Third-party risk management (TPRM) can have a different meaning for different business units, but one thing is for certain: visibility and proper oversight is an absolute must.
There are a variety of stakeholders in the business who require greater visibility into vendor operations across compliance, security, and ethics officers. Historically, legal and procurement teams own third-party risk evaluations as an on-boarding exercise. Beyond that two of the most common drivers for greater third-party oversight include incident events and compliance obligations. In the event of a widespread vulnerability, businesses need to know the potential impact on its extended network.
Learn in this webinar why ITRM is essential to your third-party risk program.
Simultaneously, the compliance team needs to see what data has been or is planned to share with a third-party. Based on the context of the data, the team then needs insights into what privacy and security controls are in place to meet compliance requirements.
And while each department has its own role to play in risk management, they all share the common thread of being tasked with ensuring the security and privacy of its company’s data.
Risk Silos Create Inefficiencies
Be it low bandwidth, prioritization issues, or differences in operational requirements, each business is going to face challenges with maturing TPRM programs. On-boarding, compliance reporting, and incident response are examples of point in time vendor engagements, that are often reflected in reactive vendor evaluations. Often this leads to a lack of communication and visibility between internal teams, fueling risk silos.
When teams are managing risks in an individual or siloed manner, a ton of other problems become evident, including duplication of risk mitigation efforts, risk analysis gaps, and a lack of knowledge transfer for best practices between internal teams to manage those third-party networks and improve the business’s overall risk posture.
The interconnectivity of risk throughout a business is more prevalent than ever before; a single risk from a third party can create endless impacts on the business as a whole.
Break Down Silos to Open Visibility
The crux of TPRM is to ensure a business’s wider network, throughout their supply chain and business enablement tools, is keeping its goods secure, and also maintaining compliance to support their organizational requirements as well as the needs of their customers.
Legal compliance is essentially a function of risk. It is typically executed as a check-box exercise reviewed periodically. Compliance requirements do provide a clear starting point — a baseline, not a goal — to communicate effectively with third parties. But risk on the other hand is fluid and changes depending on the context of the product or service being outsourced and must be evaluated in the context of business objectives: How does this impact the organization as a whole?
Since third-party risk is horizontal across most business functions, understanding those broader implications requires a collaborative, ongoing perspective rather than a function of check-point certification or compliance reporting.
What’s the business value of standing up a TPRM program? Find out more in this white paper.
The stakeholders who own the TPRM programs need to take a collaborative approach to assess their vendors and understand each one’s true impact on the business. If third-party risk only lives in compliance or procurement, that collaboration aspect can easily be overlooked because it falls outside that business unit’s scope. Or, it is only evaluated during onboarding, compliance audits, or incident events. In order to break down those silos, the same stakeholders need to reach across the aisle and collaborate with critical risk counterparts such as IT and security, privacy, ethics, and even Environmental, Sustainability, and Governance (ESG).
As the cyber landscape and third-party networks grow in tandem, a new wave of regulations around reporting breaches and other incidents have also evolved. Cyber risk should be seen as an essential function across all business units in a holistic manner — rather than exclusive to a particular department or group — in order to reduce the risk and events of non-compliance. The broader context of risk must be communicated and considered in compliance-based engagements to avoid critical, business-damaging information from being kept in a silo.
Answering the question of ‘who owns third-party risk’ is not about pinpointing a specific person or role within the organization. Rather, all businesses and their stakeholders have a hand in making sure third-party risk management is both in place and informed on how outsourced products, assets and service enable associated business units within the company in an ongoing manor.
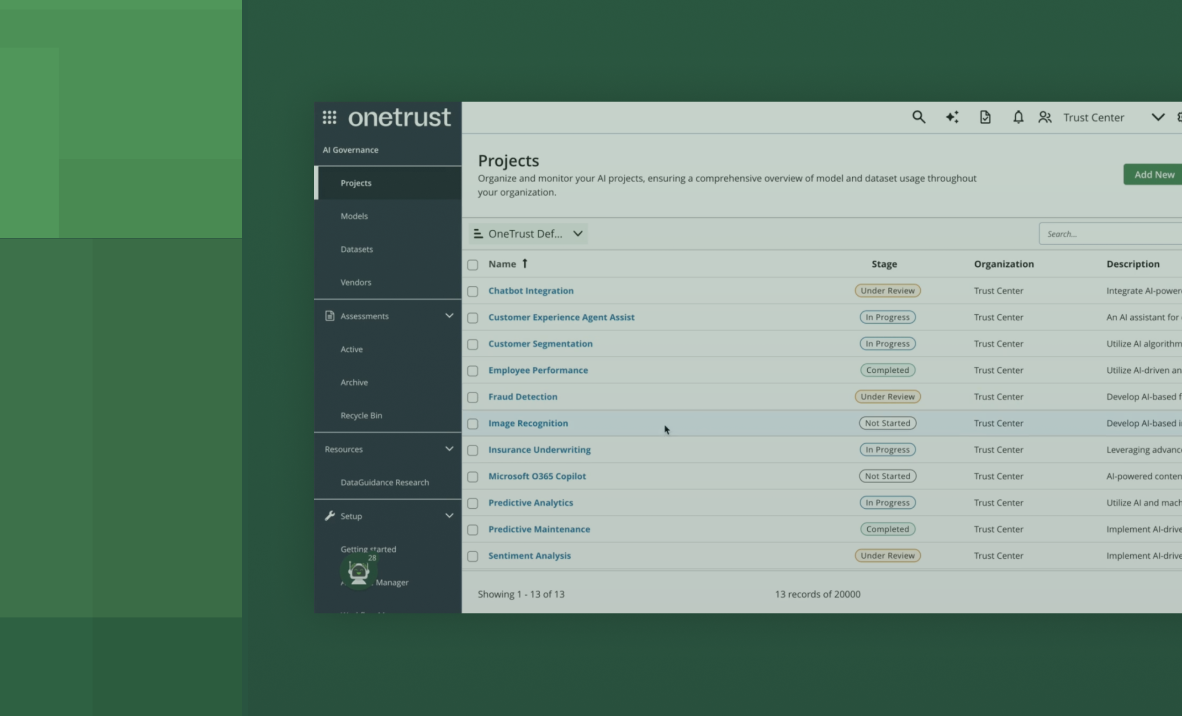
How Does OneTrust Help?
OneTrust delivers an integrated platform for risk management, specifically across IT, Security, and Third-party risk management. Organizations can scale collaboration by sharing automation best practices from assessments and automated workflows with the proper tooling. More importantly, third-party risk teams collaboratively share information with risk-adjacent programs and ease friction across traditionally manual collection points.
Contact our team to learn more about how OneTrust can help streamline information gathering and remediation activities with tailored functionality and automation backed by compliance intelligence.
Follow OneTrust on LinkedIn, Twitter, or YouTube for the latest on privacy and security compliance.