understanding the trio of US privacy laws
Attend our webinar, to better understand privacy laws in the US.
March 23, 2022

Webinar
Privacy Management
Navigating opt-out of sale vs. share
Watch our US Privacy Law masterclass to learn about opt-out of sales and share requirements and best practices for approaching compliance.
March 23, 2022

Webinar
Privacy Management
New to US privacy: Privacy impact assessments
Watch our webinar as we discuss privacy impact assessments and how they relate to US privacy laws.
March 23, 2022

Webinar
Privacy Management
Privacy rights: Enhance Your DSAR process with automation, discovery & redaction
As part of our Privacy Automation webinar series, we discuss why it's important to automate DSAR fulfillment and the latest regulatory trends.
March 22, 2022

Webinar
Data Discovery & Classification
UK DSAR automation: From intake to redaction and beyond
Join us for this instalment of our Future of Privacy Automation Series for a discussion of the challenges, key components, and building blocks of DSAR automation.
March 14, 2022

Webinar
Data Discovery & Classification
Tackling unstructured data challenges
In this webinar, learn about the risks of unstructured data and effective strategies in automating discovery.
March 02, 2022

Webinar
Privacy Management
Privacy 101: Steps to establishing a sustainable privacy program
Join CrossCountry Consulting and OneTrust to learn everything you need to get the fundamentals of building a privacy program.
February 24, 2022

Webinar
Privacy Management
US Privacy series: Effectively governing personal and sensitive personal information part 3
Watch our webinar on US privacy laws and gain insight on effective personal information managment strategies.
February 02, 2022

Webinar
Privacy Management
Privacy 101: Where do I start?
Join LevelUp and OneTrust to learn everything you need to get started in building or improving an existing privacy program.
January 20, 2022

Webinar
Privacy Management
Privacy 101: The basics of building a privacy program (No matter your size)
Join Red Clover Advisors and OneTrust to learn everything you need to get the fundamentals of building a privacy program.
January 20, 2022

Webinar
Privacy Management
Austria DSB rules on Analytics Complaint: The implications on data transfers
Watch this free webinar and learn about the recent Austrain DSB ruling on Google Analytics and the implicactions on data transfers under the GDPR.
January 19, 2022

Webinar
Privacy Management
Global data residency requirements: What you need to know
Watch our webinar on global data residency requirements and learn about their implications and challenges.
January 18, 2022

Webinar
Privacy Management
Mature your privacy program through automation, intelligence & governance
Watch this webinar and learn how to achieve real time visibility into you data and the policies for an effective privacy program.
January 14, 2022

Webinar
Privacy Management
Israel Privacy Protection Bill: Unpacking the proposed amendments
Watch this webinar where we discuss the Israel Privacy Protection Bill, its proposed amendments, and what it means for your organization.
January 13, 2022

Infographic
Privacy Automation
4 steps for automating your privacy platform
Automate your privacy program and reduce manual inefficiencies
January 13, 2022

Webinar
Privacy Management
US Privacy series: Effectively governing personal and sensitive personal information part 2
Join us for an overview of US privacy laws and strategies for dealing with compliance.
January 11, 2022

Webinar
Data Discovery & Security
Automating the classification and mapping of sensitive data
In this free webinar, learn how to automate the classification and mapping of sensitive data and speed compliance.
January 10, 2022
eBook
Privacy Management
CCPA vs. CPRA: next steps
The CPRA enters into effect on Jan 1, 2023 expanding the CCPA's requirements. This eBook outlines the next steps from CCPA to CPRA compliance.
January 05, 2022

Webinar
Privacy Management
2022 Third-party trust predictions and preparations
Prepare for 2022 Trends in Third-Party Risk Management and future-proof your Third-Party Trust program.
January 04, 2022

Webinar
Privacy Management
[Part 1] US Privacy Series: Establishing a foundation for compliance
In the first part of our US Privacy Series, we discuss US privacy laws such as the CPRA and best practices towards compliance.
December 21, 2021

Webinar
Privacy Management
Operationalizing iOS app account deletion
Watch our webinar on implementing account deletion for iOS apps and best practices.
December 09, 2021

Checklist
Privacy Automation
Automate your privacy program
Download the checklist and discover the steps you can take to automate critical processes across your privacy program.
December 01, 2021

Webinar
Consent & Preferences
Google consent mode & OneTrust CMP
Learn the benefits of using Google Consent Mode with the OneTrust CMP (Cookie Consent) to balance compliance and marketing objectives.
October 27, 2021

Webinar
Privacy Management
CCPA, CPRA, and Global Privacy Control: Moving toward a more private web
Watch this webinar to learn about Global Privacy Control (GPC), how it centralizes user opt-out preferences, and streamlines compliance with CCPA and CPRA.
September 08, 2021

Webinar
Privacy Management
Managing data retention strategies
As organizations become more data-driven, one of their biggest challenges is managing data retention strategies.
August 27, 2021

Webinar
Privacy Management
Build an incident management playbook
Prepare for privacy and security incidents by building an incident management playbook.
August 27, 2021

Webinar
Privacy Management
Know your laws: Japan's APPI
Join the OneTrust DataGuidance privacy analyst team for a deep-dive webinar examining Japan's APPI and what it means for organizations.
July 22, 2021

Infographic
Privacy Management
CDPA vs CCPA: Comparing US privacy laws
Download this infographic comparing the Virginia CDPA to the California CCPA.
July 22, 2021

Webinar
Third-Party Risk
Are you a trusted vendor? 10 things every customer wants to know
Access this free webinar to learn how to be a trusted vendor.
July 22, 2021

Webinar
Privacy Management
UK adequacy decision: What you need to know
Join this webinar to hear more about the UK Adequacy Decision and what it means for data flows between the UK and the EU.
July 21, 2021
eBook
Privacy Management
The Ultimate Guide to Privacy Management eBook
Download the Ultimate Guide to Privacy Management to understand the major factors that contribute to a privacy management program.
June 11, 2021

Video
Consent & Preferences
OneTrust Consent & Preference Management demo
Watch this demo video to learn how OneTrust Consent and Preference Management Cloud streamlines the consent lifecycle and accelerates fulfillment.
October 24, 2020
White Paper
Privacy & Data Governance
Privacy governance framework
Download our white paper and learn about OneTrust's Privacy Governance Framework and how it can serve as a blueprint for your privacy program.
January 01, 2020

Webinar
AI Governance
Mature your data privacy program
OneTrust DataGuidance and Sidley are joined by industry experts for the annual Data Protection in Financial Services Week.

Webinar
US Privacy Masterclass: Countdown to 2023 compliance
Join this US Privacy Masterclass series as we delve into the evolving US privacy landscape and how you can build a trust-based privacy program in 2023.

Webinar
Privacy Management
US Privacy Masterclass 2022
Watch the OneTrust US Privacy Masterclass series and gain insight on the major US privacy law and best practices.

Webinar
Privacy Management
Navigating Canadian consumer rights requests
Join our webinar to learn how to effectively manage DSARs and comply with Quebec's Law 25, ensuring your organization meets customer and regulatory expectations.

Webinar
Privacy Management
Mature your data privacy program
Learn how to mature your data privacy program beyond reactive compliance to become a strategic enabler for your business.

Demo
Privacy Automation
Privacy Automation demo
Automate DSR fulfillment, track regulations, maintain an evergreen data map, and so much more — all in one powerful privacy solution.

Webinar
Privacy Management
Privacy in Practice with PA Consulting
Join OneTrust and expert speakers from PA Consulting for a webinar series discussing the need-to-knows for creating a successful privacy management program in your organization.

Webinar
Privacy Automation
PIA and DPIA demo webinar with Data Privacy Group
Join our webinar to learn the benefits of automating your PIAs and DPIAs using the OneTrust platform
Find the Privacy Automation package that meets your needs
FAQ
Our software supports your data privacy compliance with key privacy regulations like GDPR, CCPA, and countless others by providing a centralized platform to help you manage the workflows, tasks, and reporting required for privacy compliance.
Purpose-built applications powered by automated data discovery and embedded regulatory intelligence deliver the agility and simplification you need to navigate the complex regulatory environment.
Yes, OneTrust automates your data mapping process to give you a clear picture of your personal data processing activities and regulatory requirements associated with data transfers across jurisdictions. We’ll also provide an always-available data inventory of assets, processes, and vendors for records of processing (ROPA).
Yes, our platform approach enables you to embrace privacy by design, streamline consent and preferences, manage third-party risk, implement AI and data governance, and even support your ethics and compliance strategy.
In addition to providing the latest innovations, automation tools, and enablement to support effective privacy management and data protection, we also:
Facilitate educational webinars, events, and roundtables
Provide free training and certifications
Partner with industry-leading organizations and thought leaders, such as IAPP
