If you find you’re looking at your privacy program and sighing in frustration, it’s time for a change. Your CCPA compliant program needs to evolve into something more. In this blog post, we’ll take you through how you can automate your consumer requests within your CCPA program.
What are the three levels of consumer request automation?
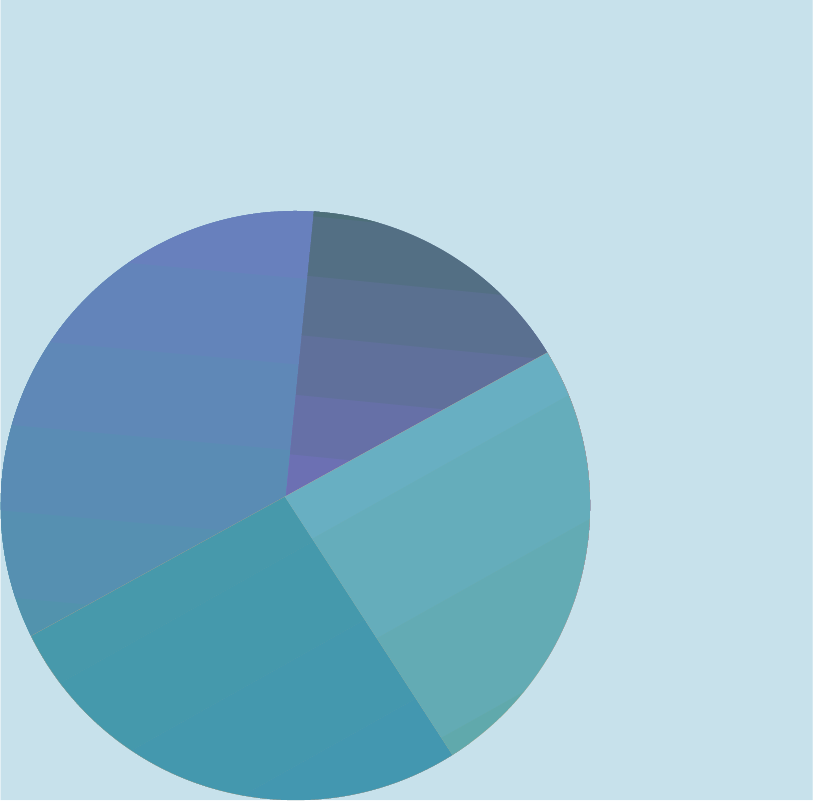
There are three standard levels of request automation out there: manual tasks, a hybrid of manual and automation, and full automation.
Manual tasks force the users to painstakingly fulfill and respond to each aspect of every single consumer request. It sounds exhausting, doesn’t it?
Well, that’s where the hybrid of manual and automation comes in. Users have partial automation to help with fulfilling requests with exception triggers built-in so the user can step in and manually enter information when necessary.
The third level is the most time-efficient process to rely on: full request automation. In a fully automated situation, all of the manual tasks that users had to deal with are automated. Instead of having to reply manually to each individual consumer (flooded inboxes are no fun), automated responses are used. Plus, you can have a real-time consumer portal for turnover as opposed to searching your endless inboxes and spreadsheets to keep track of everything.
Check out OneTrust Targeted Discovery Data to help you automate your manual tasks today.
What are the three common areas of request automation?
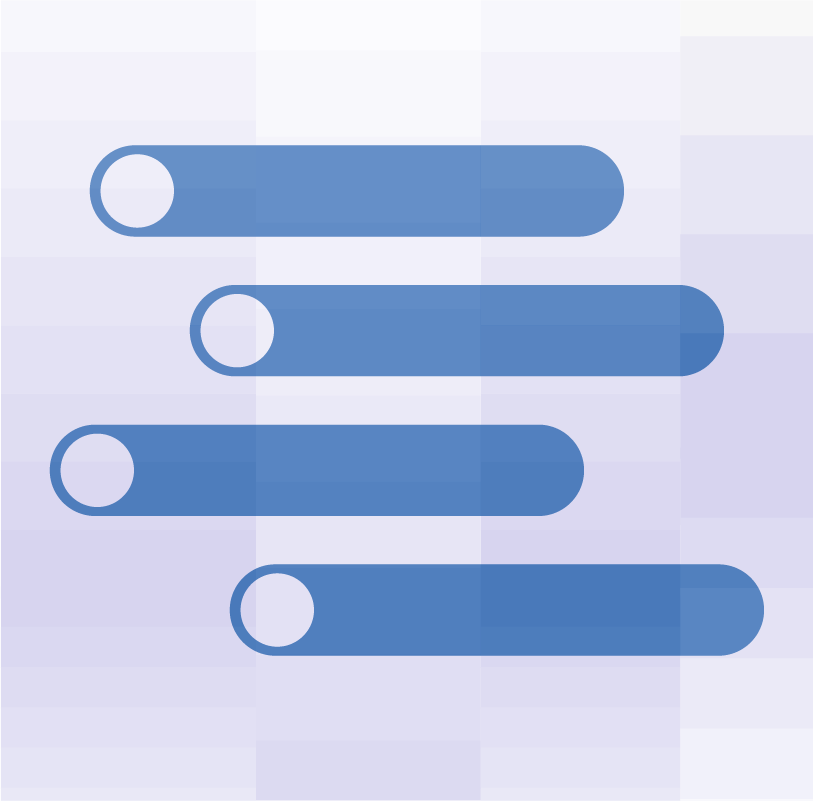
The three common areas of request automation that privacy experts deal with are intake, verification, and fulfillment of the request.
With intake, you receive the request from the consumer either through a website, the toll-free number provided, or in person.
Verification is necessary to verify the consumer’s identity. This can include security questions, personal identification, and other ways of verifying the authenticity of the consumer making the request depending on your business processes and how sensitive the information being requested is.
Finally, the fulfillment of the request occurs. This is where the retrieval and action for the data occurs. These actions include access, deletion, portability, or pseudonymization. There is a lot that can be done with the data.
The “Privacy inbox”: Why doesn’t it work?
Unfortunately, many companies nowadays take a rather unstructured approach to handling consumer requests: the privacy inbox. The privacy inbox is like a vortex where the consumer can enter anything they want (say “no” to spam) and even if they enter in a lot of information, what they have entered may not even contain all of the information you actually need (no, we don’t need to know what you had for lunch).
In addition to getting all of this junk that you don’t even want or need to fulfill a request, most privacy inboxes have no form of bot detection. Who wants to try to talk to a bot all day other than another bot?
The worst part about this is that sifting through the privacy inbox actually takes effort on the user’s part. What if your entire job was just going through thousands of emails trying to figure out consumer requests? It’d probably get frustrating really quick.
Targeted data discovery™: The way to evolve your program
With Targeted Data Discovery, you can easily automate your requests. No more sifting through inboxes. Forget spending hours chatting with bots. Targeted Data Discovery easily integrates with your custom apps, has pre-built plugins in the OneTrust integrations marketplace, and has abstraction using application gateway to avoid OneTrust needing direct access. This keeps your information secure and positions your company in the best light for CCPA compliance. Check out Targeted Data Discovery today.